Anti-quantum computing RFID authentication method and system based on symmetric key pool and online and offline signatures
A symmetric key and quantum computing technology, which is applied in the field of secure communication, can solve the problems of server key storage pressure, insufficient identification security, and insufficient key security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
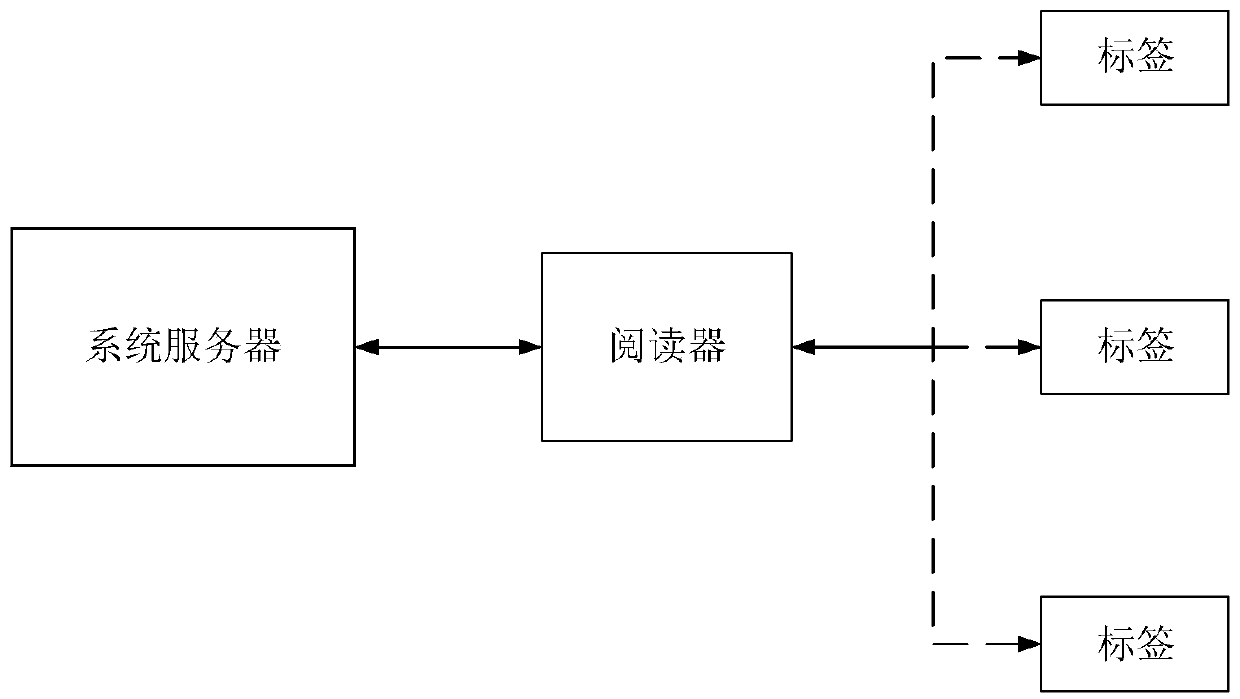
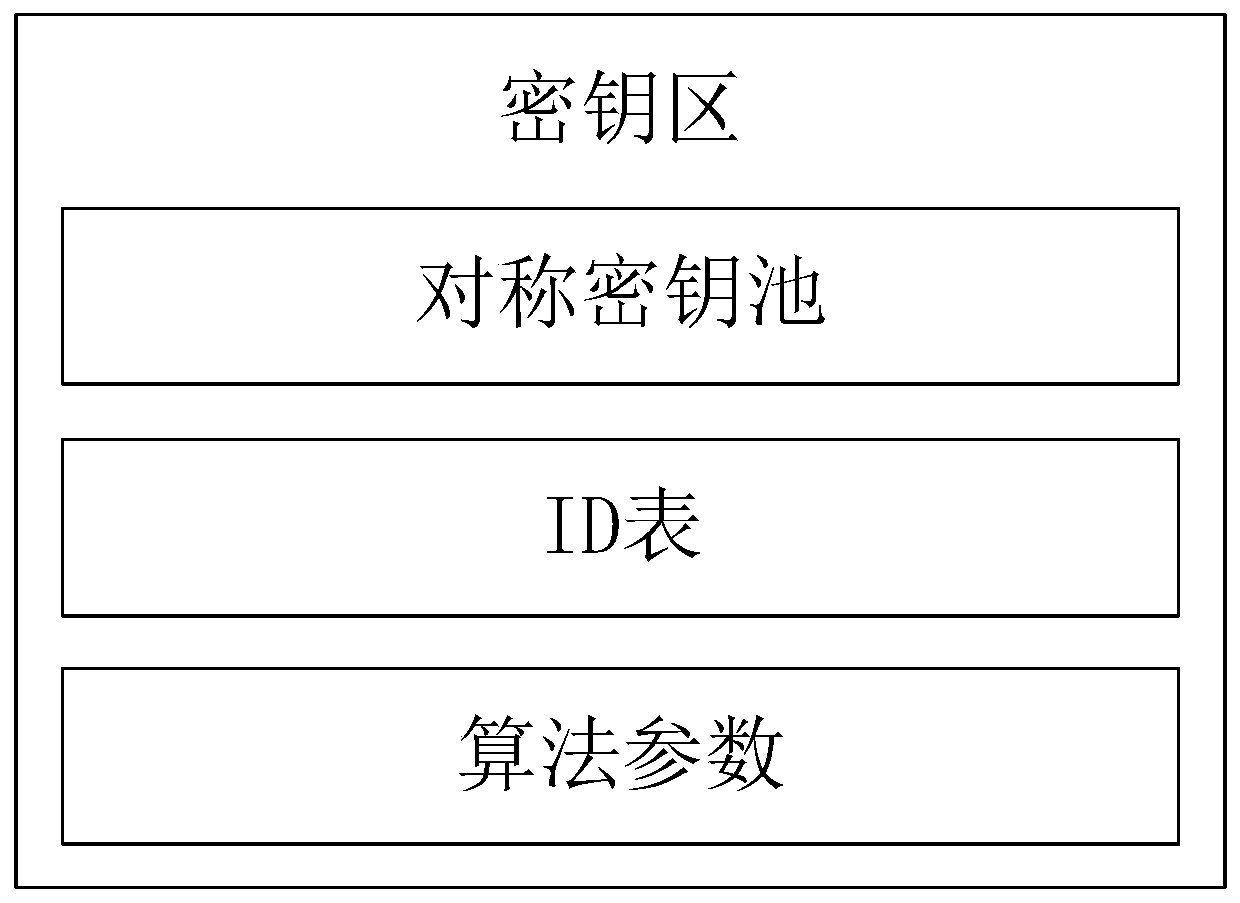
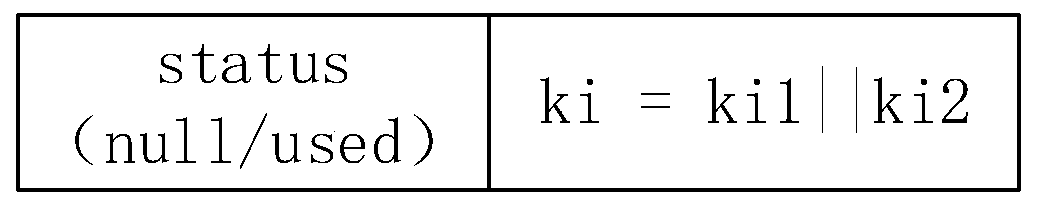
[0062] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0063] In order to better describe and illustrate the embodiments of the application, reference may be made to one or more drawings, but additional details or examples used to describe the drawings should not be regarded as an invention of the application, the presently described implementation limitations on the scope of any of the examples or preferred modes.
[0064] It should be understood that, unless otherwise specified herein, the steps are not strictly...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More