Method for processing a security message in mobile communication system
一种移动通信系统、安全消息的技术,应用在移动通信的消息处理领域
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] Reference will now be made in detail to the preferred embodiments of the invention, examples of which are illustrated in the accompanying drawings. Wherever possible, the same reference numbers will be used throughout the drawings to refer to the same or like parts.
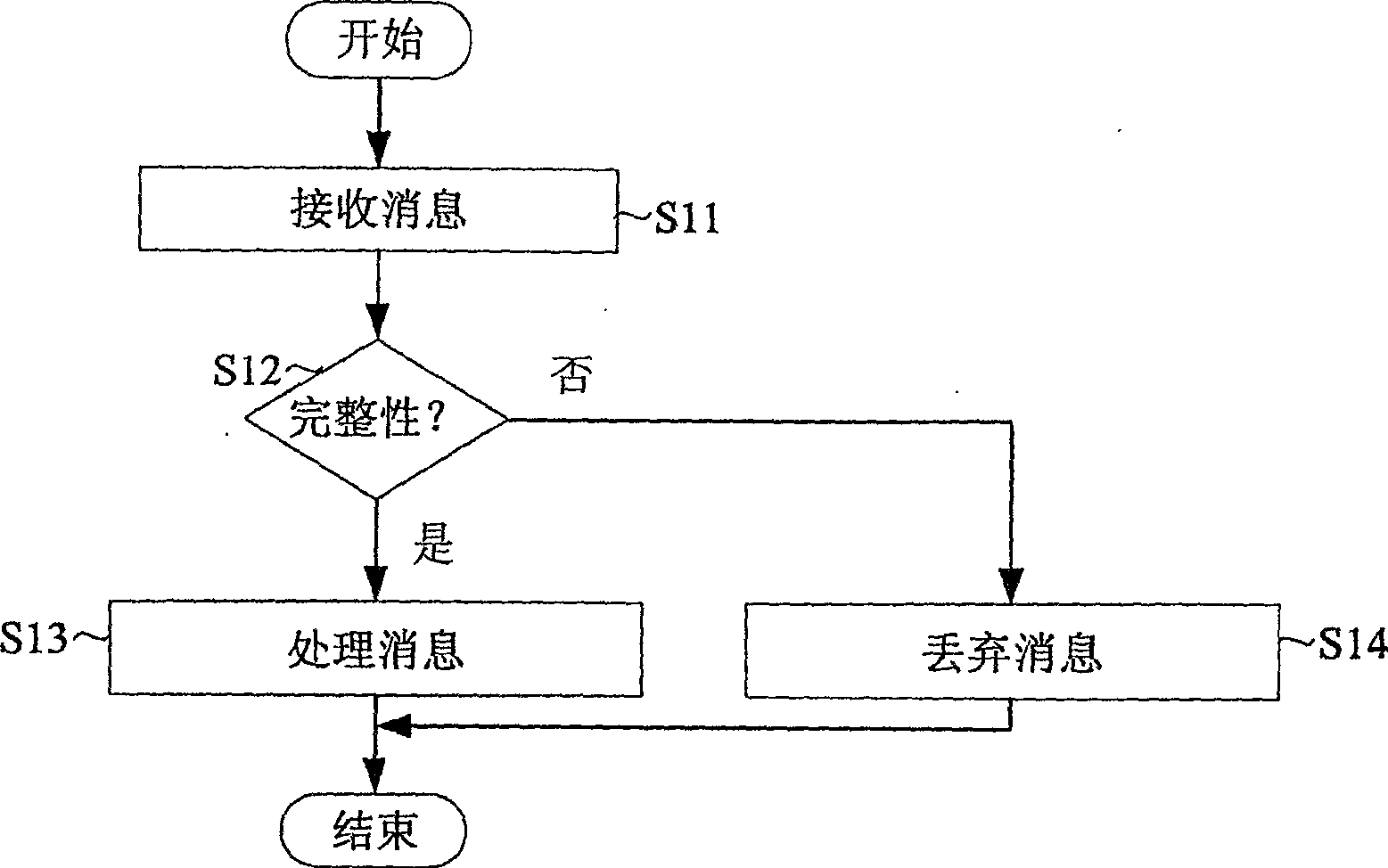
[0028] figure 1 is a flowchart illustrating a general message processing method.
