Patents
Literature
927 results about "Denial-of-service attack" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled.
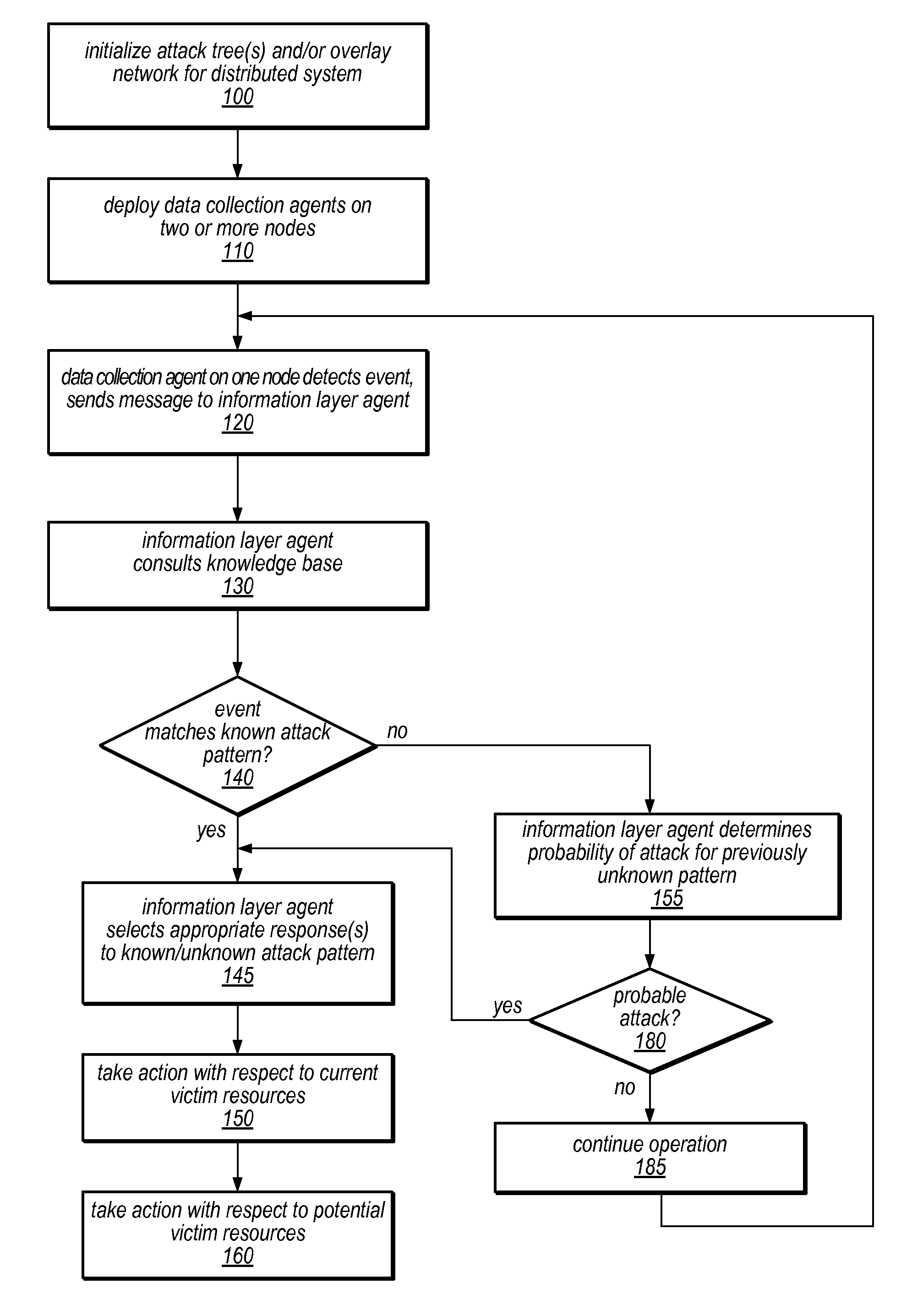
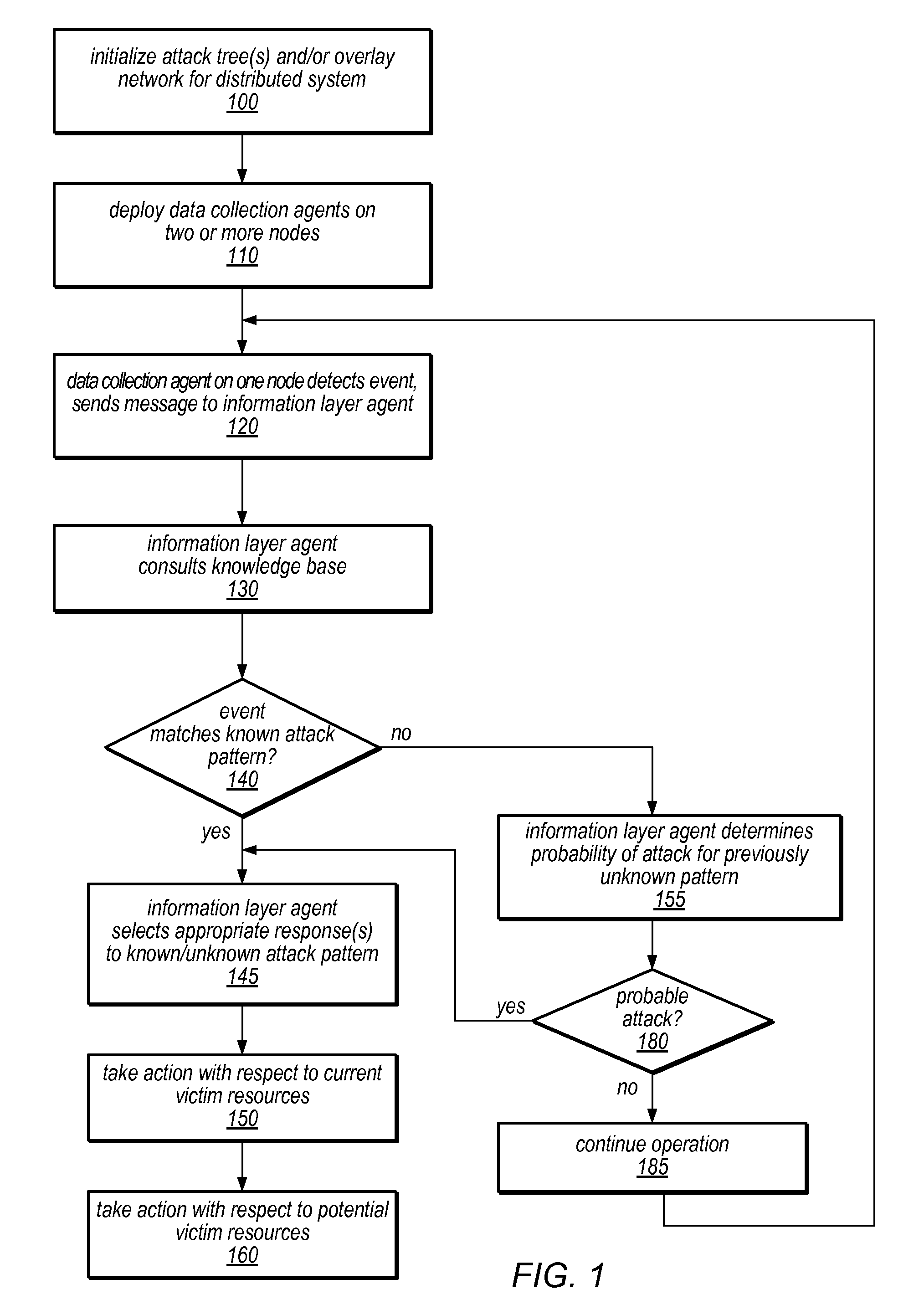
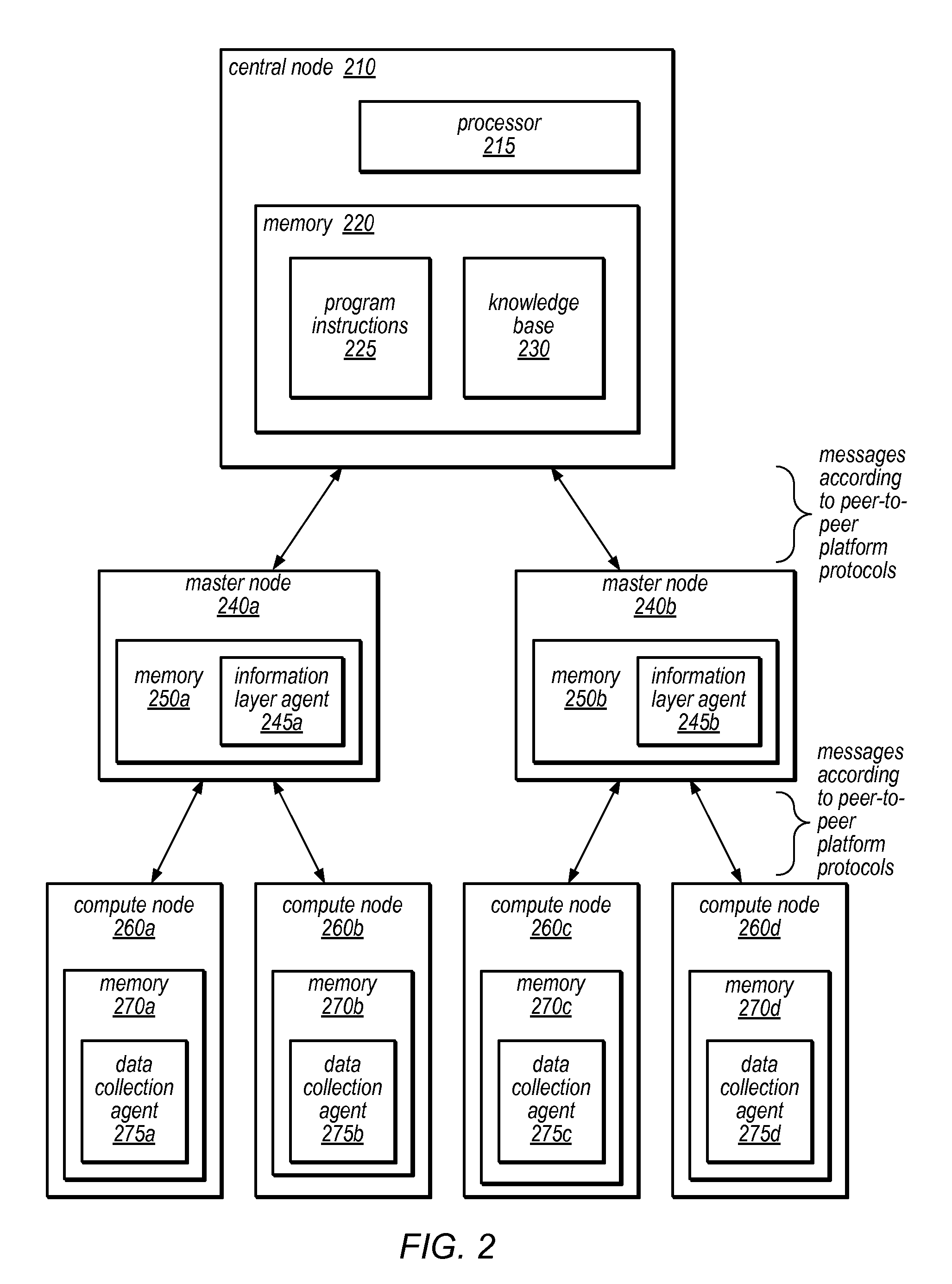
System and Method for Distributed Denial of Service Identification and Prevention
Systems and methods for discovery and classification of denial of service attacks in a distributed computing system may employ local agents on nodes thereof to detect resource-related events. An information later agent may determine if events indicate attacks, perform clustering analysis to determine if they represent known or unknown attack patterns, classify the attacks, and initiate appropriate responses to prevent and / or mitigate the attack, including sending warnings and / or modifying resource pool(s). The information layer agent may consult a knowledge base comprising information associated with known attack patterns, including state-action mappings. An attack tree model and an overlay network (over which detection and / or response messages may be sent) may be constructed for the distributed system. They may be dynamically modified in response to changes in system configuration, state, and / or workload. Reinforcement learning may be applied to the tuning of attack detection and classification techniques and to the identification of appropriate responses.
Owner:ORACLE INT CORP
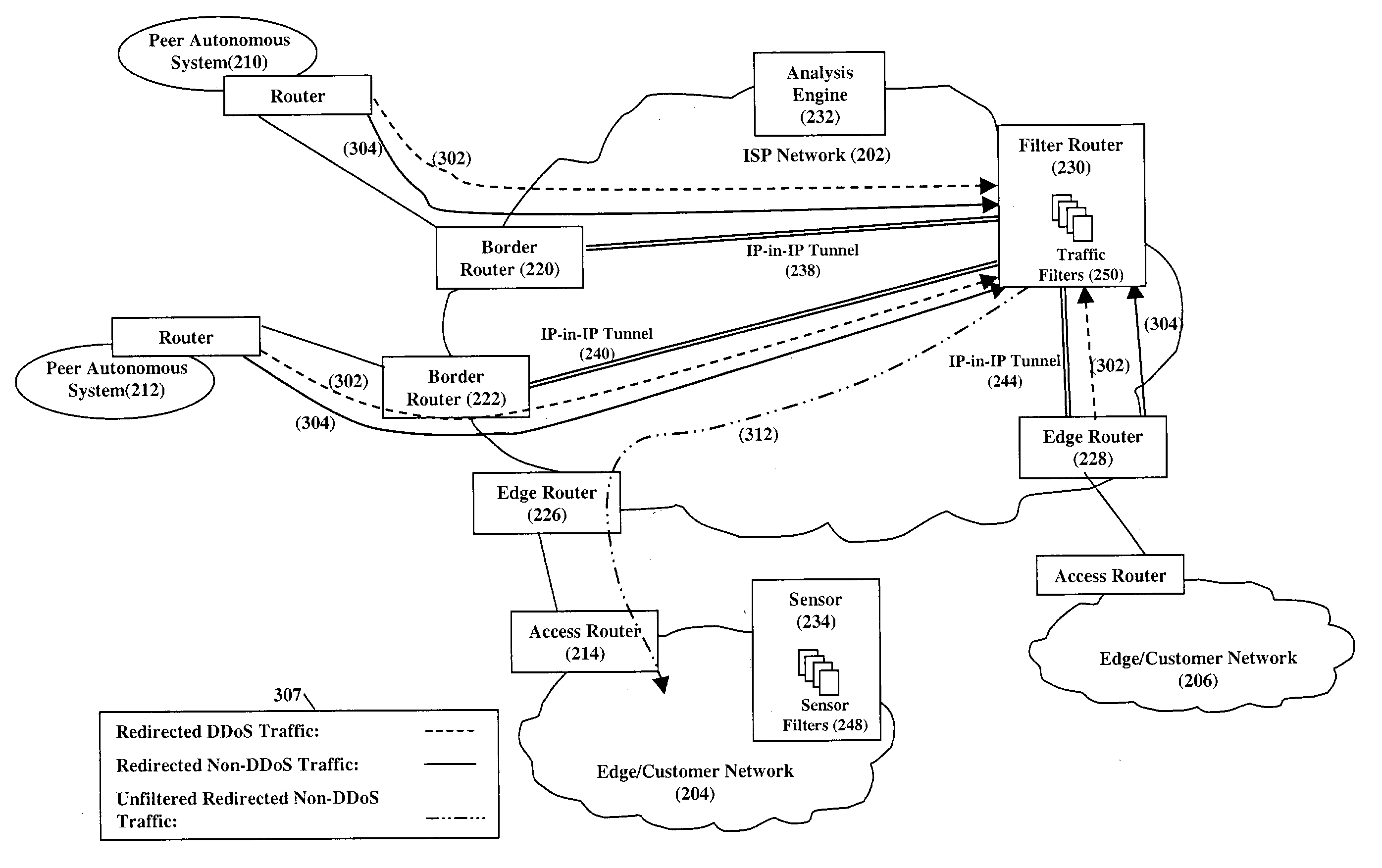
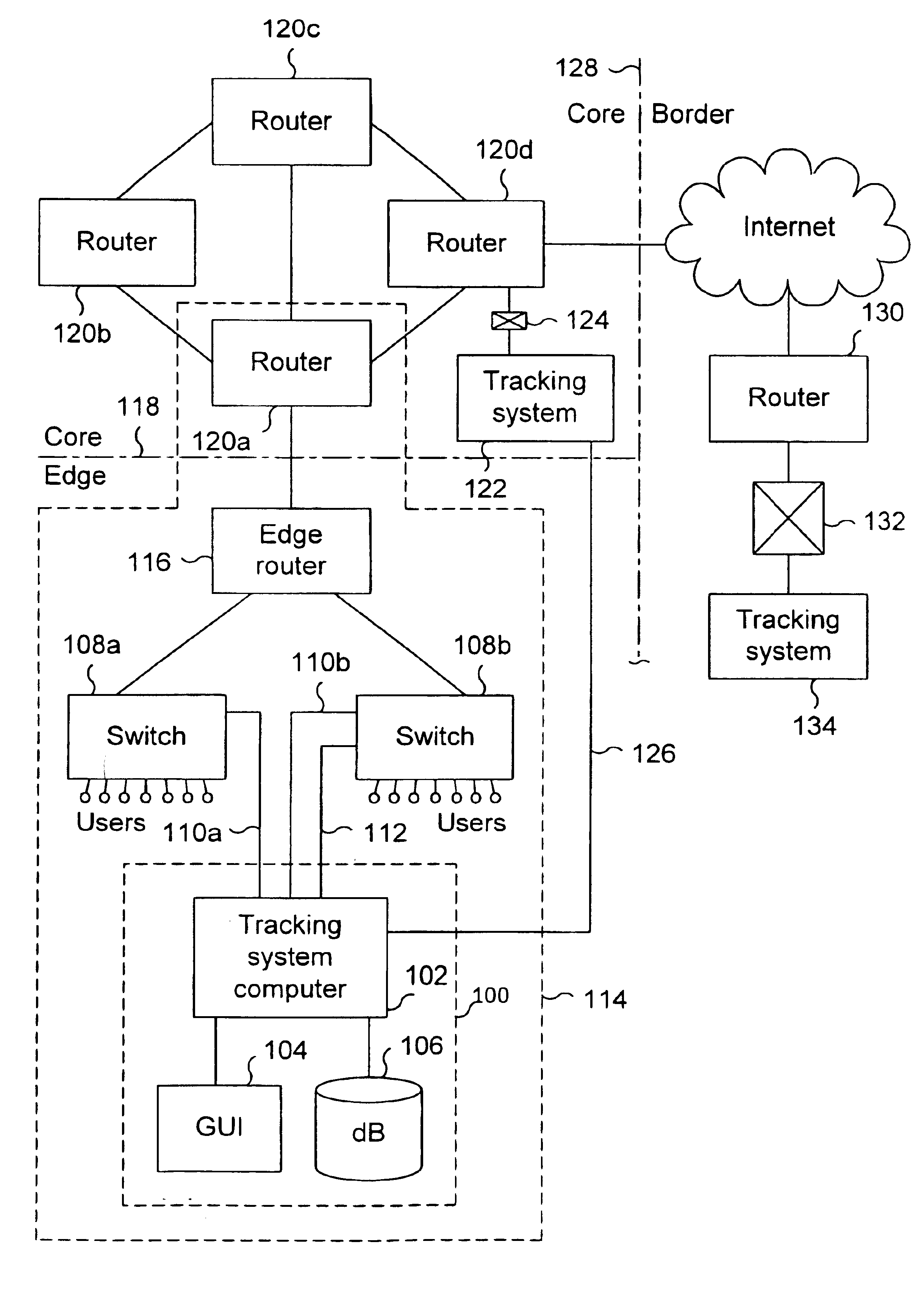
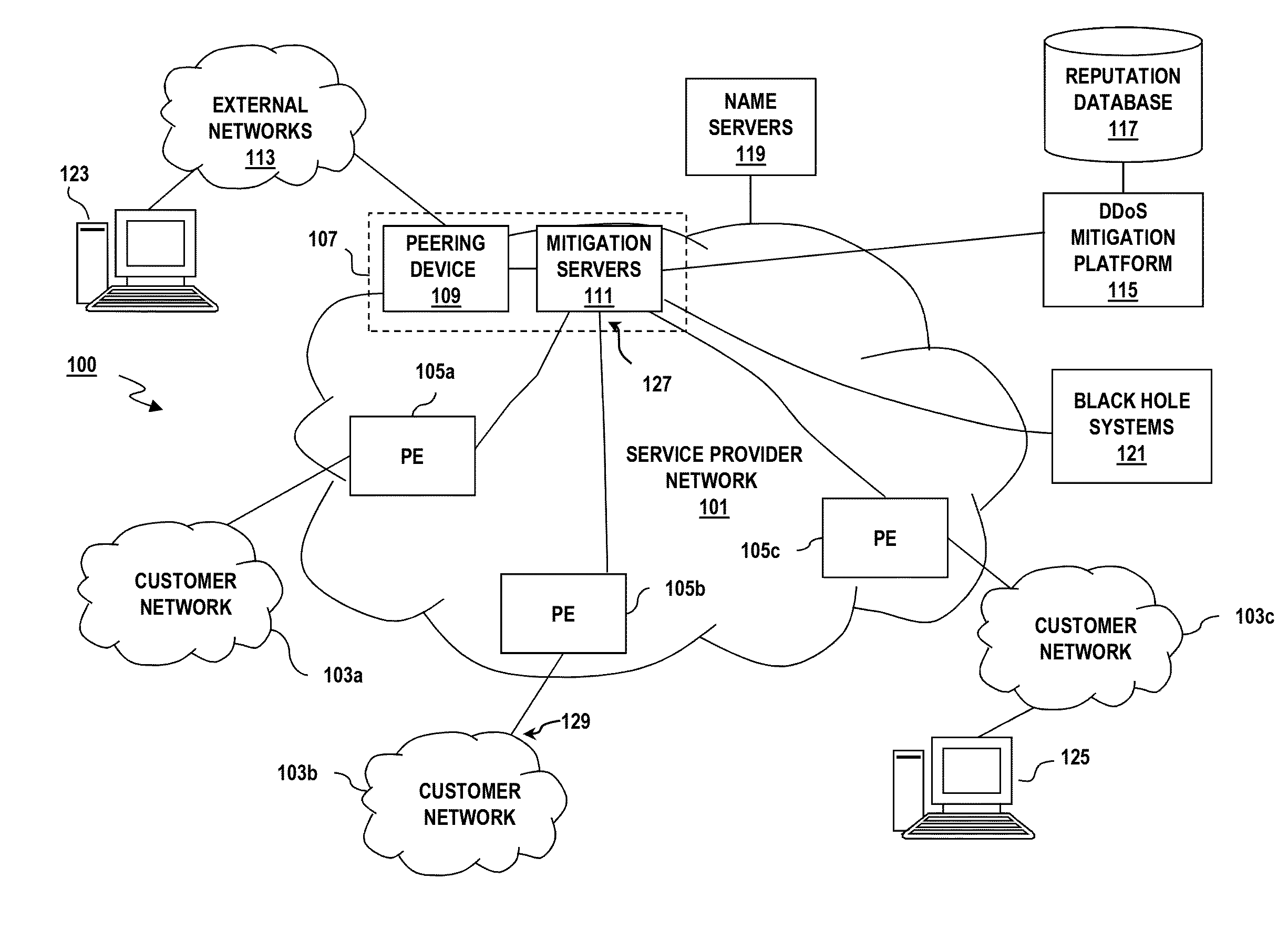
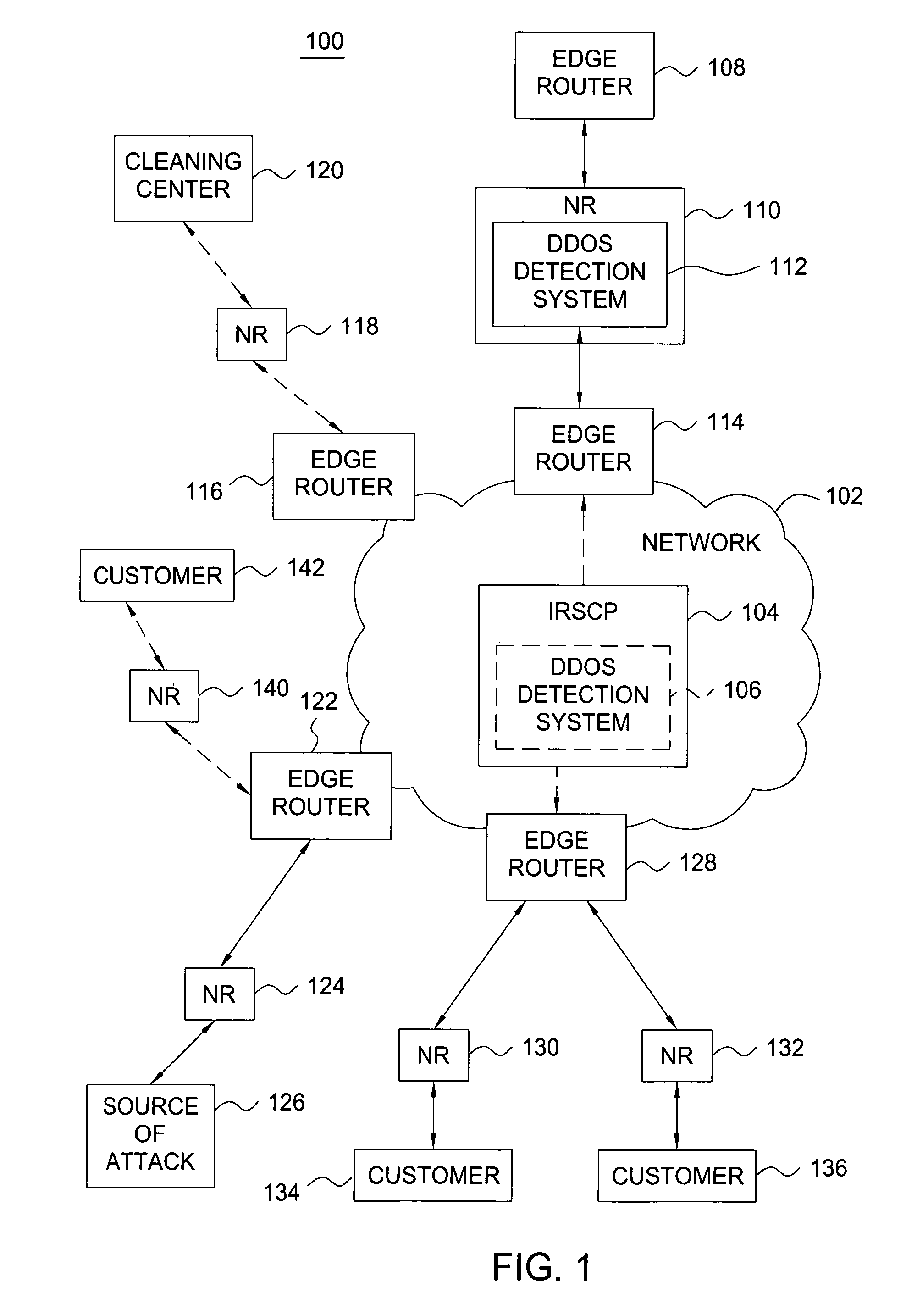
Mitigating denial of service attacks
InactiveUS20040148520A1Easily scaledMemory loss protectionUnauthorized memory use protectionThe InternetNetwork routing
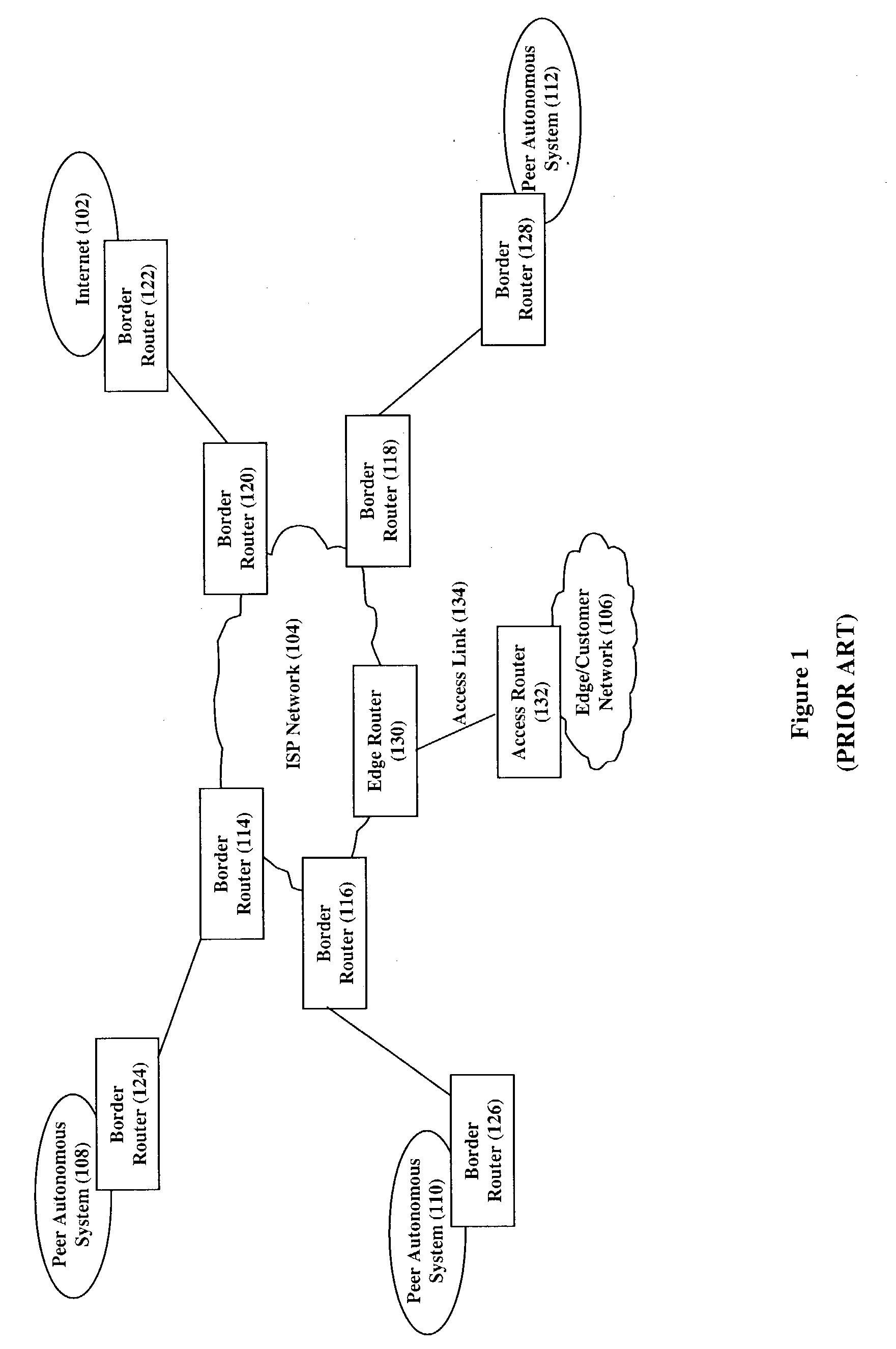
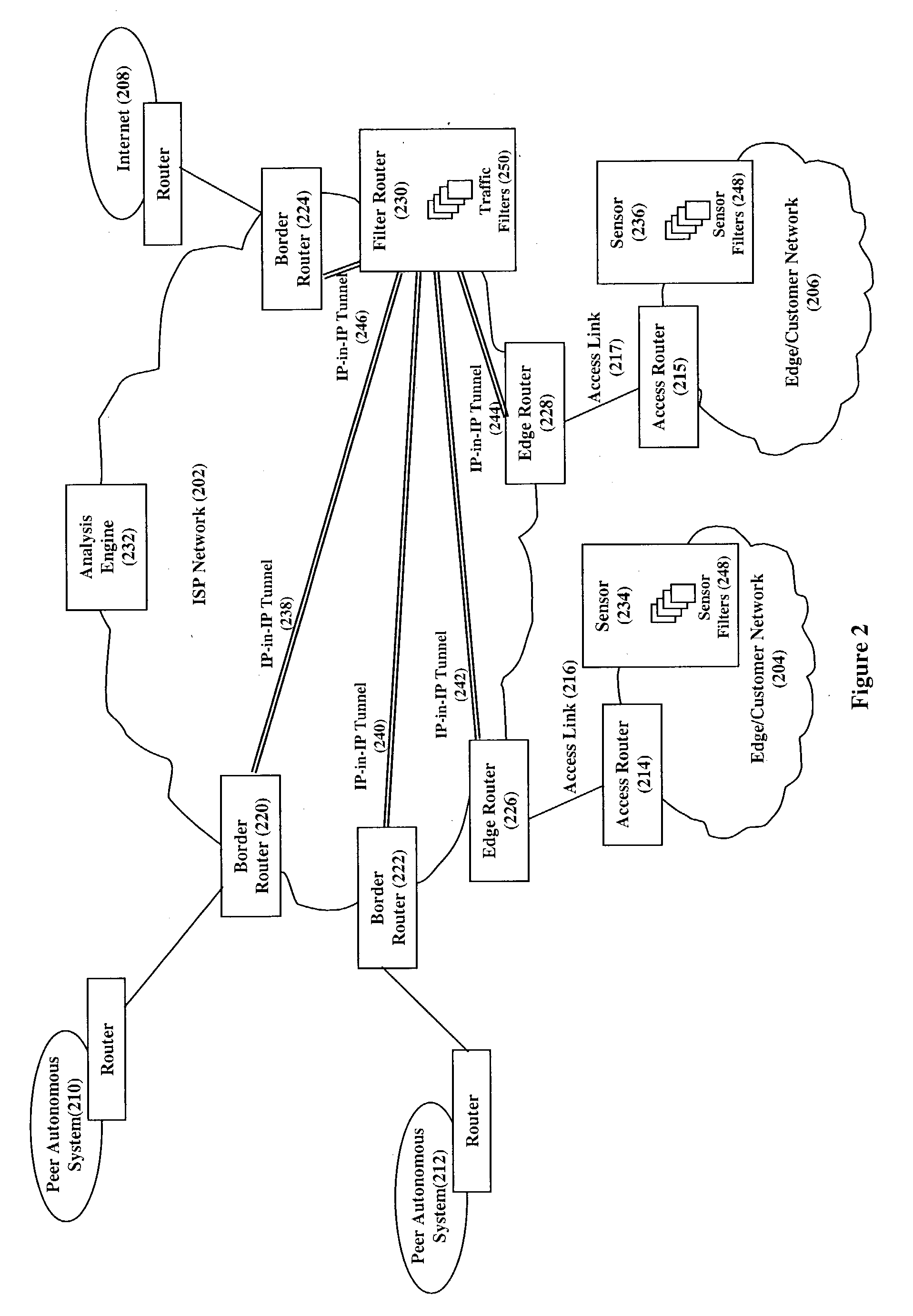
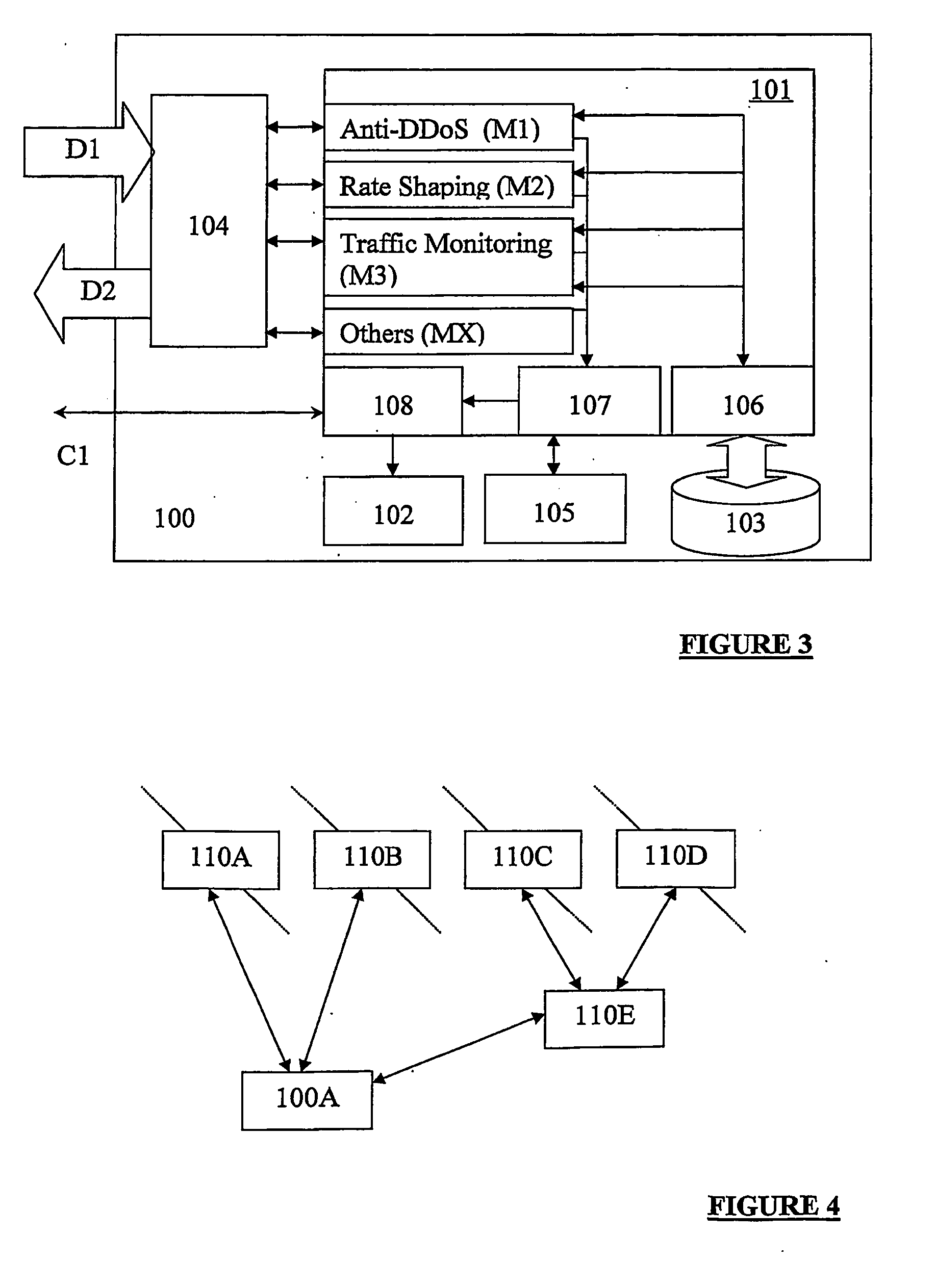
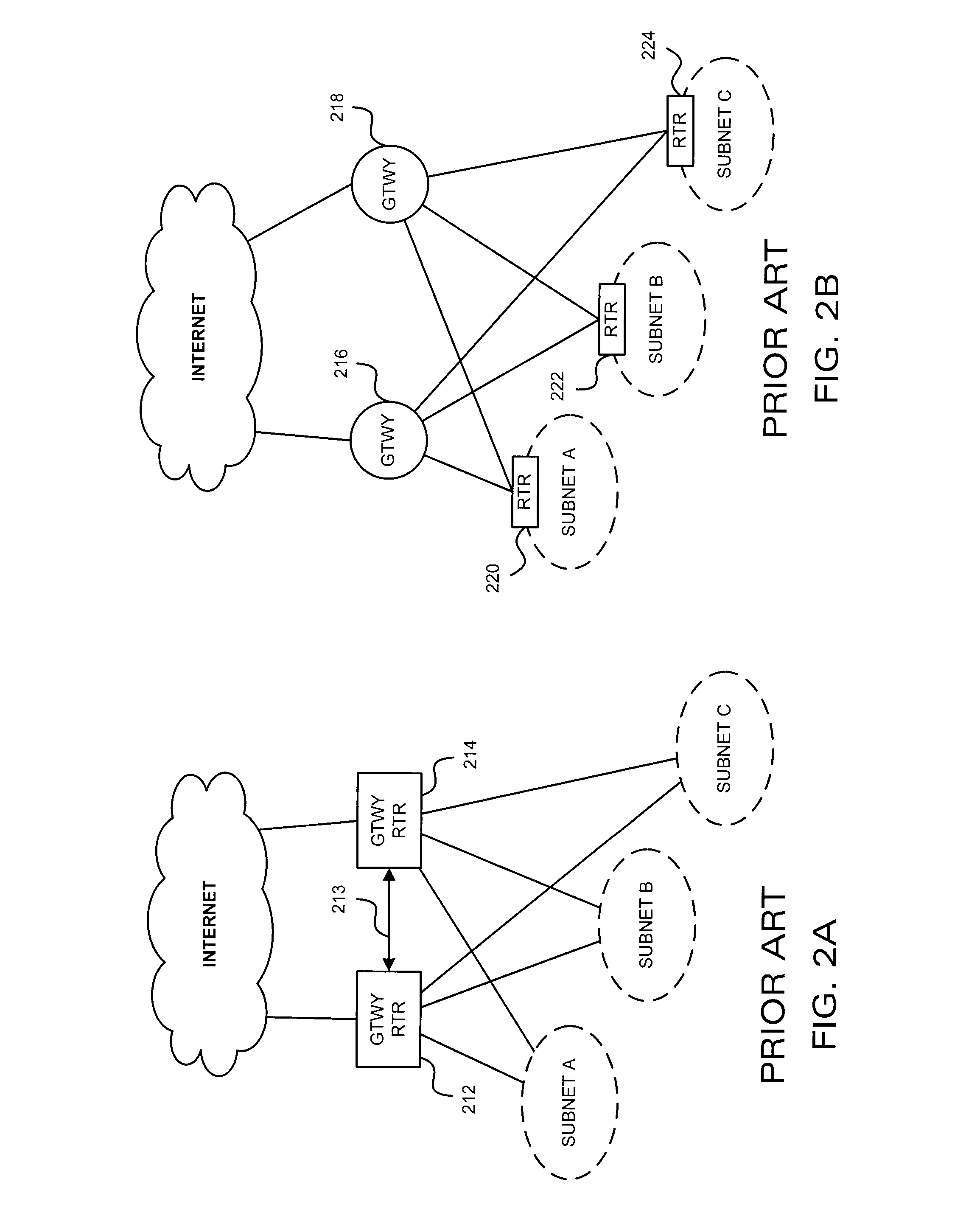
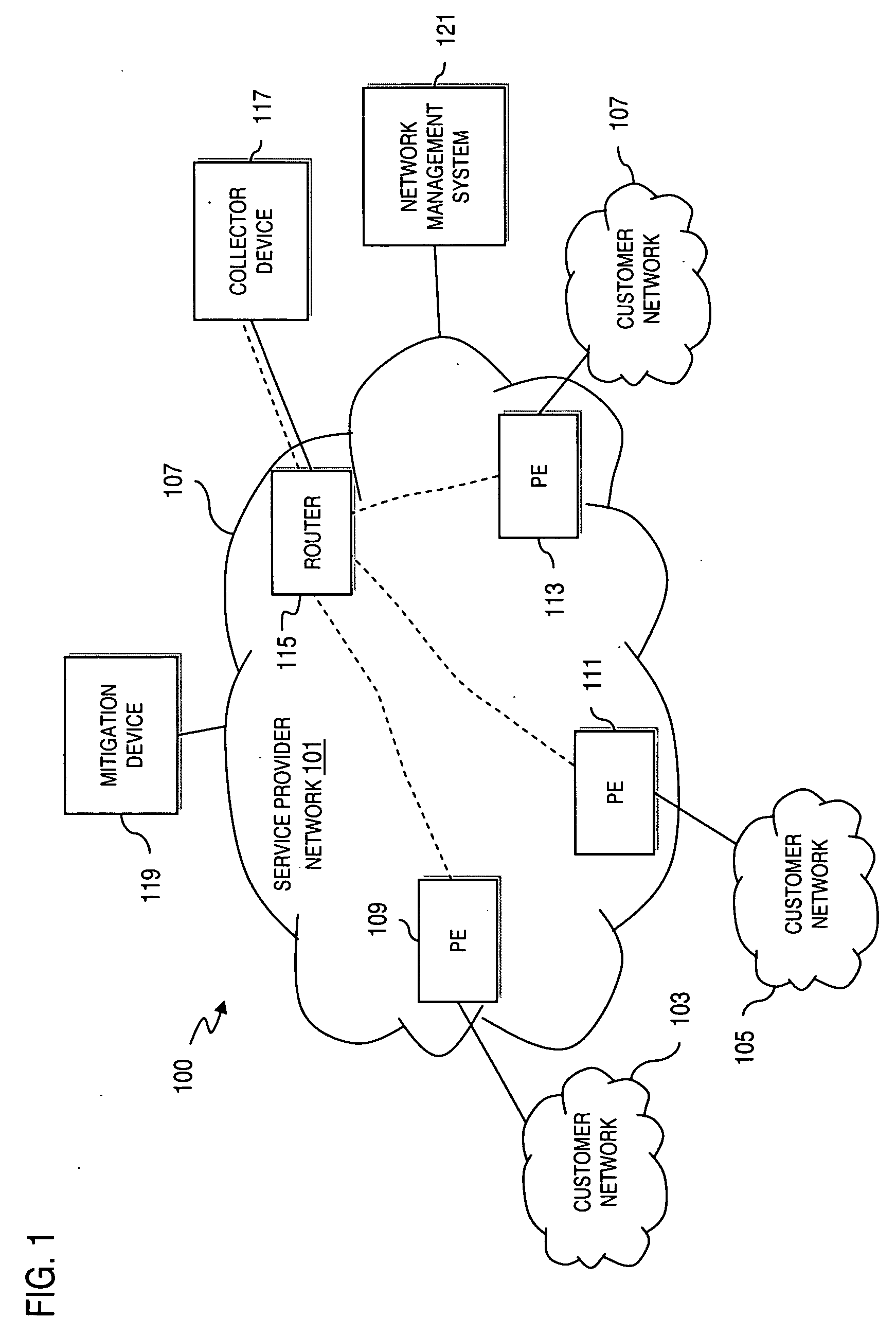
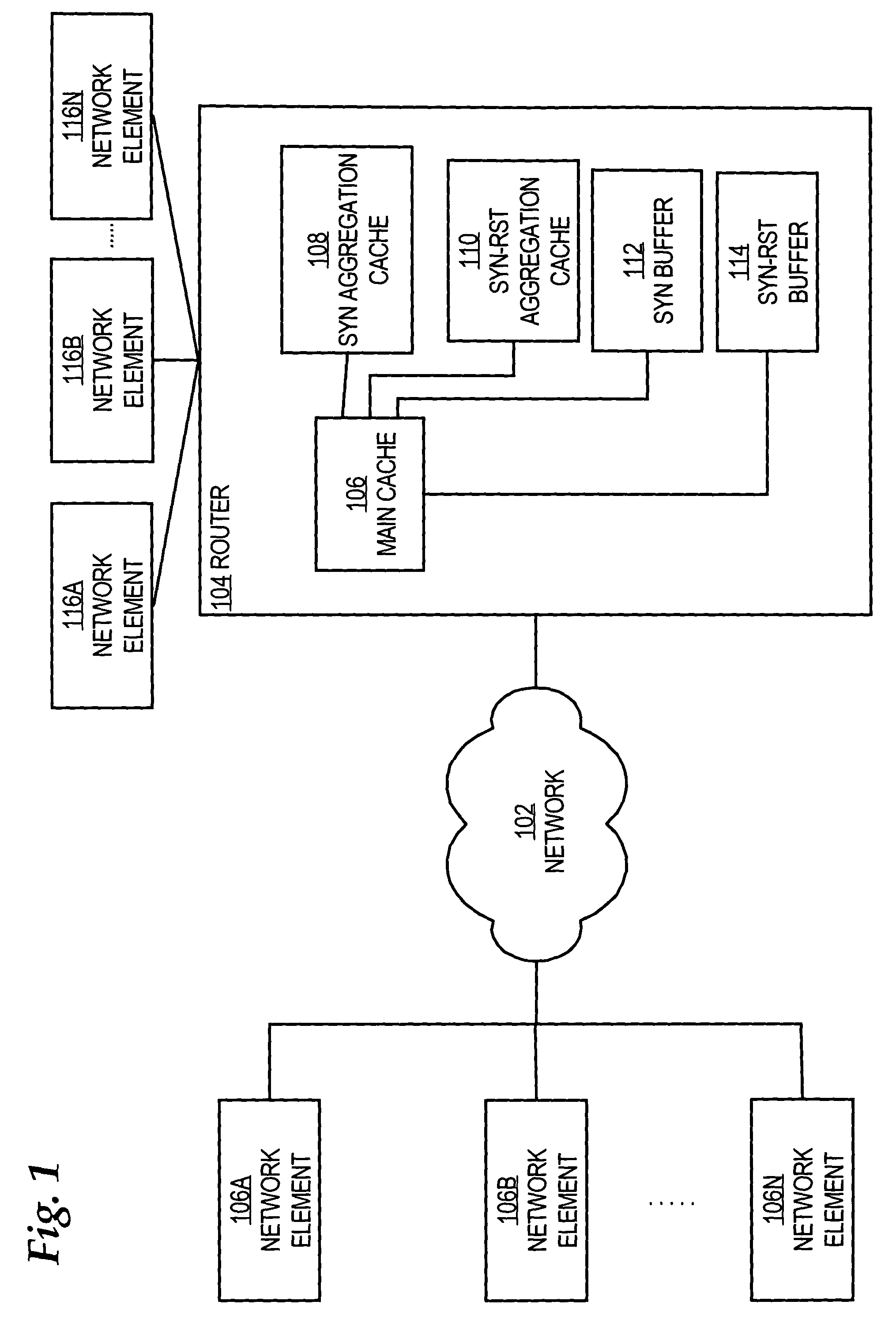
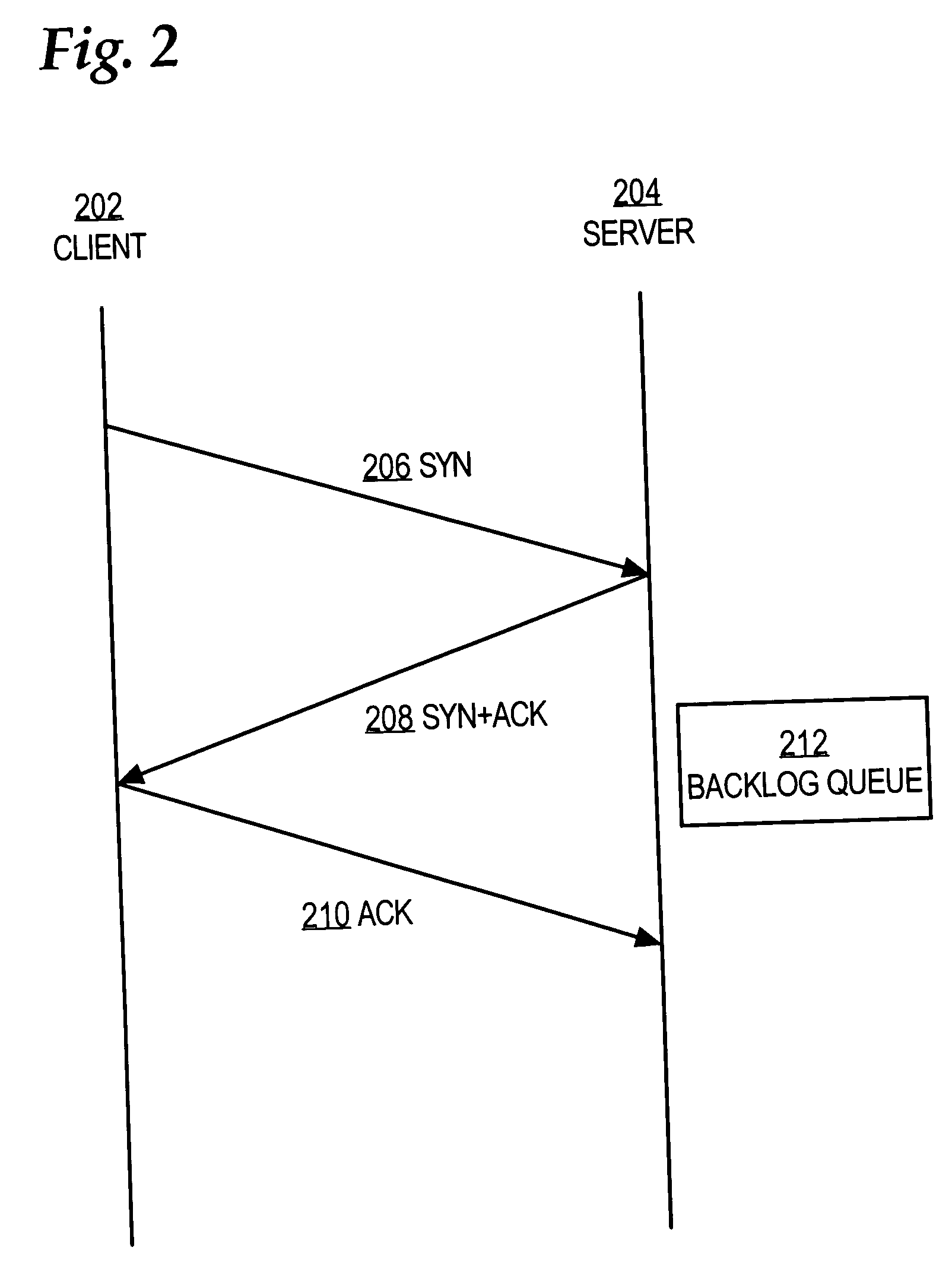
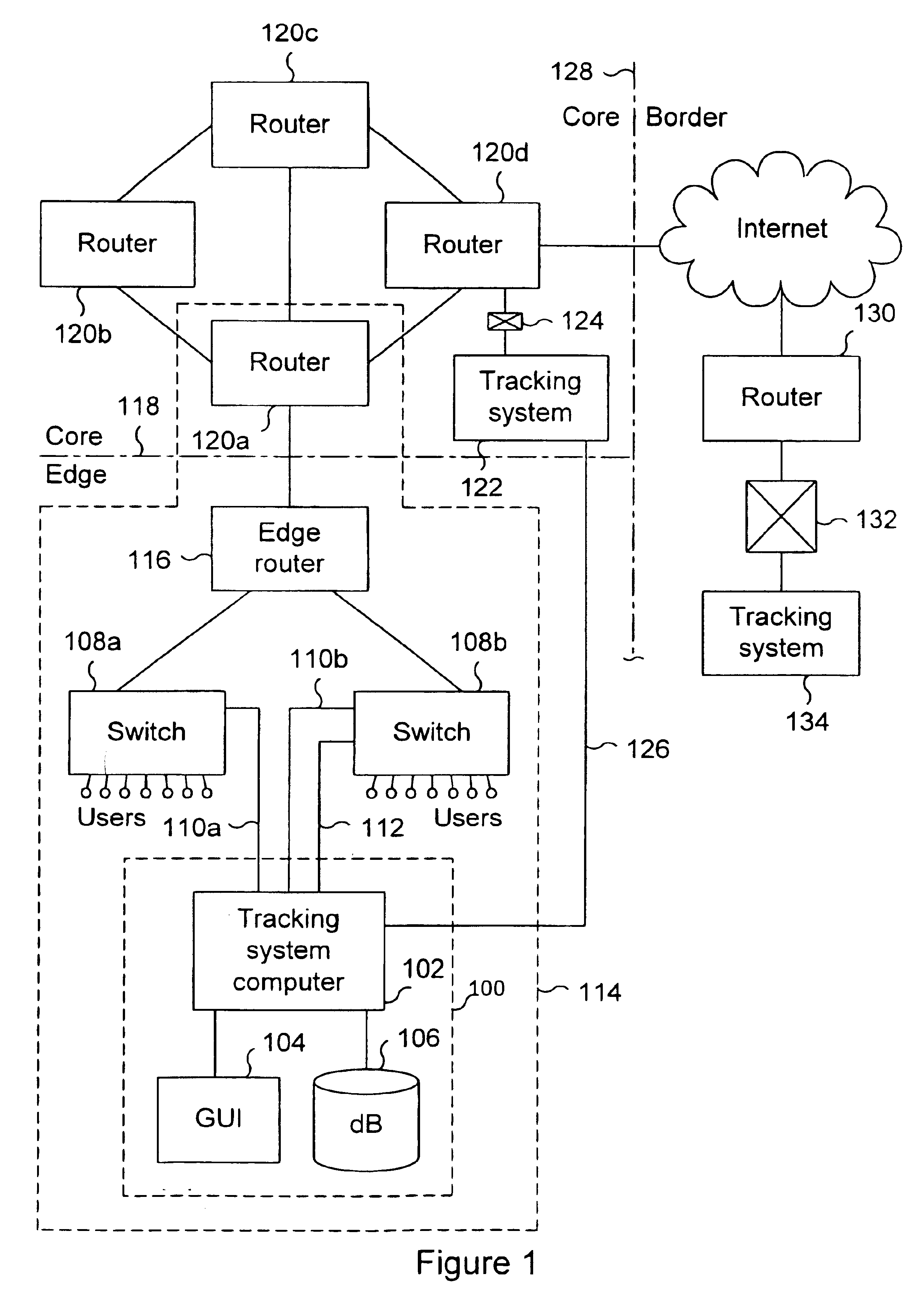
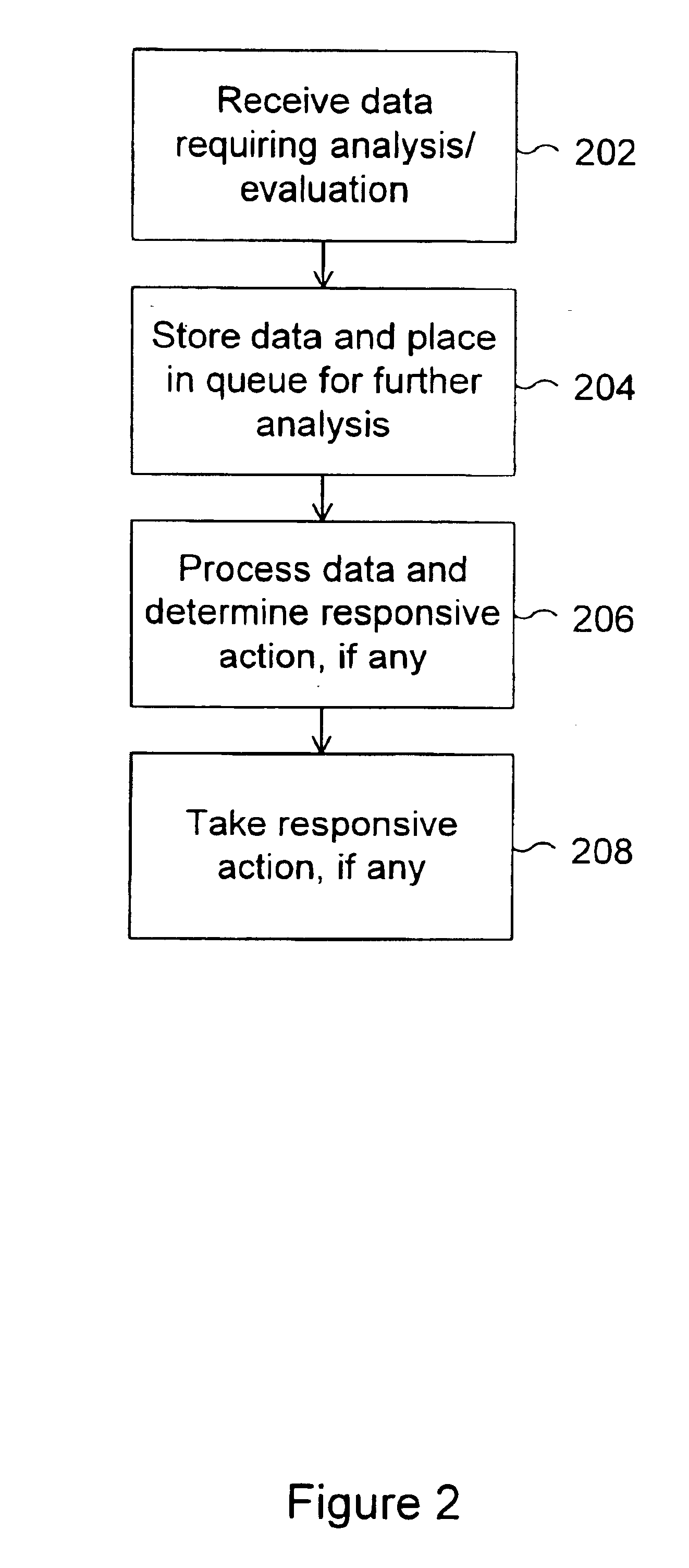
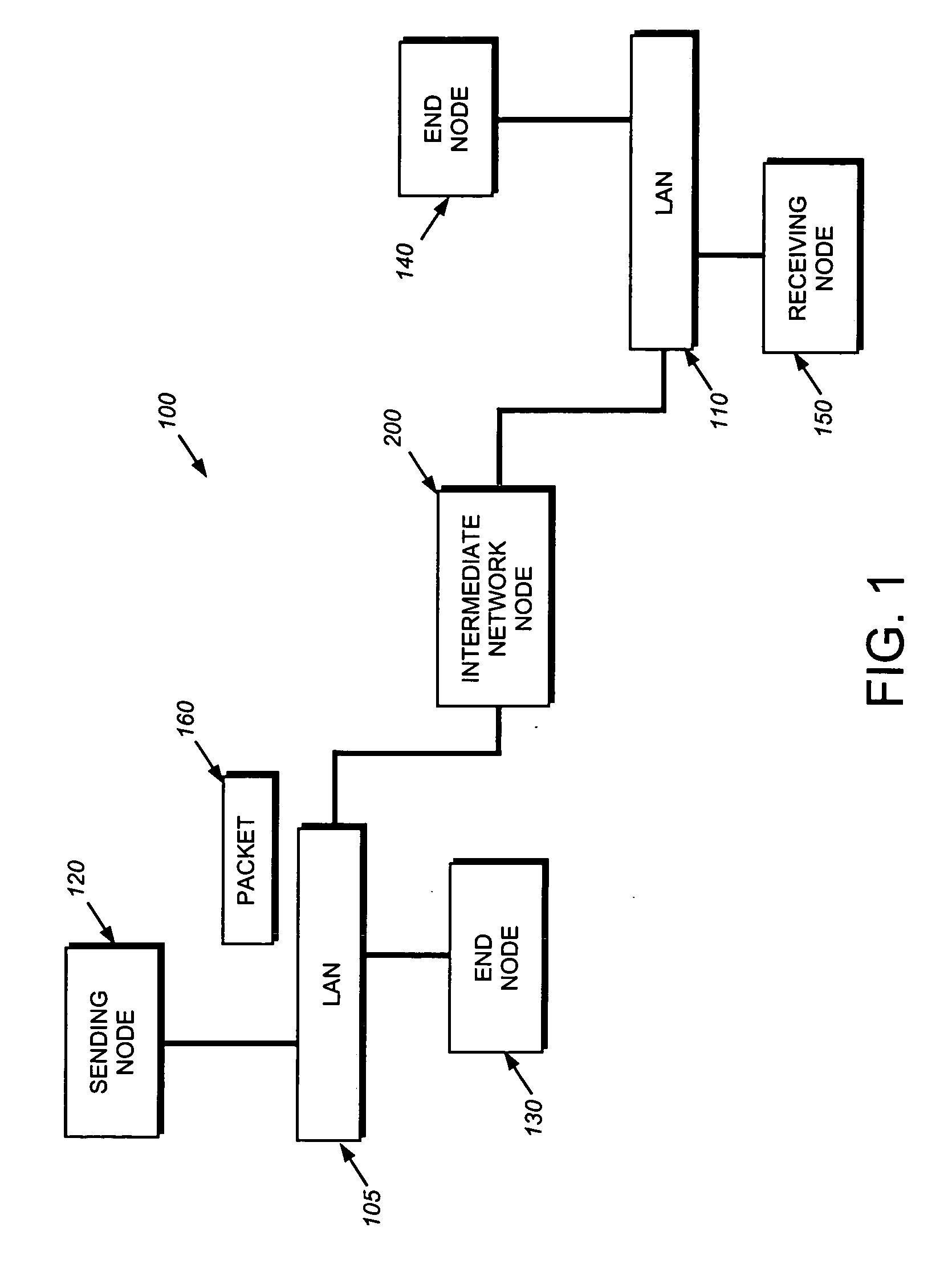
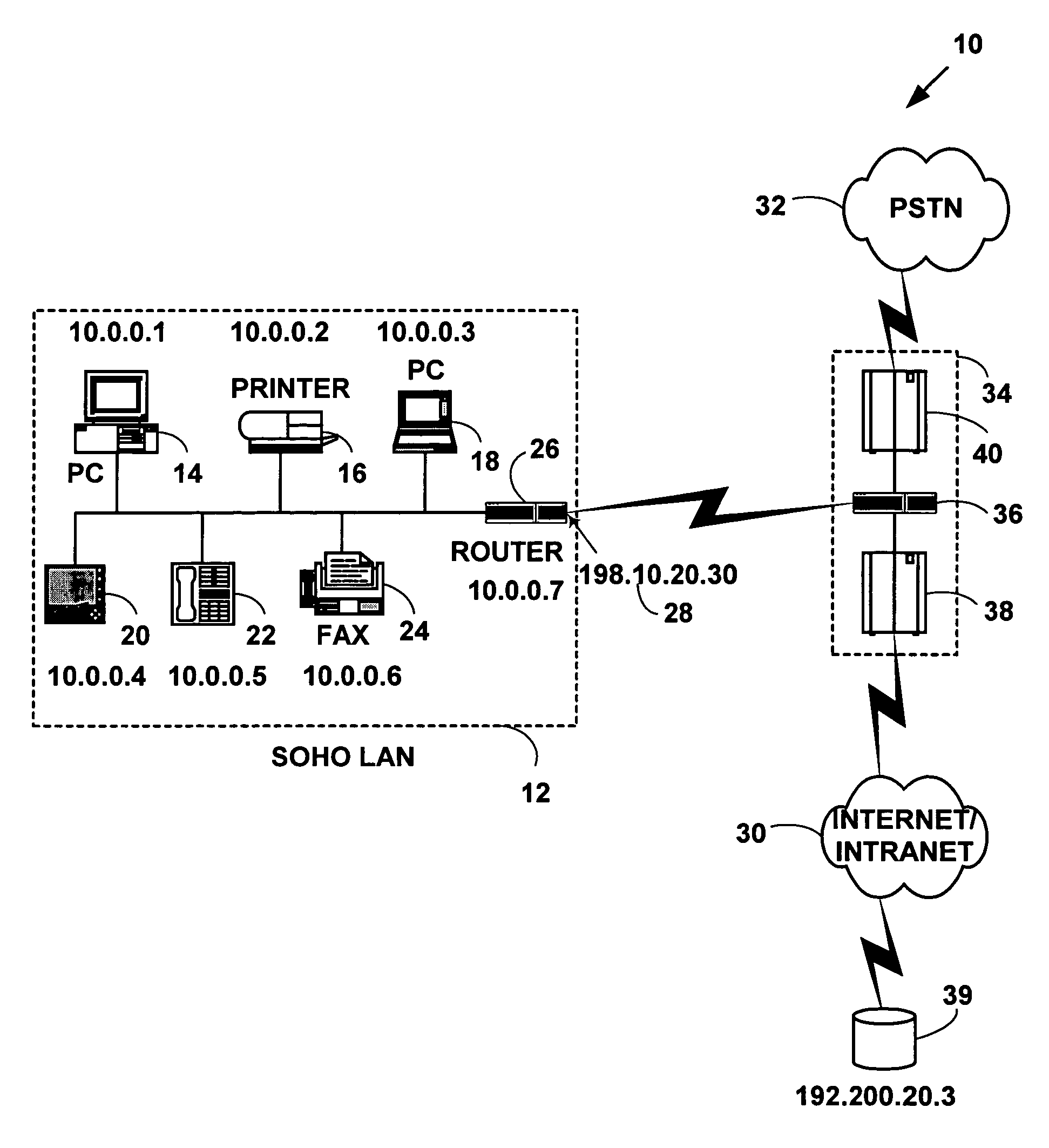
