Method for protecting computer system
A computer system and security technology, which is applied in the field of computer security, can solve the problems of no integrity verification result processing operation, and the inability to fundamentally guarantee the security of computer platforms, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
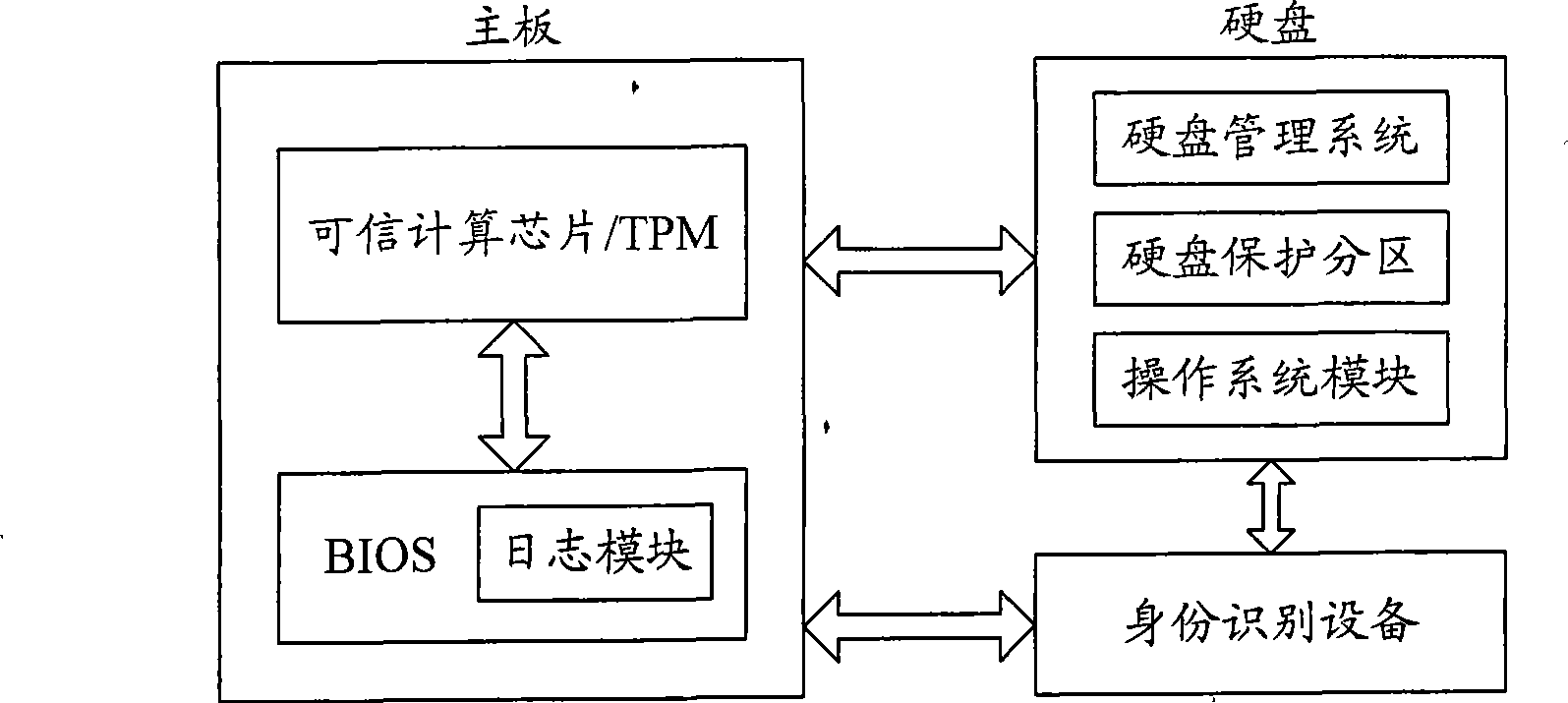
