Safety loophole mining method and device of application software under Android platform
A technology of application software and vulnerability mining, applied in the field of source code detection, can solve problems such as few automation tools, security vulnerability discovery, low hardware processing capacity, etc., and achieve the effect that is conducive to security development
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
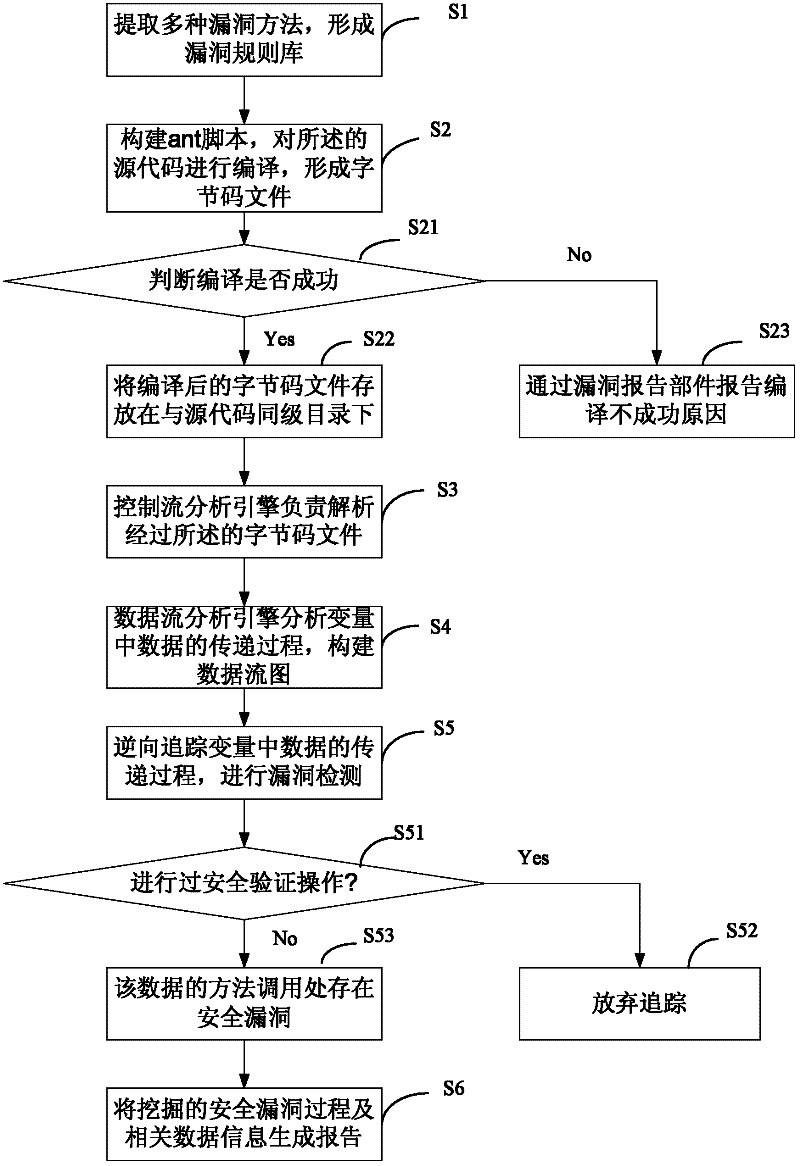
[0035] In order to describe the technical content, structural features, achieved goals and effects of the present invention in detail, the following will be described in detail in conjunction with the embodiments and accompanying drawings.
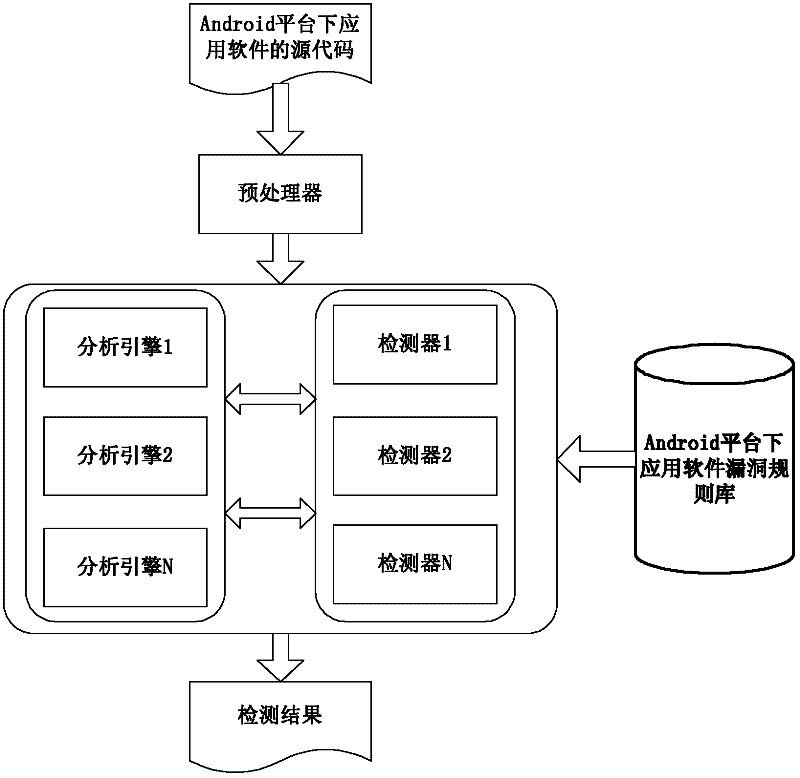
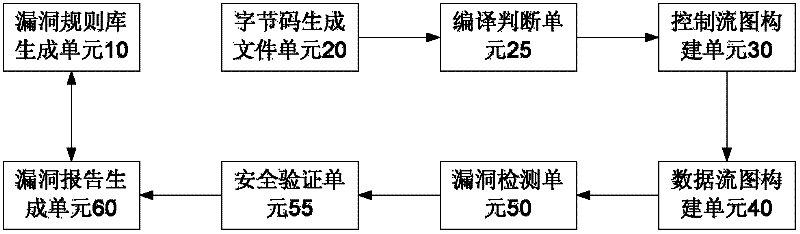
[0036] The invention relates to a technology for mining security loopholes of application software under the Android platform, which is used for mining security loopholes of application software under the Android platform, specifically mining security loopholes of application software under the Android platform based on source code static analysis technology, and a specific technical solution as follows:
[0037] see figure 1 , the embodiment of the present invention a kind of security loophole mining method of application software under the Android platform, comprising:
[0038] S1. Extract the vulnerability methods of application software source codes under various Android platforms to form a vulnerability rule base;
[0039] Vulnerabi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More