High-efficiency, deniable, safety-unforgeable cryptographic key exchanging protocol of on-line computation
A key exchange protocol and protocol technology, which is applied in the field of key exchange protocols, can solve the problems of unforgeable security, the protocol cannot be repudiated, and the resistance to denial of service attacks is not considered.
- Summary
- Abstract
- Description
- Claims
- Application Information
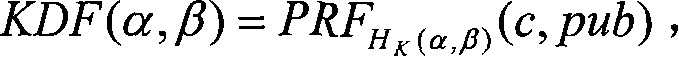
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment approach
[0116] In the specific implementation of Protocol-1, the session identifier sid can be omitted, and the DH key component (X, Y) plays the role of sid.
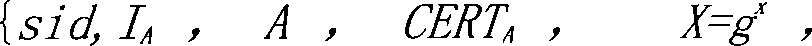
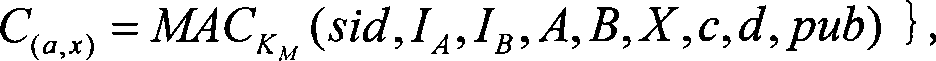
[0117] First round, from "A" to "B": {I A , A, CERT A , X=g x (mod p)}, where x is from Z q randomly selected from. X is called the DH keying component of "A".
[0118]After receiving the information sent by "A", "B" verifies the identity, public key and certificate of "A", X is not 1 and Z with order q * p elements in . If the verification is unsuccessful, "B" refuses to proceed with the protocol, otherwise, it goes to the next round.
[0119] Second round, from "B" to "A": {I B , B, CERT B , Y=g y}, where y starts from Z q randomly selected in and Y is referred to as the DH component of "B".
[0120] After receiving the information sent by "B", "A" verifies the identity, public key and certificate of "B", Y is not 1 and Z with order q * p elements in . The verification is unsuccessful, and "A" terminates the a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More