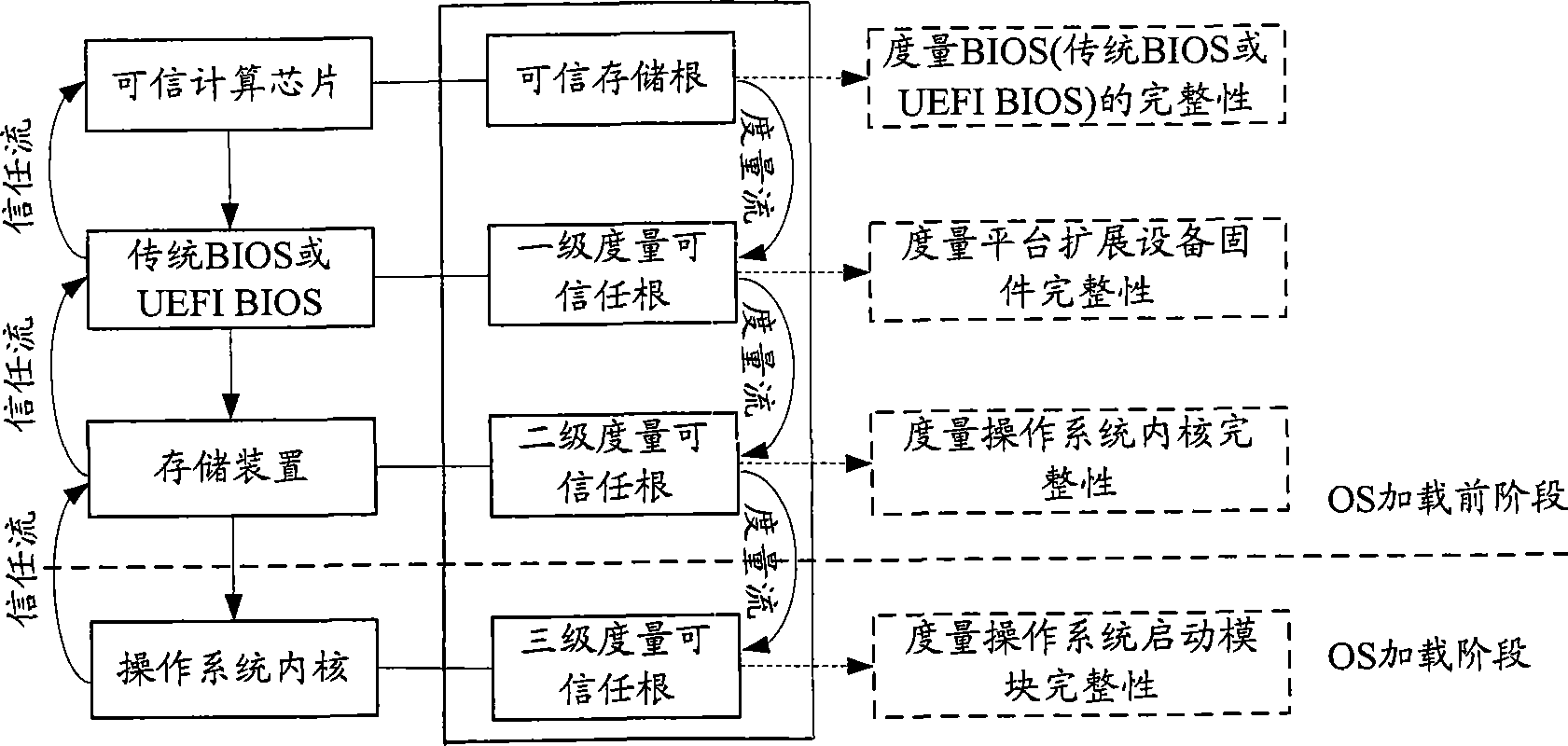
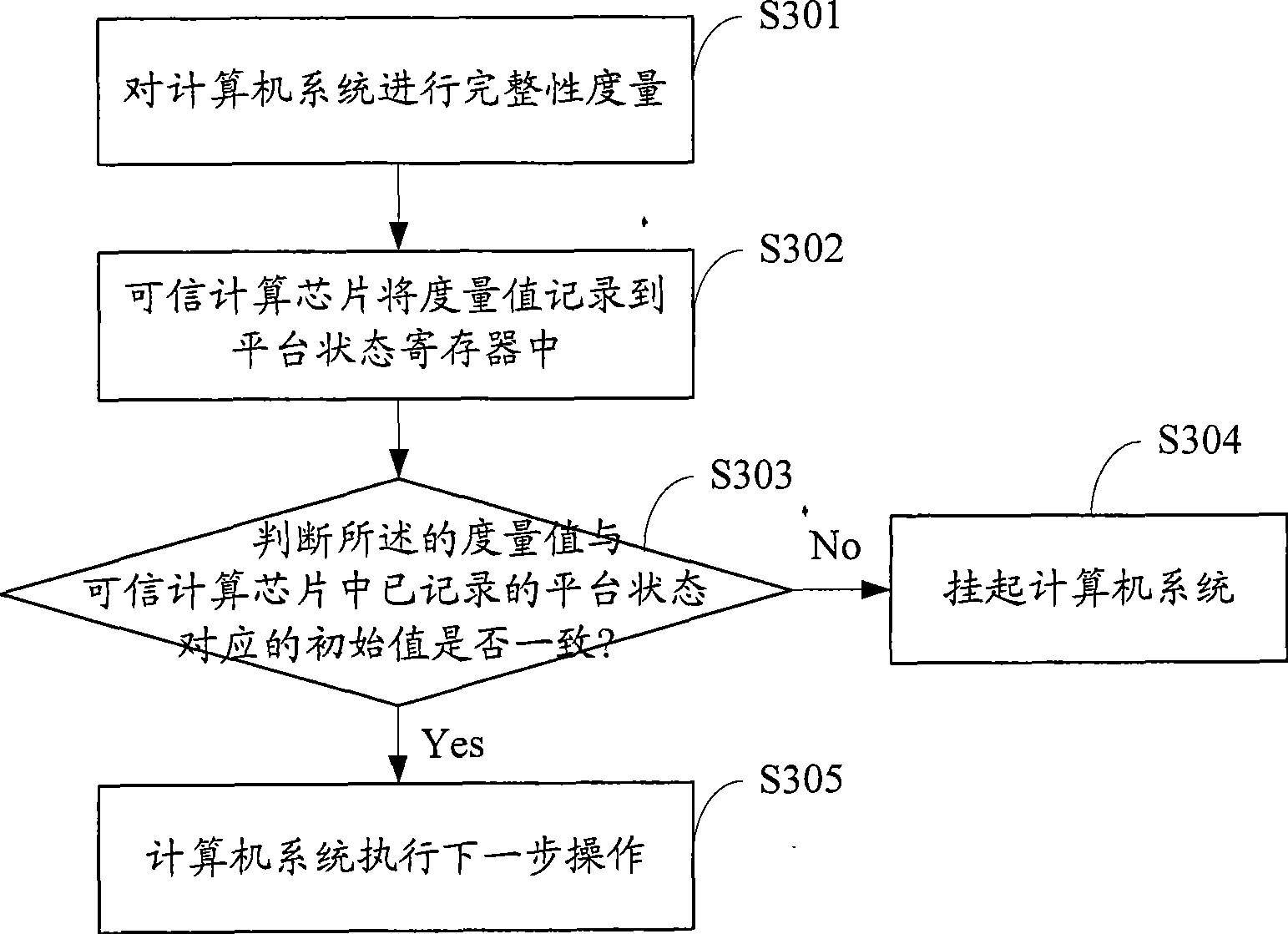
[0018] In the embodiment of the present invention, the trusted computing platform integrates a dedicated module in the computing system as the root of trust, and uses a cryptographic mechanism to establish a trust chain from the bottom layer components to the upper layer application, from the computer system boot, to the BIOS, to the configuration information detection , to the hardware platform, to load the operating system, to measure the integrity of the application operations under the operating system and network access, calculate the hash value and load it into the PCR of the trusted computing...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More