Service attacks, such as denial of service and distributed denial of service attacks, of a customer network are detected and subsequently mitigated by the Internet Service Provider (ISP) that services the customer network. A sensor examines the traffic entering the customer network for attack traffic. When an attack is detected, the sensor notifies an analysis engine within the ISP network to mitigate the attack. The analysis engine configures a filter router to advertise new routing information to the border and edge routers of the ISP network. The new routing information instructs the border and edge routers to reroute attack traffic and non-attack traffic destined for the customer network to the filter router. At the filter router, the attack traffic and non-attack traffic are automatically filtered to remove the attack traffic. The non-attack traffic is passed back onto the ISP network for routing towards the customer network.
Owner:TELCORDIA TECHNOLOGIES INC
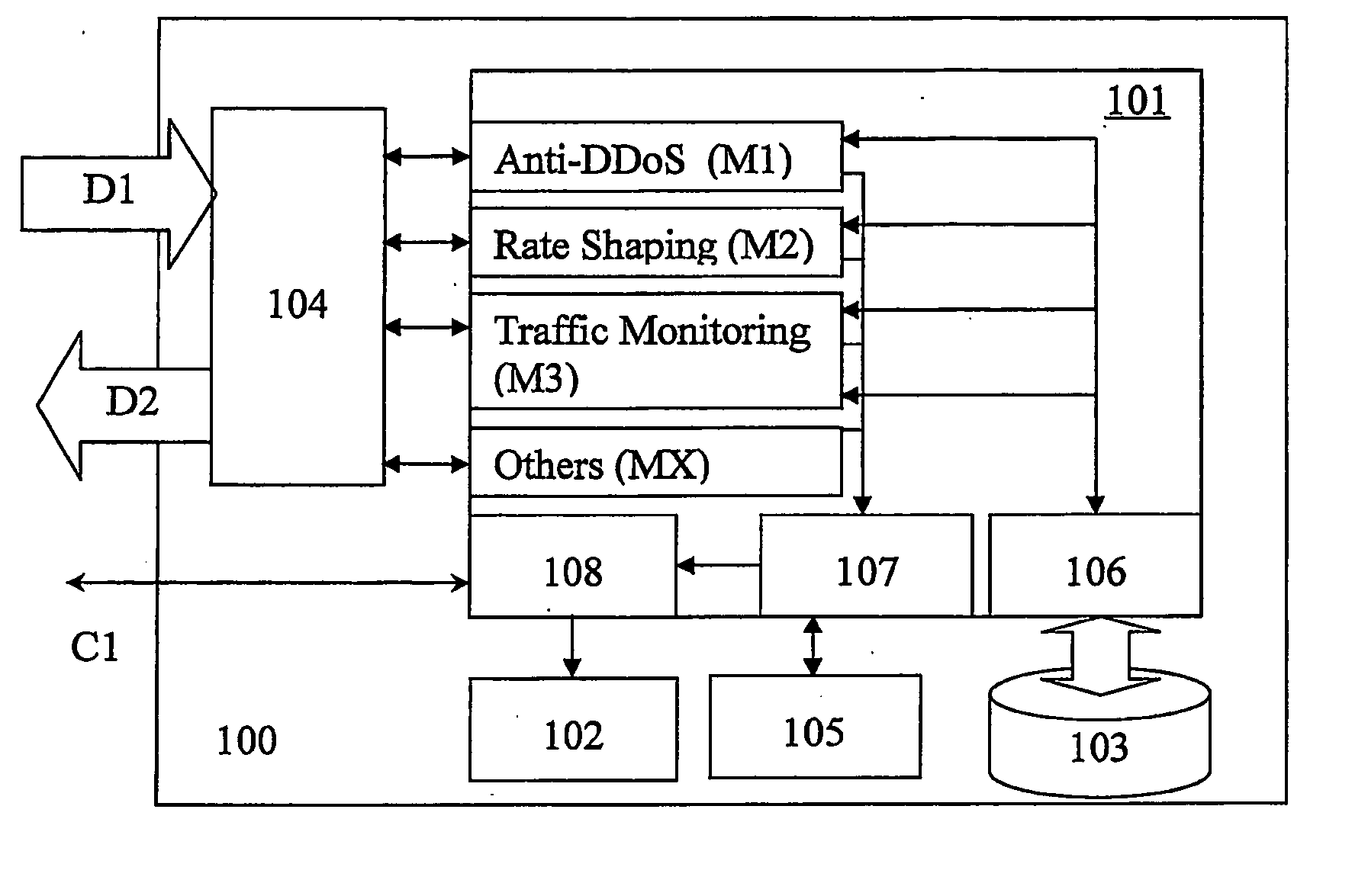
Method, apparatus and sofware for network traffic management
A network traffic evaluation device is provided that may be used to warn of or prevent trafficabnormalities such as denial of service attacks. The device includes a data interface to receive one or both of network traffic and data indicative of characteristics f network traffic. The network traffic and / or data received by the data interface is processed for predeterminedcharacteristics that indicate that the network traffic contains a subset of attack traffic. Upon detection of the predetermined characteristics information defining a superset is provided. The superset is a portion of the network traffic that contains the subset and defines network traffic that may be redirected and / or blocked by a network device.
Owner:ESPHION
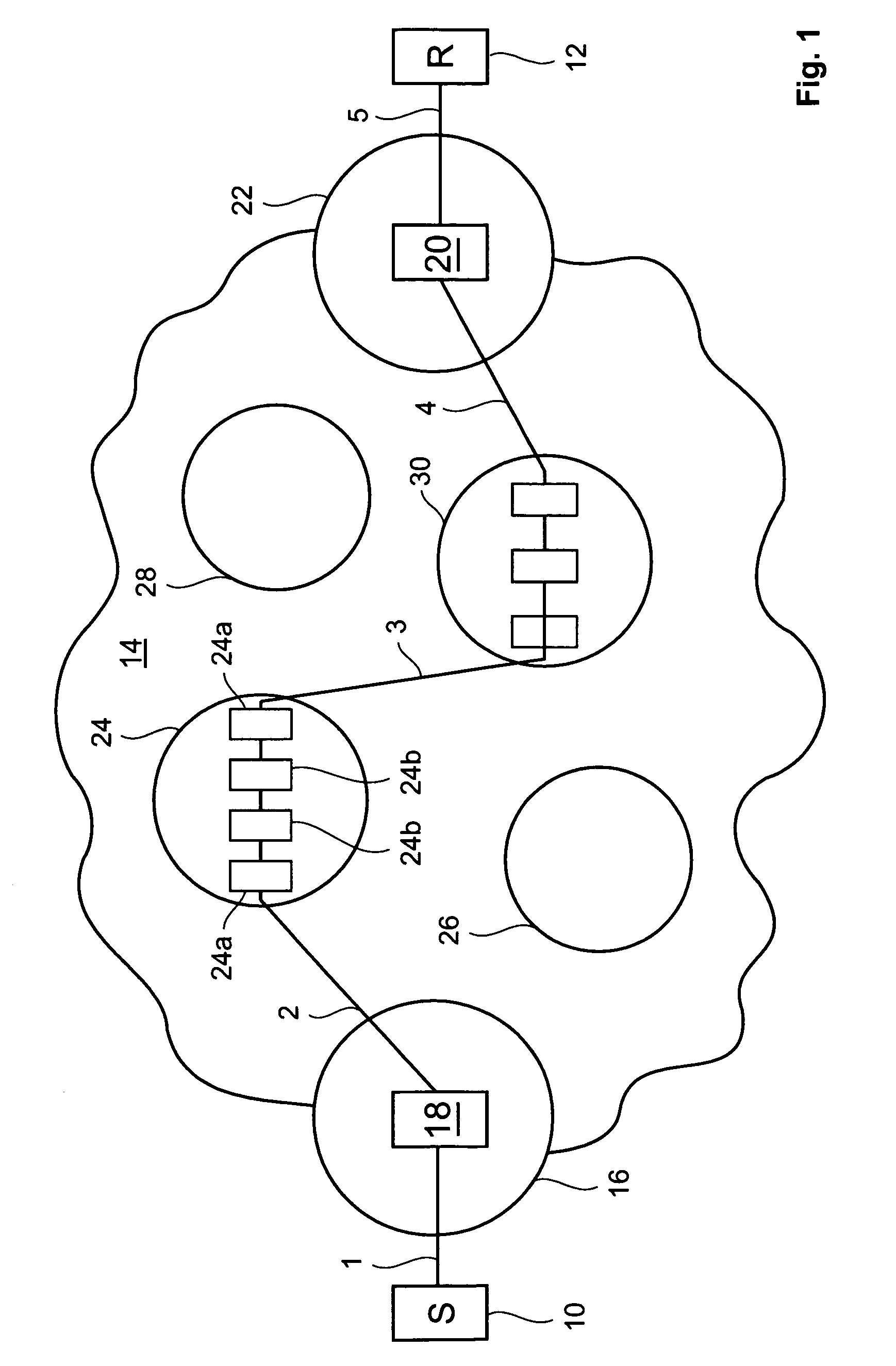
Detection of Distributed Denial of Service Attacks in Autonomous System Domains
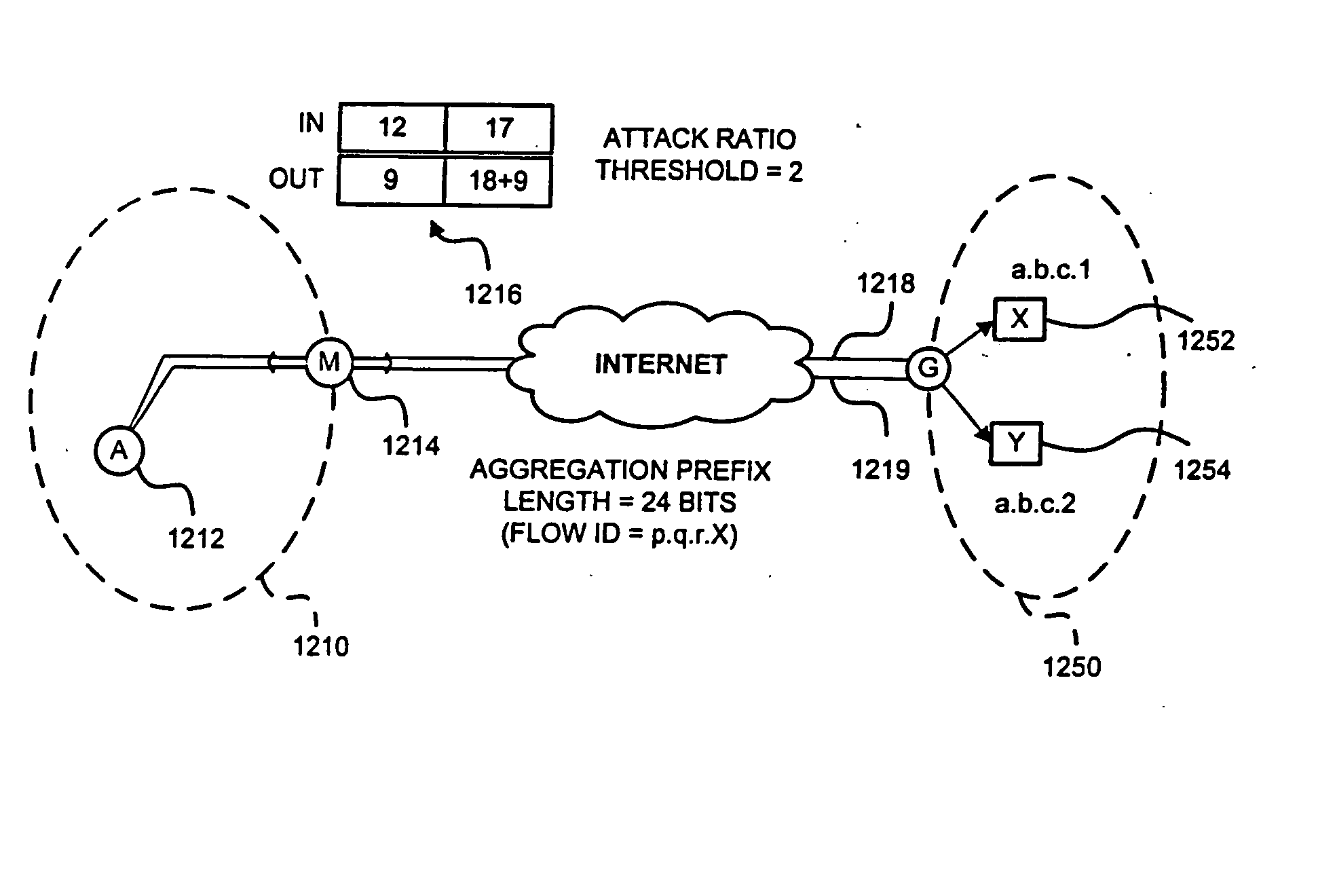
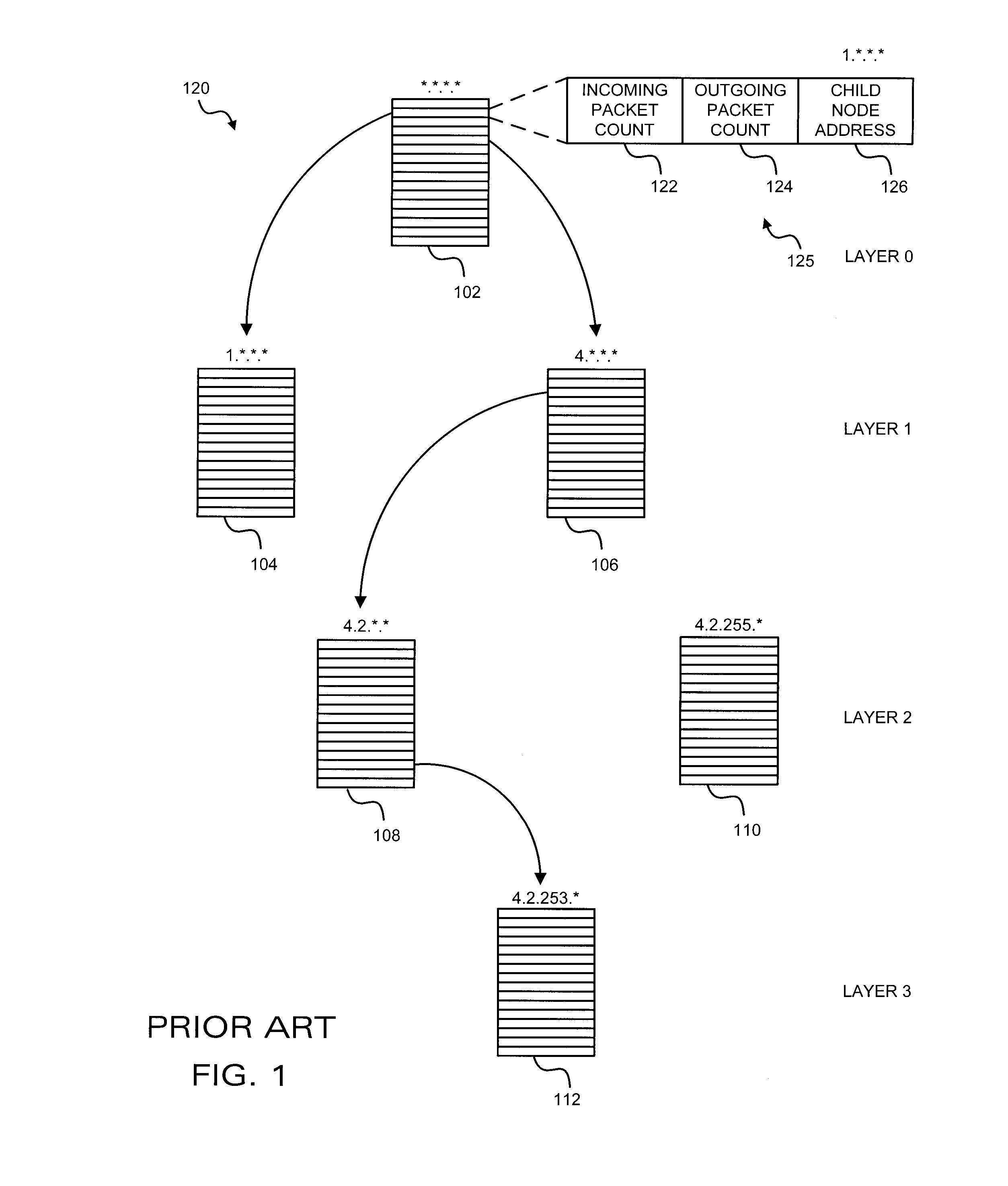
A denial-of-service network attack detection system is deployable in single-homed and multi-homed stub networks. The detection system maintains state information of flows entering and leaving the stub domain to determine if exiting traffic exceeds traffic entering the system. Monitors perform simple processing tasks on sampled packets at individual routers in the network at line speed and perform more intensive processing at the routers periodically. The monitors at the routers form an overlay network and communicate pertinent traffic state information between nodes. The state information is collected and analyzed to determine the presence of an attack.