[0029] refer to figure 1 , UE (User Equipment) first receives a general message (S11) and performs an integrity check on it (S12). Depending on the result of the integrity check, the message is processed normally or discarded. That is, if the message passes the integrity check, it is processed normally (S13). If the message does not pass the integrity check, it will be discarded due to security issues (S14).
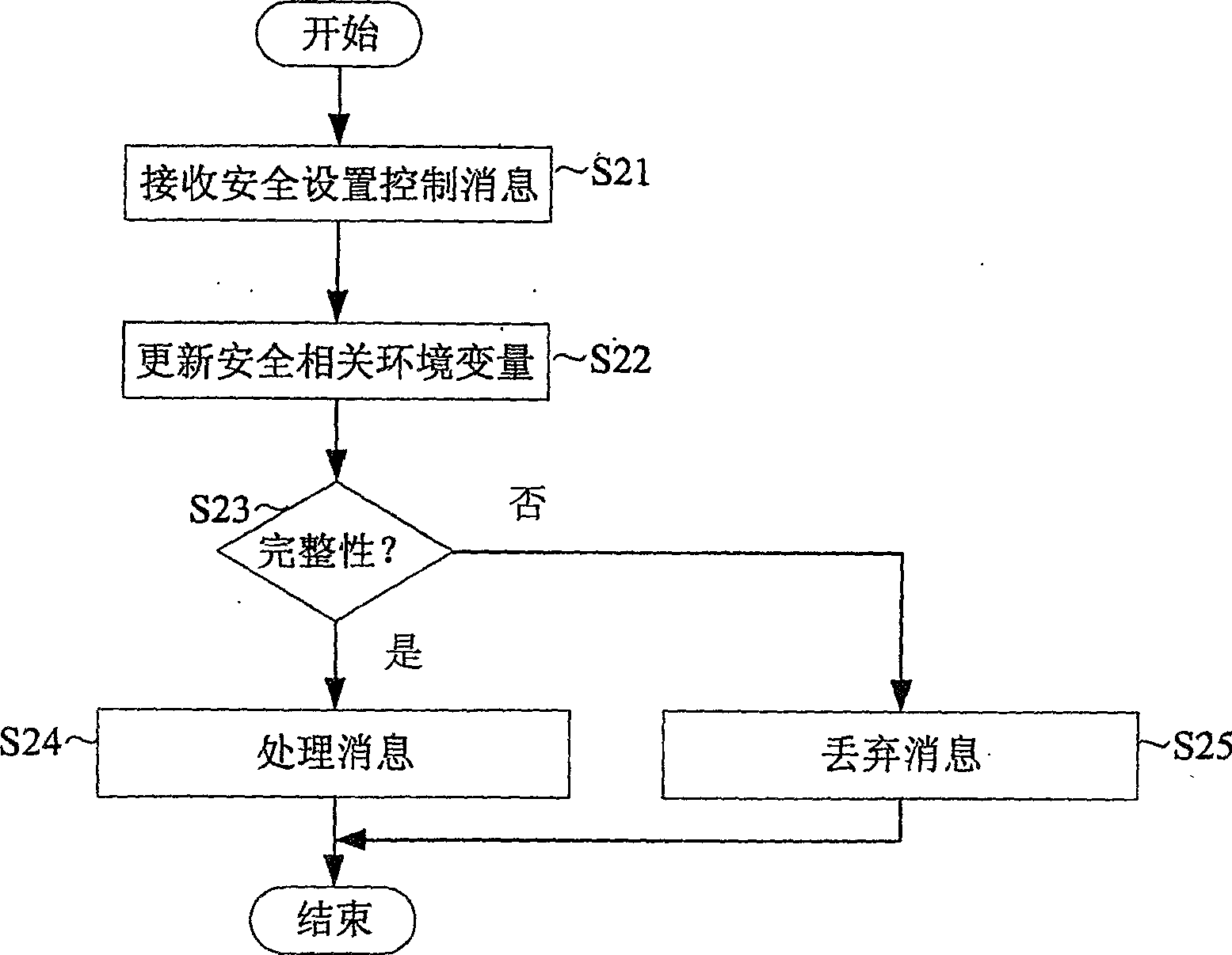
[0030] figure 2 is a flowchart illustrating a method of processing a security setting control message according to the first embodiment of the present invention.
[0031] refer to figure 2 , UE (User Equipmen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More