Method and device for protecting user behavior at operating terminal
A behavioral and user-based technology, applied in the field of communication, can solve problems such as manual deletion of data, and achieve the effect of flexible data protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
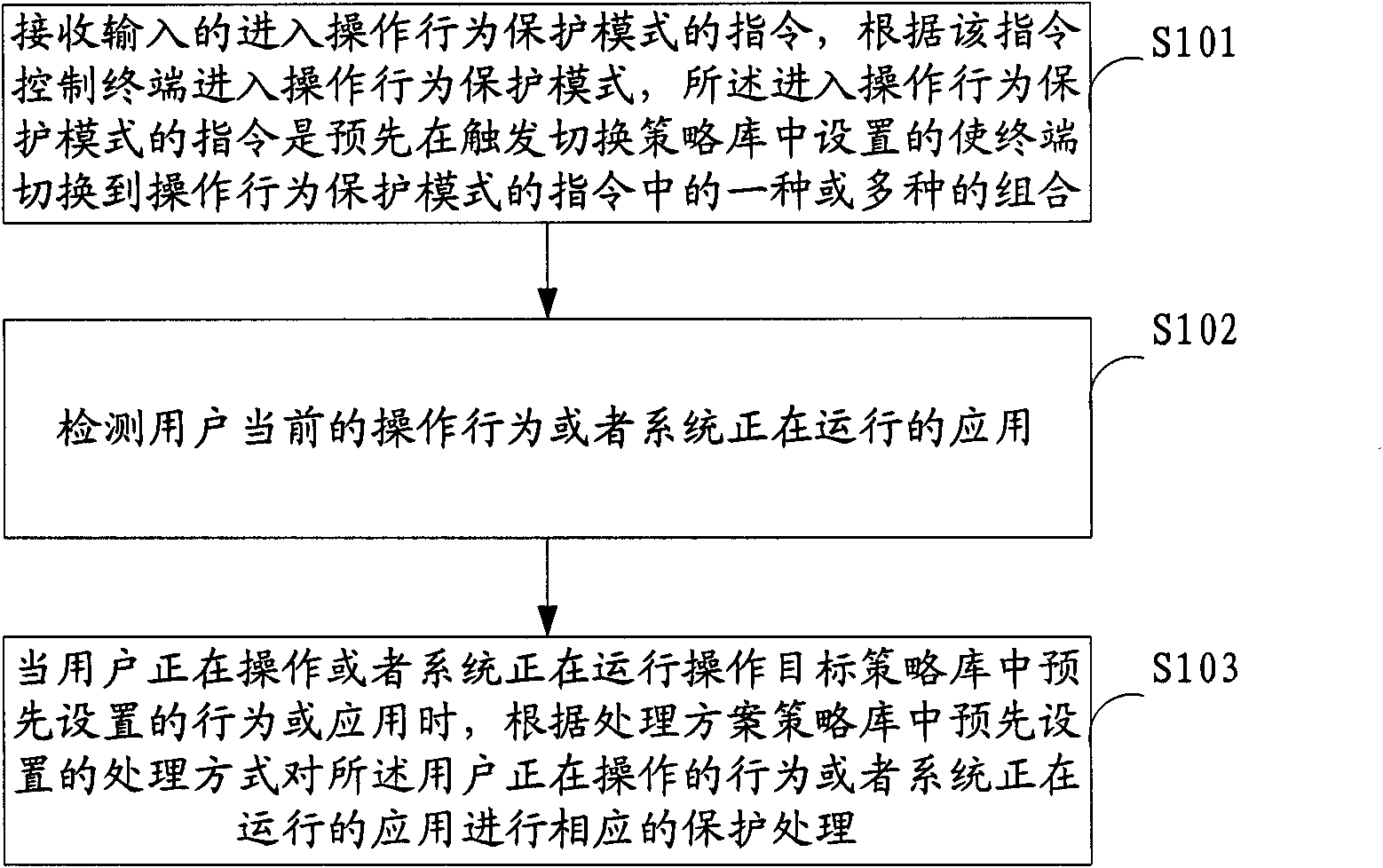
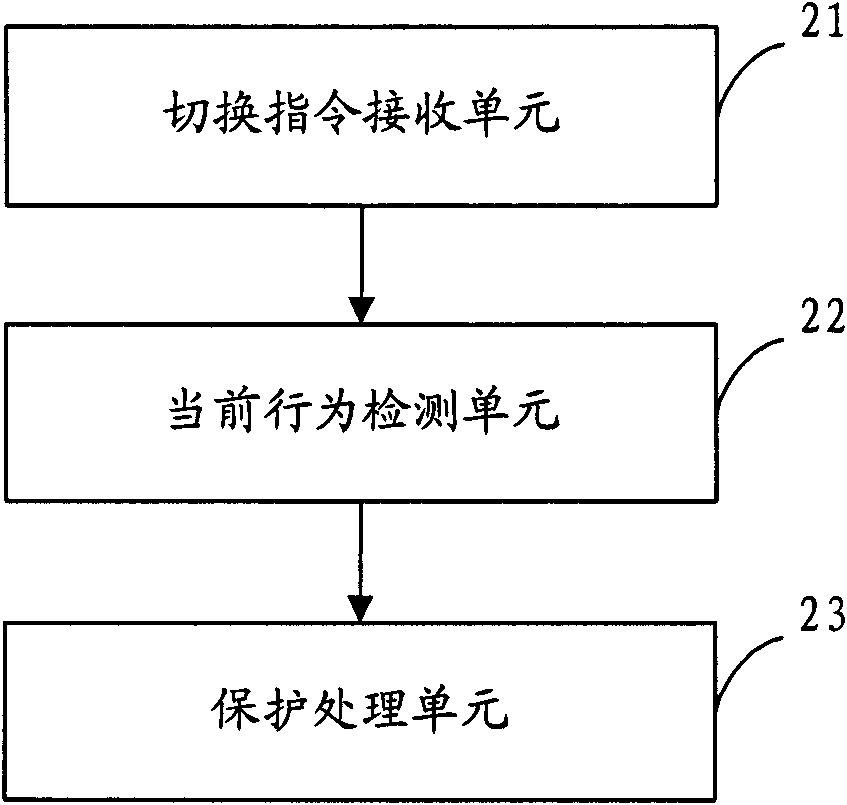
[0016] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0017] In the embodiment of the present invention, a series of policy libraries are preset, including a preset or custom "trigger switching policy library" for switching to protection mode, a preset or custom "operation target policy library" for specific protected applications or behaviors " and the "handling plan policy library" that presets or customizes actions for protection and processing of specific applications or behaviors. Whether the current operation behavior or the application that the system is running is the preset operation behavior or application in the "Operation Target Policy Lib...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More