Owner:MARYLAND UNIV OF
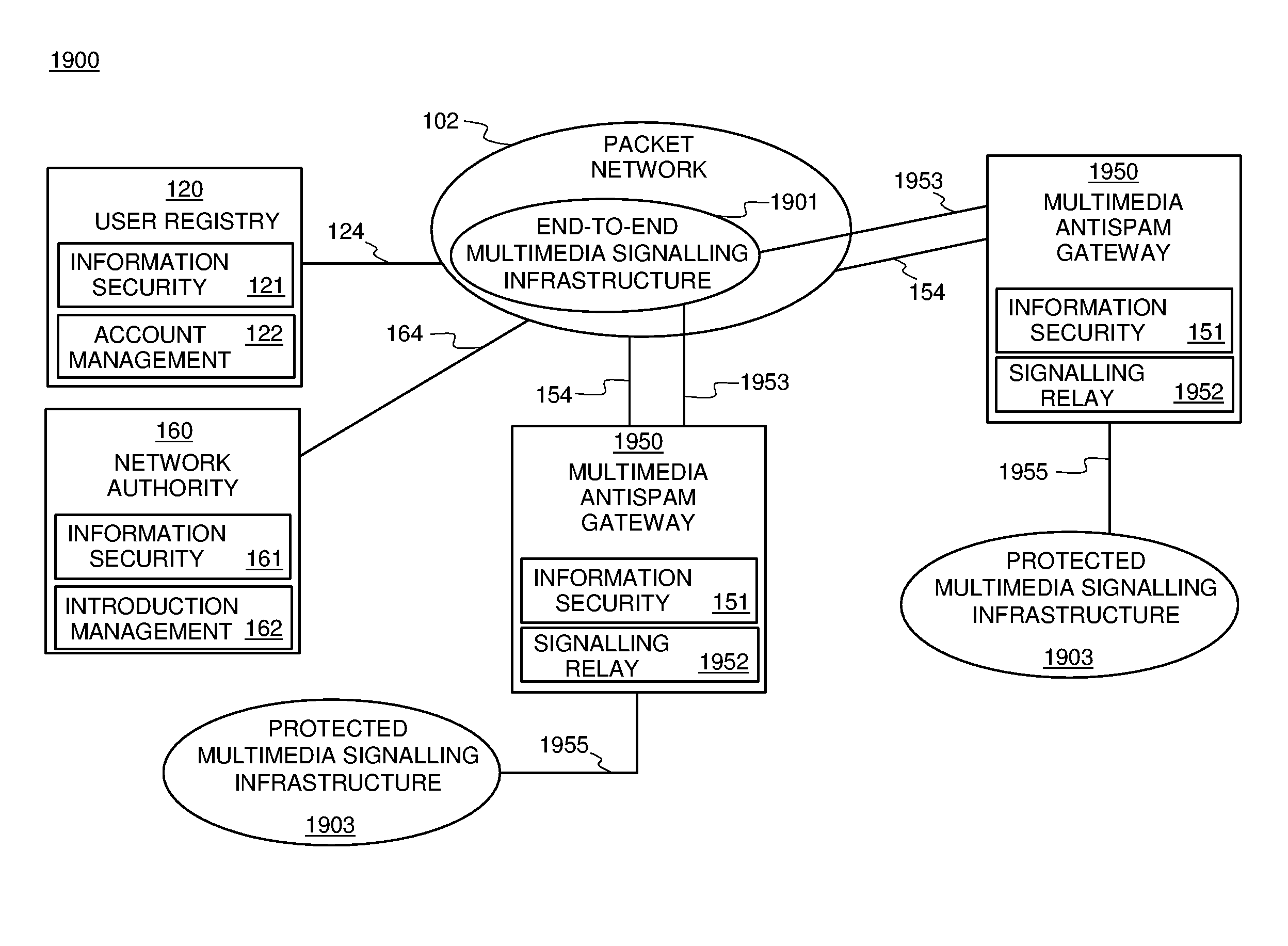
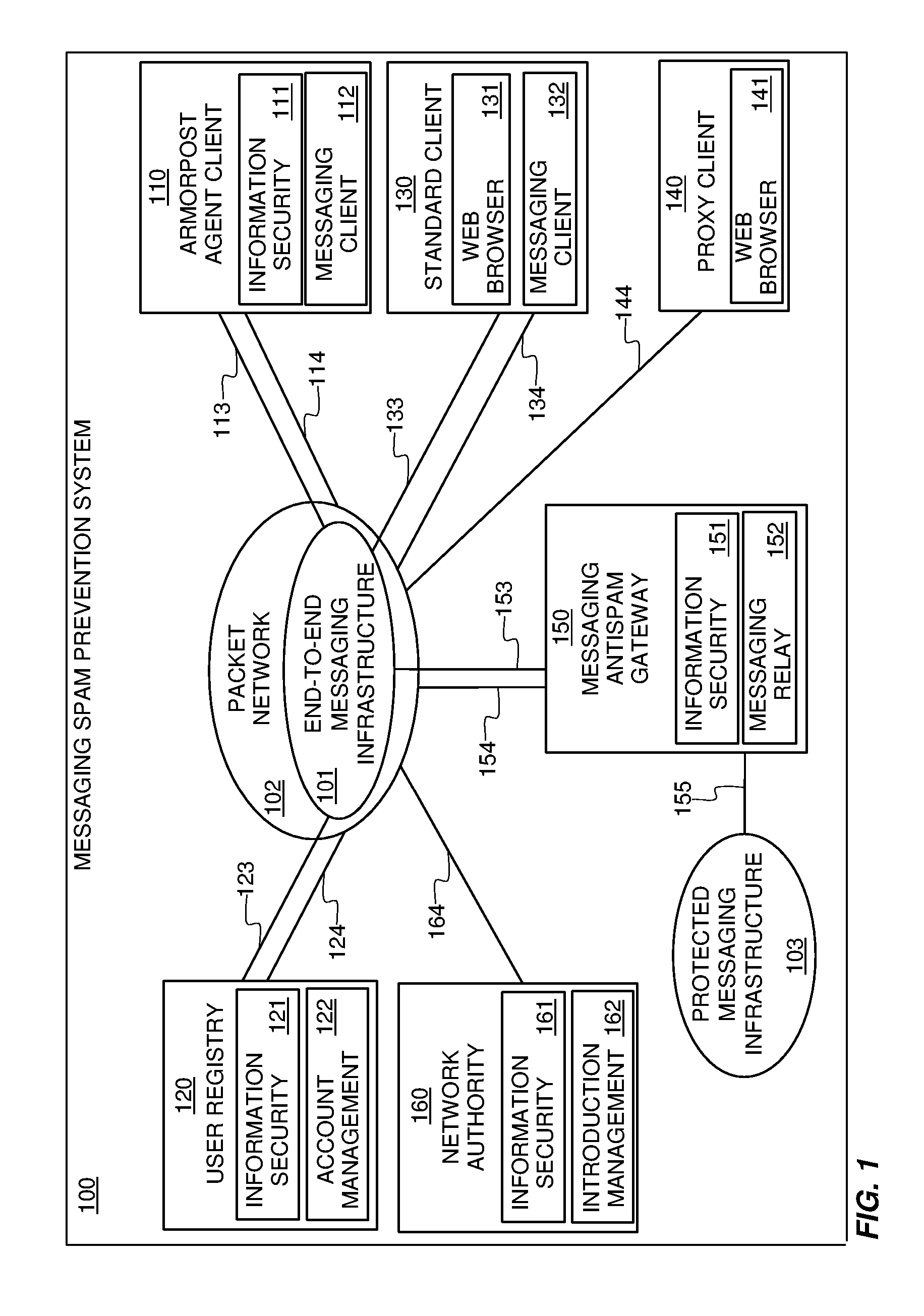
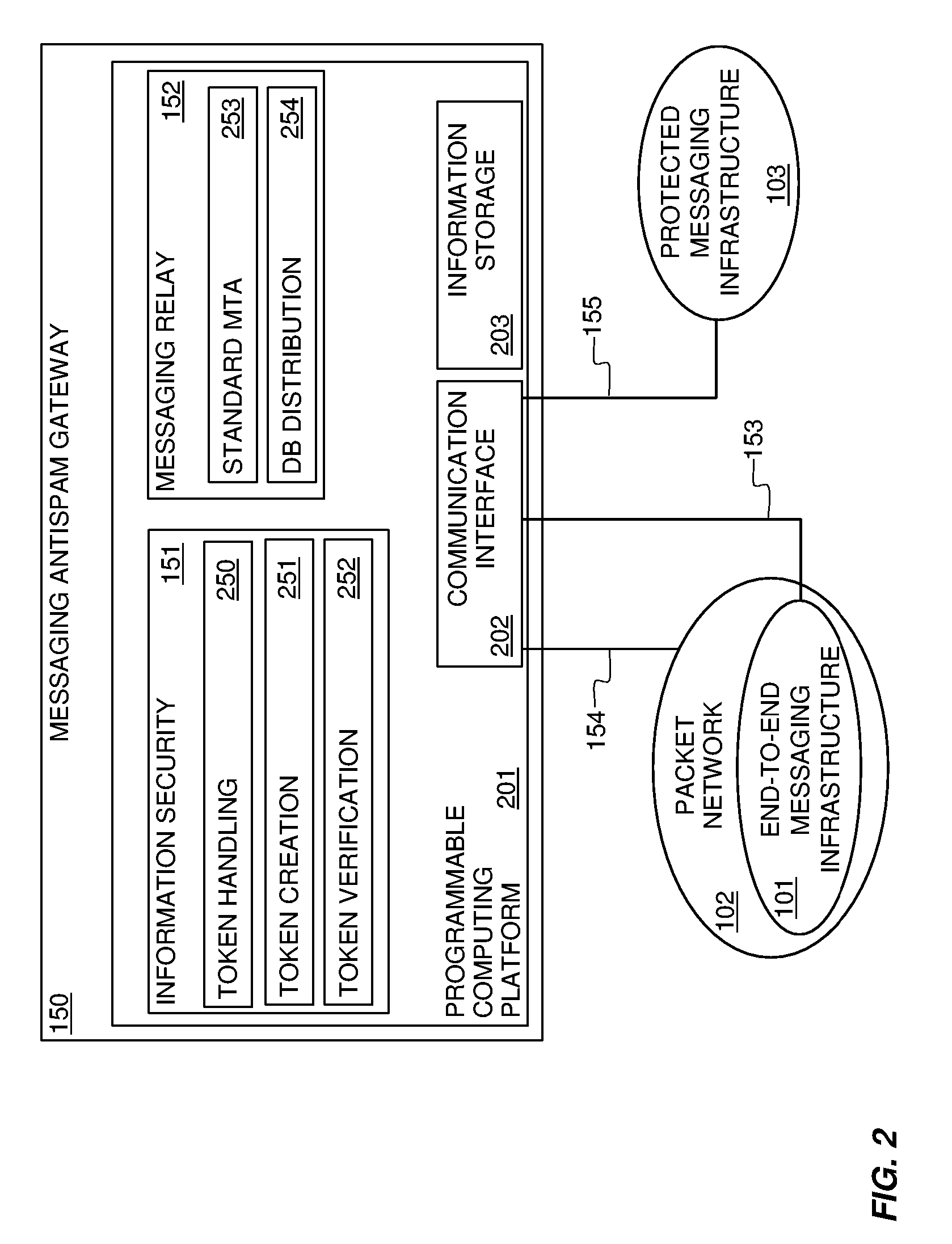
Systems and methods for preventing spam and denial of service attacks in messaging, packet multimedia, and other networks
InactiveUS20050132060A1Low costRaise priorityMultiple digital computer combinationsData switching networksData packSpamming
A system, various methods, and various apparatuses are provided for the purpose of supplying and including in an electronic message or multimedia session signalling unit a valid cryptographic authentication token, verifying said token's validity upon arrival of said message or signalling unit, and thereby providing message recipients or session parties with the assurance that said message or signalling unit is from a valid sender. A system, apparatus, and various methods are further provided for the purpose of protecting legitimate application traffic and the network elements exchanging it from intrusion by wild packets attempting to consume application resources and thereby deny service to legitimate users or network elements. A system, various methods, and various apparatuses are further provided for the purpose of enabling legitimate advertising via electronic messages, relying upon message and sender authentication to assure both advertisers and viewers of advertising messages that all participants are valid, legitimate, and accountable for any abuse that may occur.
Owner:AUTOUPTODATE LLC
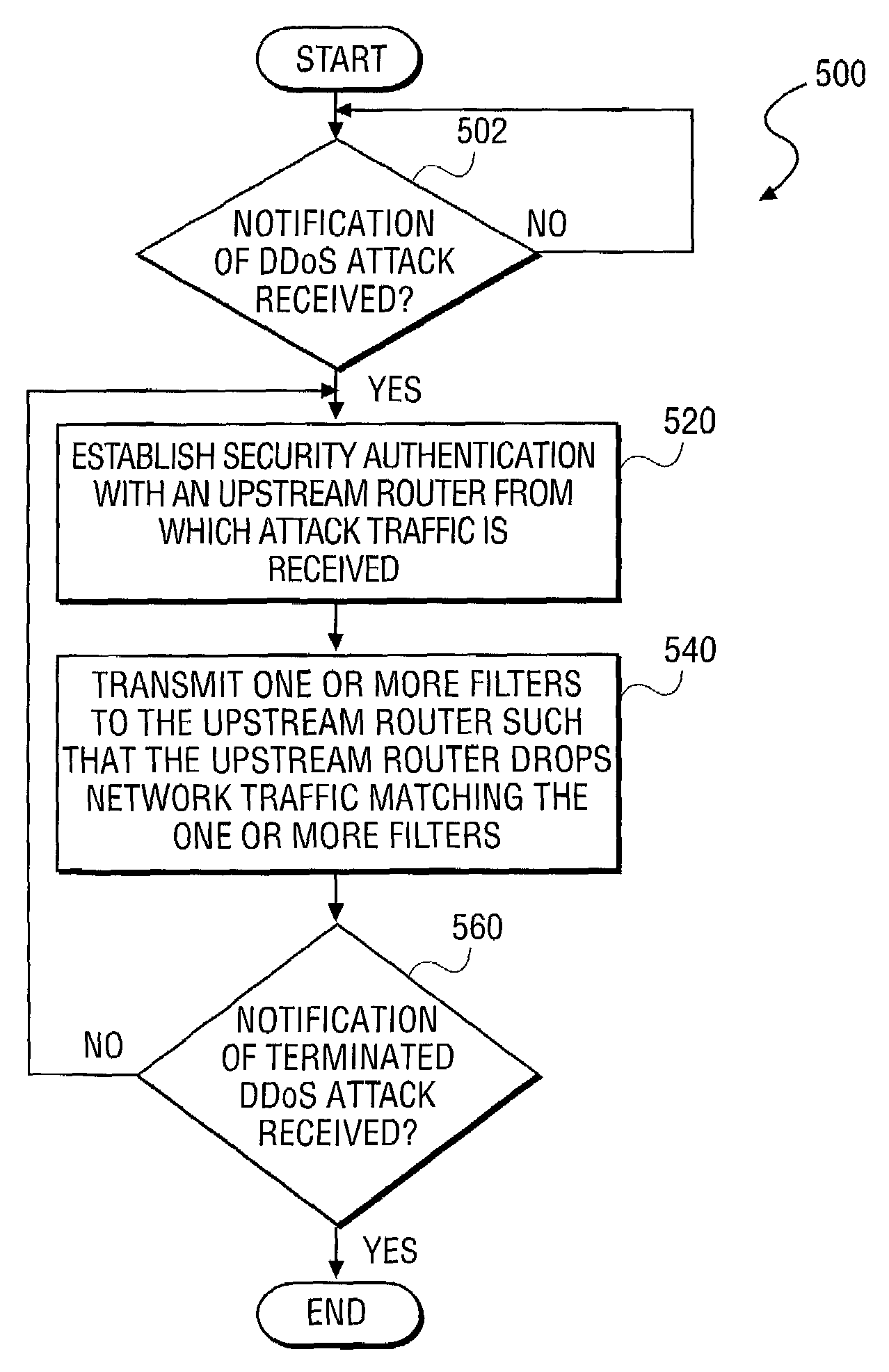
Apparatus and method for secure, automated response to distributed denial of service attacks
InactiveUS7028179B2Memory loss protectionError detection/correctionThe InternetSecurity authentication
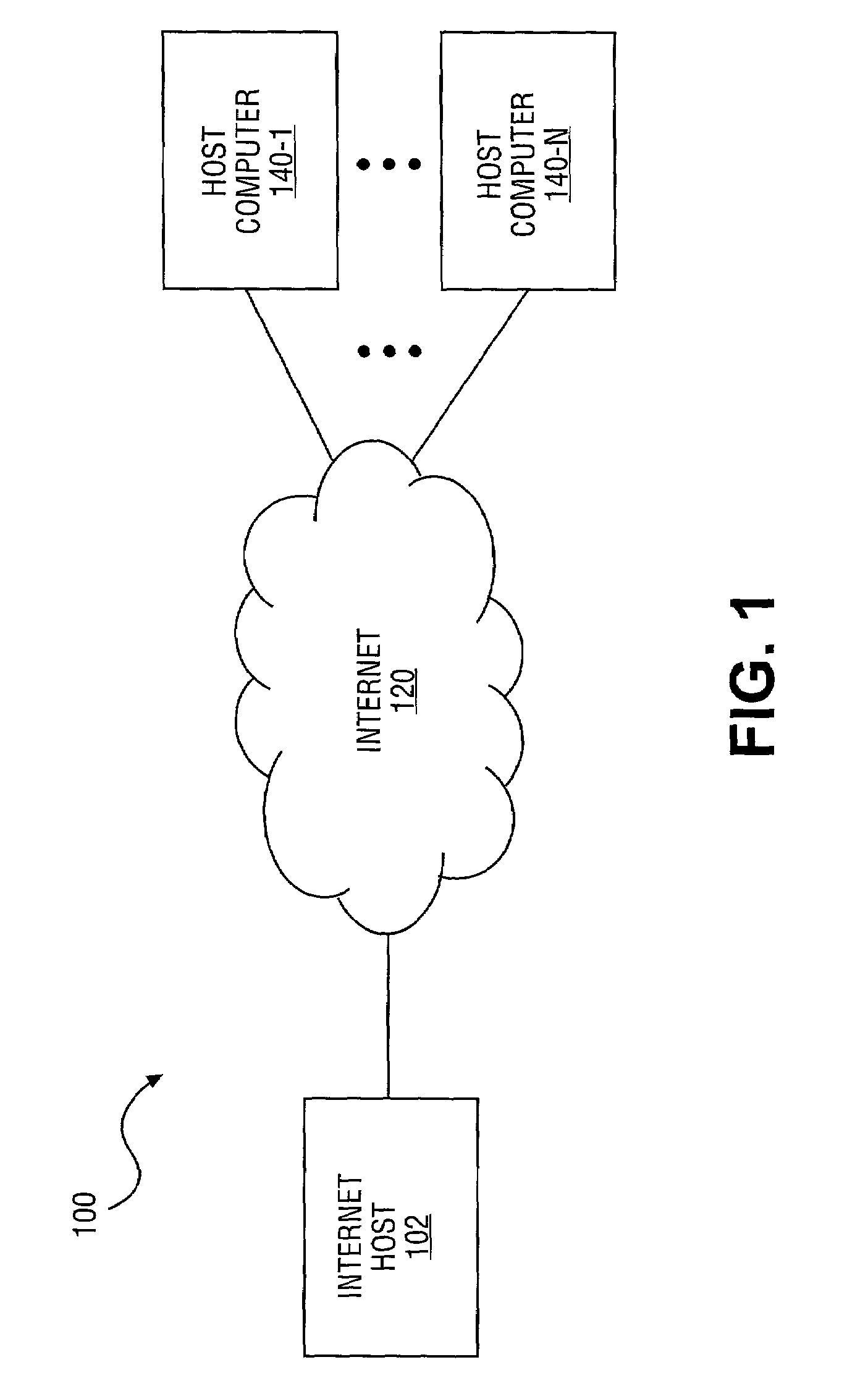
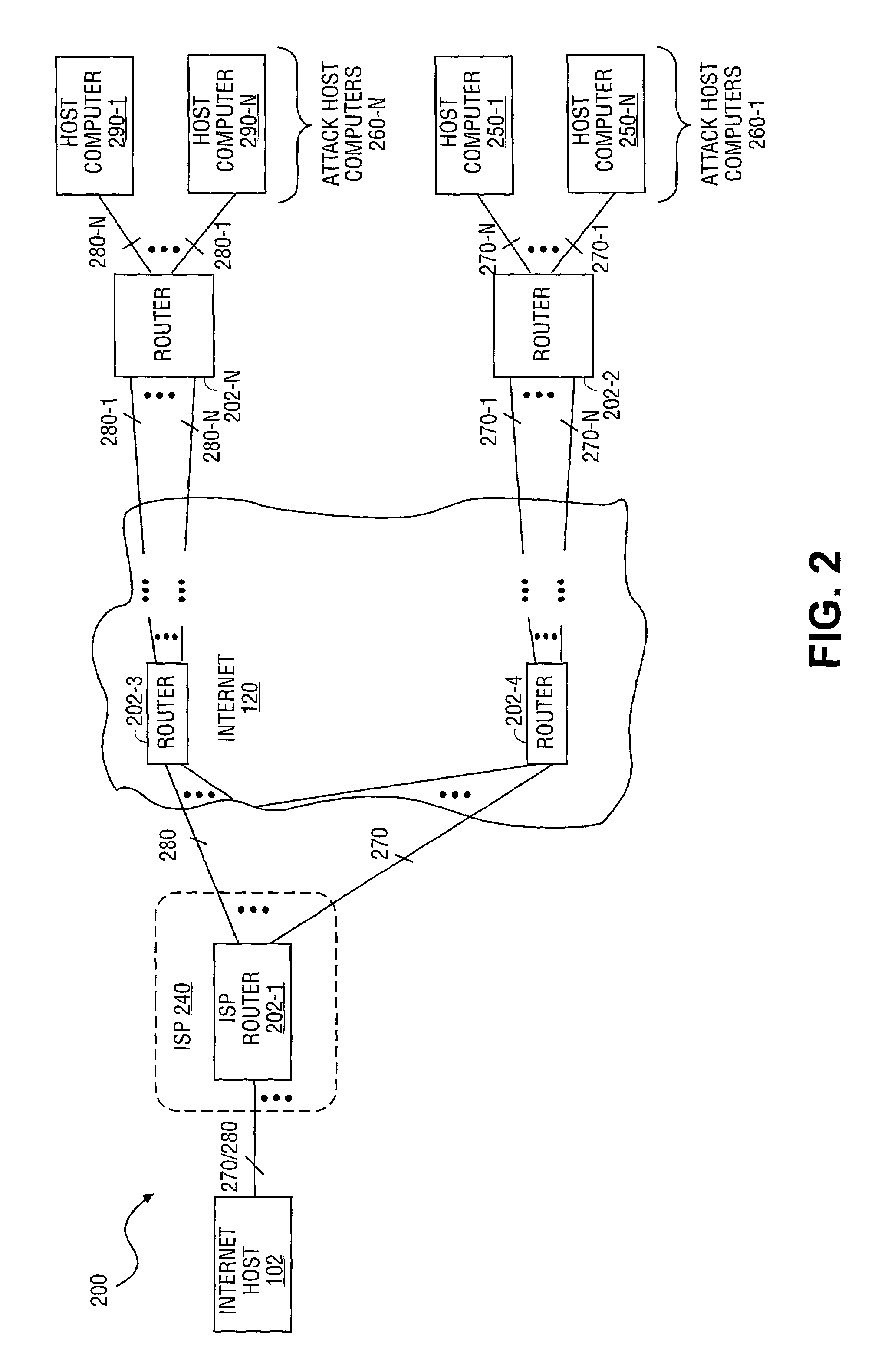
An apparatus and method for secure, automated response to distributed denial of service (DDoS) attacks are described. The method includes notification of a DDoS attack received by an Internet host. Once received by an Internet host, the Internet host establishes security authentication from an upstream router from which the attack traffic, transmitted by one or more host computers, is received. The Internet host then transmits filter(s) to the upstream router generated based upon characteristics of the attack traffic. Once installed by the upstream router, the attack traffic is dropped to terminate a DDoS attack. In addition, the router may determine upstream router(s) coupled to ports from which attack traffic is received, and securely forward the filter(s) to the upstream routers as a routing protocol updated in order to drop the attack traffic at a point closer to a source of the DDoS attack.
Owner:INTEL CORP
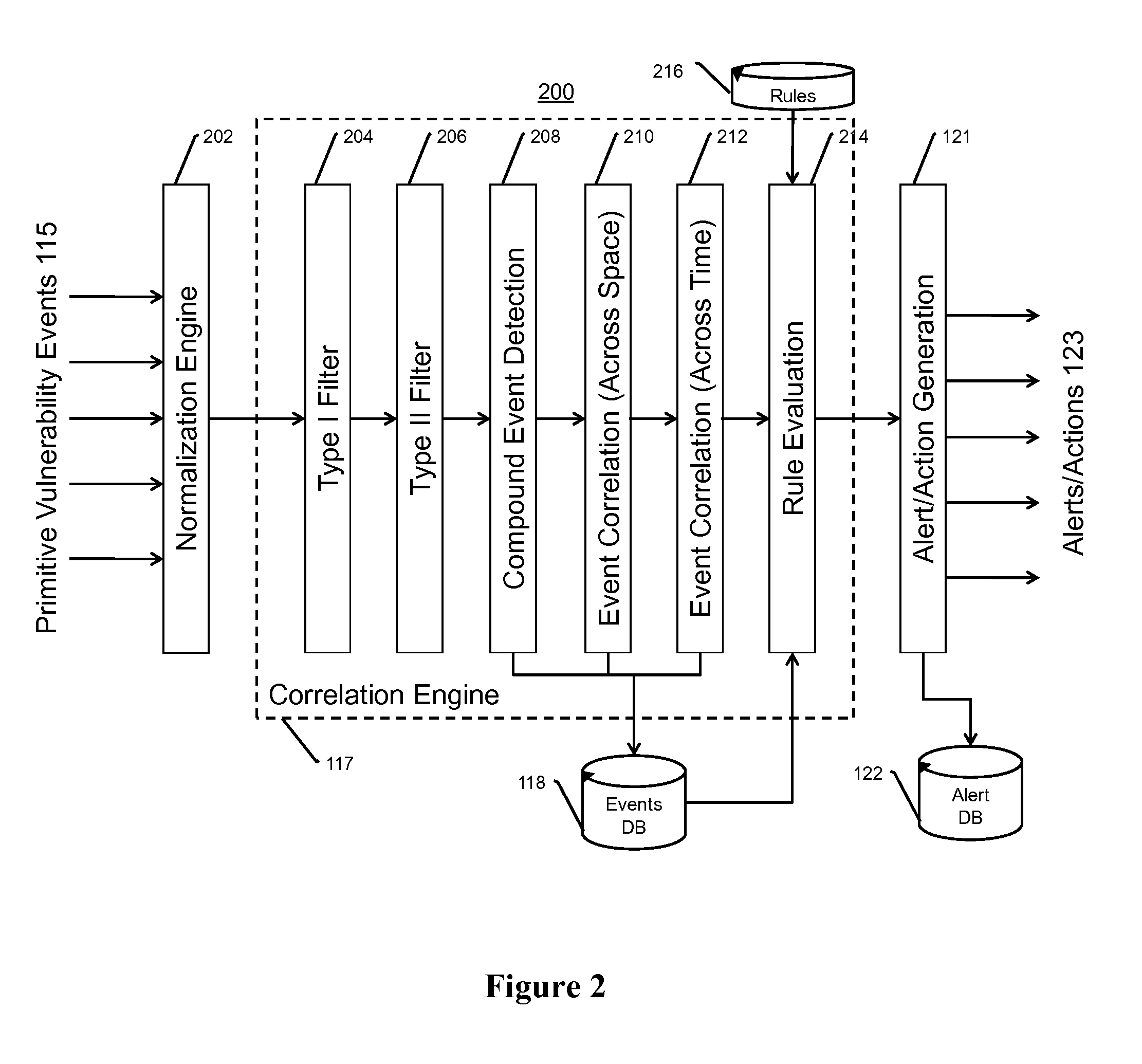
Systems, methods, and devices for detecting security vulnerabilities in IP networks
InactiveUS20100262688A1Detect and prevent spoofingEasy to addMemory loss protectionDigital data processing detailsBaseline dataData stream
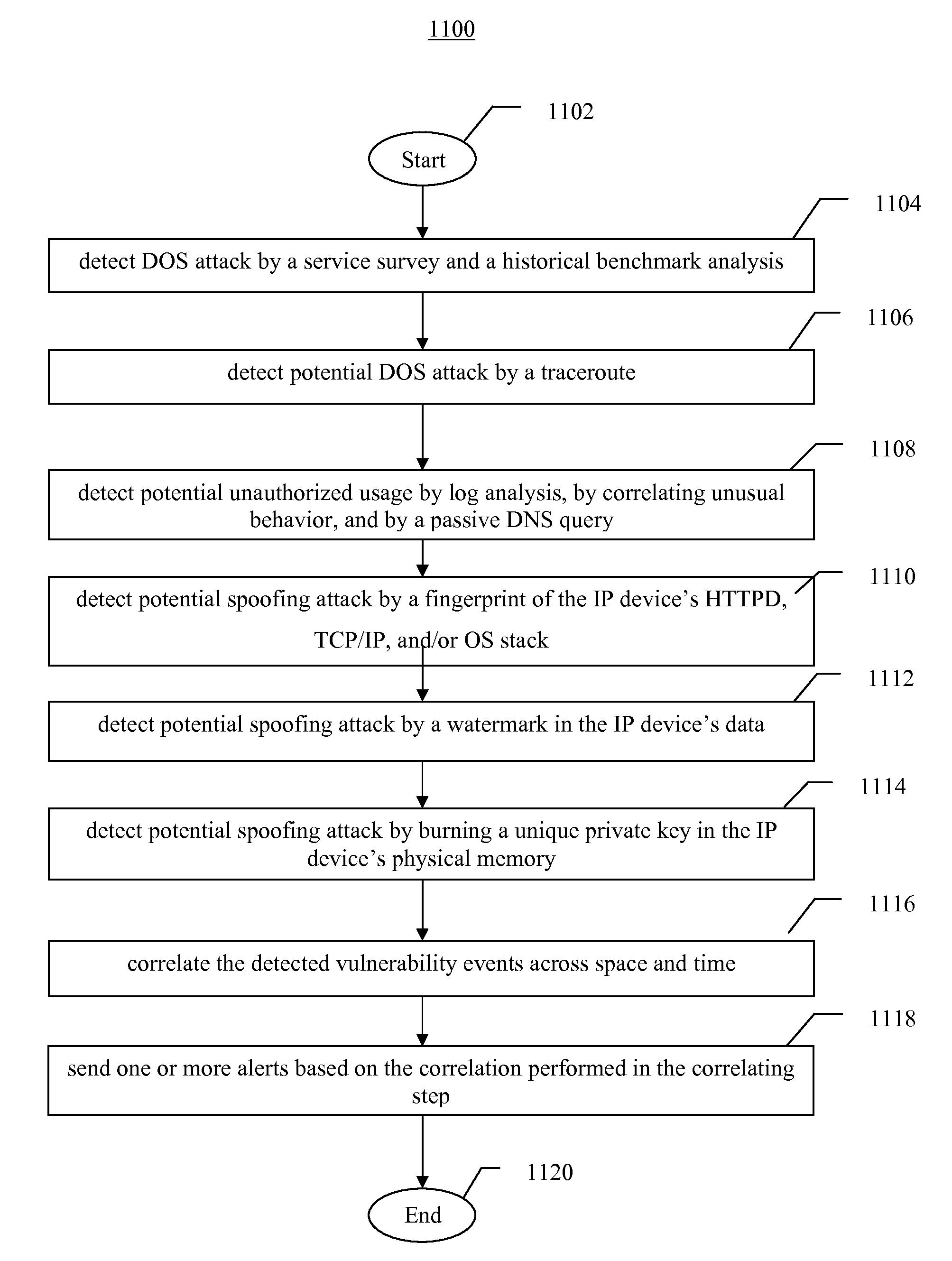
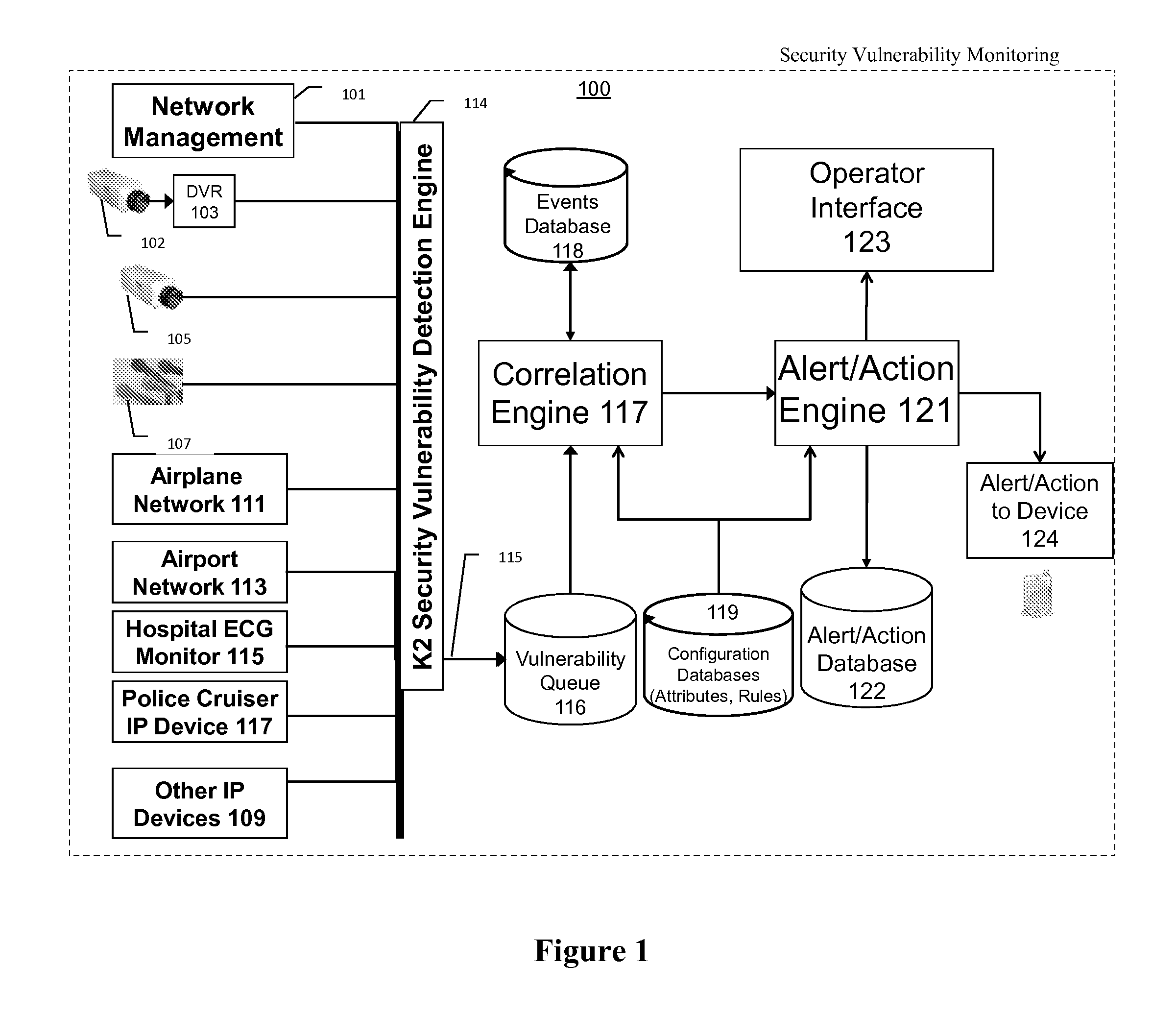
This invention is a system, method, and apparatus for detecting compromise of IP devices that make up an IP-based network. One embodiment is a method for detecting and alerting on the following conditions: (1) Denial of Service Attack; (2) Unauthorized Usage Attack; and (3) Spoofing Attack. A survey of services running on the IP device, historical benchmark data, and traceroute information may be used to detect a possible Denial of Service Attack. A detailed log analysis and a passive DNS compromise system may be used to detect a possible unauthorized usage. Finally, a fingerprint of the IP device or its configuration settings, a watermark inserted in the data-stream, and a private key burned into the IP devices' physical memory may be used to detect a possible spoofing attack. The present invention may be used to help mitigate intrusions and vulnerabilities in IP networks.
