Detecting method of unsafe variable use in software program
A software program and detection method technology, applied in the field of program analysis, can solve problems such as unsafe use, achieve the effects of improving reliability, improving code quality, and reducing development costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
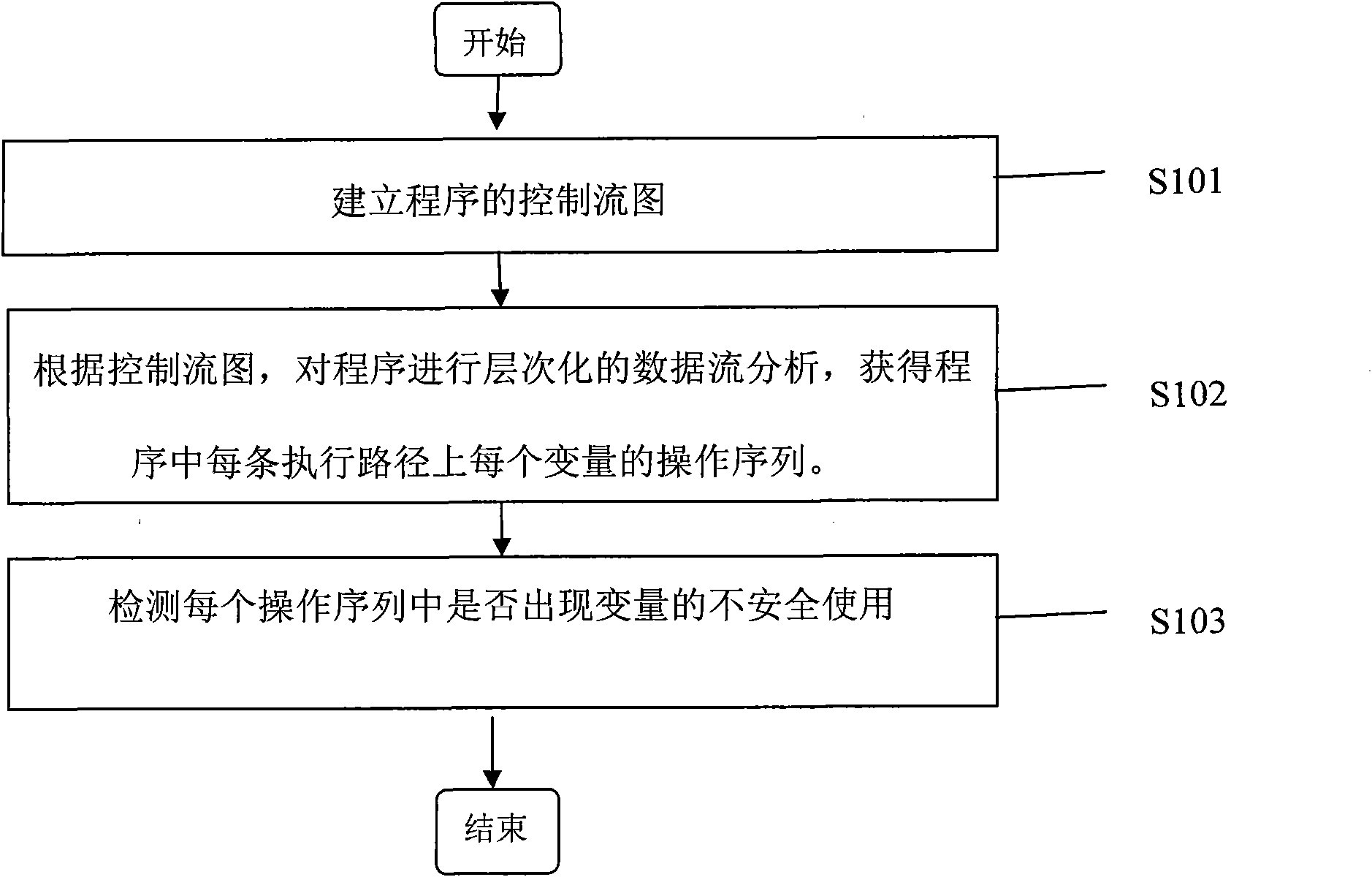
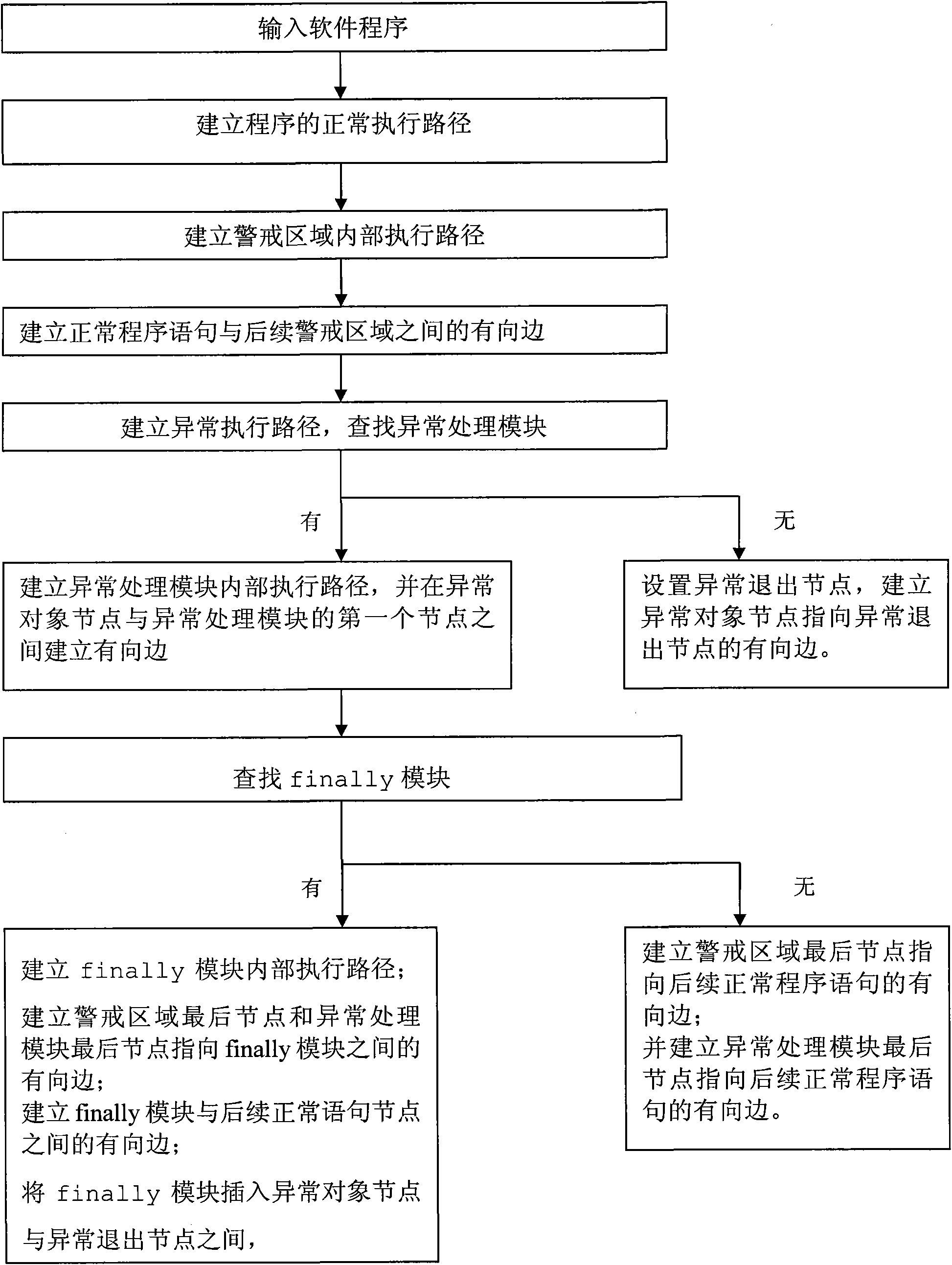
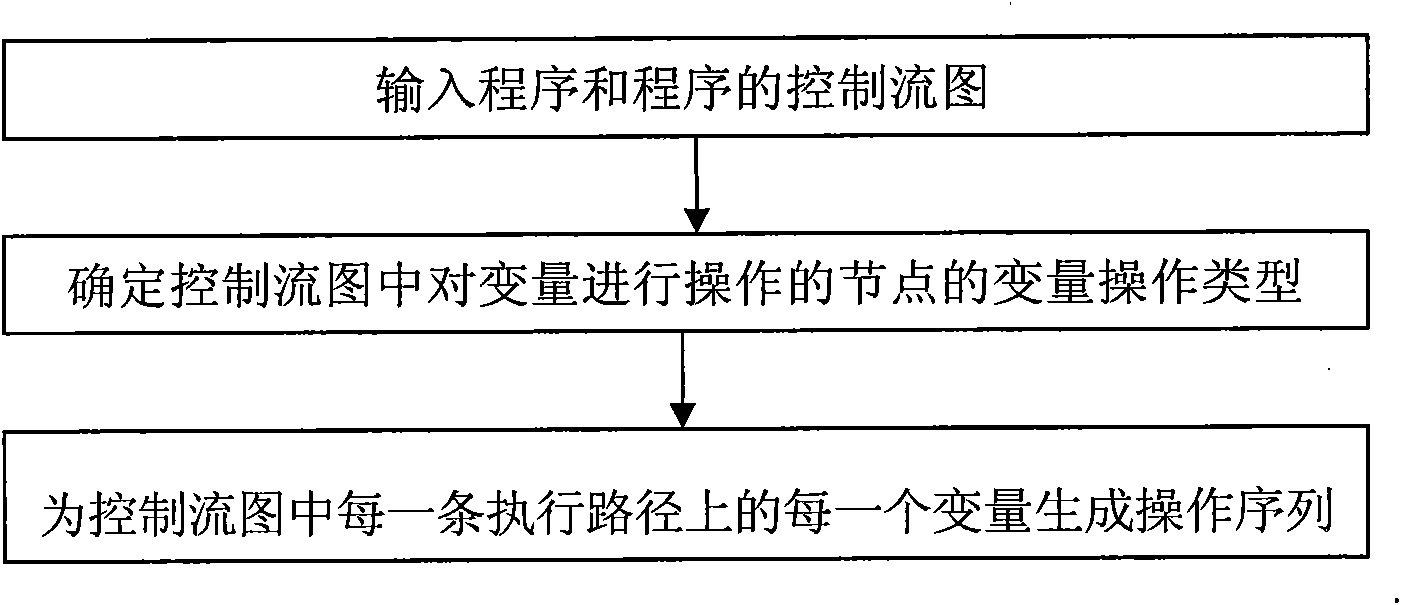
Method used
Image
Examples
Embodiment 1
[0058] Table 1 is a Java program. In addition to normal program statements, the program also includes try statement block, catch statement block and finally module. The try statement block is the warning area, and the catch statement block is the exception handling module. When the program is running, there may be exceptions in the statements in the 4th and 5th lines of the program. If an exception object of type IOException is thrown during the execution of the statement in the 5th line, the control flow will be transferred to the statement in the 8th line. The assignment to the variable str on line 5 is invalid. The program continues to execute, and the variable