Network identity authenticating method and system
A network identity and network authentication technology, applied in the field of network identity authentication, can solve the problems of low security and insufficient security, and achieve the effect of making up for low security and strong security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
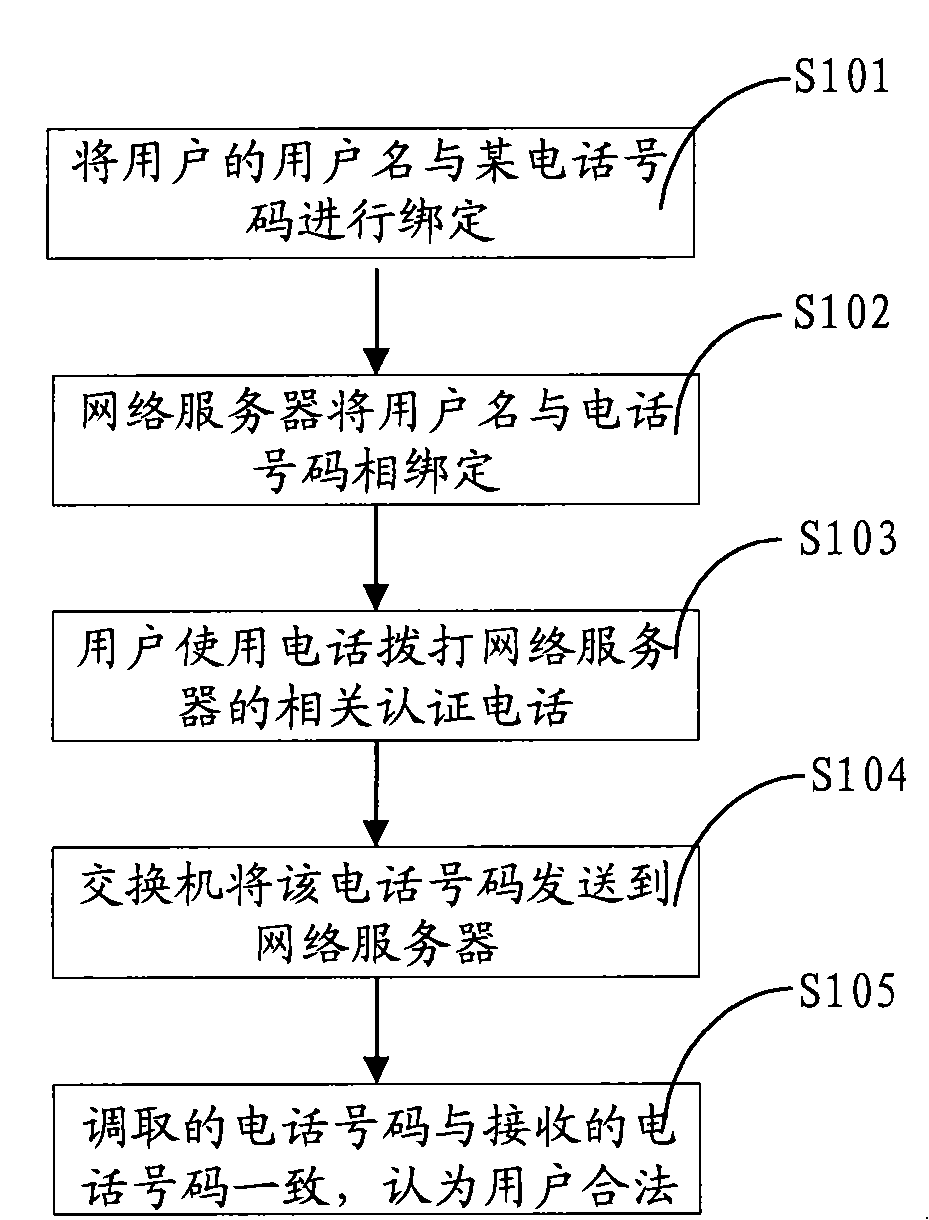
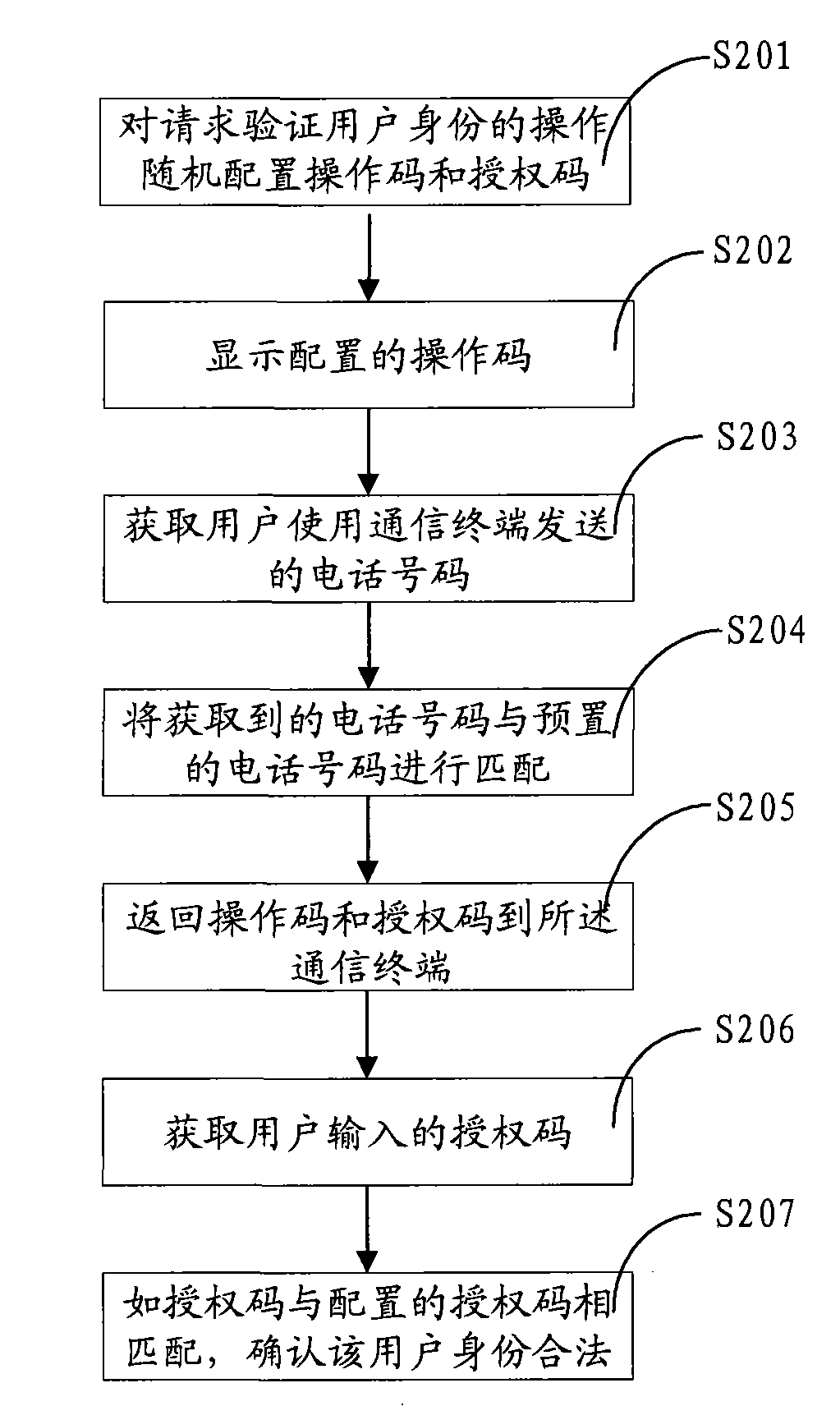