Owner:HUSSAIN DANIAR +1
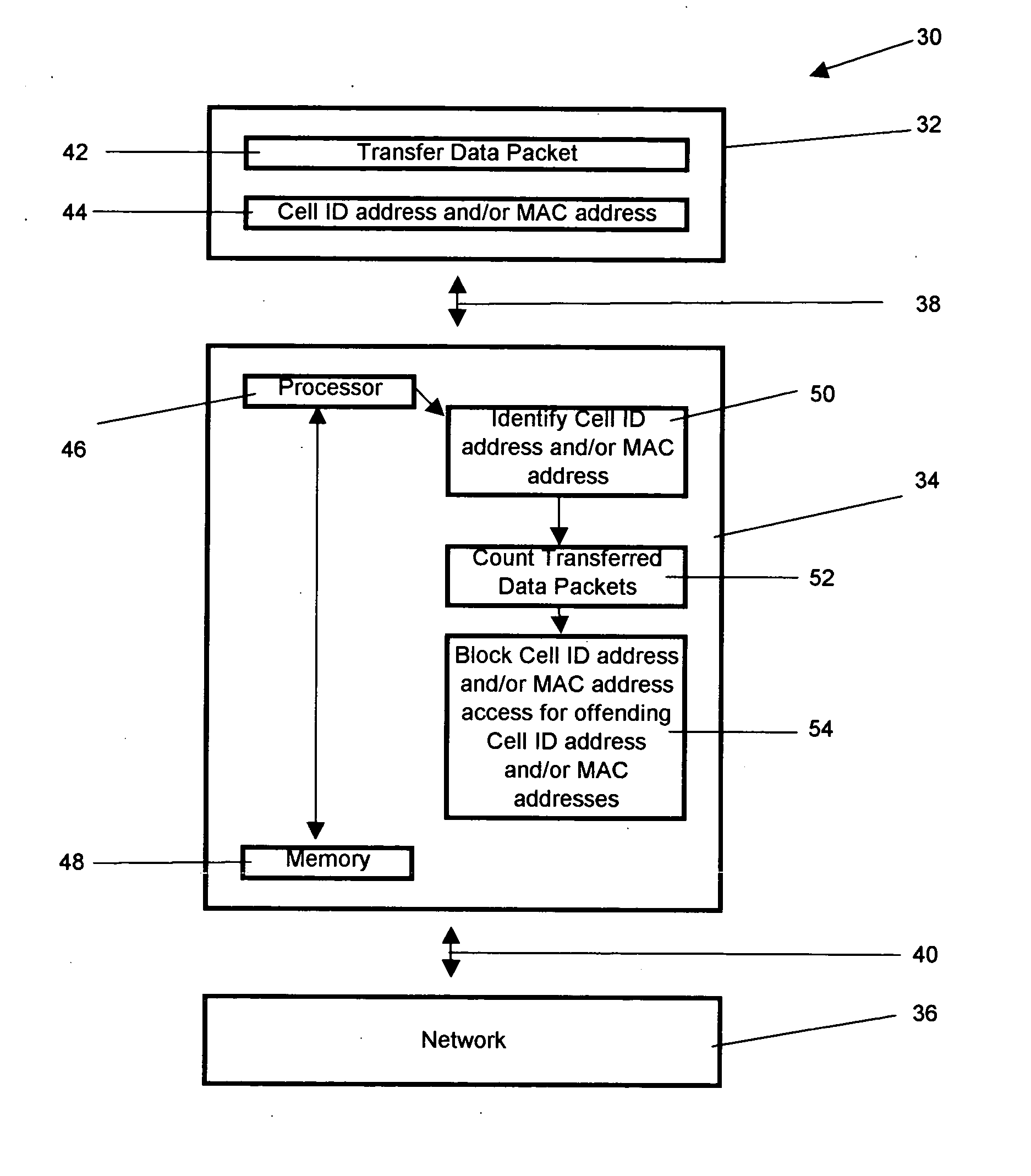
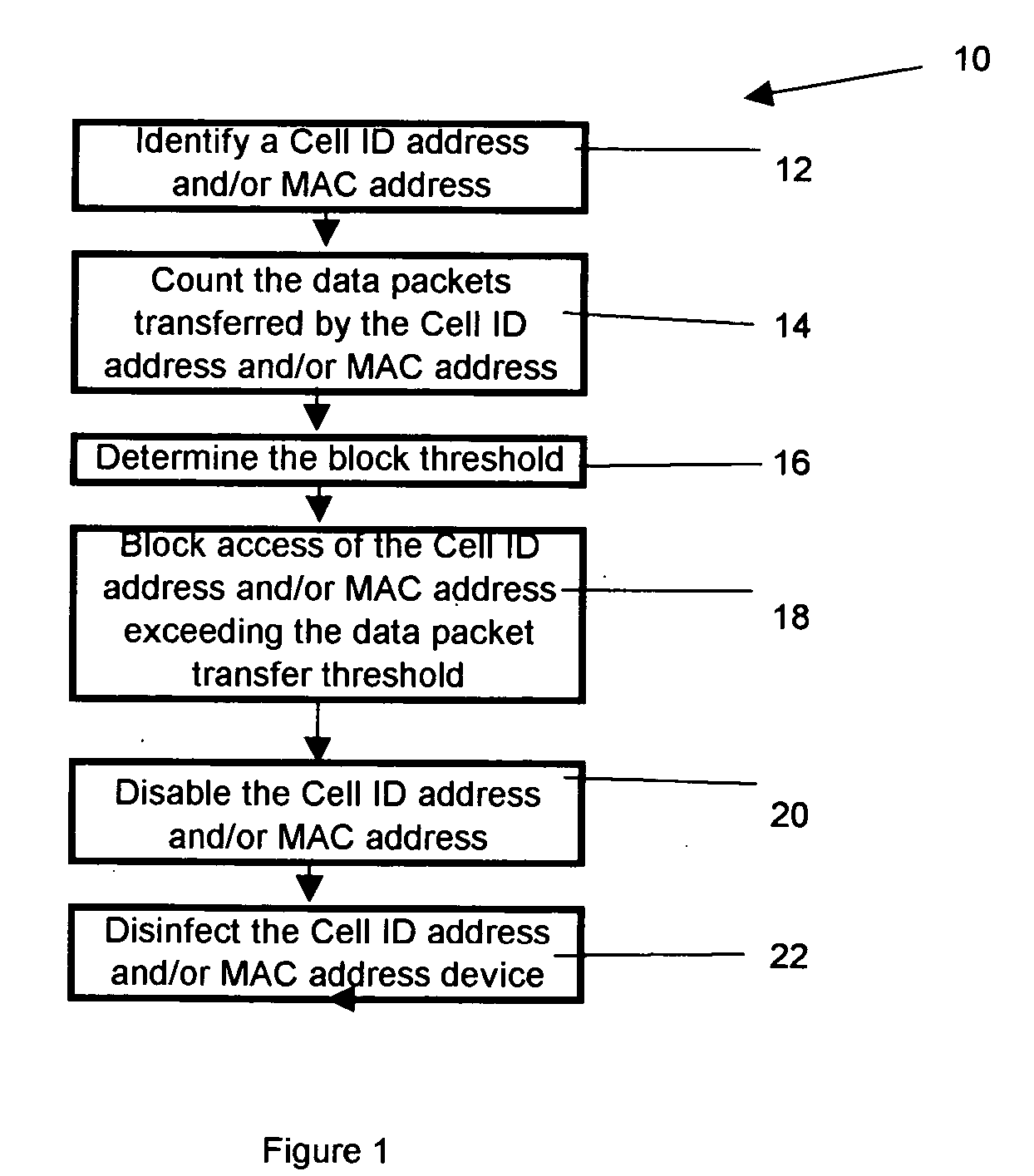
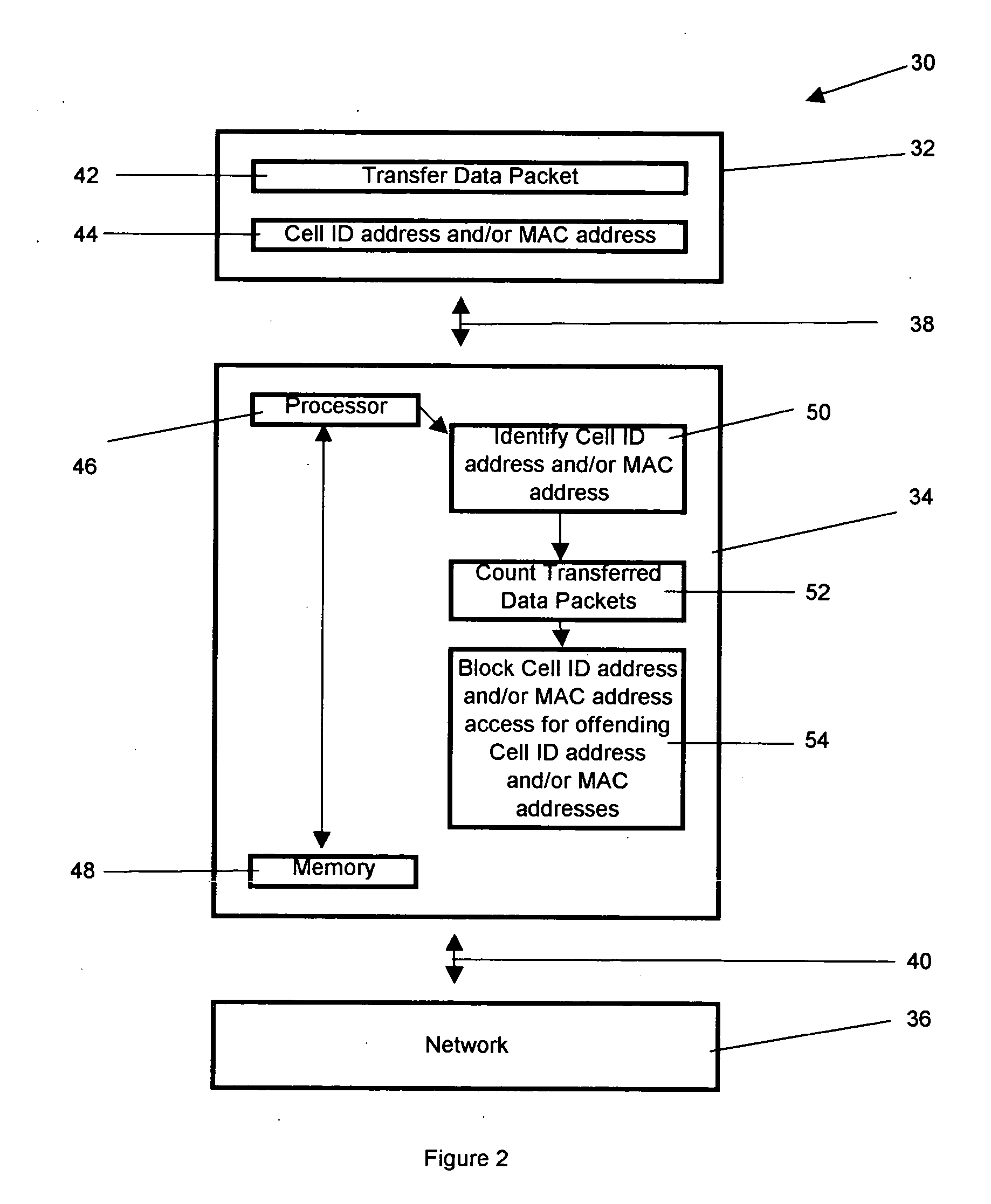
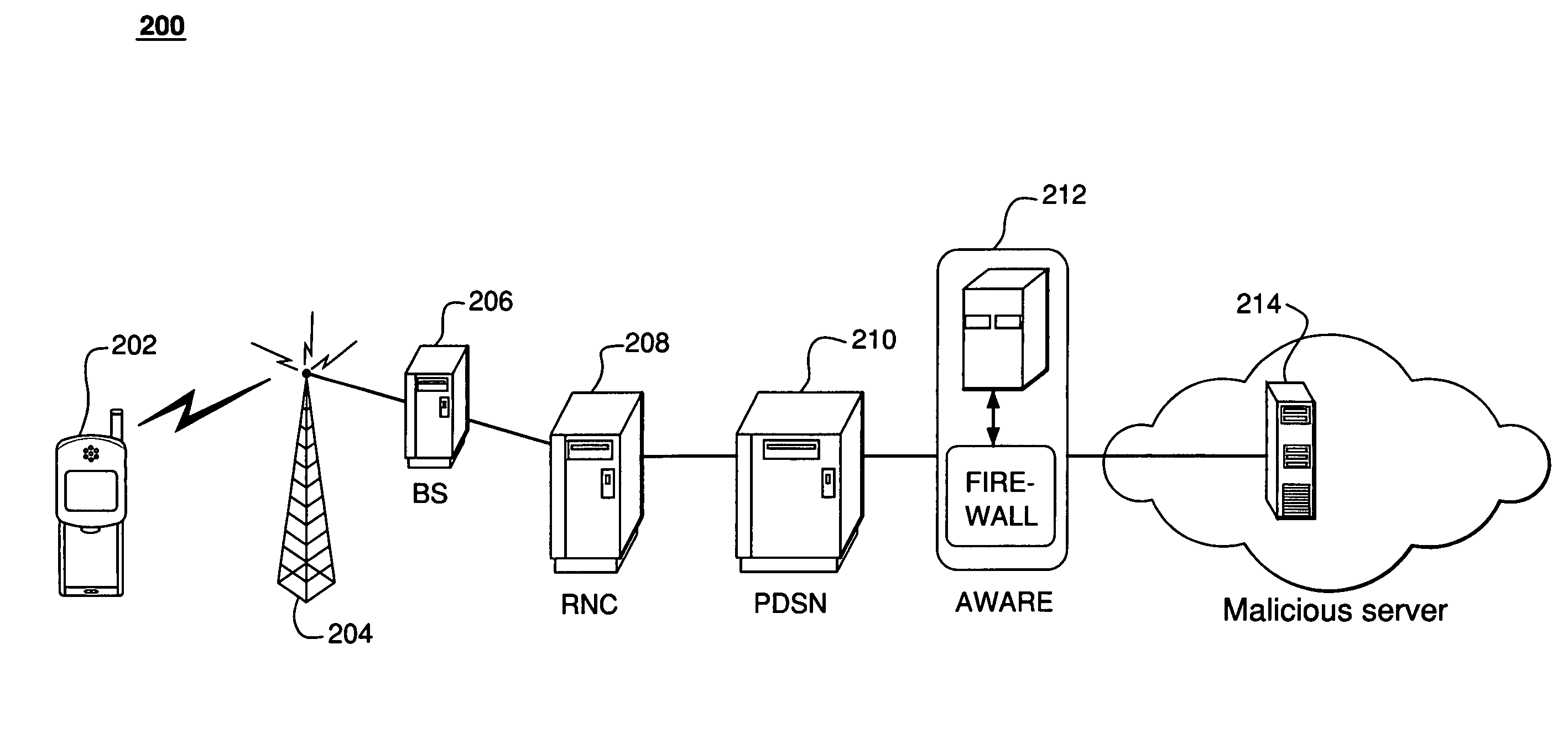
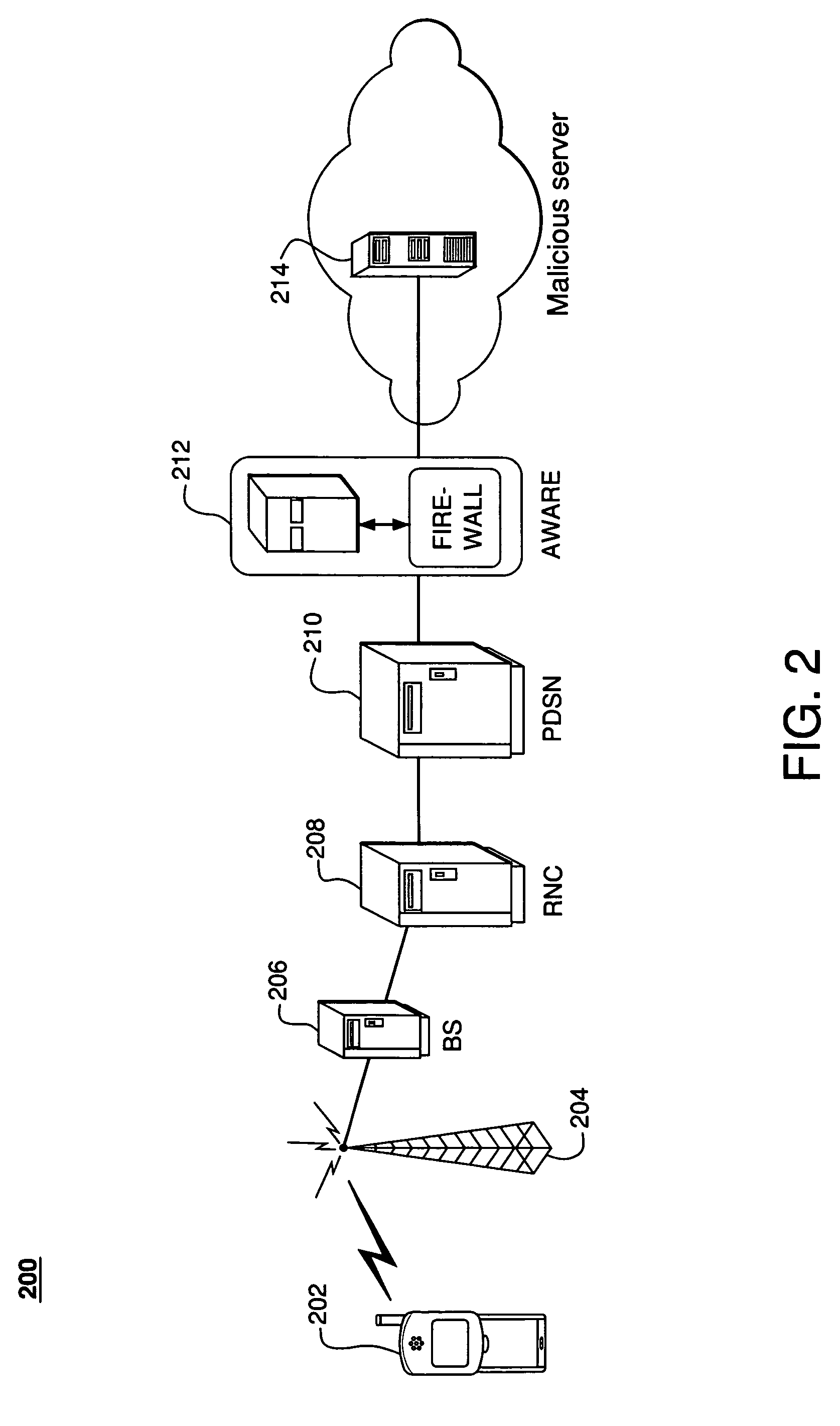
Method of preventing denial of service attacks in a cellular network
InactiveUS20070140275A1Lower cost of capitalFacilitate identification and management and isolationData switching by path configurationStore-and-forward switching systemsSystems approachesCellular network
A system, method, and computer readable medium for preventing denial of service attacks in a cellular network, that comprises, counting a data packet generated by an address on the cellular network and blocking access to the cellular network of the address if the counted data packets exceeds a pre-defined threshold.
Owner:BOWMAN CHRIS +2
Method and apparatus for detecting denial of service attacks
InactiveUS20060272018A1Memory loss protectionError detection/correctionBehavioral analyticsData stream
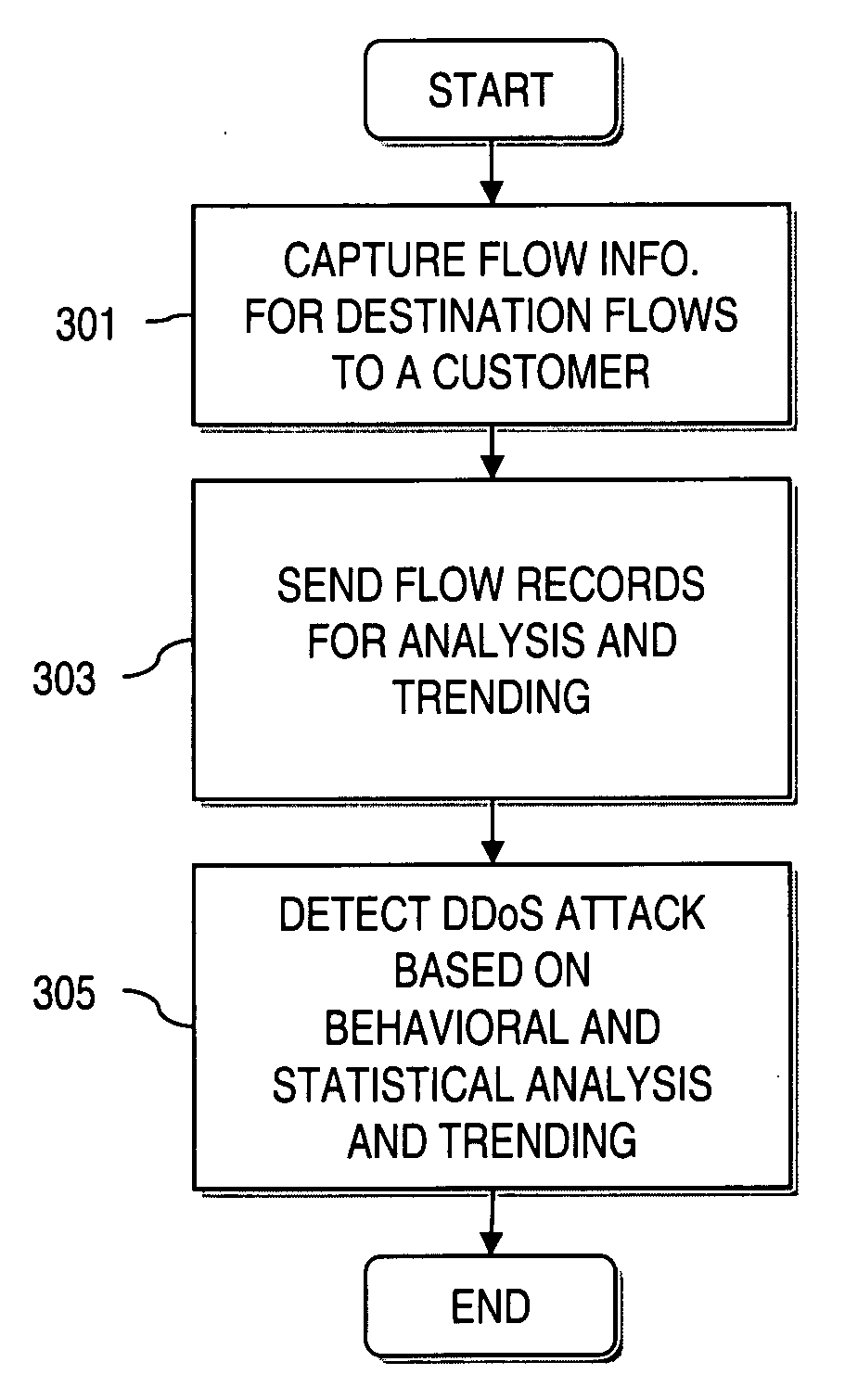
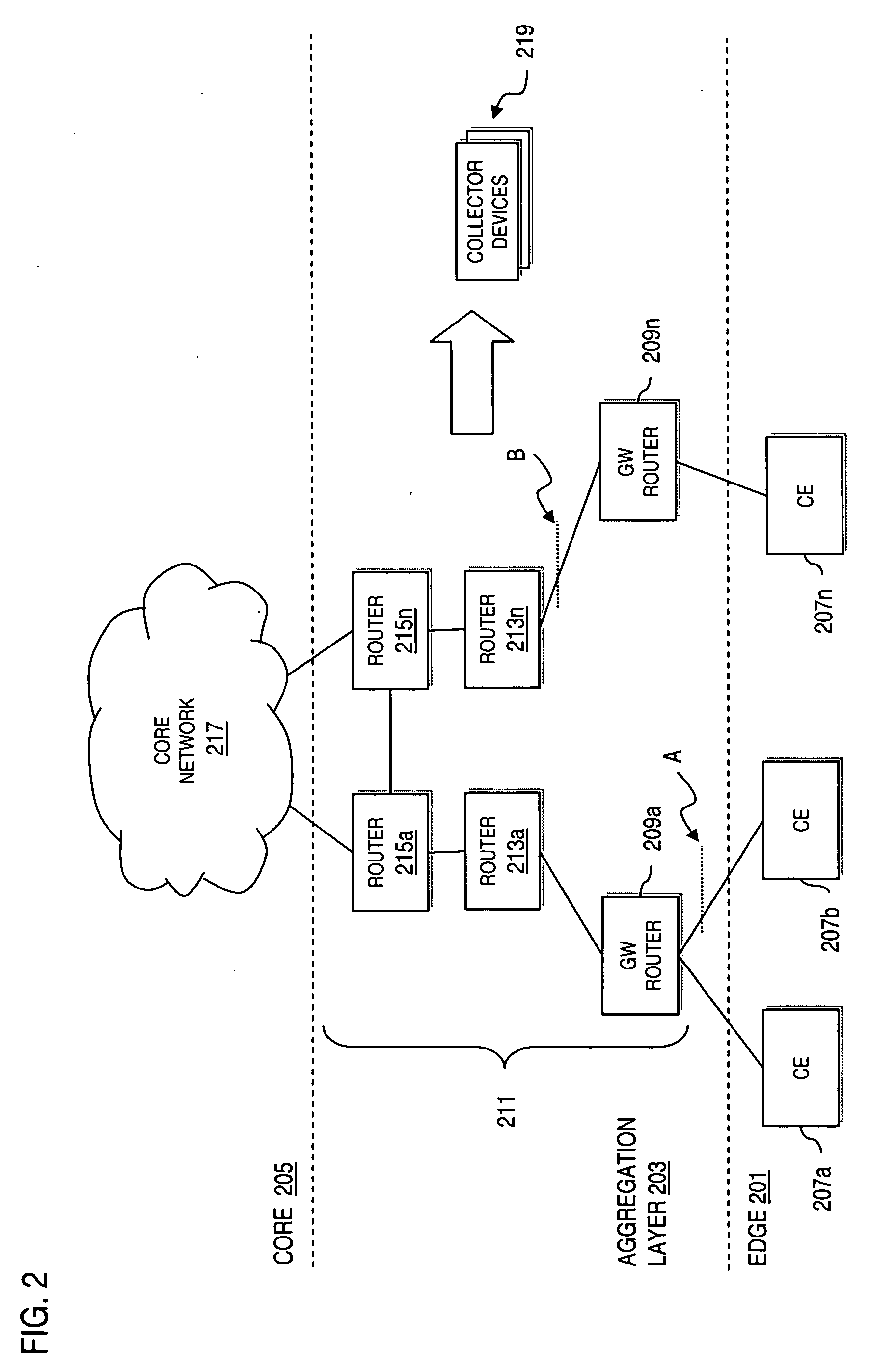
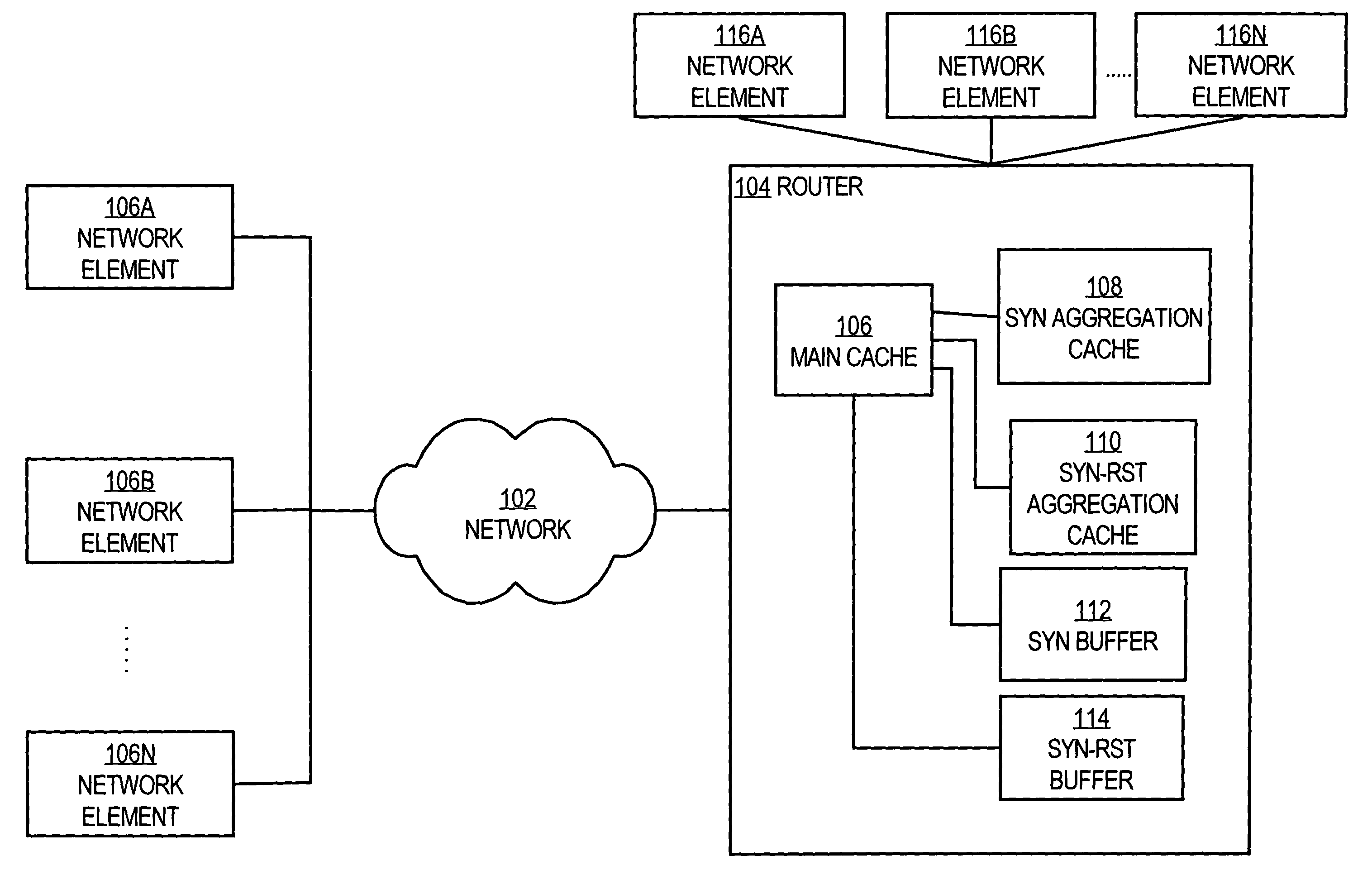
An approach is provided for supporting network security. A dataflow destined for an end user network is received. The dataflow is sampled according to a predetermined sampling rate. Flow information is generated from the sampled dataflow. The flow information is forwarded to a collector device for remote behavioral analysis to determine a behavioral profile indicative of a Denial of Service (DoS) attack (e.g., distributed Denial of Service (DDOS) attack) of the end user network.
Owner:VERIZON PATENT & LICENSING INC
Detecting network denial of service attacks
Owner:CISCO TECH INC
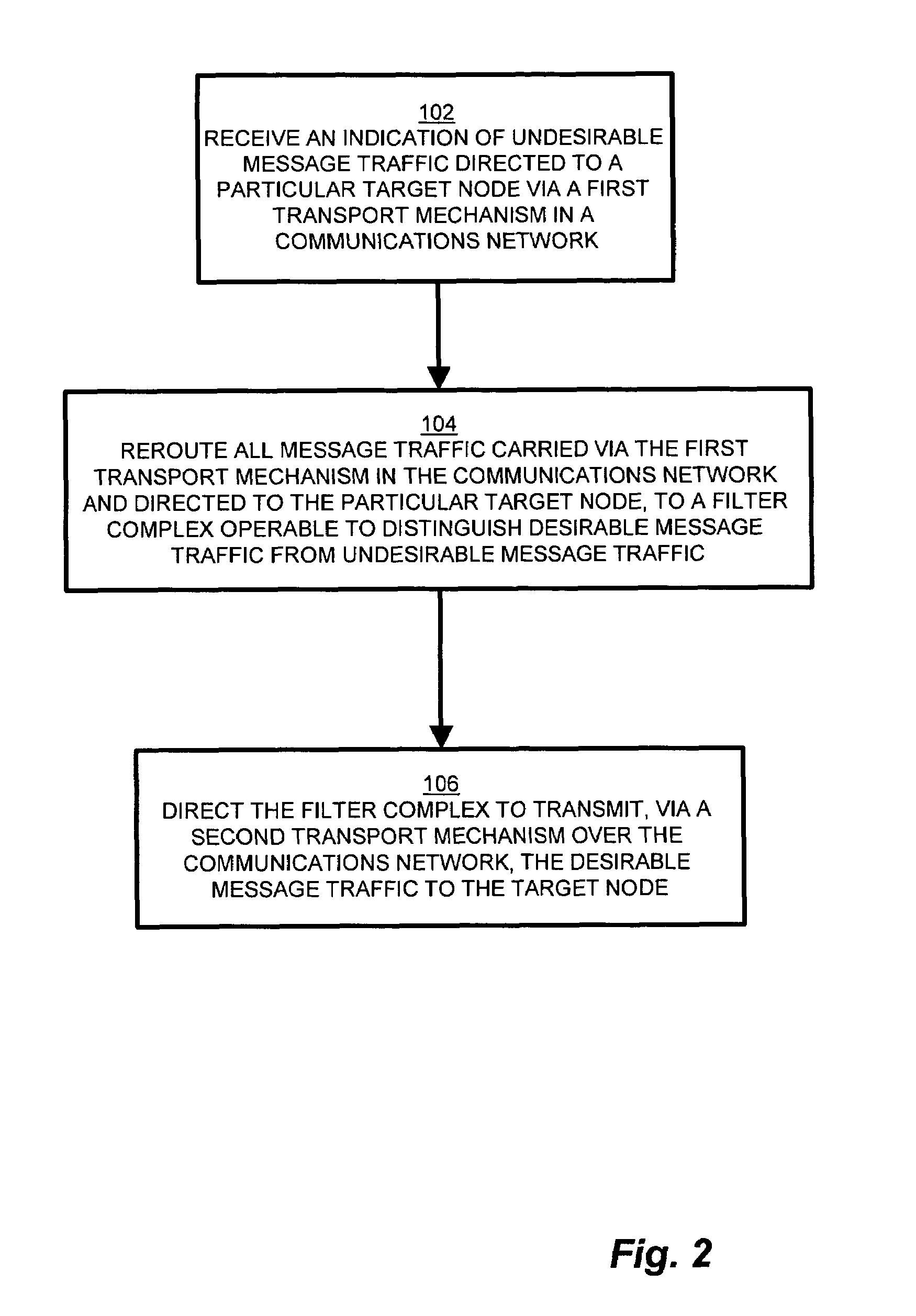
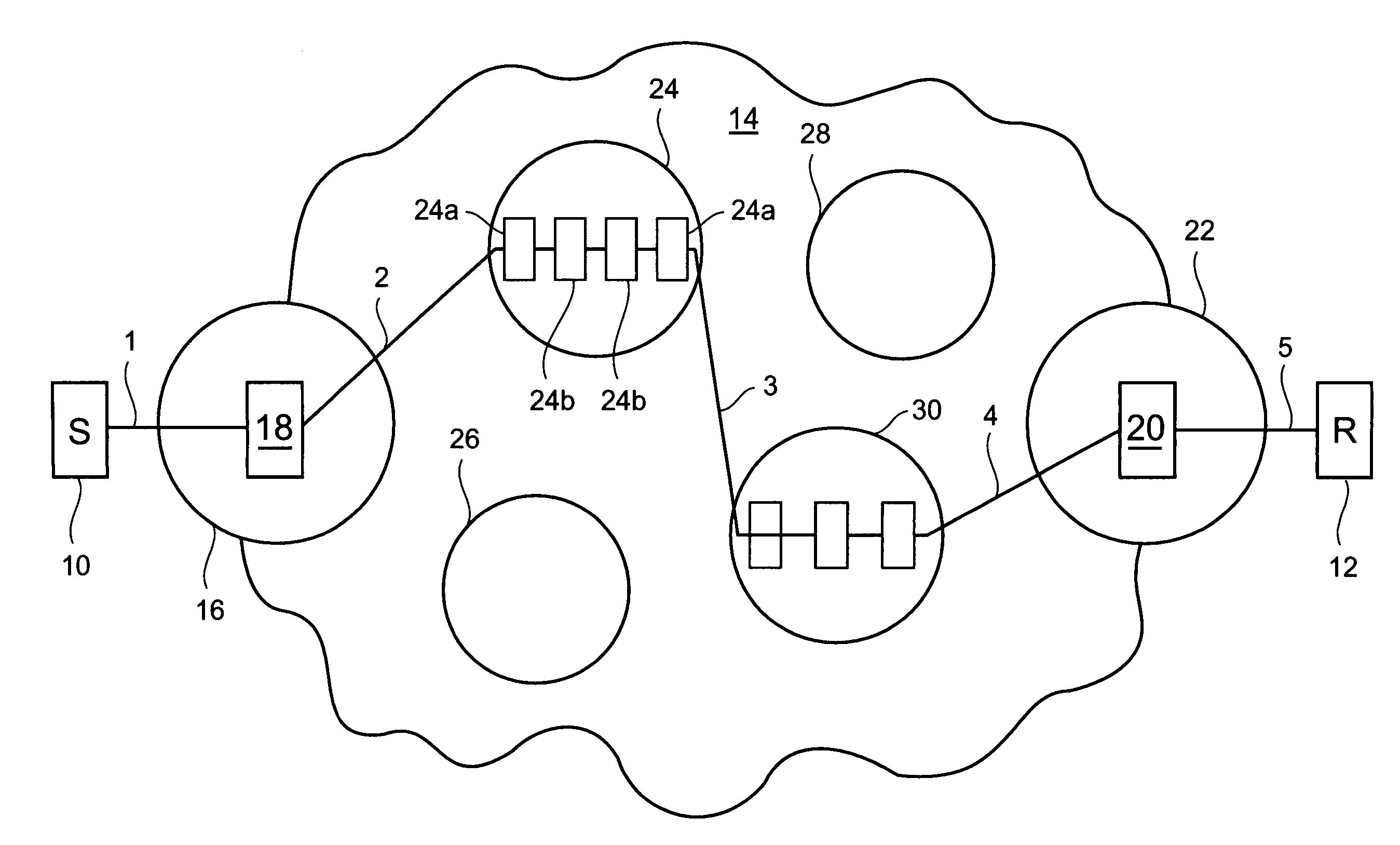
Methods and apparatus for network message traffic redirection
ActiveUS7409712B1Avoid reconfigurationMemory loss protectionDigital data processing detailsTraffic capacityCountermeasure
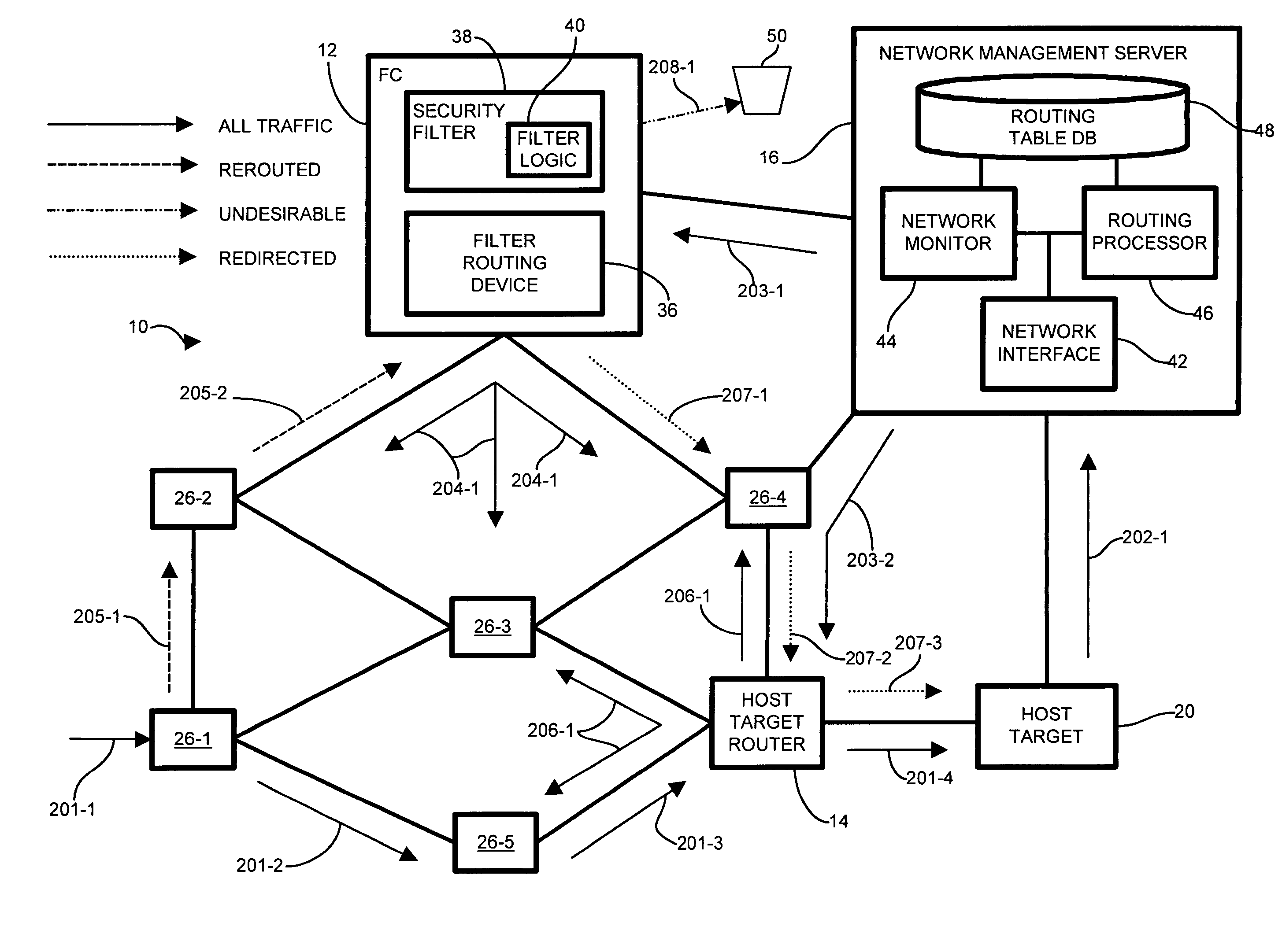
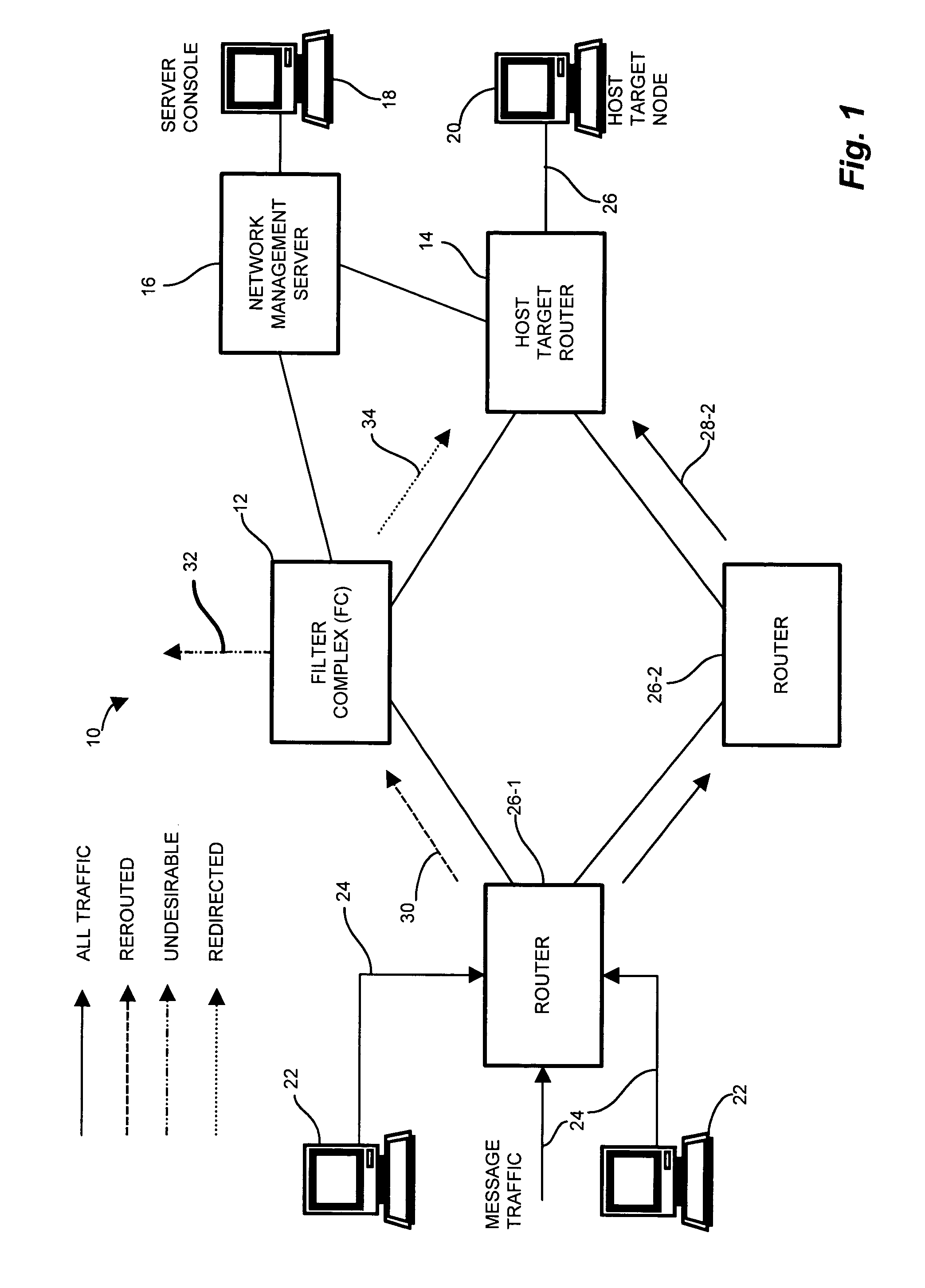
Conventional methods of addressing a Distributed Denial of Service attack include taking the target node offline, and routing all traffic to an alternate countermeasure, or “sinkhole” router, therefore requiring substantial lag time to reconfigure the target router into the network. In a network, a system operator monitors a network for undesirable message traffic. Upon a notification of such undesirable message traffic, traffic is rerouted to a filter complex to separate undesirable traffic. The filter complex establishes an alternate route using a second communications protocol, and uses the alternate route to redirect the desirable message traffic to the target node. The use of the second protocol avoids conflict between the redirected desirable traffic and the original, or first, protocol which now performs the reroute. In this manner, the filter complex employs a second alternate communications protocol to reroute and redirect desirable message traffic to the target node while diverting undesirable message traffic, and therefore avoids widespread routing configuration changes by limiting the propagation breadth of the second protocol.