str is used by calling the str.length() method on line 14, which is an unsafe use of the variable str. Since the assignment to str in line 5 is unsuccessful, the value of str is still null, so when str is used in the statement in line 14, the program will throw an exception of type NullPointerException, resulting in ...
Embodiment 2
[0091] Table 3 is a section of Java program, which includes normal program statement, try statement block and finally module, does not contain catch statement block, and try statement block is a warning area.
[0092] Table 3 Example program fragment table of embodiment 2
[0093]
[0094] The method of detecting the use of unsafe variables of the program in Table 3 is:
[0095] S101, establish the control flow graph of the program in Table 3
[0096] A. Establish a normal execution path. Set the first and second statements in the program fragment in Table 3 as nodes and mark them with line numbers; establish a directed edge from node 1 to node 2; set the 14th line statement as node 14.
[0097] B. Establish the internal execution path of the try statement block in the alert area. Set each statement on lines 3-7 in the try block as a node. The execution sequence of the statements inside the try statement block is: starting from the statement on line 3, and executing to ...
Embodiment 3
[0112] Table 5 is a Java program, which includes a normal program statement, a try statement block and a catch statement block, excluding the finally module, the catch statement block is an exception handling module, and the try statement block is a warning area.
[0113] Table 5 Example program fragment table of embodiment 3
[0114]
[0115] The method for detecting the use of unsafe variables of the program in Table 5 is:
[0116] S101, establish the control flow graph of the program in Table 5
[0117] A. Establish a normal execution path. Set the first and second statements in the program fragment in Table 4 as nodes and mark them with line numbers; establish a directed edge from node 1 to node 2; set the 14th line statement as node 14.
[0118] B. Establish the internal execution path of the try statement block in the alert area. Set each statement on lines 3-7 in the try block as a node. The execution sequence of the statements inside the try statement block is: ...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap