Updating and distributing encryption keys
A key and storage key technology, applied in key distribution, can solve the problem of not being able to know the dual key and so on
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030]The making and using of the presently preferred embodiments are discussed in detail below. It should be appreciated, however, that the present invention provides many applicable inventive concepts that can be embodied in a wide variety of specific contexts. The specific embodiments discussed are merely illustrative of specific ways to make and use the invention, and do not limit the scope of the invention.
[0031] The invention will be described with respect to a preferred embodiment in a specific context, ie a pair of nodes communicating with each other. However, the invention can also be applied to other communications, such as multicast, broadcast or other multiplex communications, where several nodes are used to communicate.
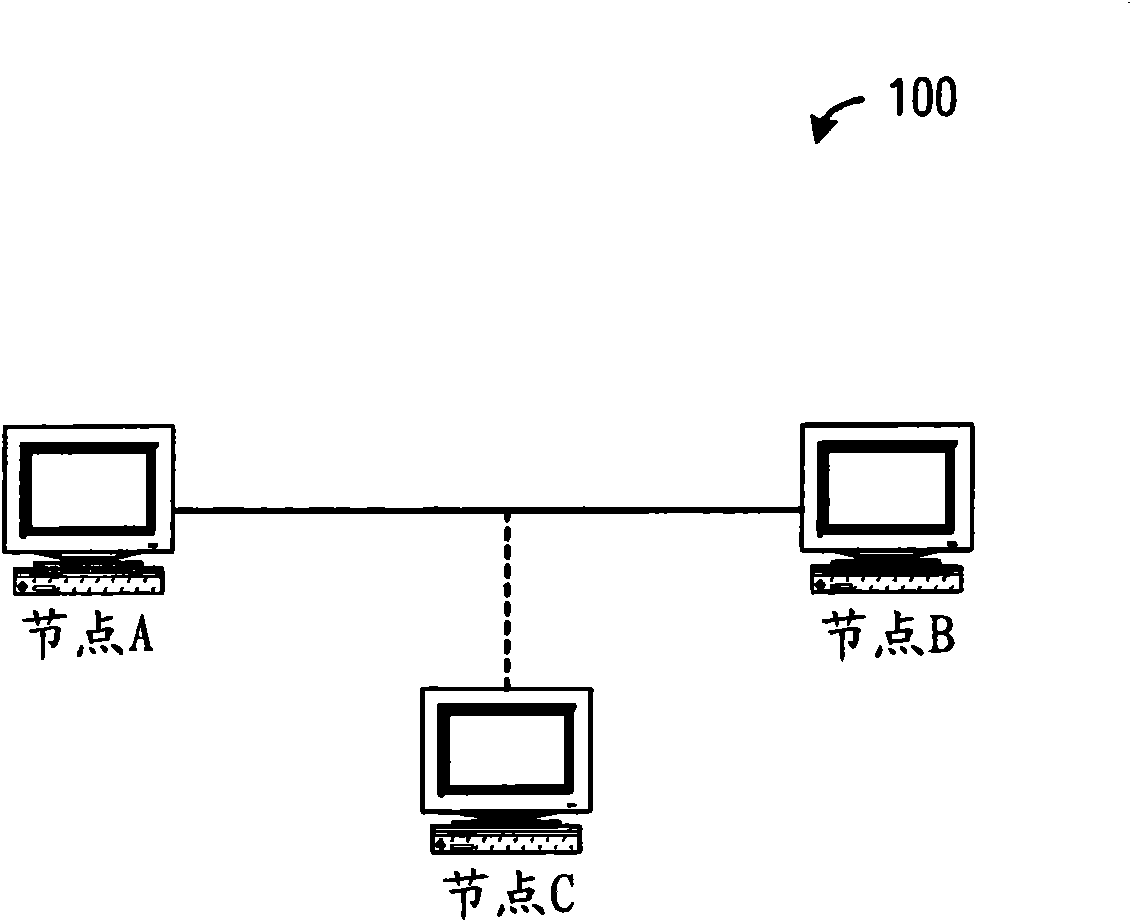
[0032] now refer to figure 1 , which illustrates a network environment 100 embodying features of the present invention. In network environment 100, node A communicates with node B directly. It should be noted that Node A and Node B are ill...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More