Owner:CISCO TECH INC
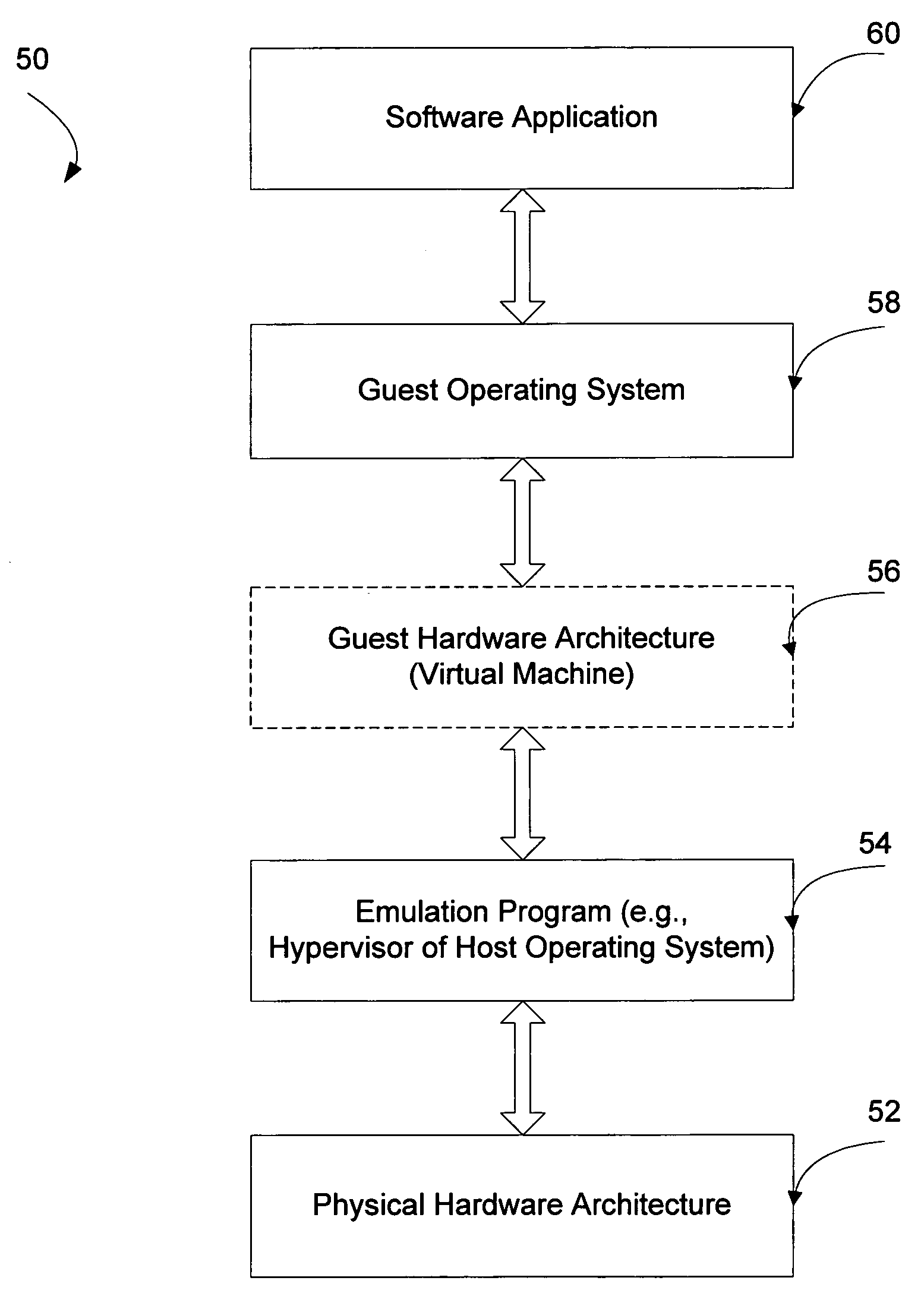
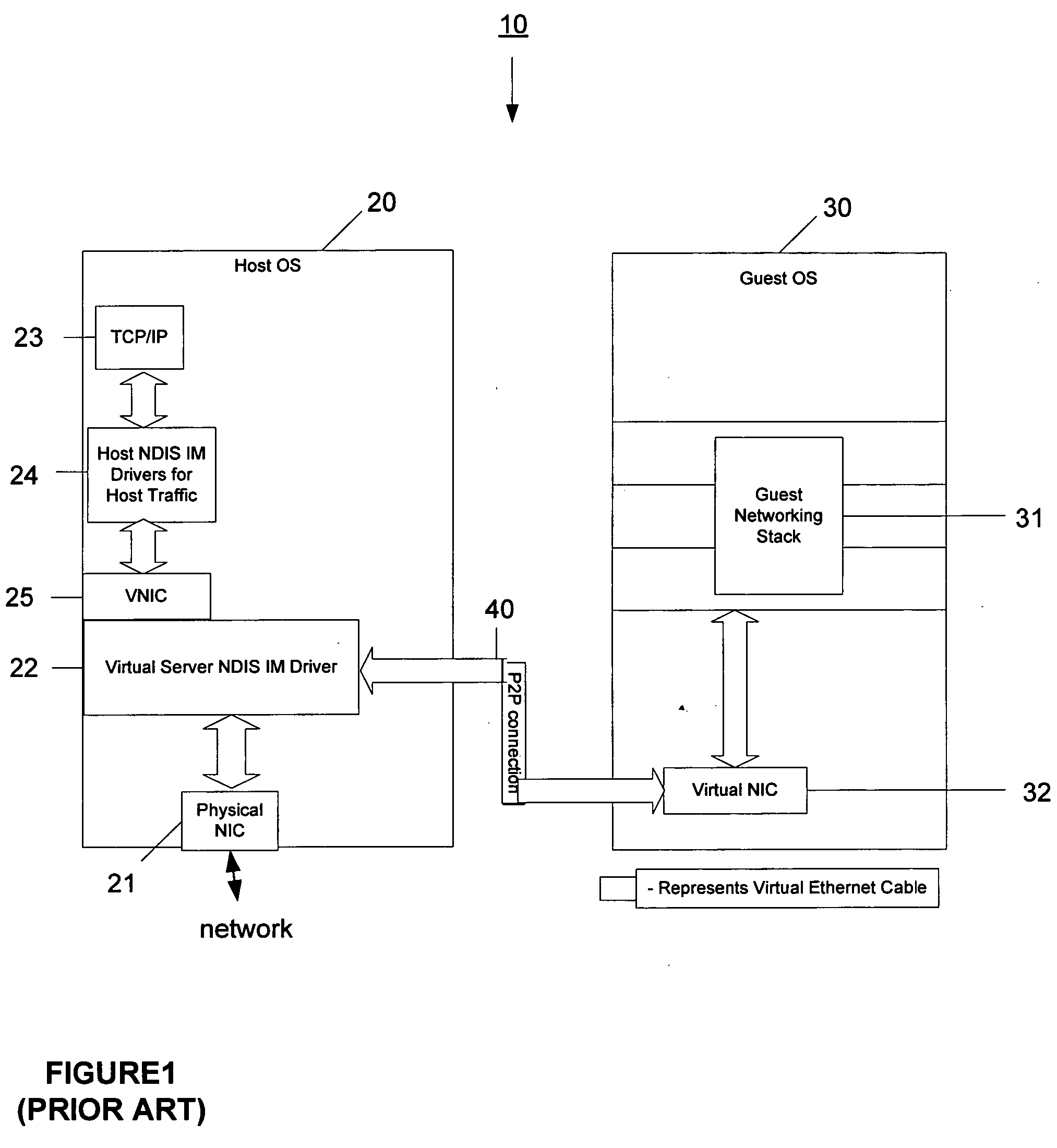
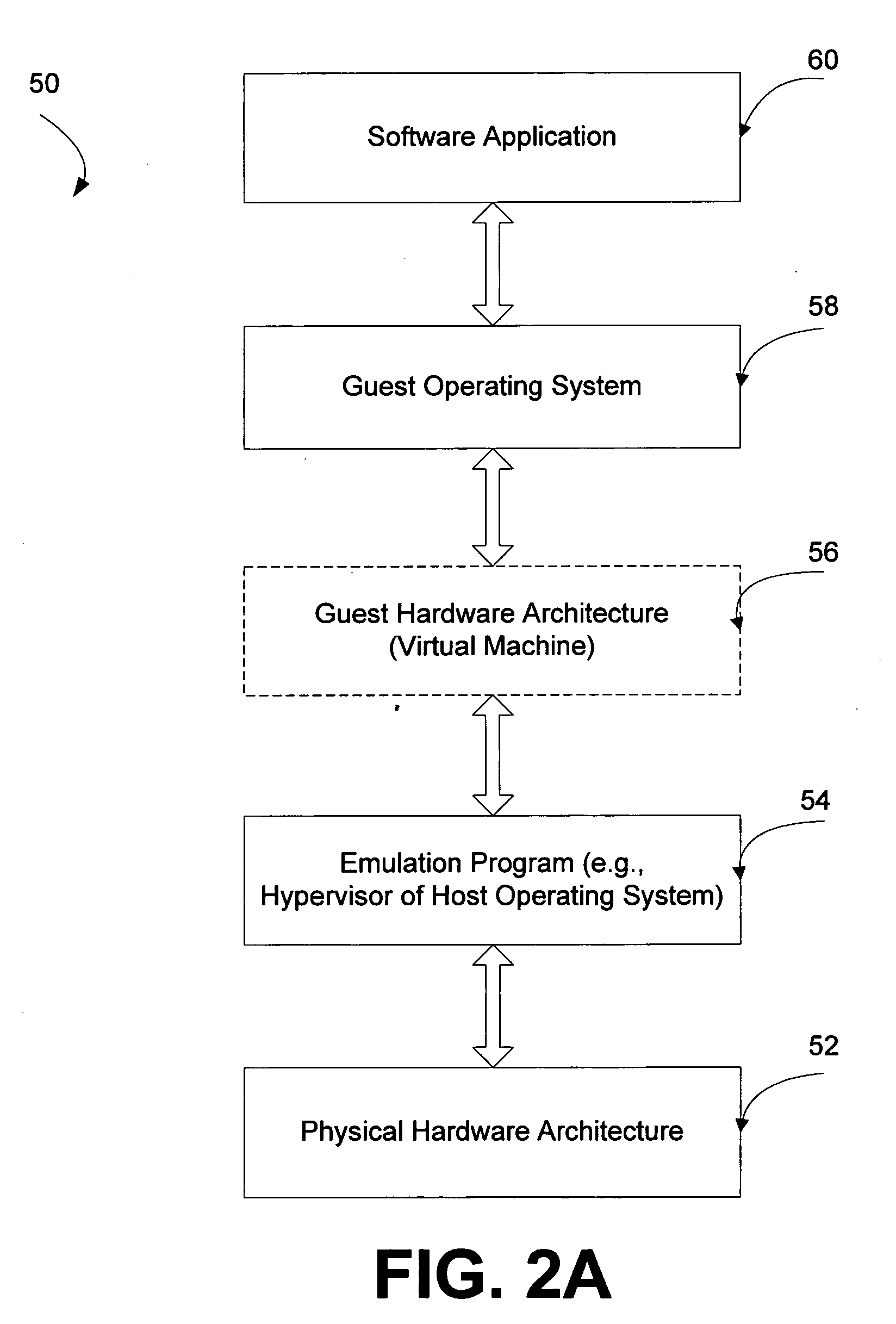
VM network traffic monitoring and filtering on the host
InactiveUS20060206300A1Software simulation/interpretation/emulationMemory systemsQuality of serviceOperational system
A system and method is provided that enables older legacy guest operating systems like Windows NT 4.0 and Windows95® to take advantage of newly developed NDIS Intermediate (IM) drivers that support firewalls, quality of service, IP security, intrusion detection, and other functionality for monitoring / filtering incoming and outgoing network traffic in contemporary host operating systems such as Windows XP operating in a virtual machine (VM) environment. The invention thus makes such older legacy operating systems less susceptible to Internet viruses, and worms, network denial of service (DOS) attacks, and the like. For each Virtual Network Interface Card (VNIC) in a guest VM, a corresponding VNIC is created on the host OS, and a point to point connection is established between the guest and host VNICs. The NDIS IM drivers bind themselves on top of the host VNIC and effectively place themselves as a filter on the point to point connection.
Owner:MICROSOFT TECH LICENSING LLC
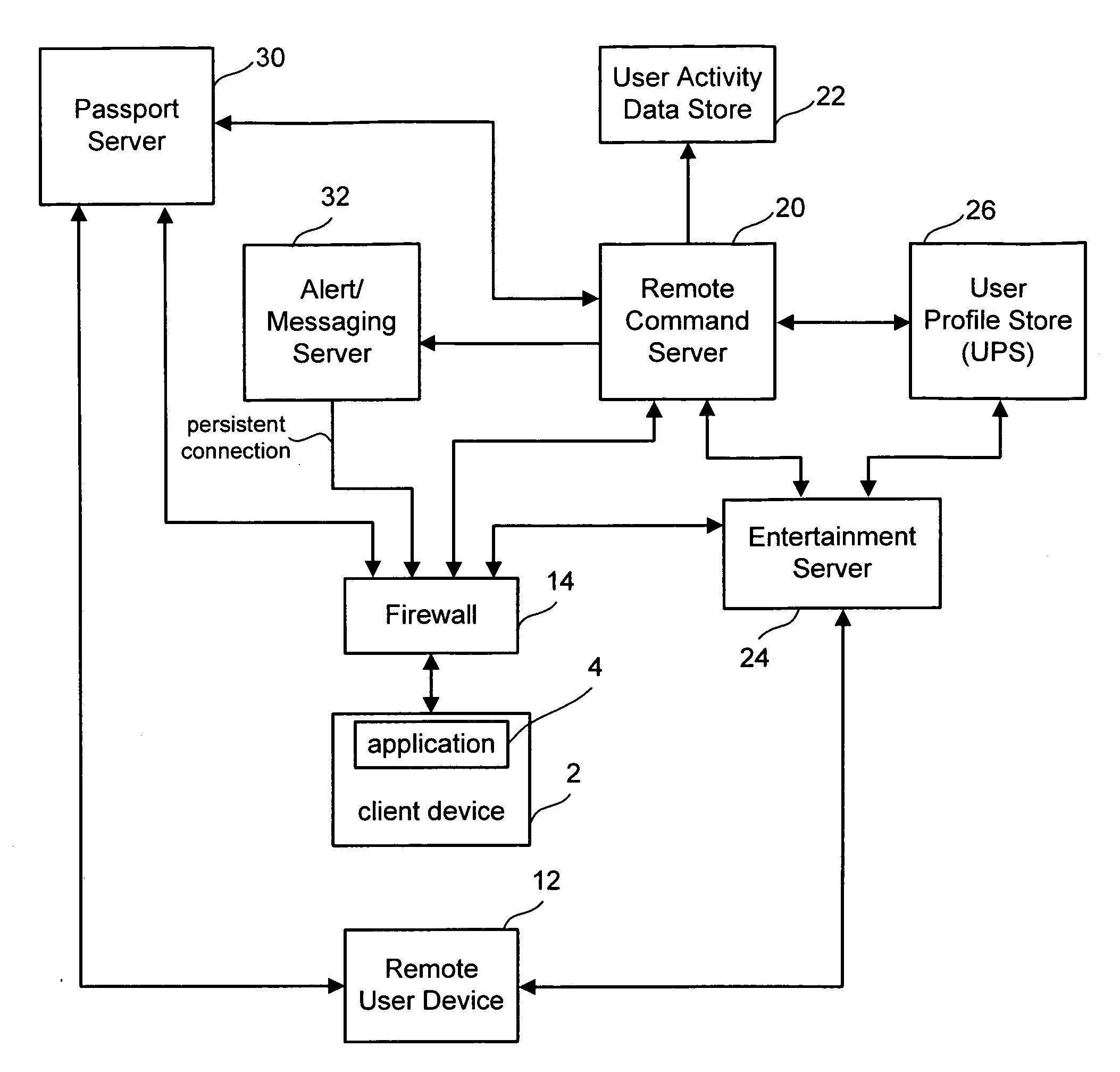
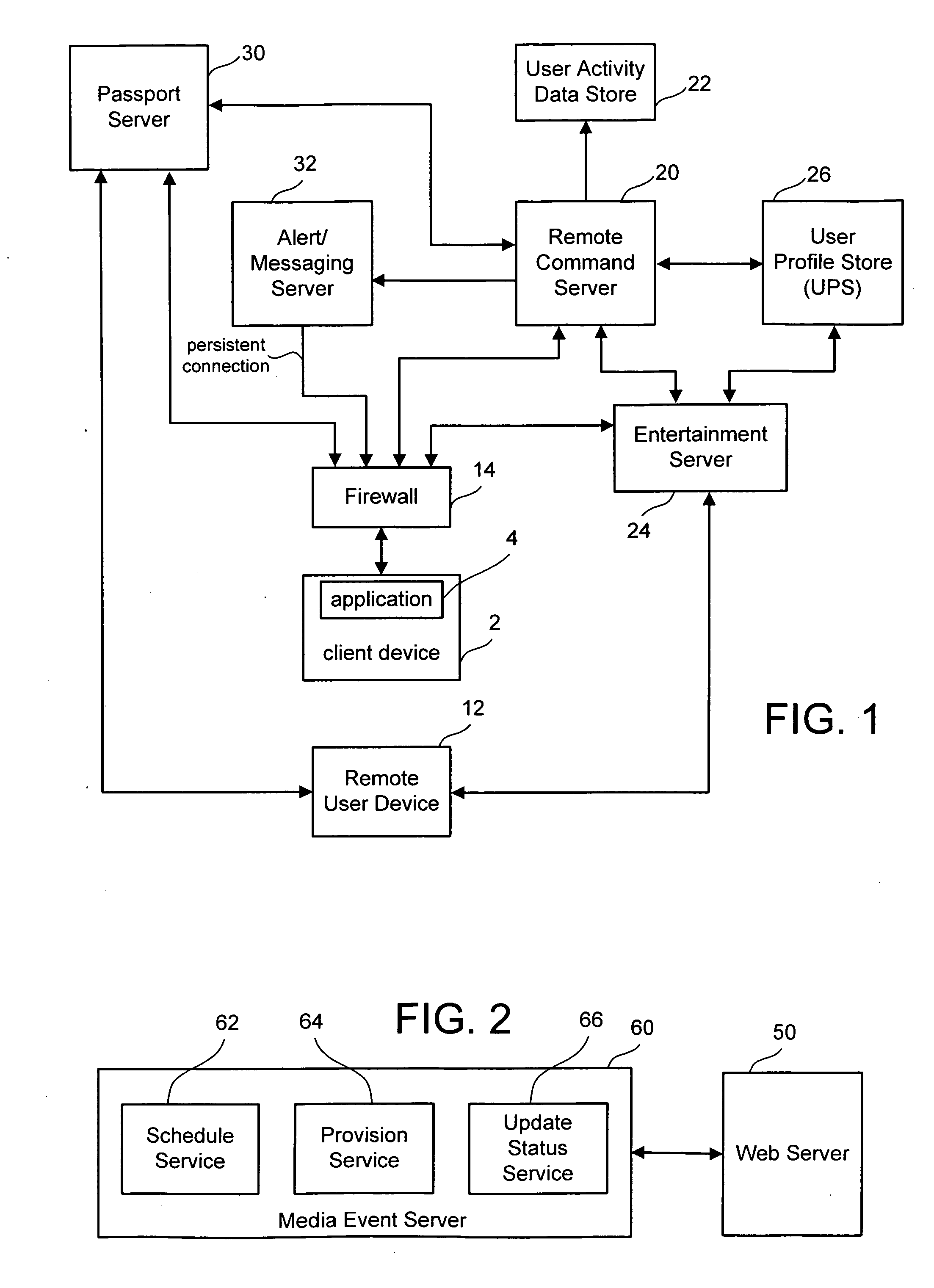
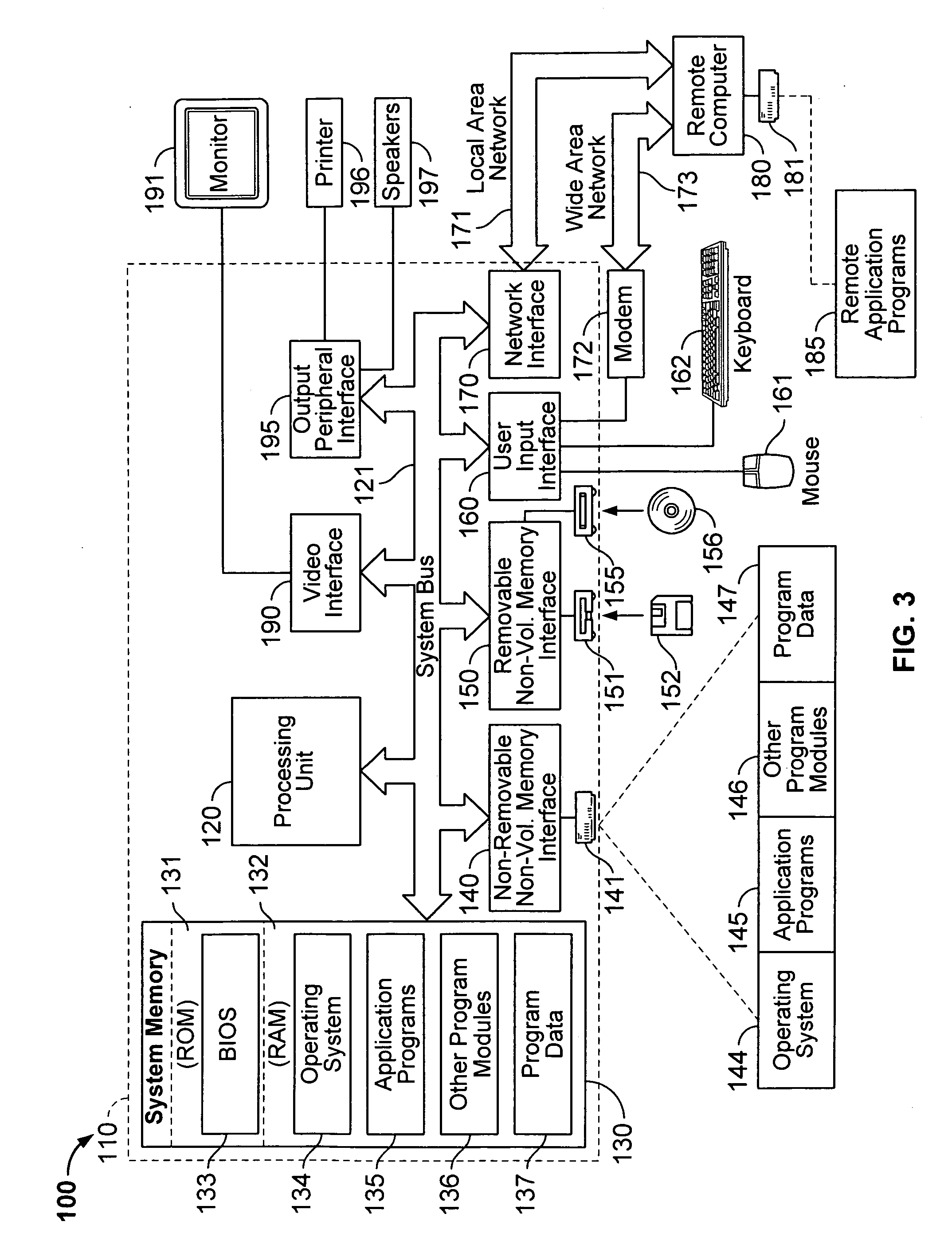
Remote command framework for devices
ActiveUS20060161662A1Improve protectionMemory loss protectionError detection/correctionThe InternetHigh availability
A robust device messaging framework is disclosed that enables a user to send commands to a device. A provisioning service is used to provision unique device identities and maps user web identities to device identities. The provisioning service also limits device per day provisioning attempts to limit denial of service attacks. A command service allows remote users to issue commands to a device, synchronize outgoing commands with incoming results, receive accurate feedback about whether a command was received, and maintain state information about the device. A device layer encrypts and stores device identities, authenticates itself with the command service, establishes a high-availability Internet connection to receive alerts that a command has issued, and reports results to the server-based command service.
Owner:MICROSOFT TECH LICENSING LLC
System and method for protecting a computer network against denial of service attacks
InactiveUS6886102B1Memory loss protectionError detection/correctionComputerized systemDenial-of-service attack
A system and method are disclosed for determining whether a sender seeking to send a message to a receiving computer system via a network is an authorized sender. A request to communicate is received from the sender. A number N1 is selected. A hash value for the number N1 is calculated. The hash value is sent to the sender.
Owner:CA TECH INC
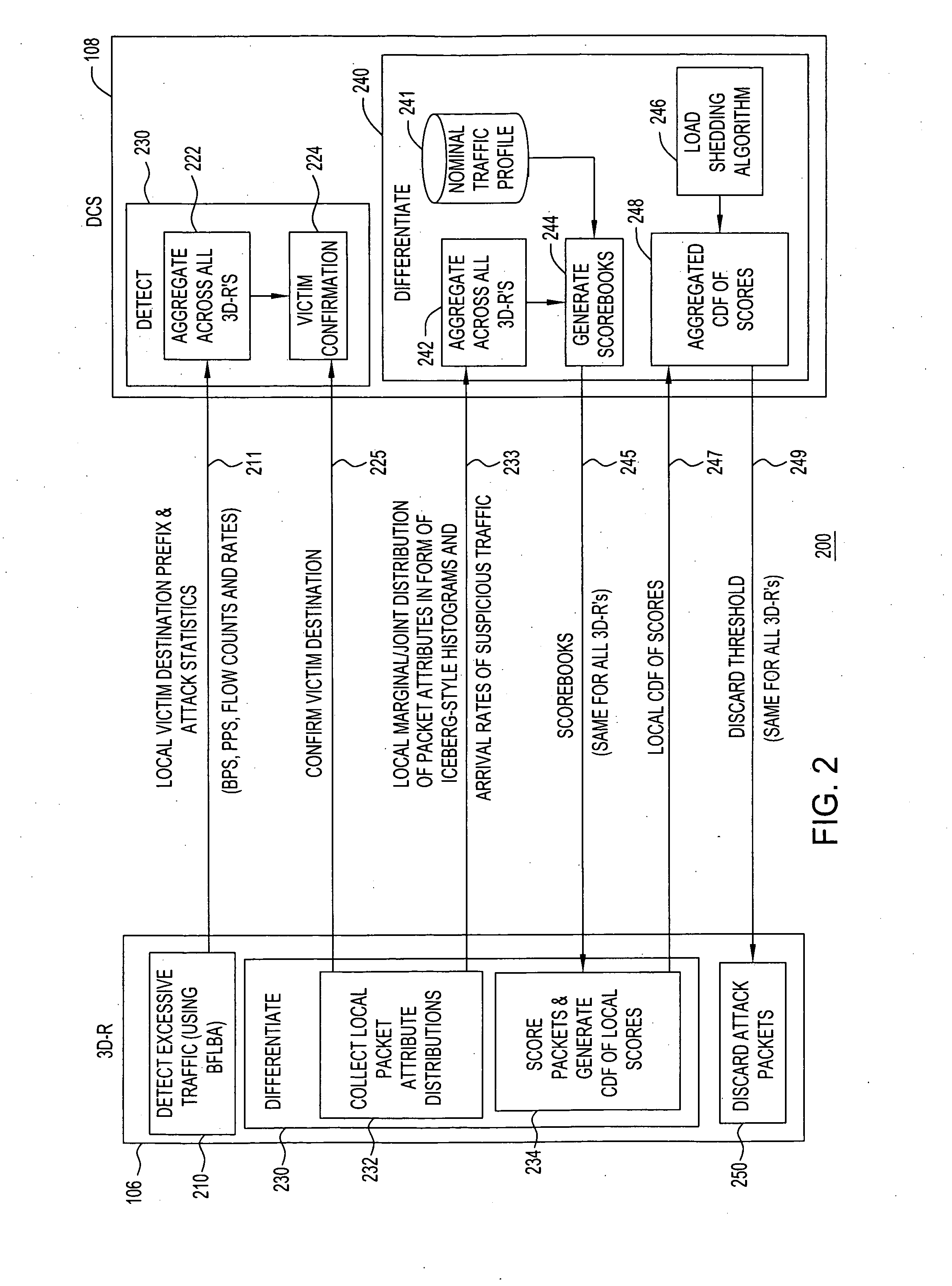
Distributed architecture for statistical overload control against distributed denial of service attacks
ActiveUS20050111367A1Overcome disadvantagesError preventionTransmission systemsOverload controlDistribution function
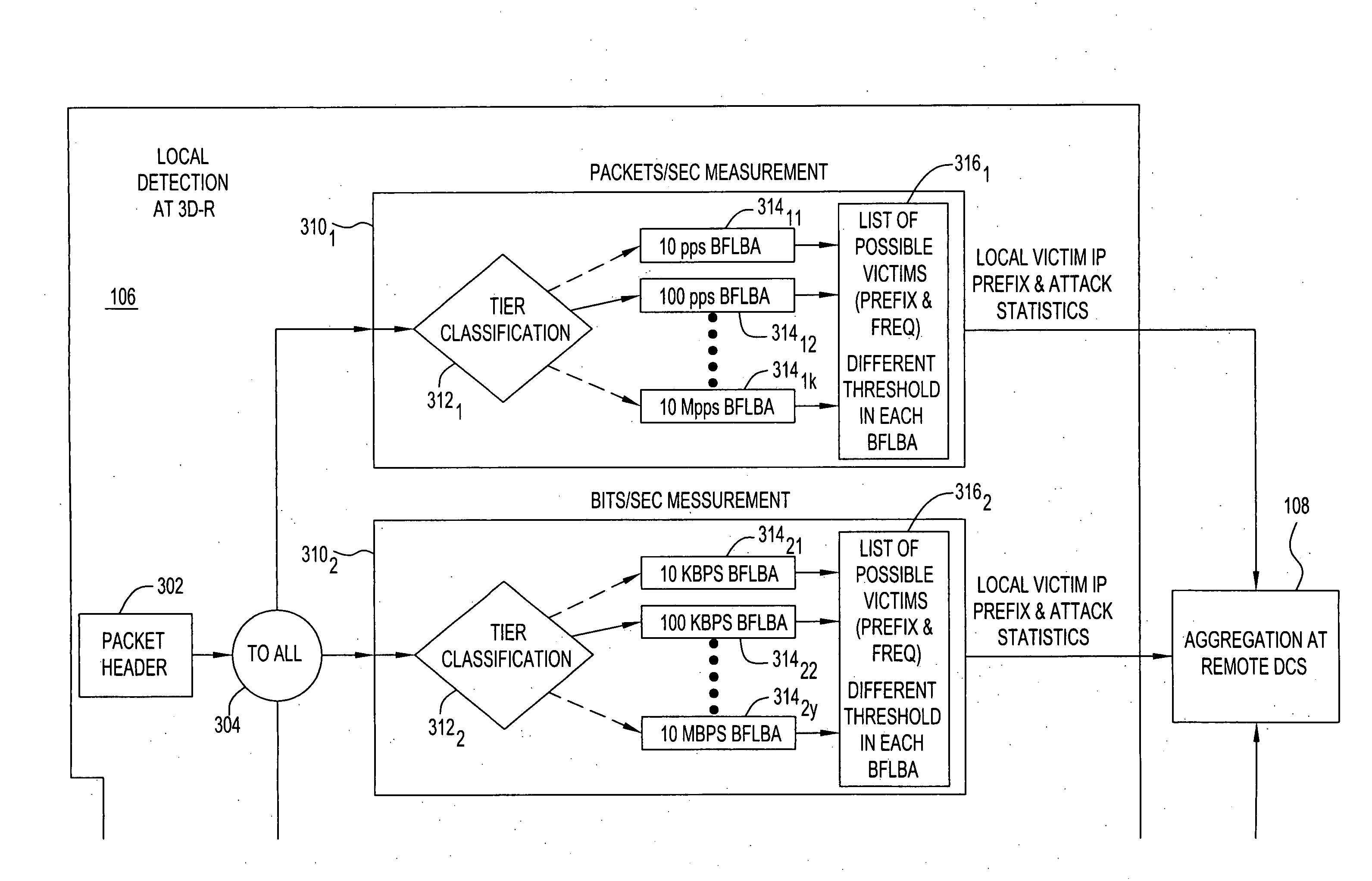
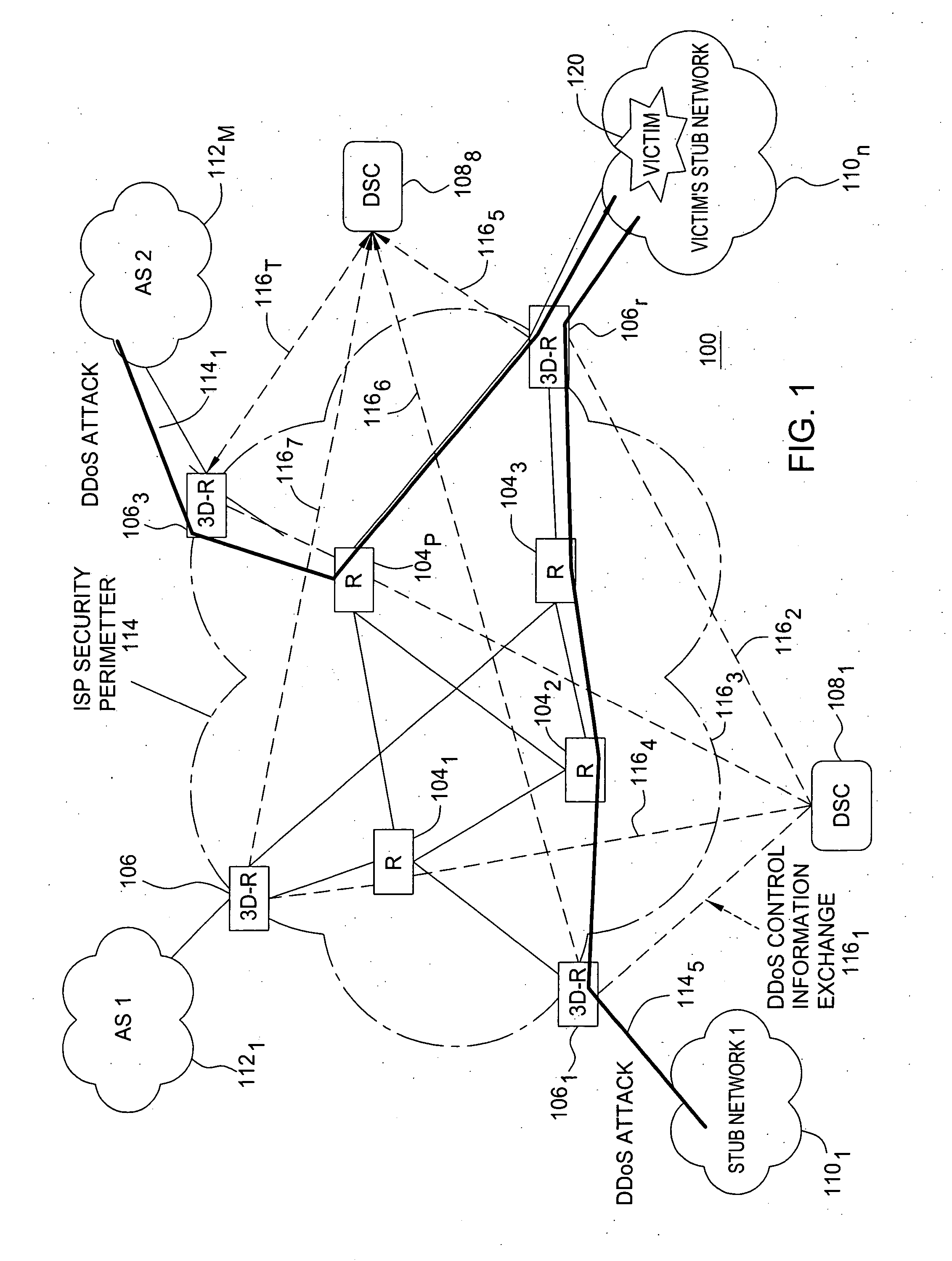
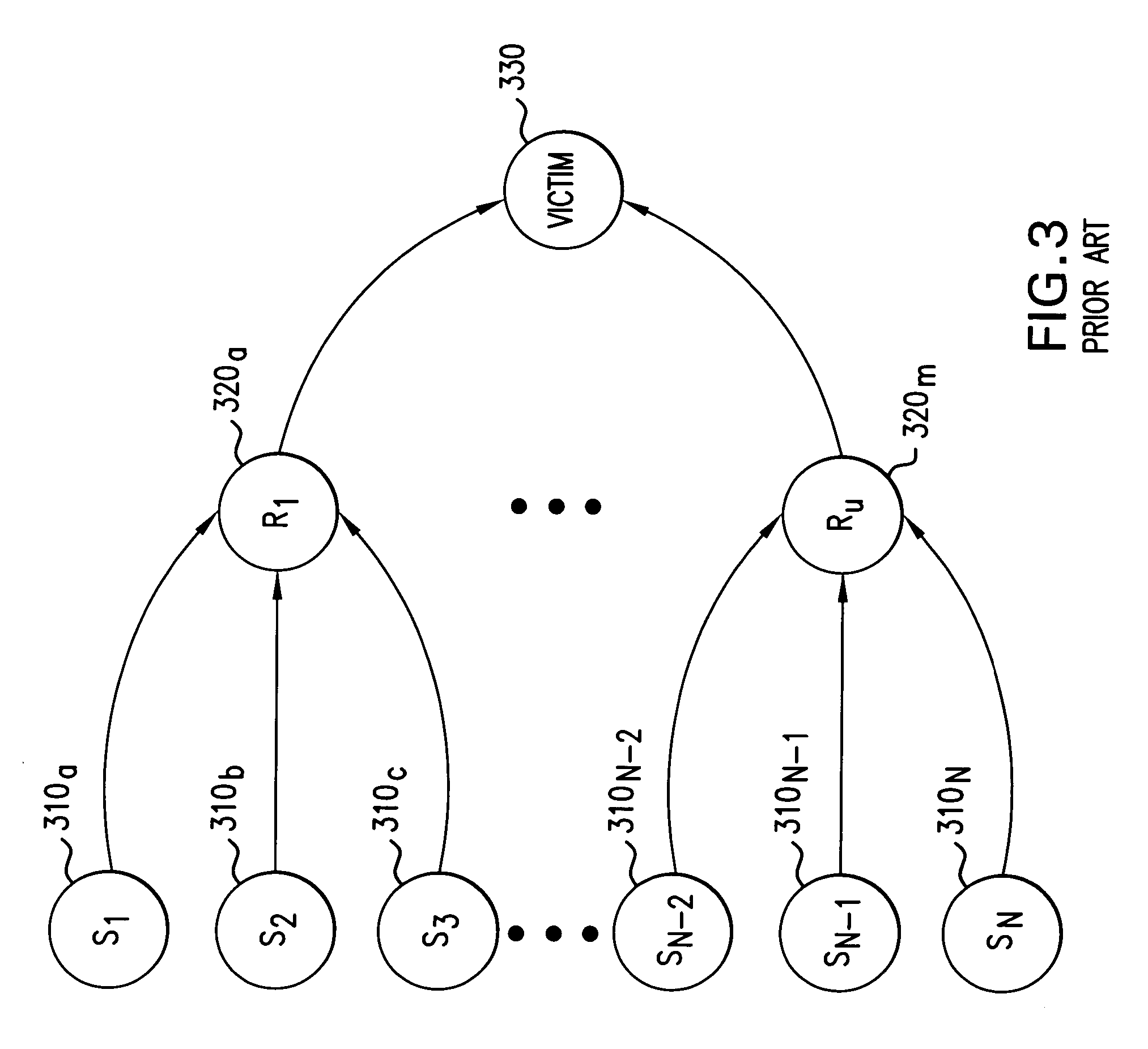
In a network including a centralized controller and a plurality of routers forming a security perimeter, a method for selectively discarding packets during a distributed denial-of-service (DDoS) attack over the network. The method includes aggregating victim destination prefix lists and attack statistics associated with incoming packets received from the plurality of routers to confirm a DDoS attack victim, and aggregating packet attribute distribution frequencies for incoming victim related packets received from the plurality of security perimeter routers. Common scorebooks are generated from the aggregated packet attribute distribution frequencies and nominal traffic profiles, and local cumulative distribution function (CDF) of the local scores derived from the plurality of security perimeter routers are aggregated. A common discarding threshold is derived from the CDF and sent to each of the plurality of security perimeter routers, where the discarding threshold defines a condition in which an incoming packet may be discarded at the security perimeter.
Owner:WSOU INVESTMENTS LLC
Detecting network denial of service attacks
Owner:CISCO TECH INC
Detection of power-drain denial-of-service attacks in wireless networks
ActiveUS7515926B2Power drainEnergy efficient ICTTime-division multiplexTelecommunicationsEngineering
Owner:ALCATEL-LUCENT USA INC +1
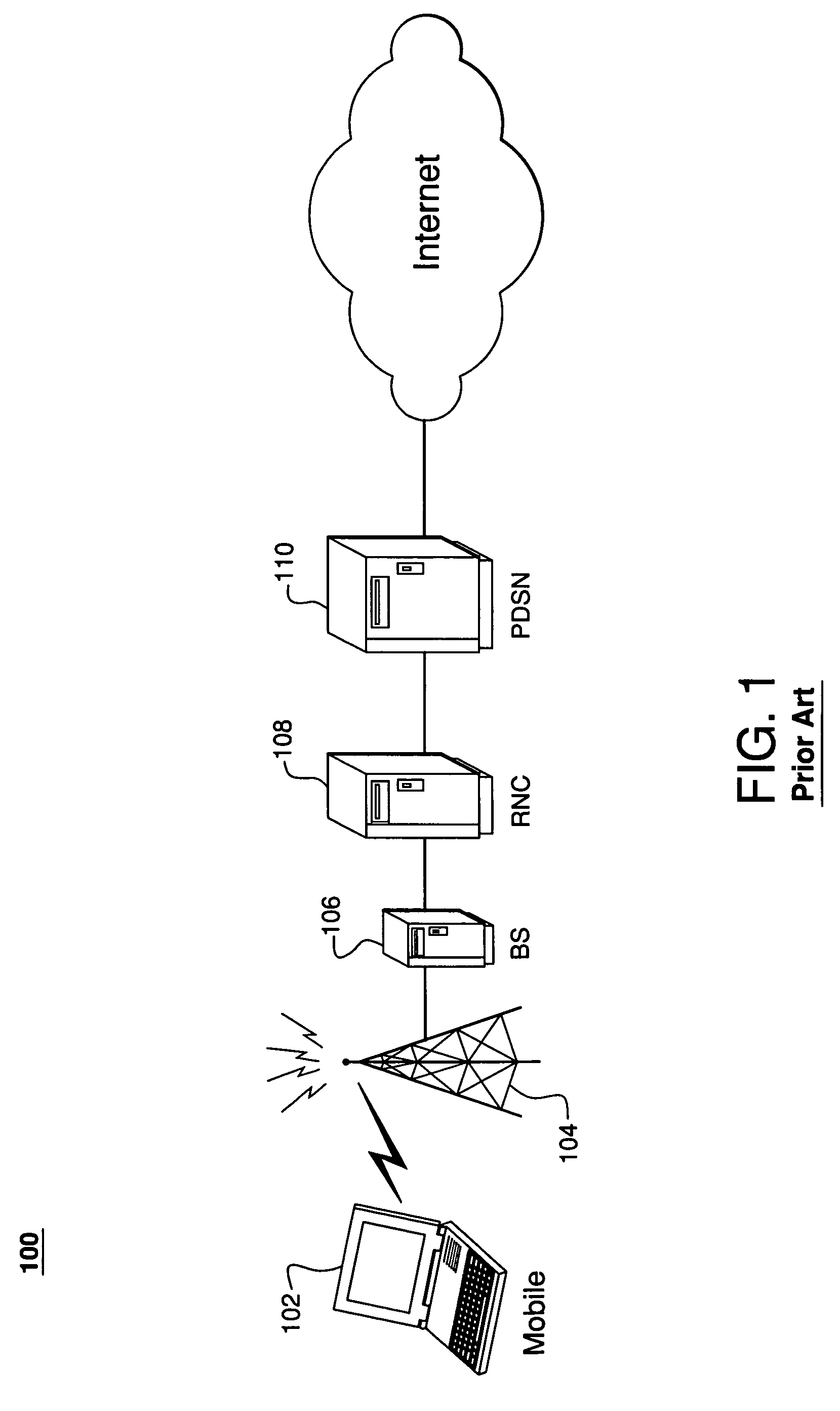
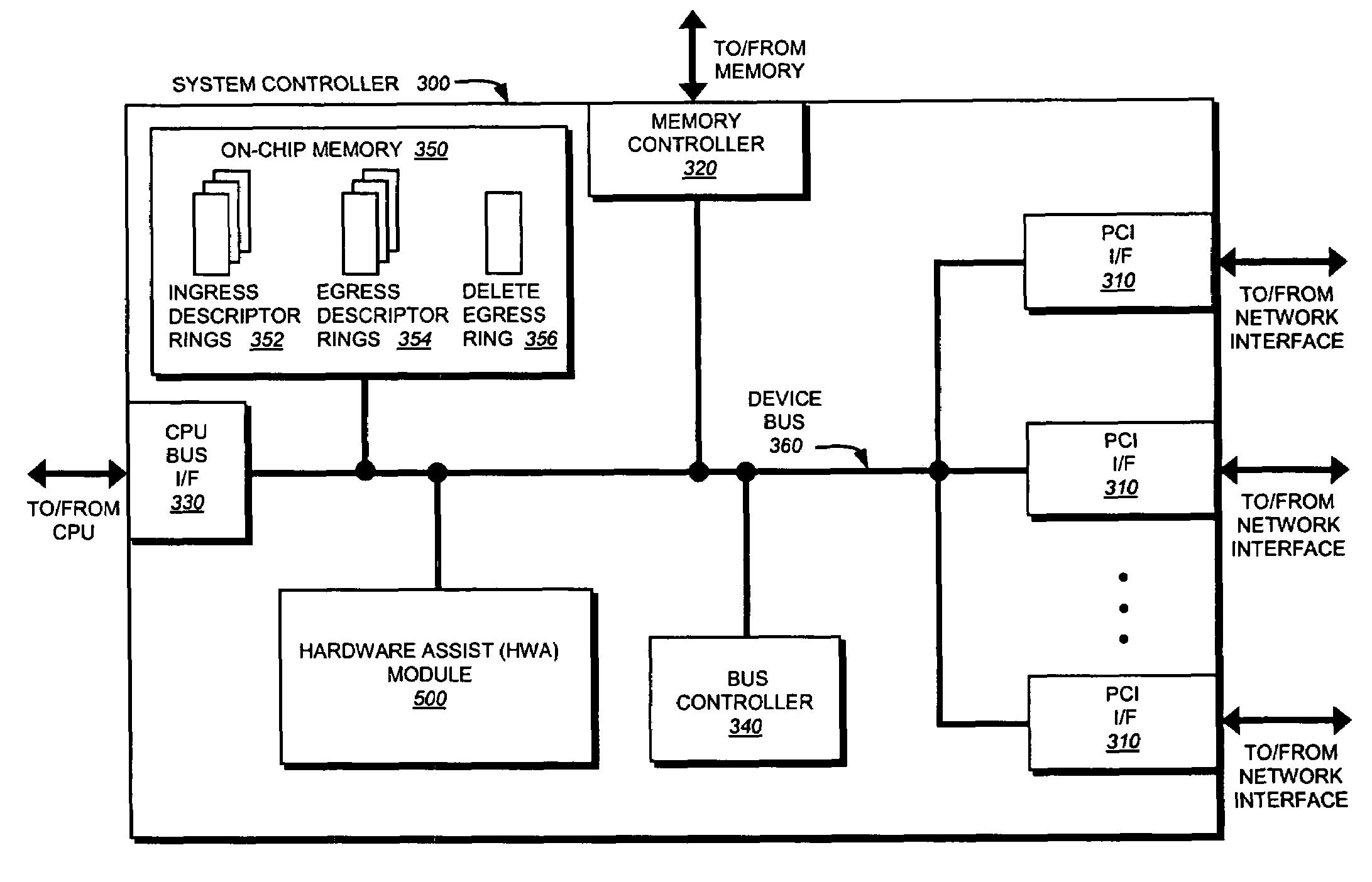
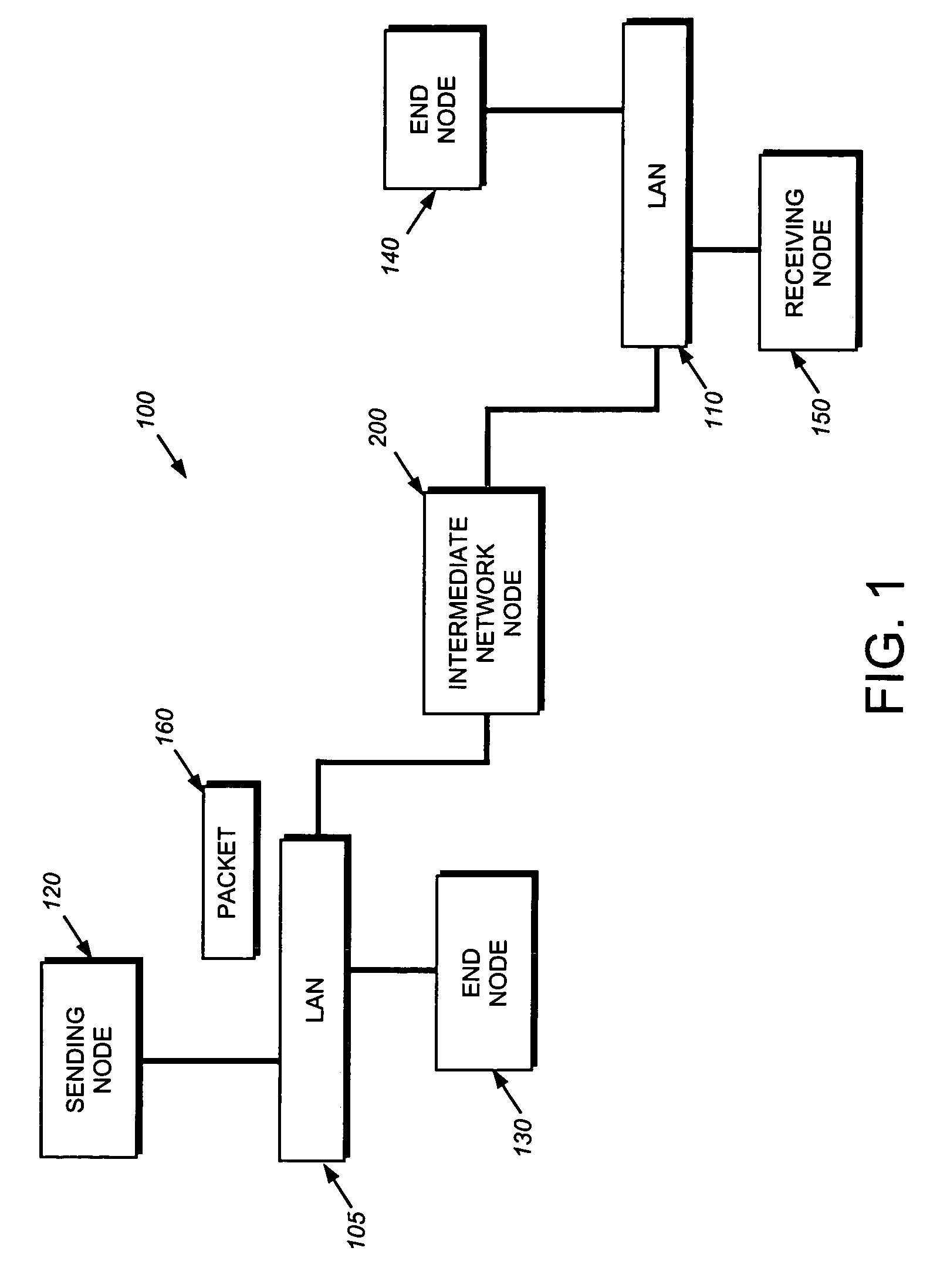
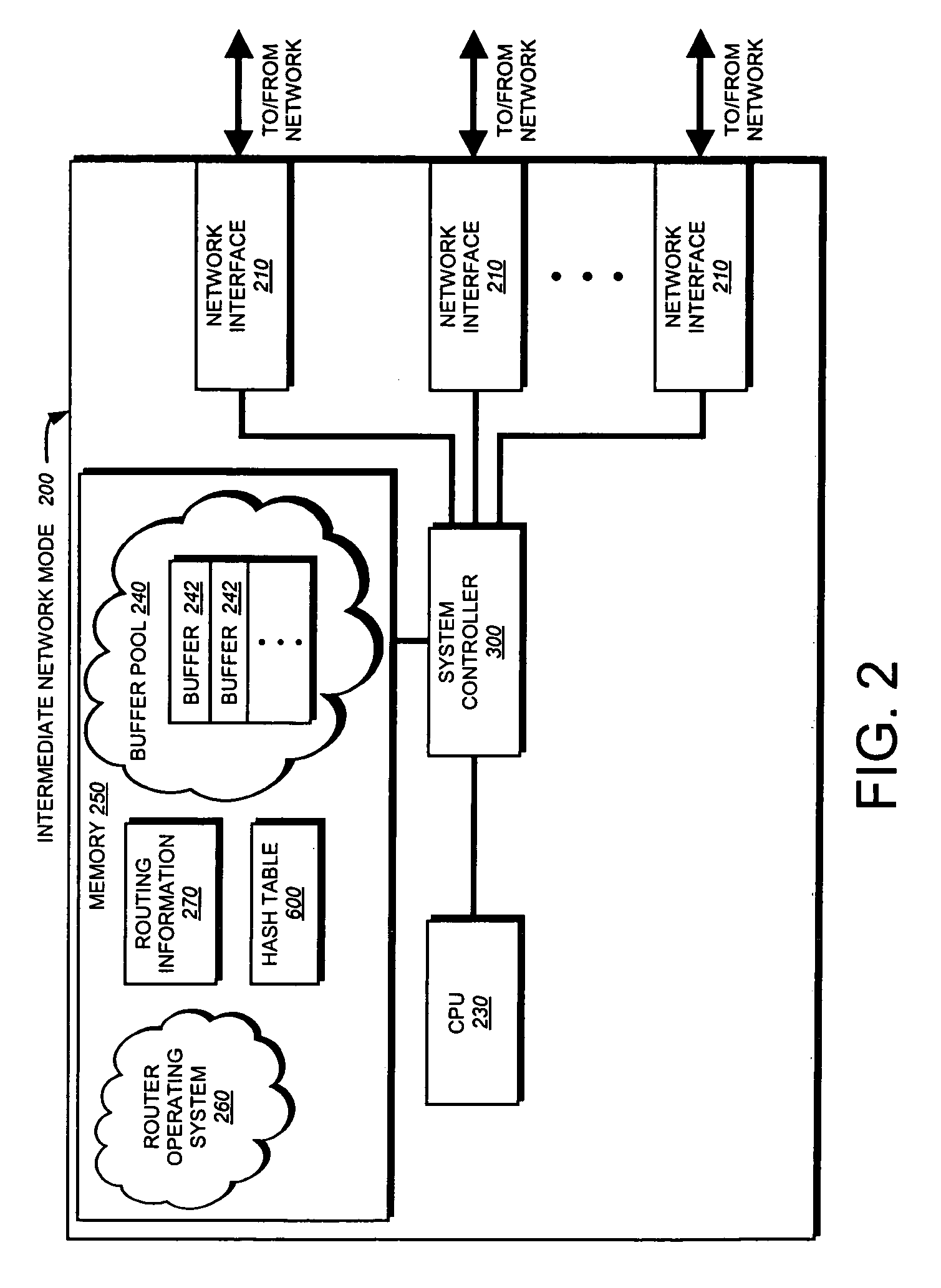
Hardware filtering support for denial-of-service attacks
InactiveUS20050213570A1Processing bandwidthOvercome disadvantagesData switching by path configurationNetwork packetLookup table
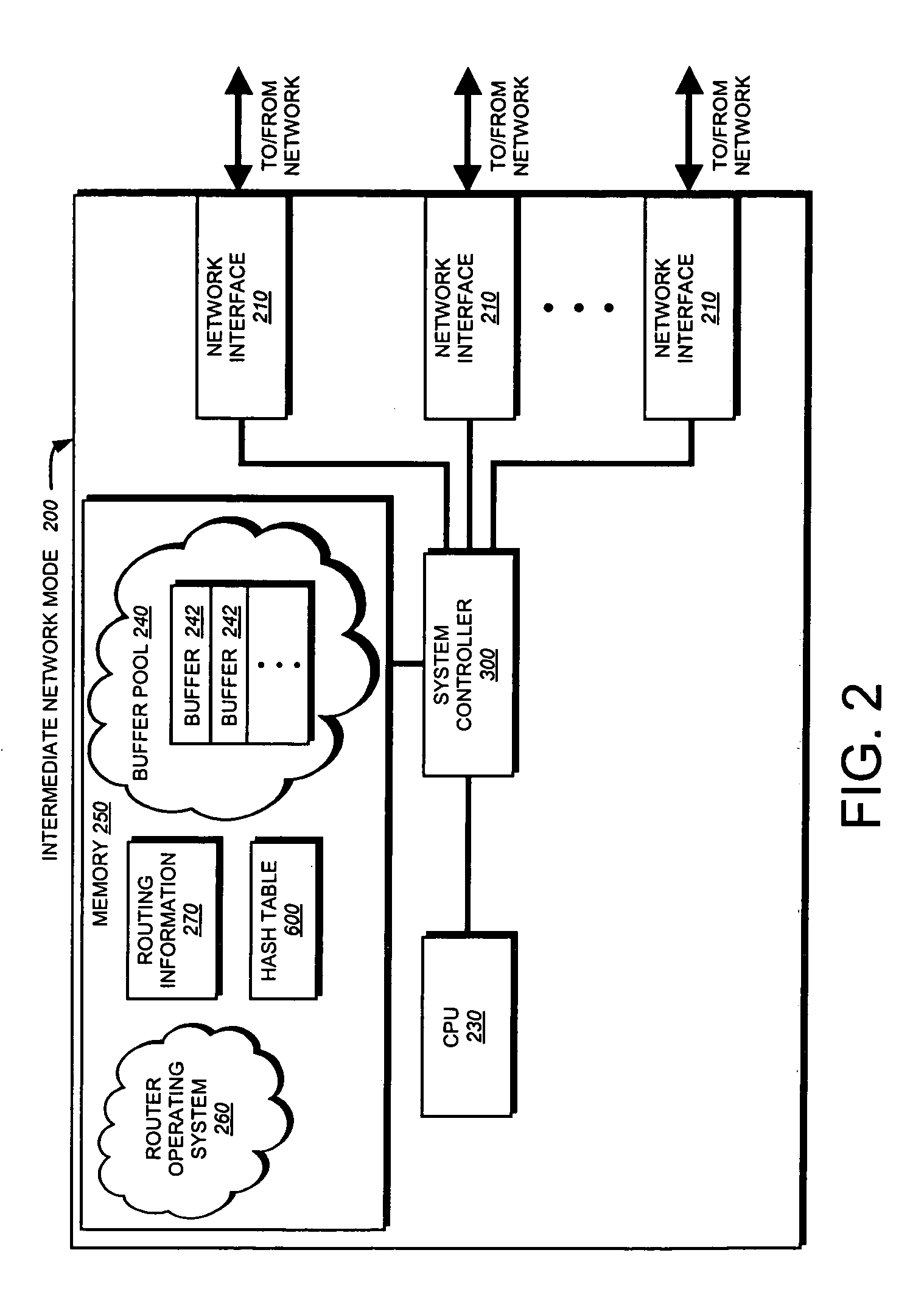
A system and method is provided for automatically identifying and removing malicious data packets, such as denial-of-service (DoS) packets, in an intermediate network node before the packets can be forwarded to a central processing unit (CPU) in the node. The CPU's processing bandwidth is therefore not consumed identifying and removing the malicious packets from the system memory. As such, processing of the malicious packets is essentially “off-loaded” from the CPU, thereby enabling the CPU to process non-malicious packets in a more efficient manner. Unlike prior implementations, the invention identifies malicious packets having complex encapsulations that can not be identified using traditional techniques, such as ternary content addressable memories (TCAM) or lookup tables.
Owner:CISCO TECH INC
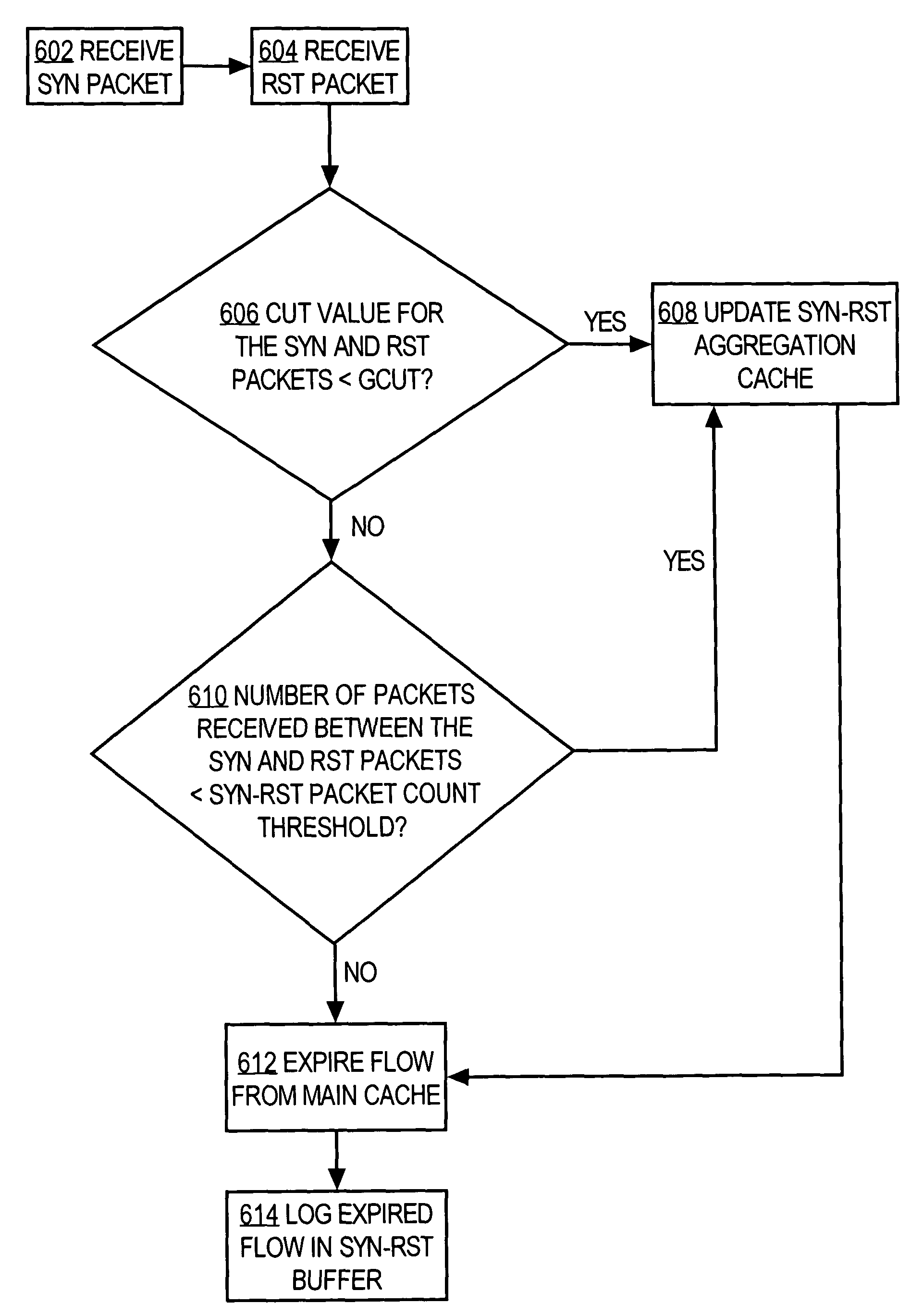
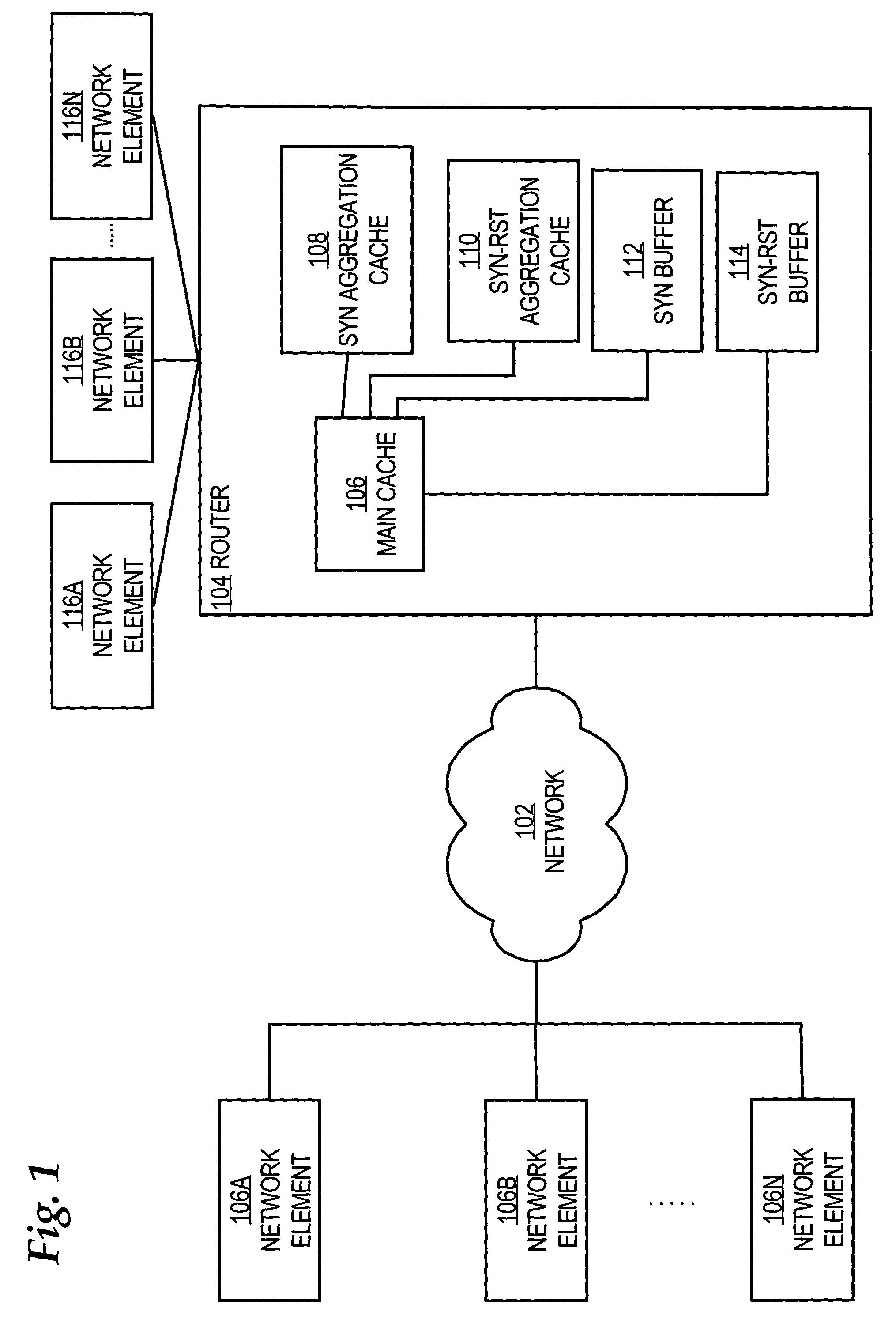
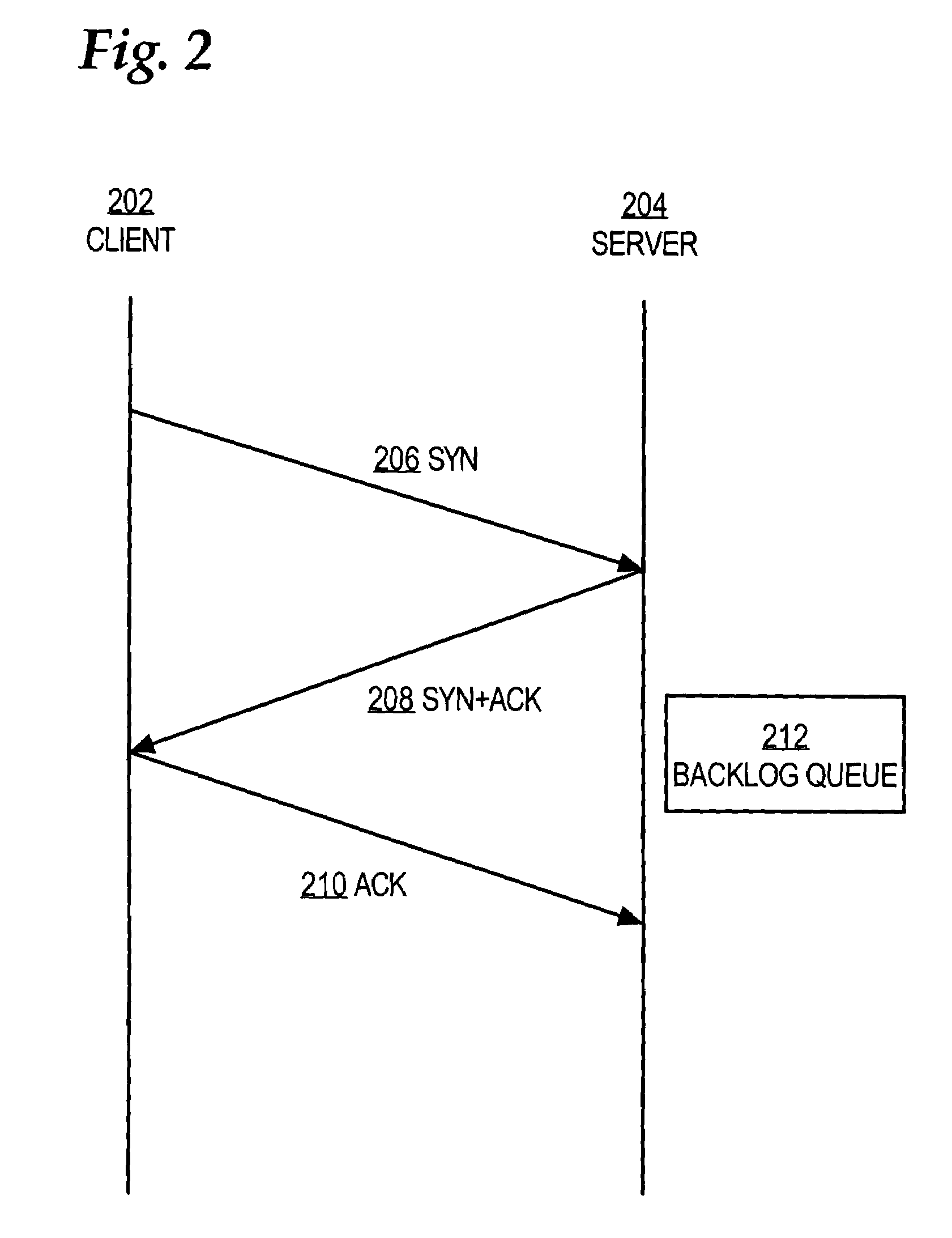
Detection of nonconforming network traffic flow aggregates for mitigating distributed denial of service attacks
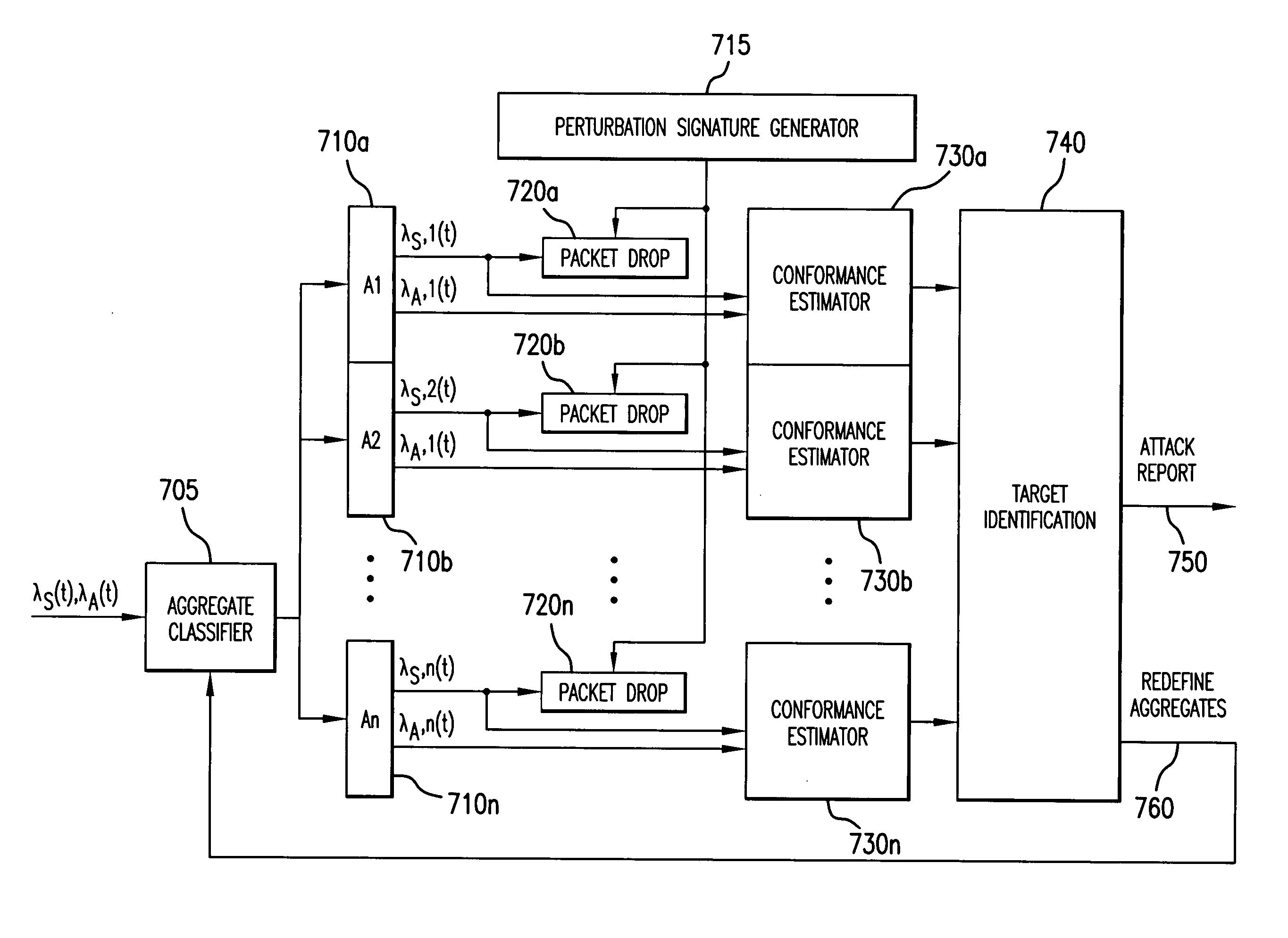
An estimate of a portion of network traffic that is nonconforming to a communication transmission control protocol is used to signal that a distributed denial of service attack may be occurring. Traffic flows are aggregated and packets are intentionally dropped from the flow aggregate in accordance with an assigned perturbation signature. The flow aggregates are observed to determine if the rate of arrival of packets that have a one-to-one transmission correspondence with the dropped packets are similarly responsive to the perturbation signature. By assigning orthogonal perturbation signatures to different routers, multiple routers may perform the test on the aggregate and the results of the test will be correctly ascertained at each router. Nonconforming aggregates may be redefined to finer granularity to determine the node on the network that is under attack, which may then take mitigating action.
Owner:MARYLAND UNIV OF
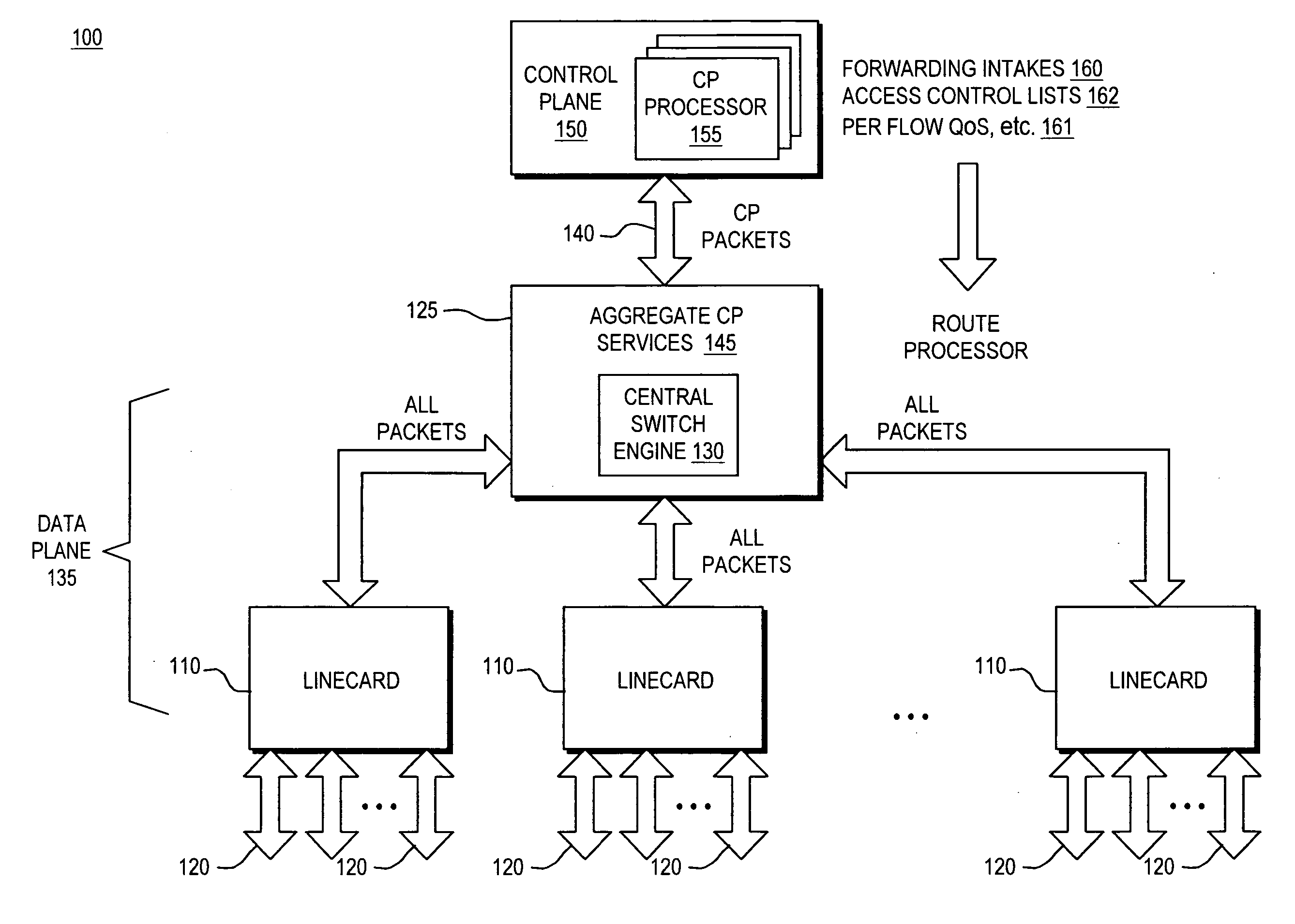
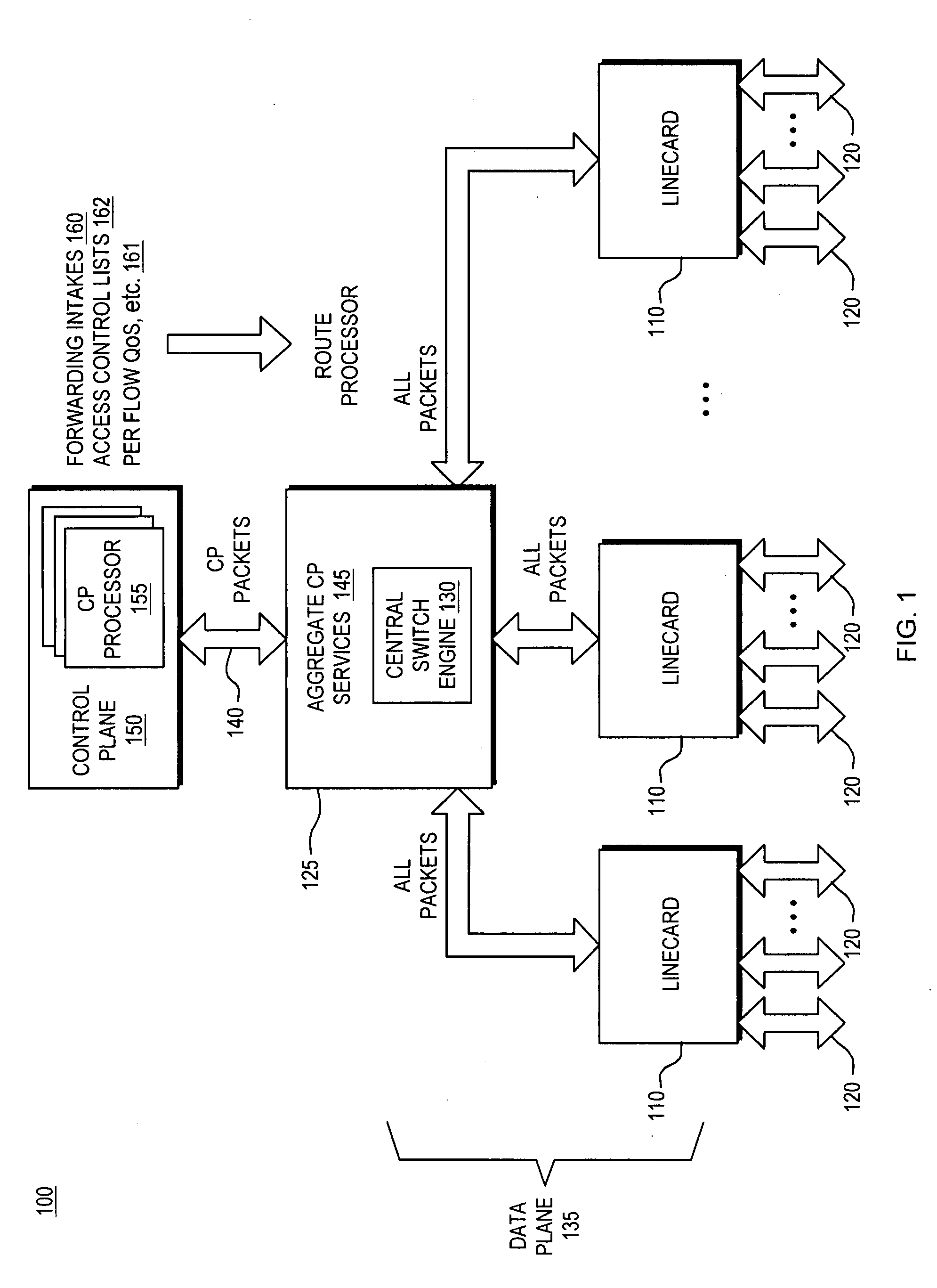
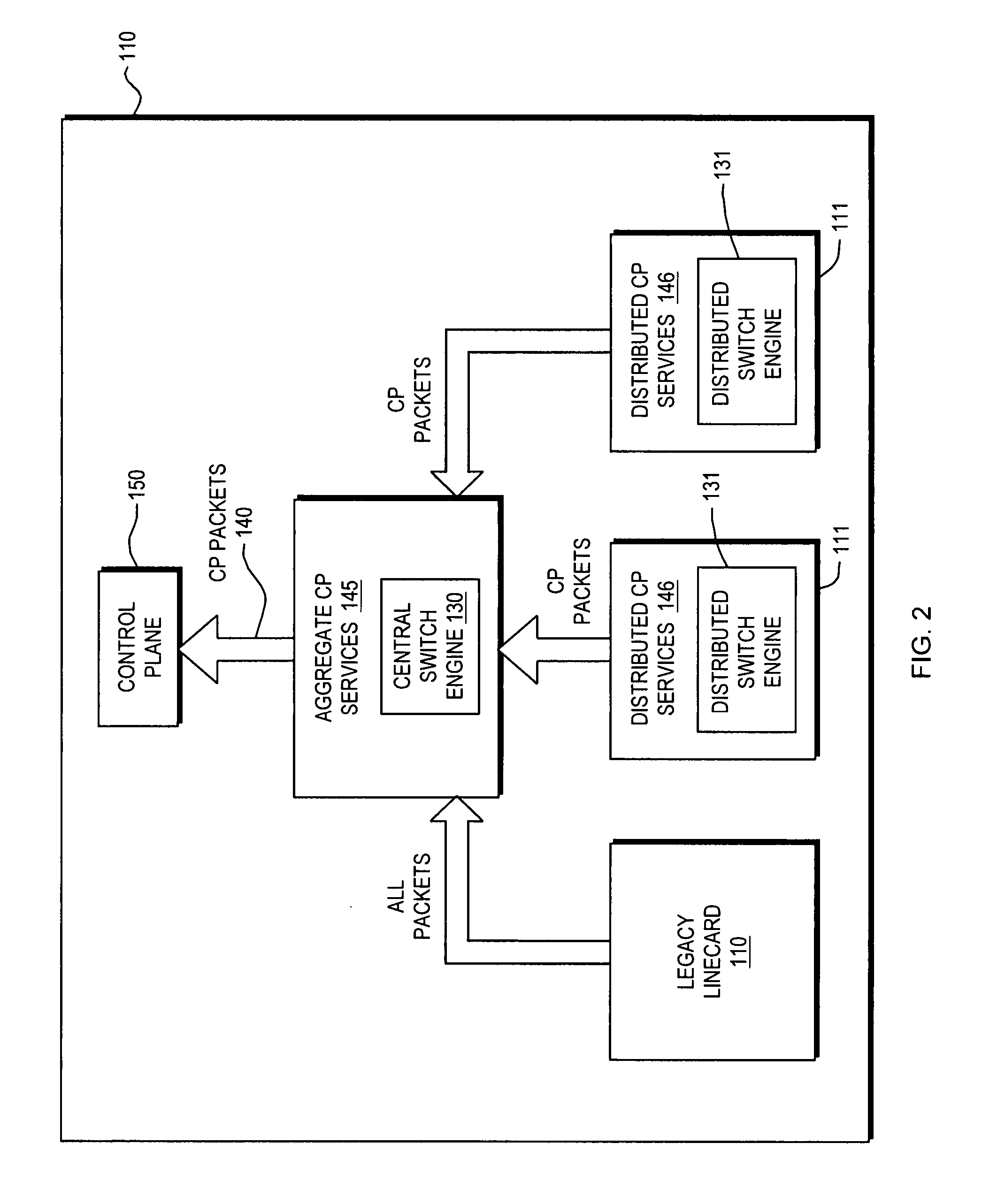
Control plane security and traffic flow management
InactiveUS20070201357A1Improve immunityImprove service qualityMultiplex system selection arrangementsInterconnection arrangementsTraffic capacityQuality of service
An internetworking device that provides improved immunity to Denial of Service attacks, and in general, improved Quality of Service (QoS). An internetworking element or other route processor is composed of two main parts, including a data forwarding plane and a control plane; the control plane runs routing, signaling and control protocols that are responsible for determining the packet forwarding behavior by the data plane. Independent control plane processes may be provided; however, they are considered to be a single network entity that is a uniquely addressable port. Packets thus intended for the control plane always pass through a designated point. As a result, a set of port services unique to the control plane may be applied to the control plane port. These control plane port services thus can be utilized to control all packet traffic entering and exiting the control plane processes as a whole.