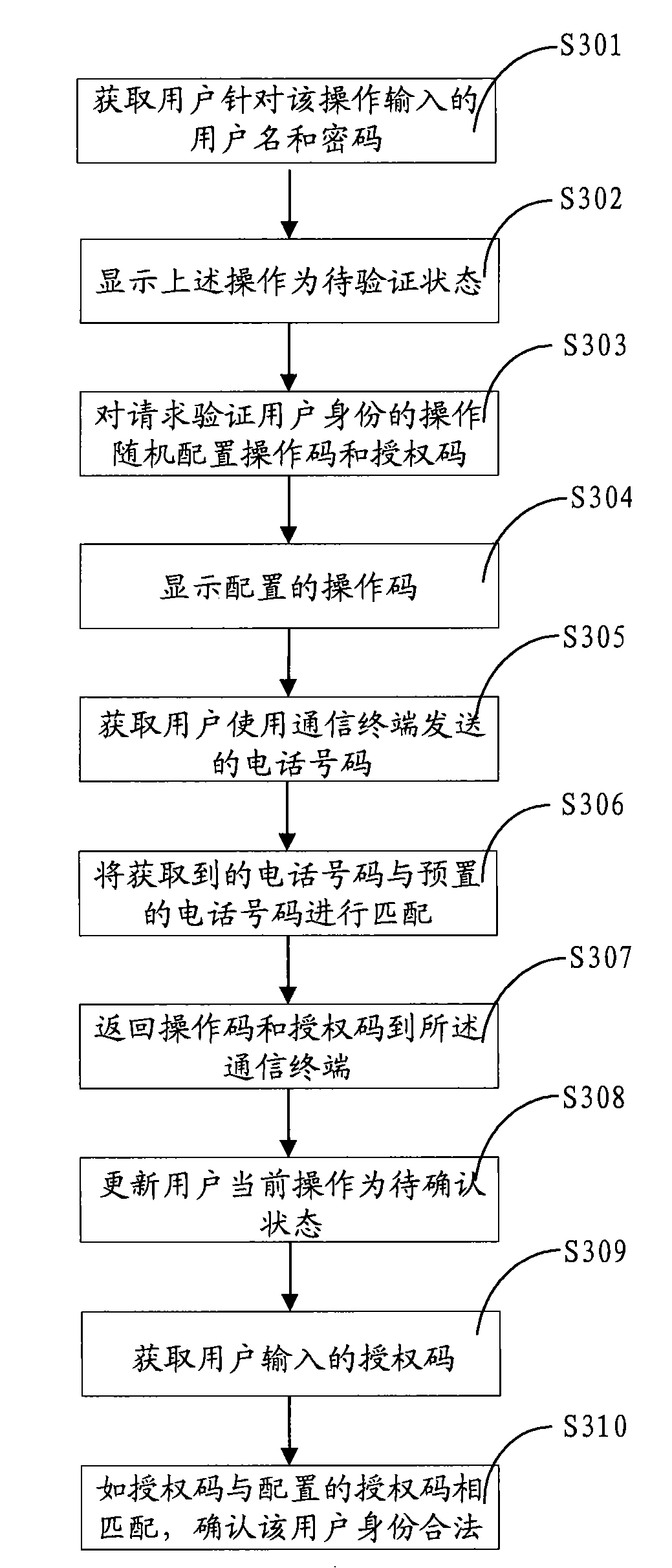
[0048] The present invention randomly configures the operation code and the authorization code for the operation of requesting to verify the user's identity, displays the operation code, and then obtains the telephone number sent by the user using the communication terminal, and matches it with the preset telephone number. If it is consistent, the operation code and the authorization code are returned. The authorization code is sent to the communication terminal; when the returned operation code is consistent with the displayed operation code, the authorization code input by the user is obtained, and if the authorization code entered by the user matches the randomly configured authorization code, it is confirmed that the user's iden...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More