Owner:CISCO SYSTEMS INC
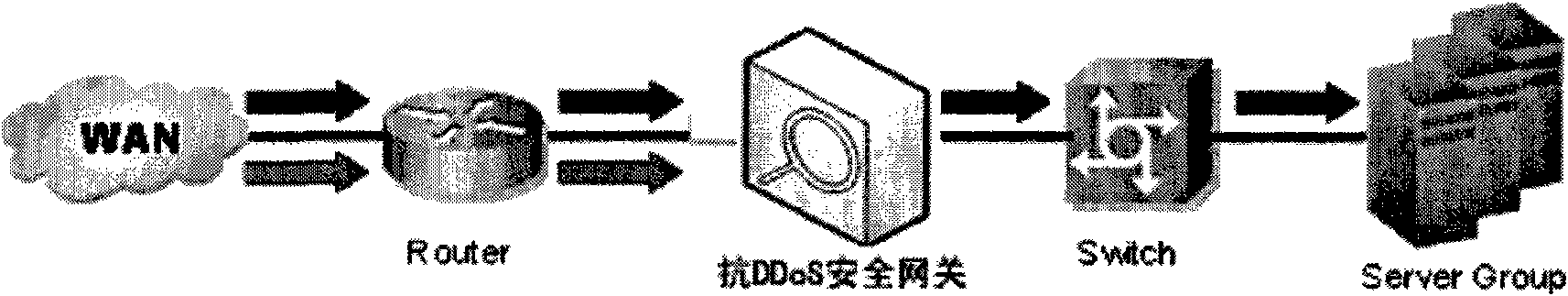
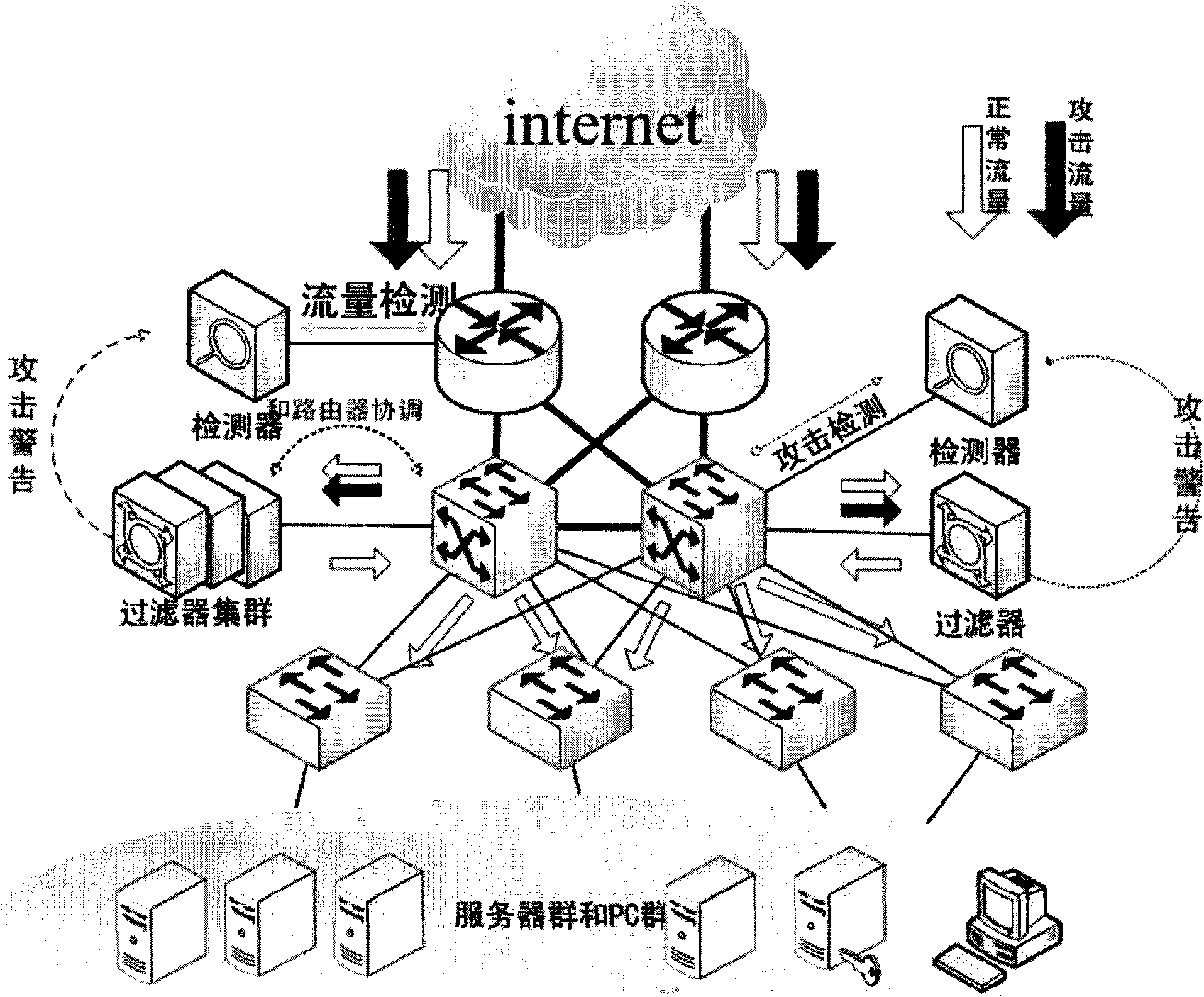
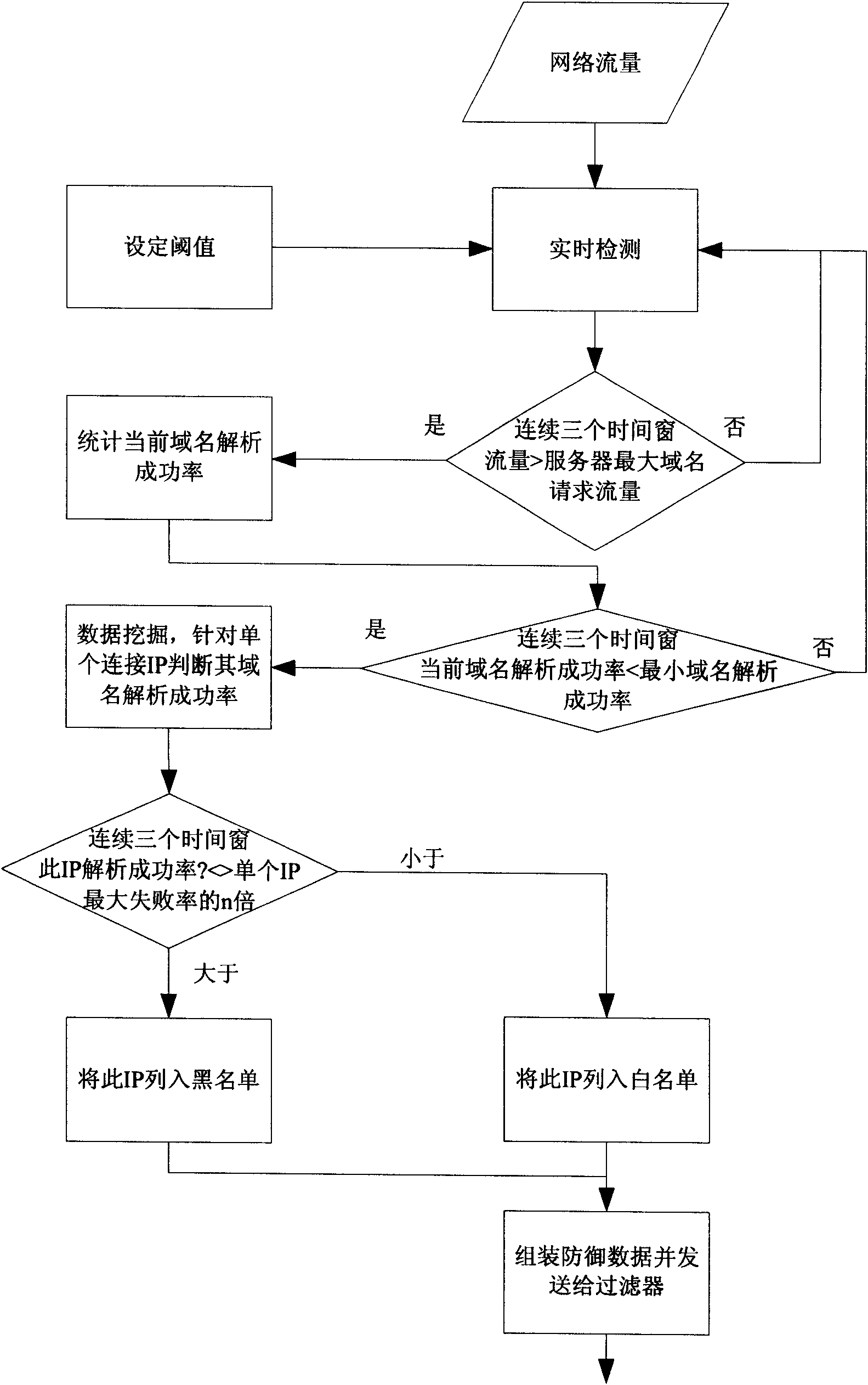
Security gateway system for resisting DDoS attack for DNS service
The invention discloses a high-efficiency anti-DDoS security gateway system, which can effectively detect and defend a DNS denial-of-service attack. The system comprises two core components, namely a detector and a filter. The system supports two deploying ways, namely serial connection and bypass. A detecting method is based on the self-learning network flow state statistic and characteristic disinterment, achieves the detection and positioning of the network abnormal flow by setting network performance parameter thresholds, and can effectively identify the suspected attack flow. A defending method carries out a thought of deep defense, and the system is deployed with two defense steps of attack characteristic defense and baseline defense so as to ensure the attack defending effect of thesystem under normal network condition and the basic defense capacity of the system in the individual and severe attack environment. The methods can effectively improve the security and attack resista nce of a DNS server and can ensure the normal operation of the DNS service.
Owner:ZHONGKE INFORMATION SECURITY COMMON TECH NAT ENG RES CENT CO LTD
Method and apparatus for mitigating distributed denial of service attacks
ActiveUS20150058976A1Memory loss protectionError detection/correctionNetwork addressingDistributed computing
An approach for mitigating distributed denial of service (DDoS) attacks includes assigning a set of temporary network addresses to a hostname for a finite period and assigning one or more other sets of temporary network addresses to the hostname in one or more following finite periods, responding to a hostname lookup request based on the set of temporary network addresses, the one or more other sets of temporary network addresses, or a combination thereof that are active, responding to a network address lookup request based on at least one of the set of temporary network addresses and the one or more other sets of temporary network addresses that is associated with a current one of the finite period or the one or more following finite periods, and retiring the set of temporary network addresses, the one or more sets of temporary network addresses, or a combination thereof after a configurable number of finite periods, wherein no further network address or hostname lookup request is served based on the retired set of temporary network addresses, the retired one or more sets of temporary network addresses, or a combination thereof.
Owner:VERIZON PATENT & LICENSING INC
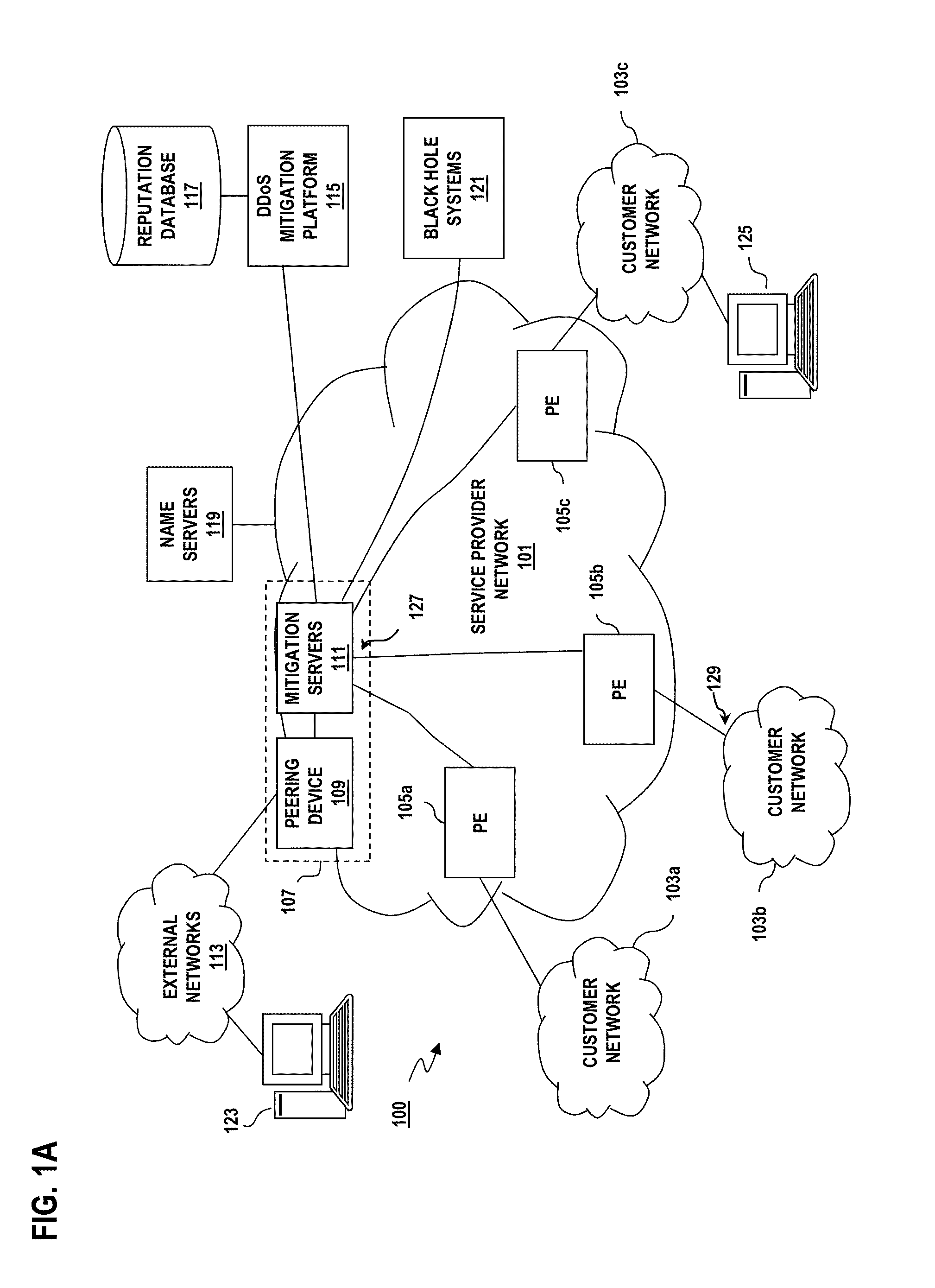
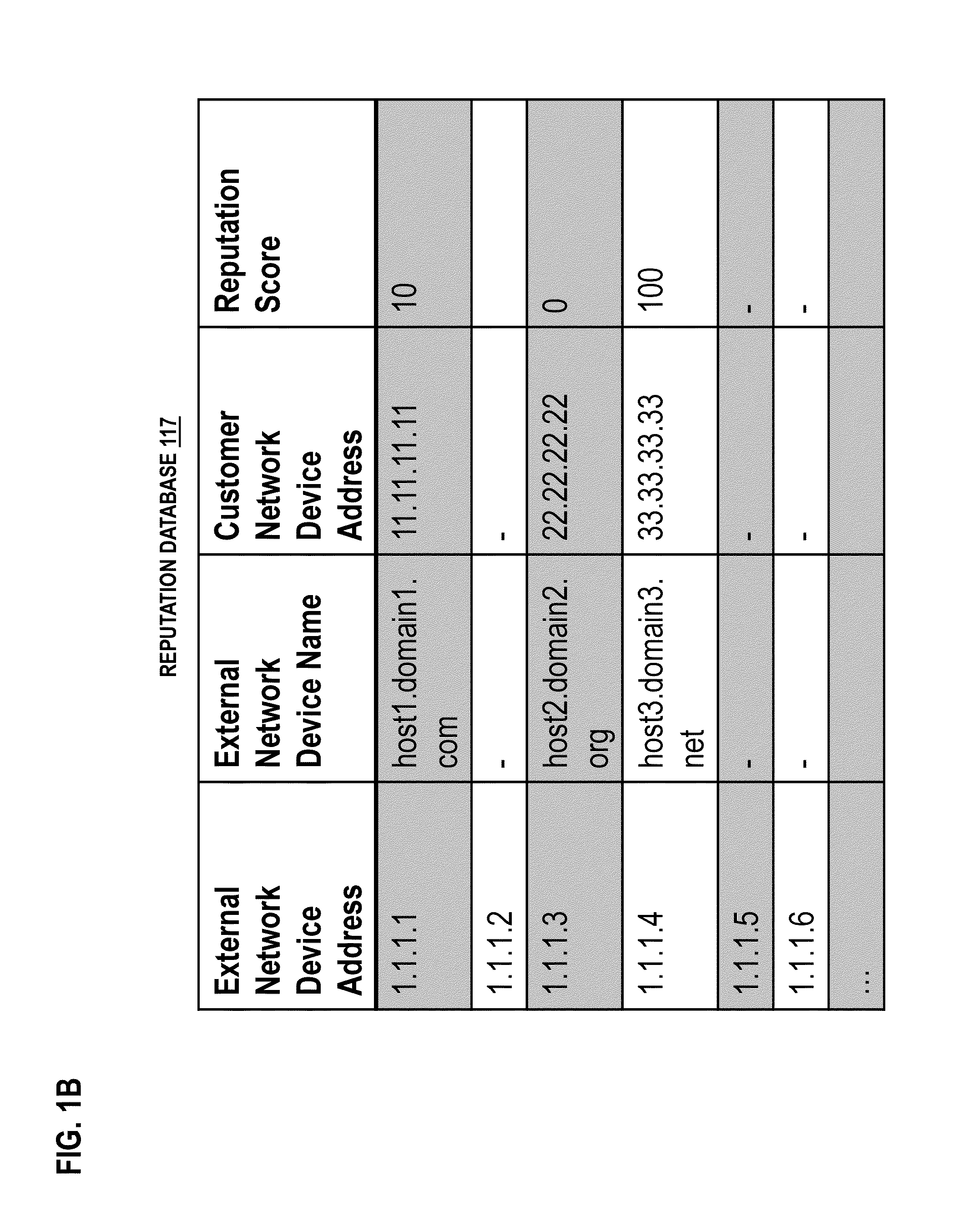
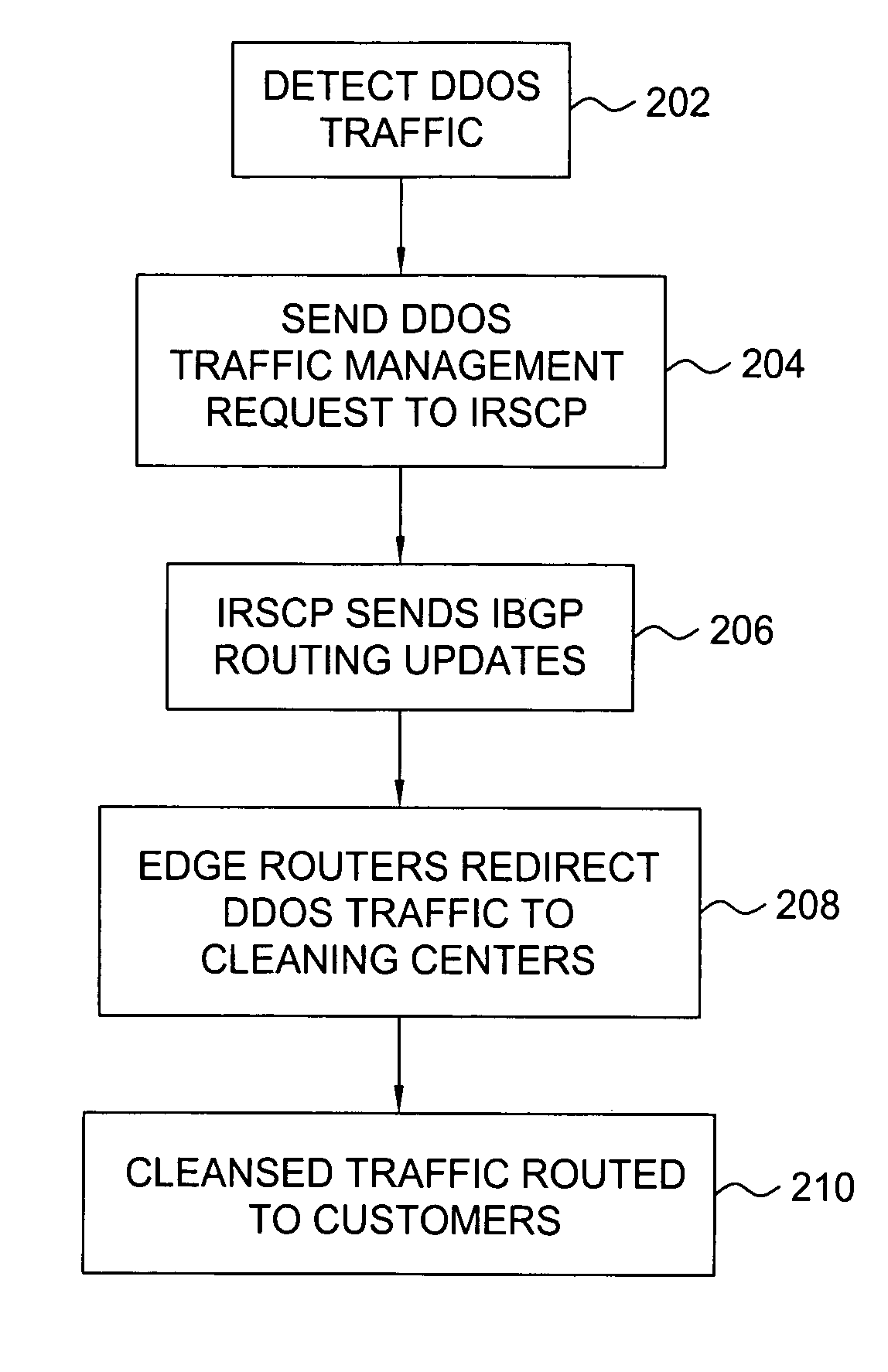
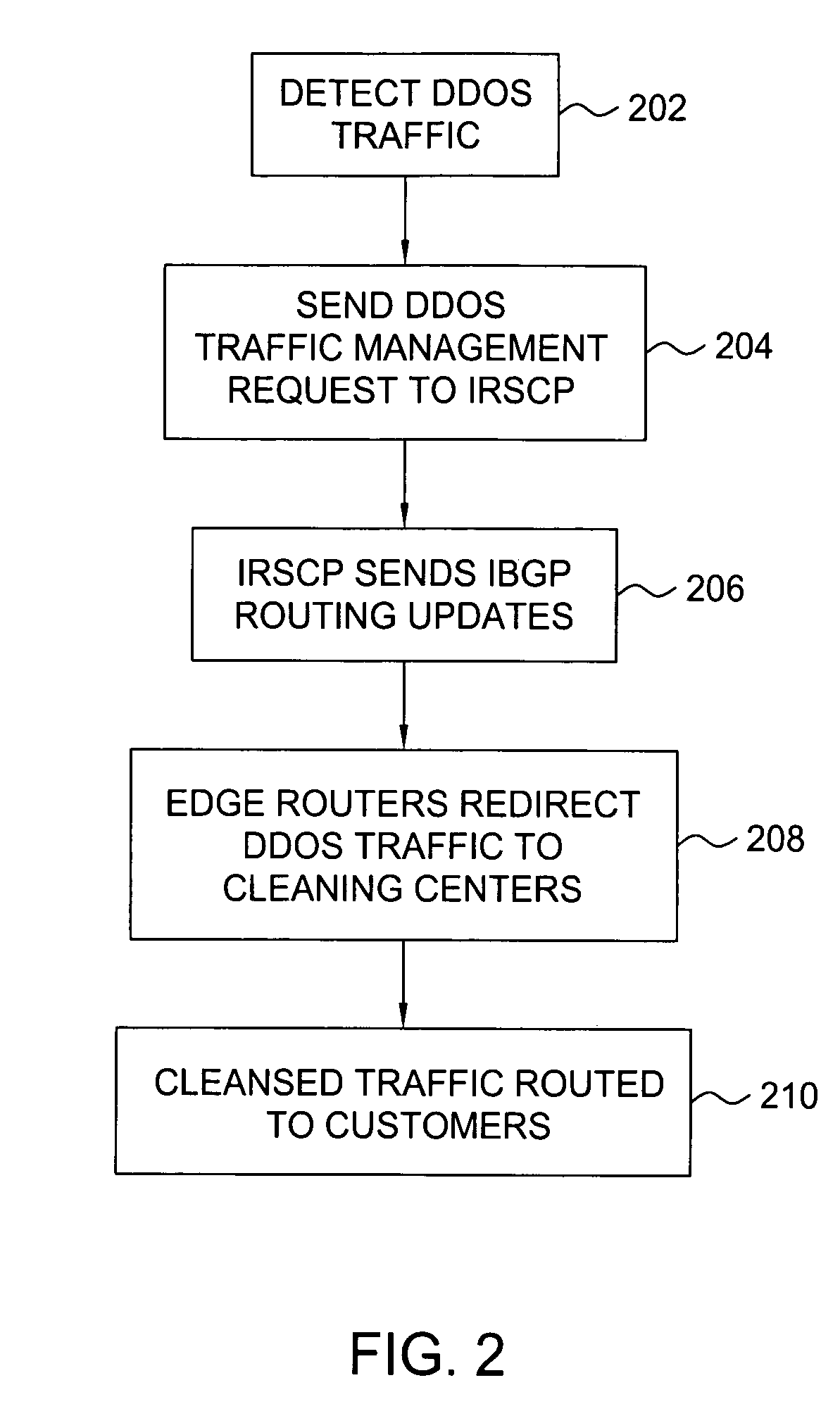
Method and apparatus for traffic control of dynamic denial of service attacks within a communications network
A method and apparatus for providing traffic management for distributed denial of service (DDOS) traffic. Within a communications network, a DDOS detection system monitors network traffic to identify traffic that is designed to attack a particular server within the network and their entry points into the network. A traffic routing control unit is requested to deny service to the DDOS traffic. By selectively manipulating the routing information propagated to network edge routers, the traffic that is denied service is limited to mostly DDOS traffic and is routed to a cleaning center or a null address in the most effective fashion.
Owner:AT&T INTPROP II L P
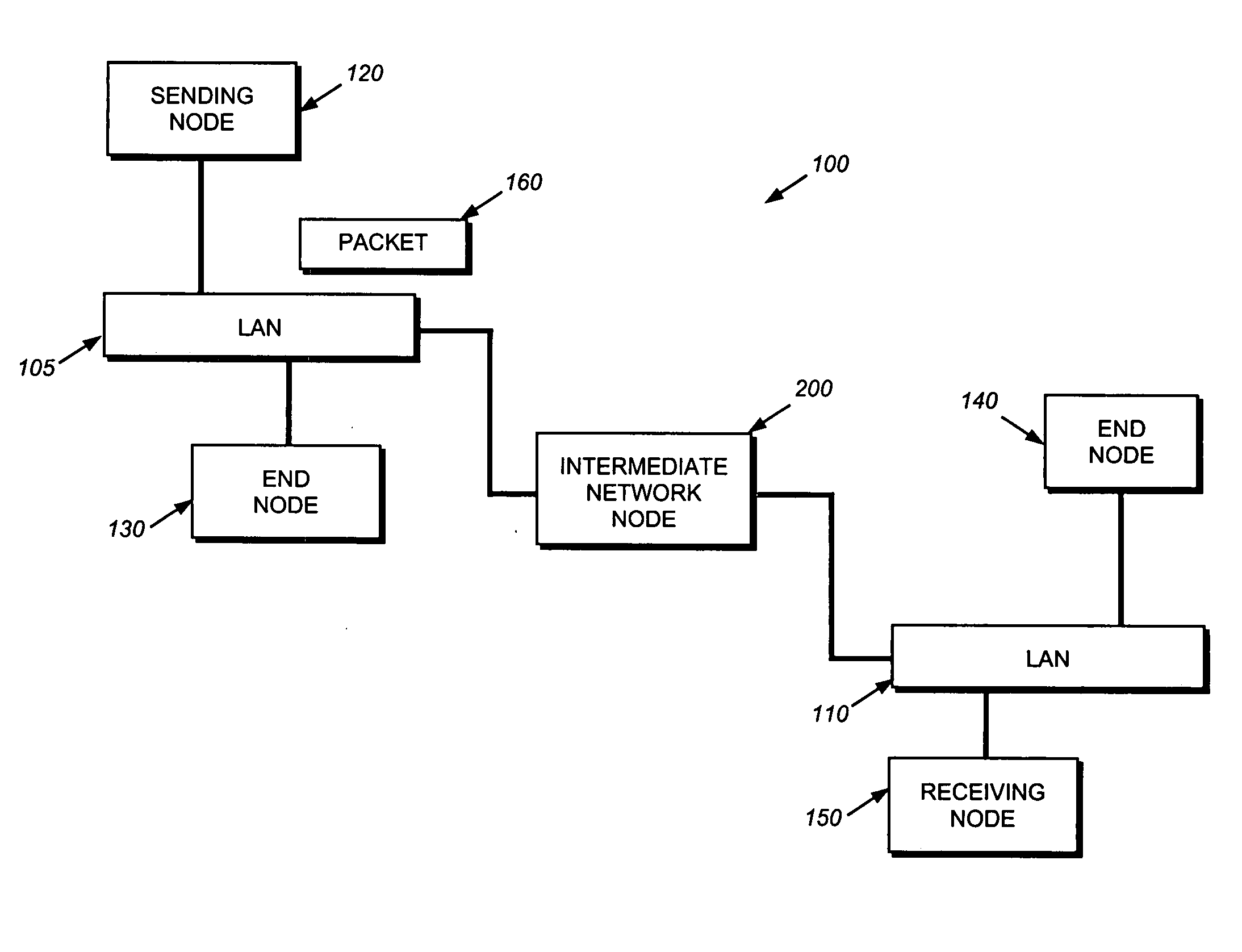
Hardware filtering support for denial-of-service attacks
InactiveUS7411957B2Processing bandwidthOvercome disadvantagesUser identity/authority verificationHardware monitoringNetwork packetLookup table
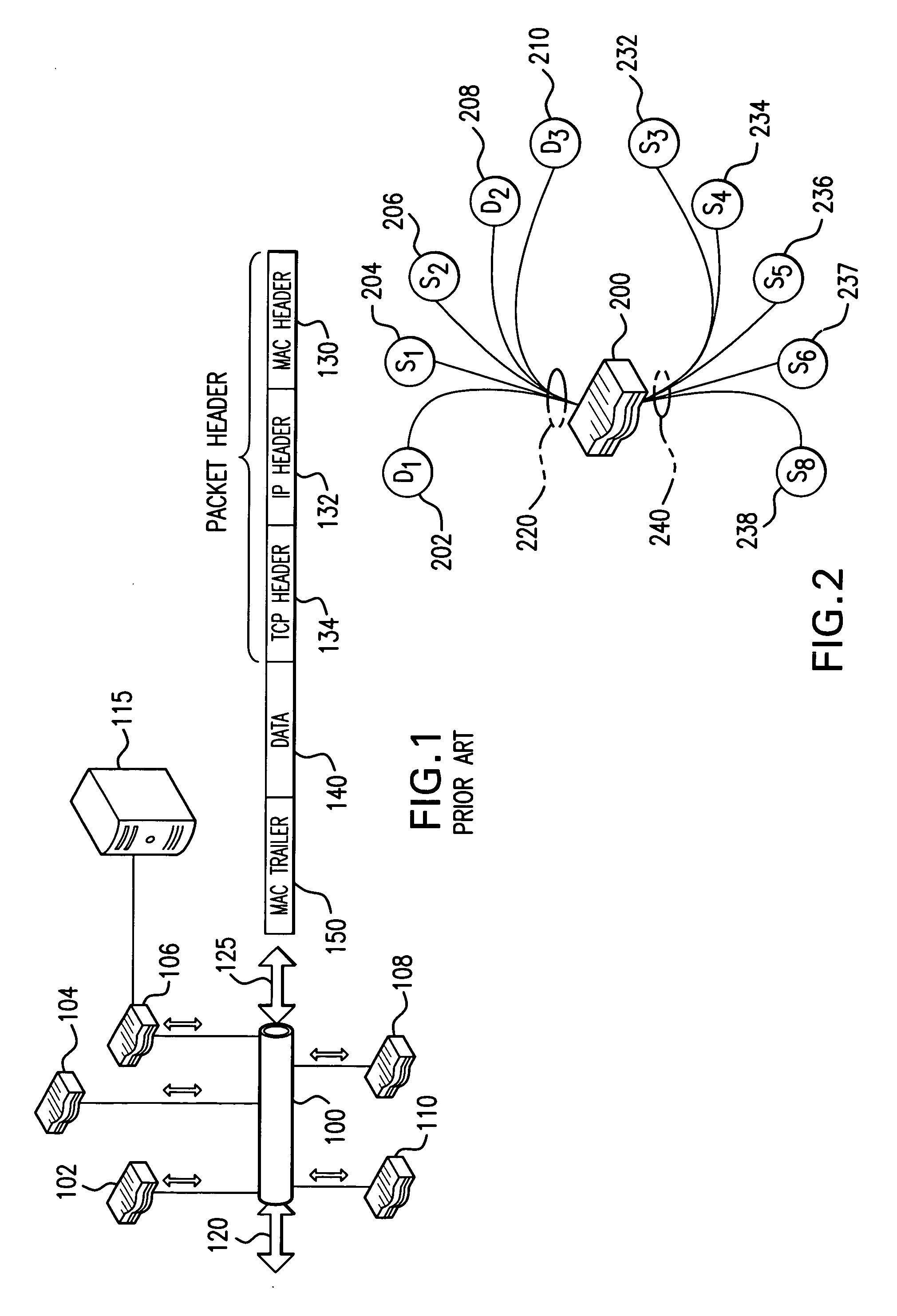
A system and method is provided for automatically identifying and removing malicious data packets, such as denial-of-service (DoS) packets, in an intermediate network node before the packets can be forwarded to a central processing unit (CPU) in the node. The CPU's processing bandwidth is therefore not consumed identifying and removing the malicious packets from the system memory. As such, processing of the malicious packets is essentially “off-loaded” from the CPU, thereby enabling the CPU to process non-malicious packets in a more efficient manner. Unlike prior implementations, the invention identifies malicious packets having complex encapsulations that can not be identified using traditional techniques, such as ternary content addressable memories (TCAM) or lookup tables.
Owner:CISCO TECH INC
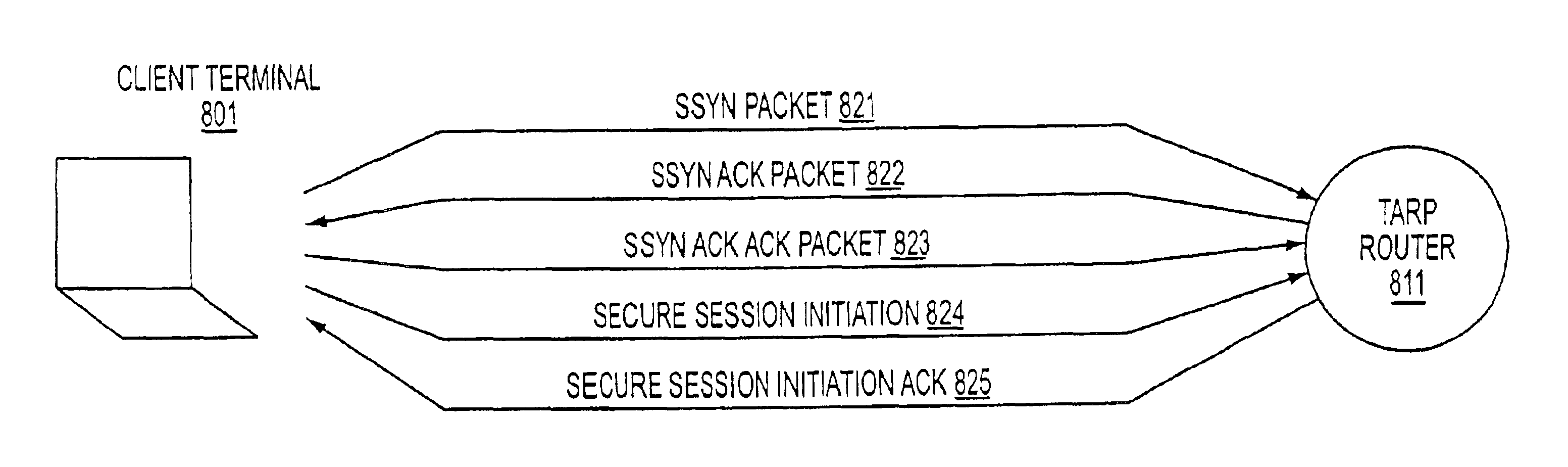
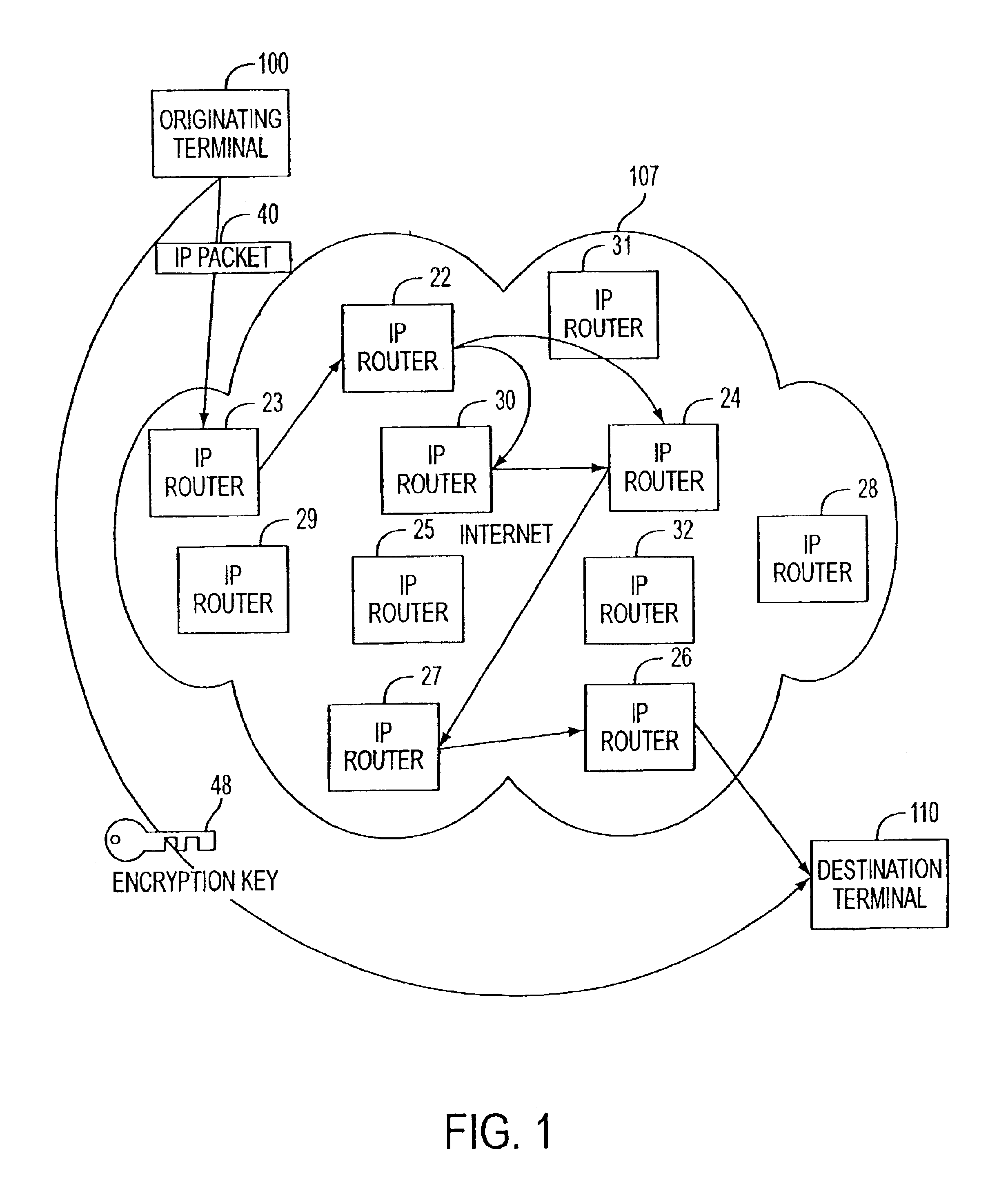
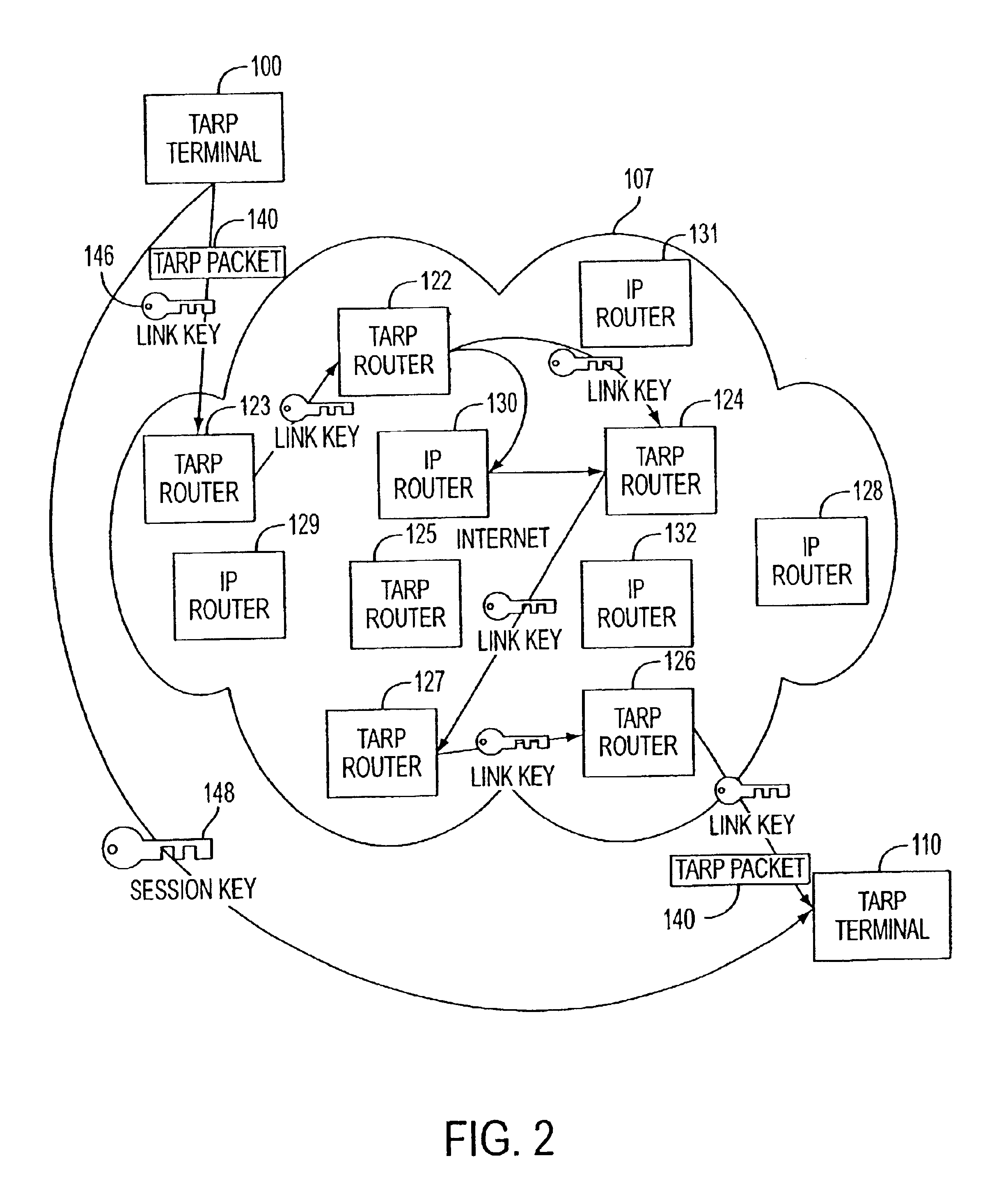
Agile network protocol for secure communications with assured system availability
InactiveUS6907473B2Prevents denial-of-service attackAvoid attackError detection/correctionMultiple digital computer combinationsSecure communicationPrivate network
A plurality of computer nodes communicate using seemingly random Internet Protocol source and destination addresses. Data packets matching criteria defined by a moving window of valid addresses are accepted for further processing, while those that do not meet the criteria are quickly rejected. Improvements to the basic design include (1) a load balancer that distributes packets across different transmission paths according to transmission path quality; (2) a DNS proxy server that transparently creates a virtual private network in response to a domain name inquiry; (3) a large-to-small link bandwidth management feature that prevents denial-of-service attacks at system chokepoints; (4) a traffic limiter that regulates incoming packets by limiting the rate at which a transmitter can be synchronized with a receiver; and (5) a signaling synchronizer, that allows a large number of nodes to communicate with a central node by partitioning the communication function between two separate entities.
Owner:VIRNETX
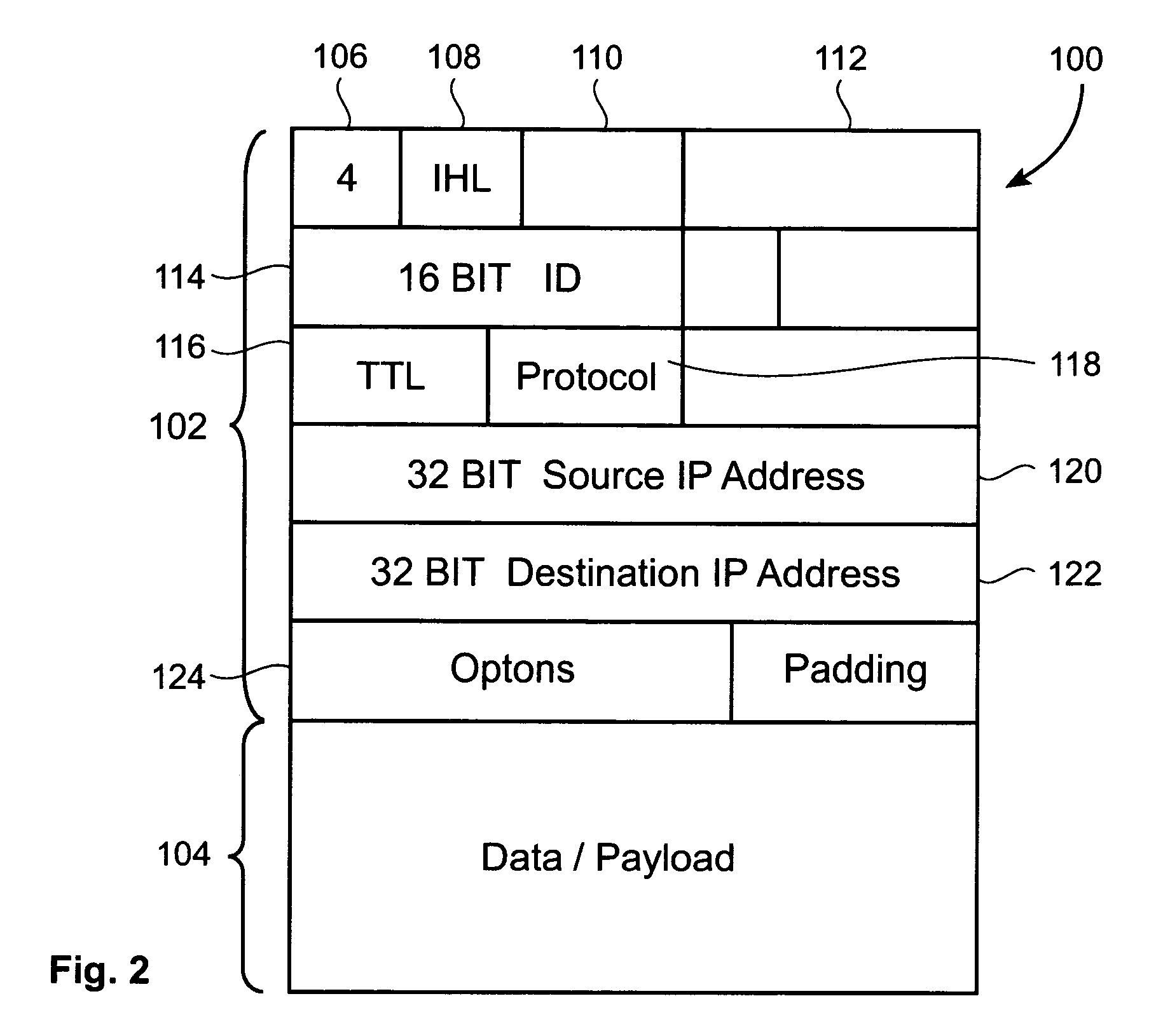
Identifying a distributed denial of service (DDoS) attack within a network and defending against such an attack
InactiveUS20060010389A1Mitigate and obviate disadvantageData taking preventionDigital computer detailsData packThe Internet
The invention provides methods, apparatus and systems for detecting distributed denial of service (DDoS) attacks within the Internet by sampling packets at a point or points in Internet backbone connections to determine a packet metric parameter. The packet metric parameter which might comprise the volume of packets received is analysed over selected time intervals with respect to specified geographical locations in which the hosts transmitting the packets are located. The expected behaviour can be employed to identify traffic distortions revealing a DDoS attack. In a complementary aspect, the invention provides a method of authenticating packets at routers in order to elevate the QoS of authenticated packets. This method can be used to block or filter packets and can be used in conjunction with the DDoS attack detection system to defend against DDoS attacks within the Internet in a distributed manner.
Owner:IBM CORP
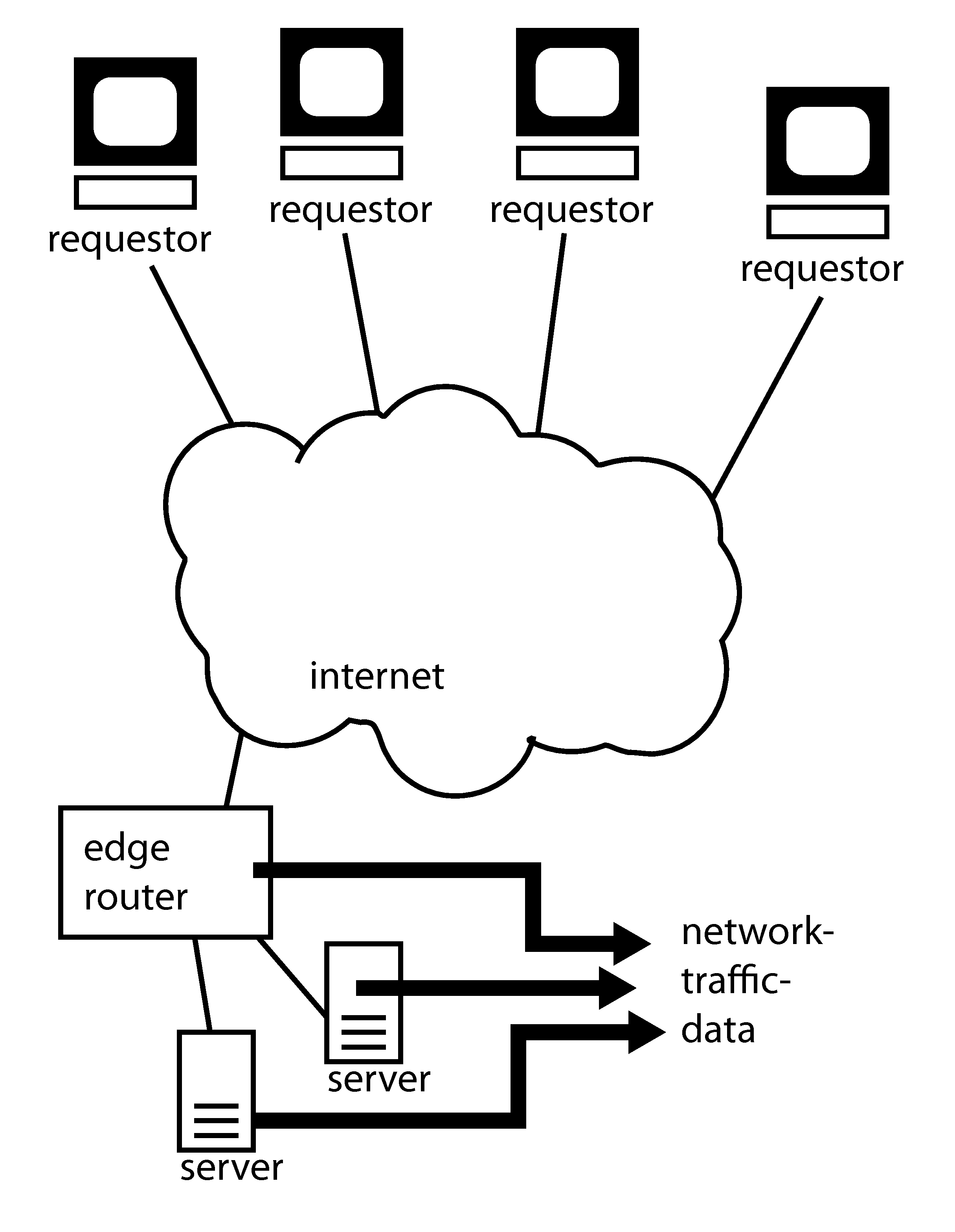
Detecting and mitigating denial of service attacks
InactiveUS20120174220A1Memory loss protectionError detection/correctionRate ratioReal-time computing
Embodiments of this invention provide methods for detecting a denial of service attack (DoS) and isolating traffic that relates to the attack. The method may begin by collecting network traffic data by observing individual packets carried over the network. The data may then be compiled into a time series comprising network traffic data relating successive time-intervals. A difference value based upon the entry in the time series for a large time-window and for a small time-window. A deviation score may then be determined by calculating the ratio of the difference values. The deviation score may indicate whether an attack occurred. In an embodiment of the invention, an attack is deemed to occur if the deviation score is between 0.6 and 1.4.
Owner:VERISIGN
Preventing HTTP server attacks
InactiveUS7389354B1Improve protectionMemory loss protectionVolume/mass flow measurementBroadcast communication networkDenial-of-service attack
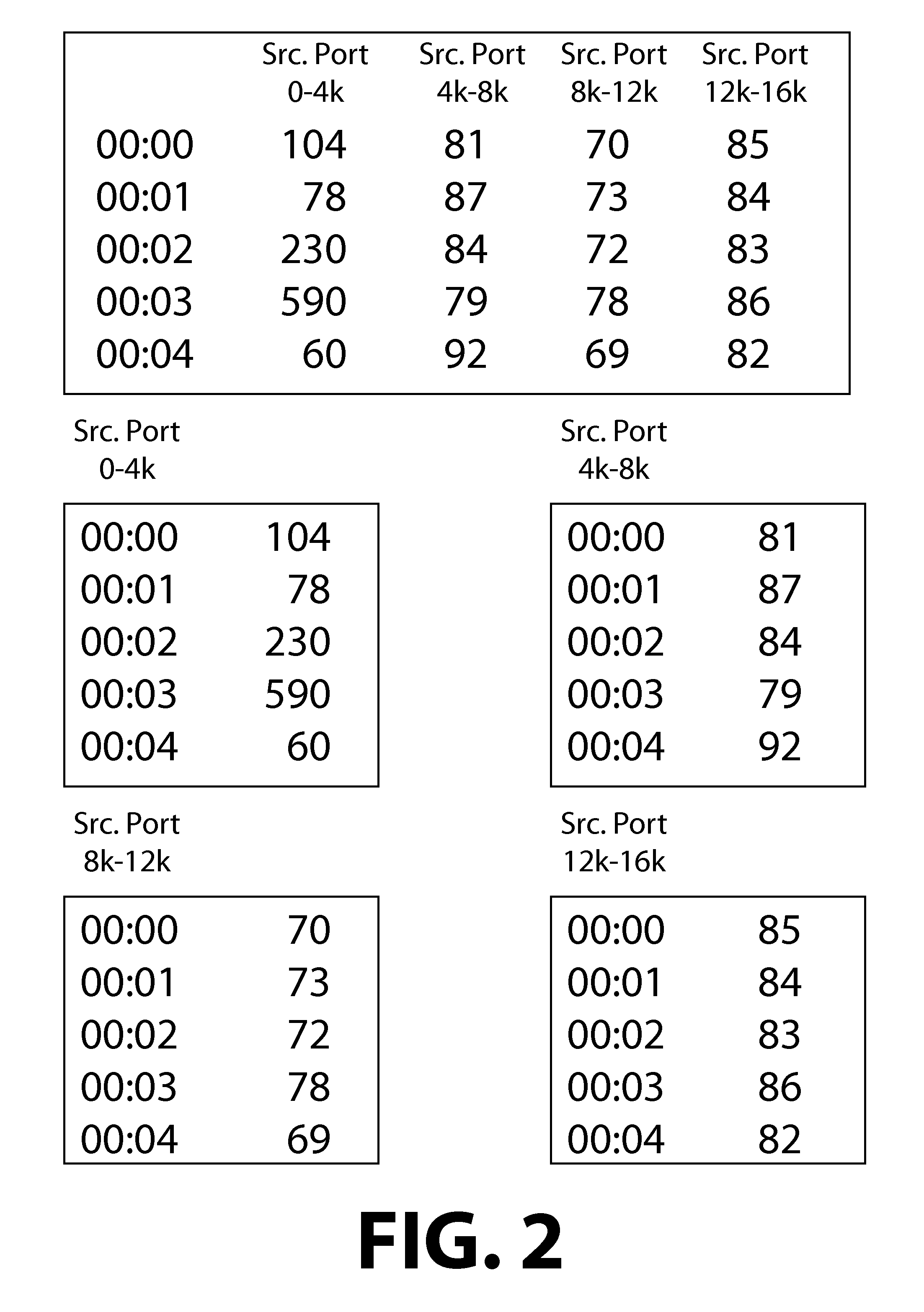
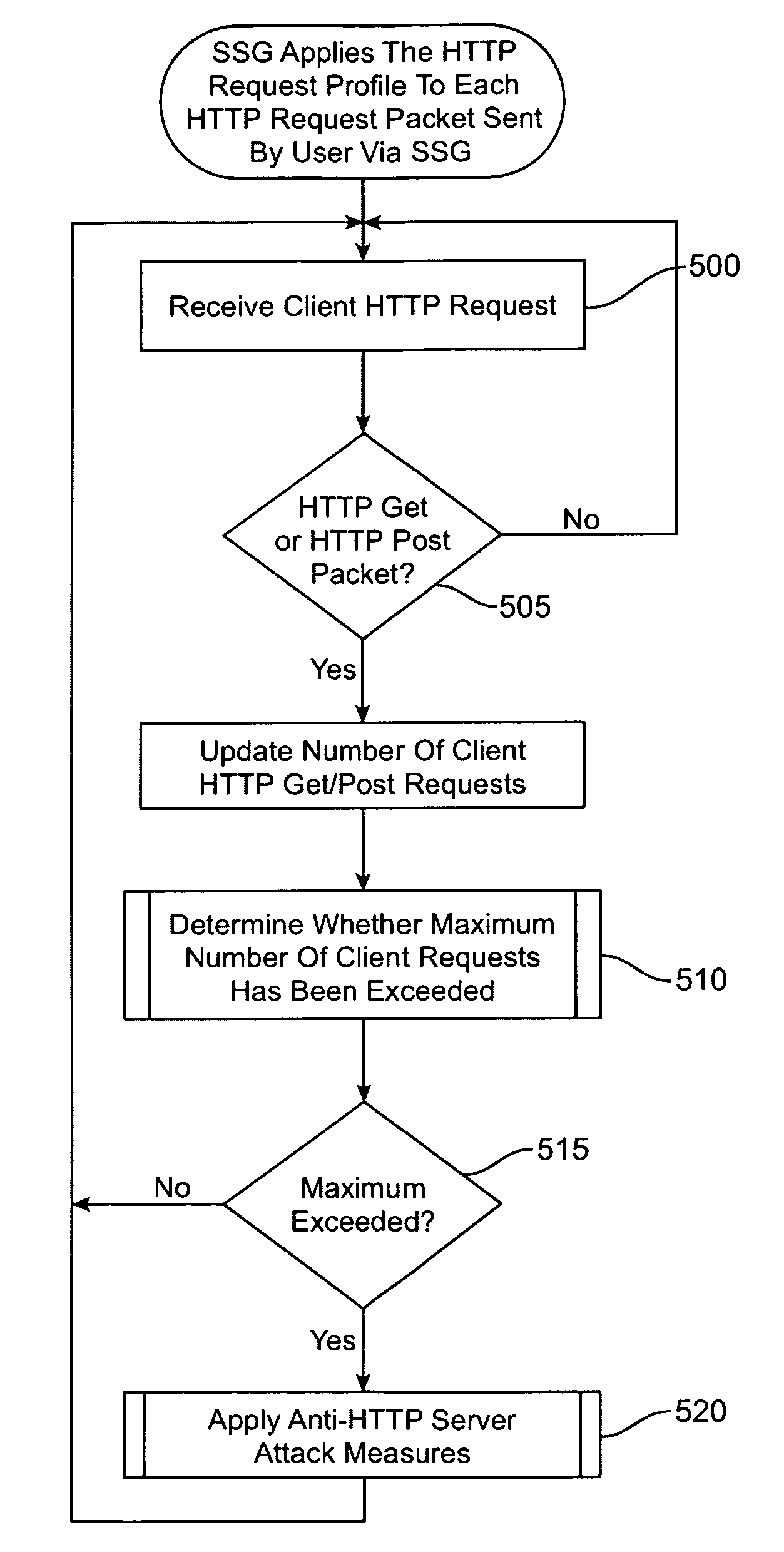
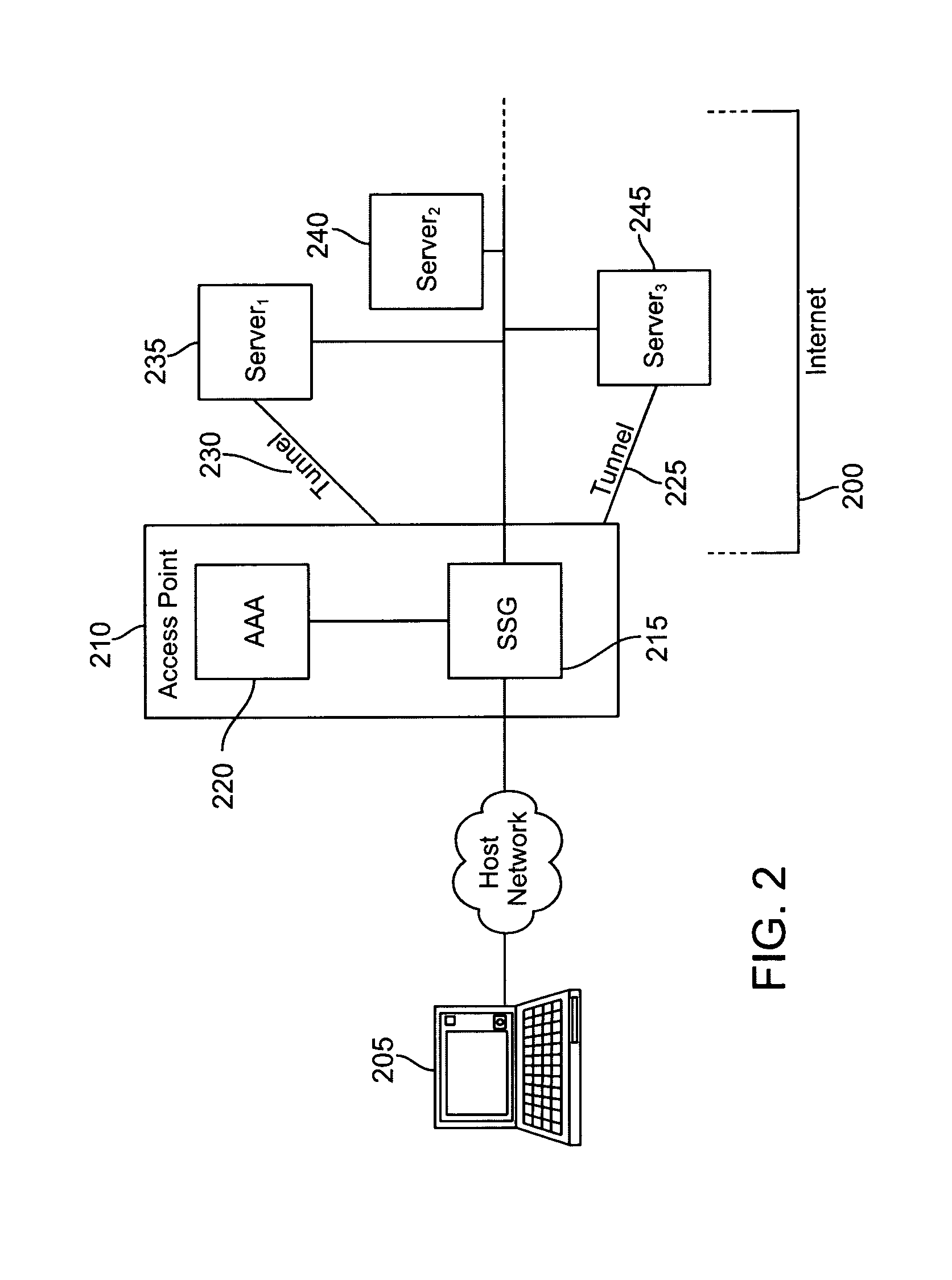
A method for preventing denial of service attacks against Hypertext Transfer Protocol (HTTP) servers includes receiving a HTTP request from a subscriber using a first communication network coupled to at least one other communication network, receiving a profile for the subscriber, filtering the request to determine whether the subscriber is authorized to make the request based upon the profile and forwarding the request to the other communication network when the subscriber is authorized to make the request. An apparatus capable of preventing denial of service attacks against HTTP servers includes a profile request generator capable of generating a profile request based upon a HTTP request received from a subscriber using a first communication network, a filter capable of determining whether the request is authorized based upon the requested profile and an authorizer capable of allowing the request to be forwarded on at least one other communication network coupled to the first communication network.
Owner:CISCO TECH INC
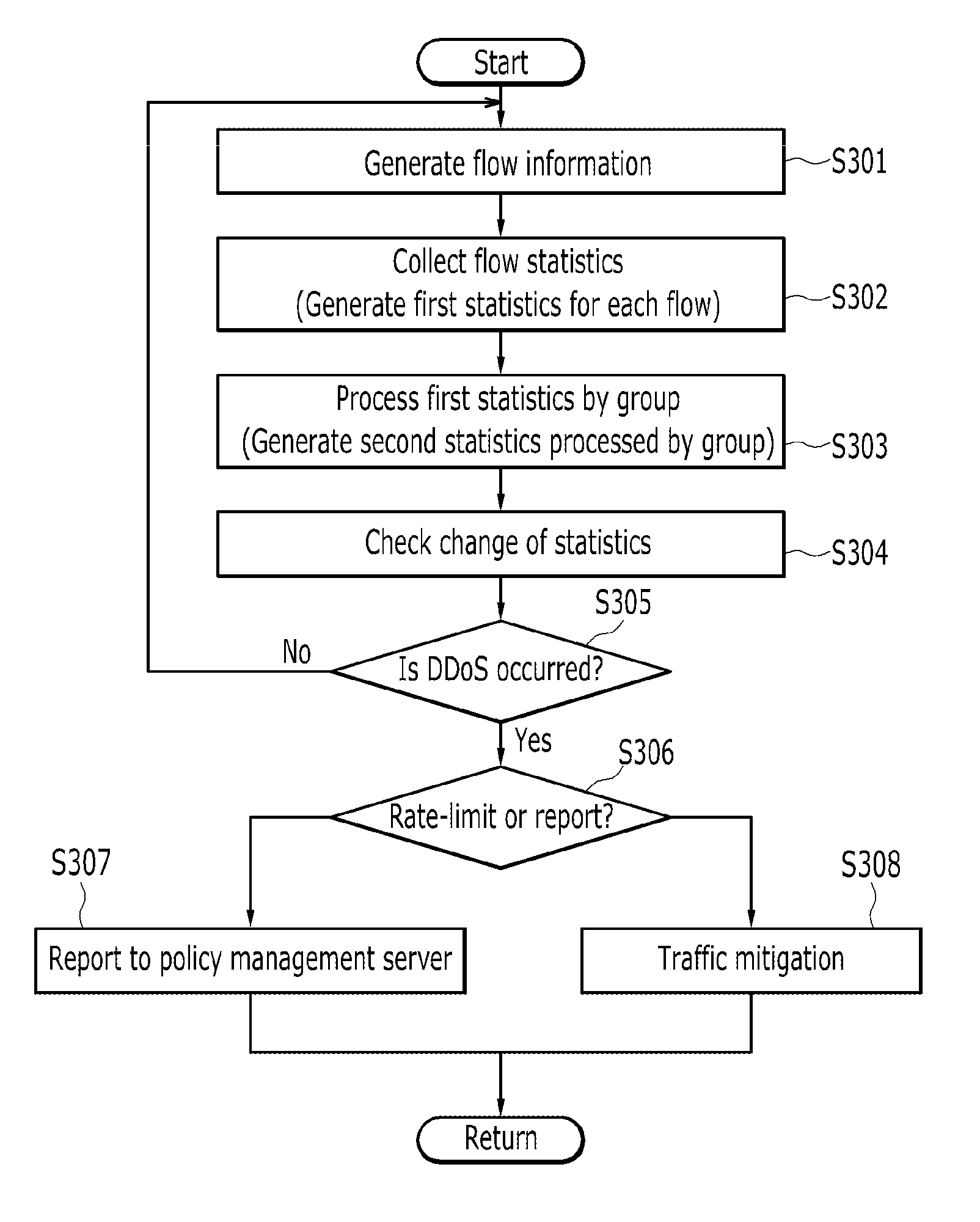
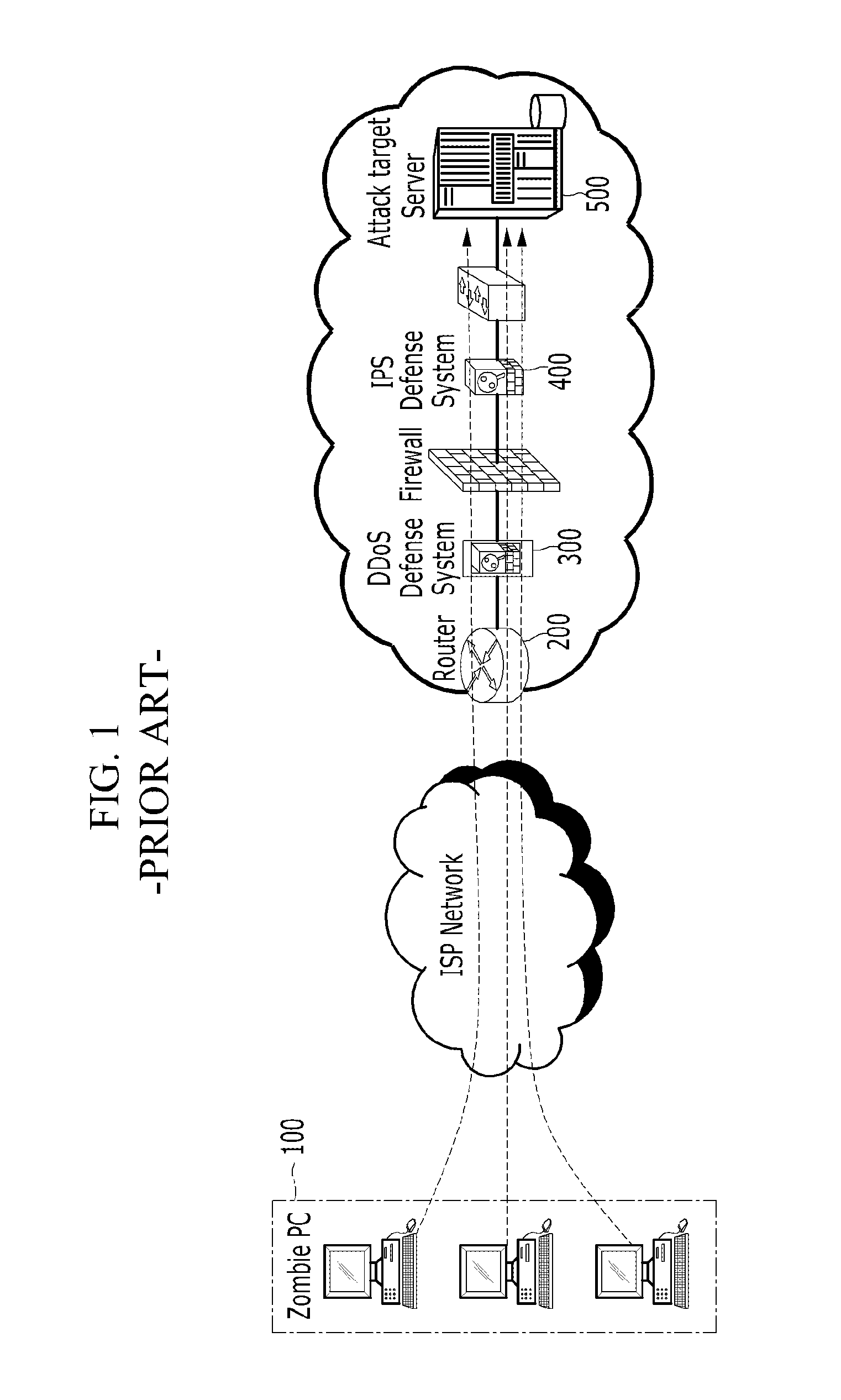
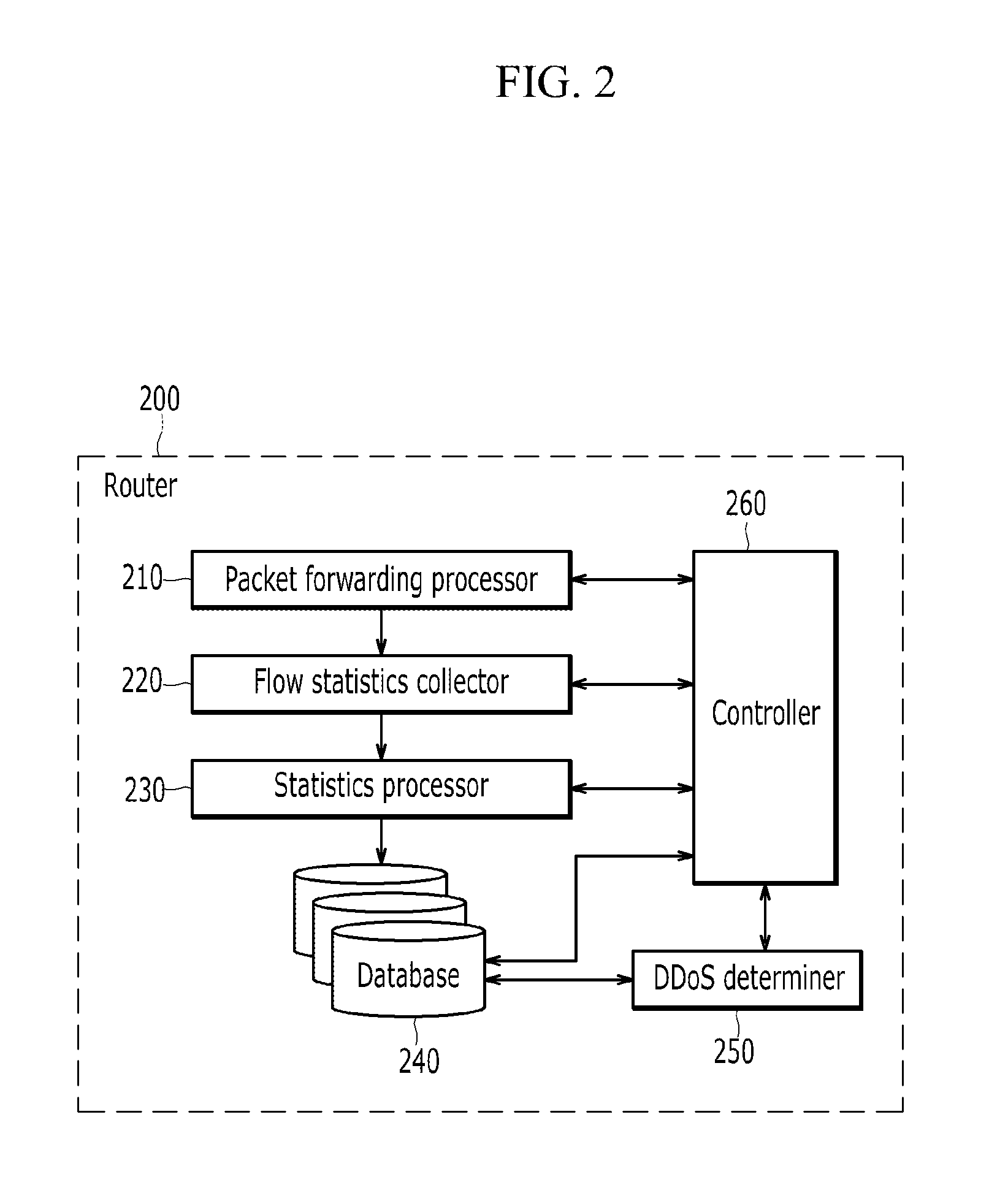
Method and system for ddos traffic detection and traffic mitigation using flow statistics
InactiveUS20110138463A1Memory loss protectionError detection/correctionTraffic capacityNetwork connection
Disclosed are a method and system for distributed denial of service (DDoS) attack detection and traffic mitigation using flow statistics. The method for DDoS attack detection and traffic mitigation using flow statistics includes: collecting first statistics for each flow based on flow information generated by traffic flow of a network connection device; and grouping the first statistics for each flow on a per-flow basis and processing the same into second statistics containing at least one of the number of bytes, the number of packets, and the number of flows per unit time.
Owner:ELECTRONICS & TELECOMM RES INST
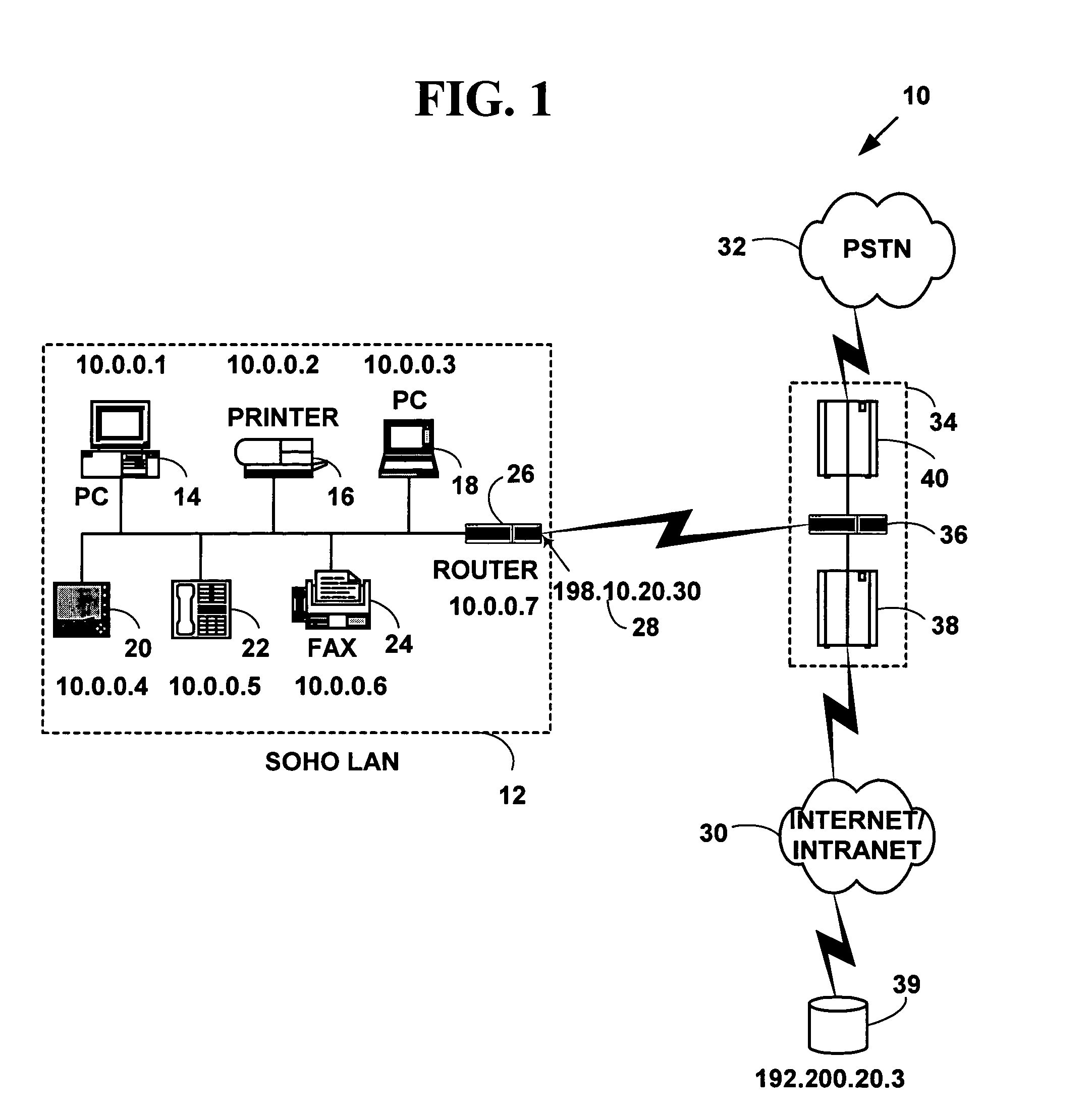
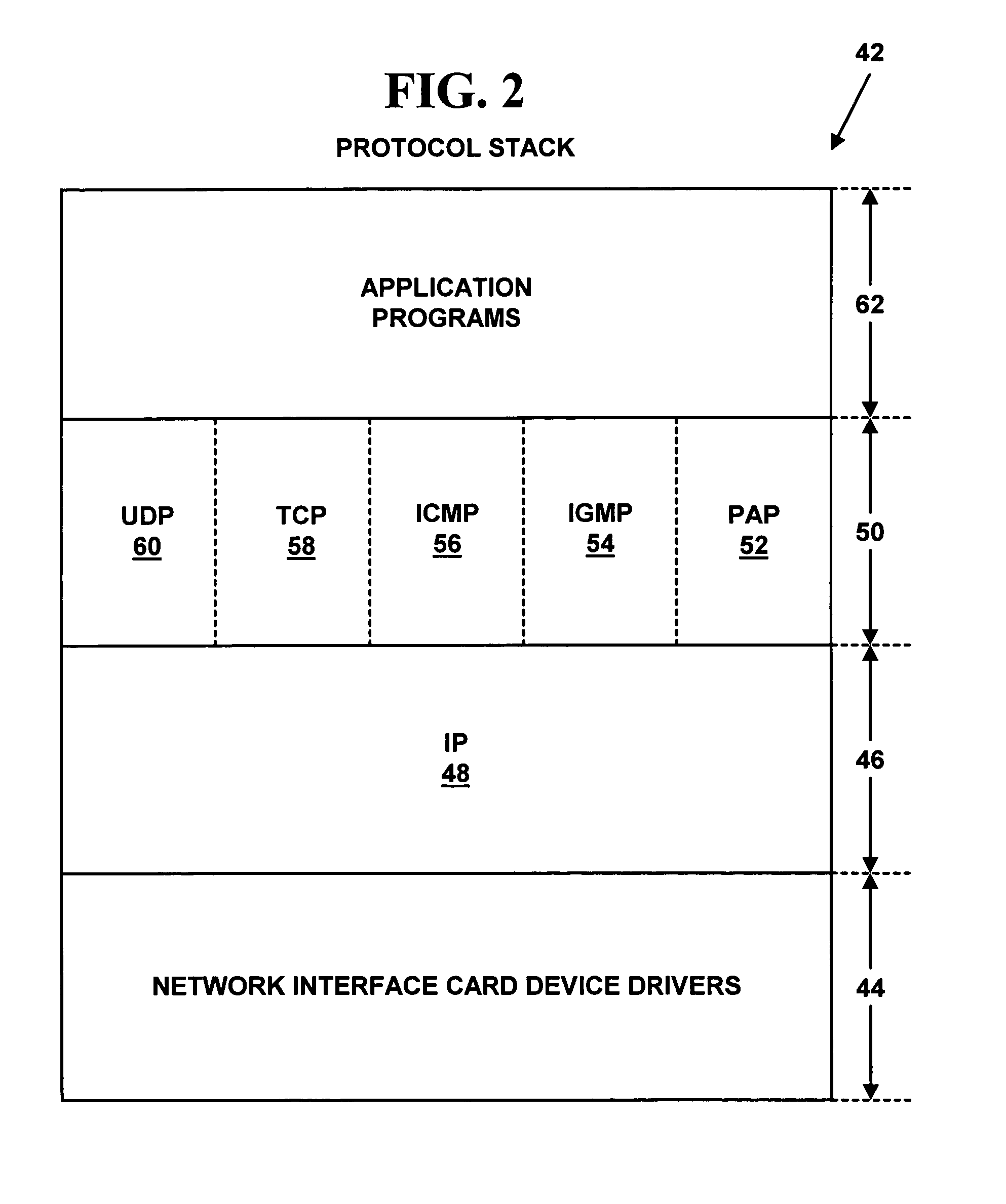
Method and system for controlling attacks on distributed network address translation enabled networks
InactiveUS7028335B1Readily apparentDigital data processing detailsUser identity/authority verificationSecurity associationNetwork address translation
A method and system for distributed network address translation with security for controlling and limiting the disruption caused by denial of service attacks. The method and system have a first network device and a second network device on a first network, and a third network device on a second network external to the first network, with an established security association between the first network device and the third network device. The first network device specifies an external address of the third network device for the security association to the second network device, which stores the external address in a table. The second network device then maps at least one of an internal address and a security value to the external address in the table. Any packets sent from the third network device to the first network device are intercepted by the second network device, which determines the external address and security value of the packet. If the security value of the packet has been allocated to the first network device, and the external address of the packet has been specified by the first network device as being valid, the packet is sent from the second network device to the first network device using distributed network address translation with security. Otherwise, the packet is discarded by the second network device.
Owner:HEWLETT-PACKARD ENTERPRISE DEV LP
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com