Implementation system of p-element domain SM2 elliptic curve public key cryptographic algorithm
A technology of elliptic curve and public key cryptography, which is applied in the field of information security and can solve problems such as difficult algorithms to be applied
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
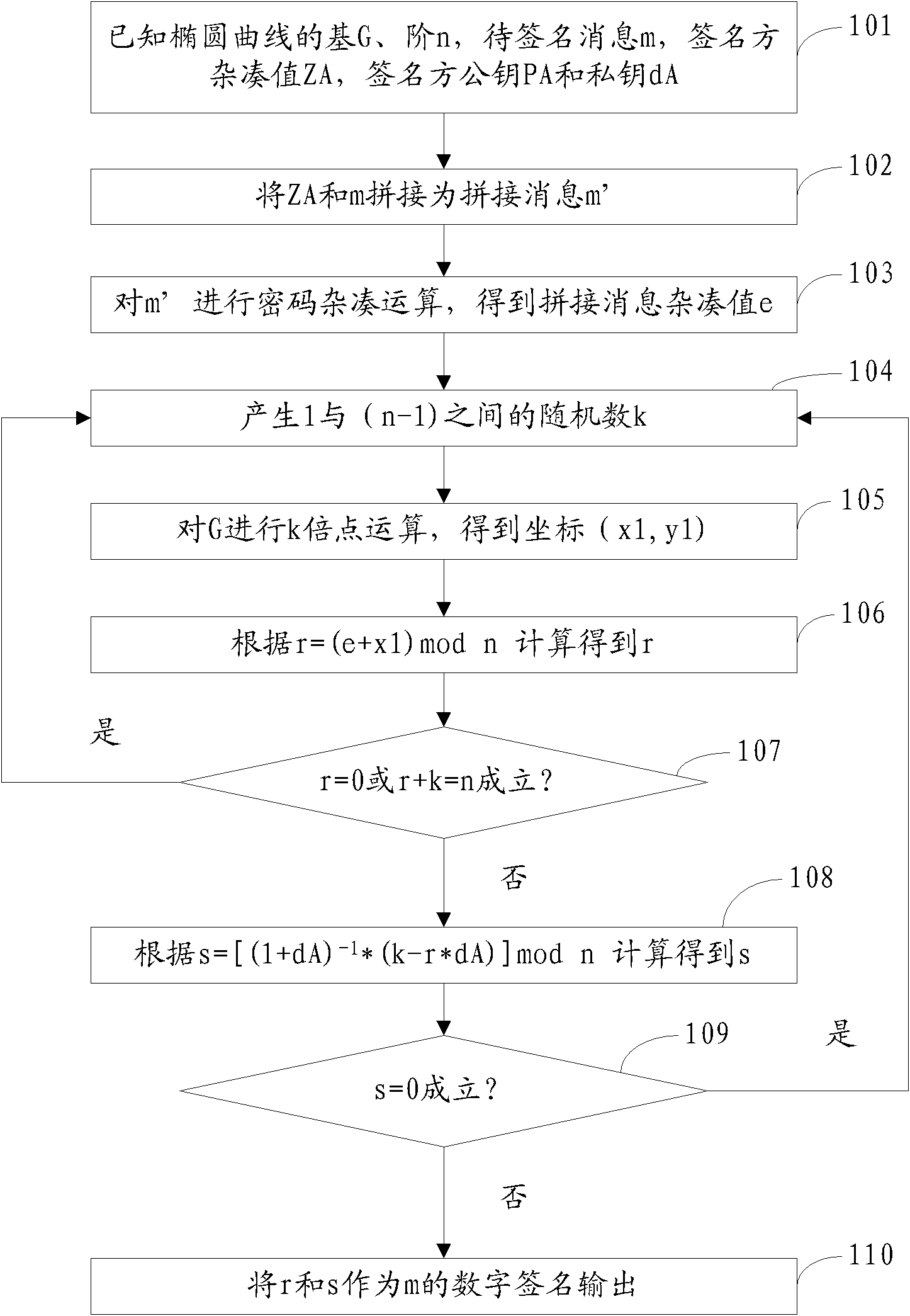
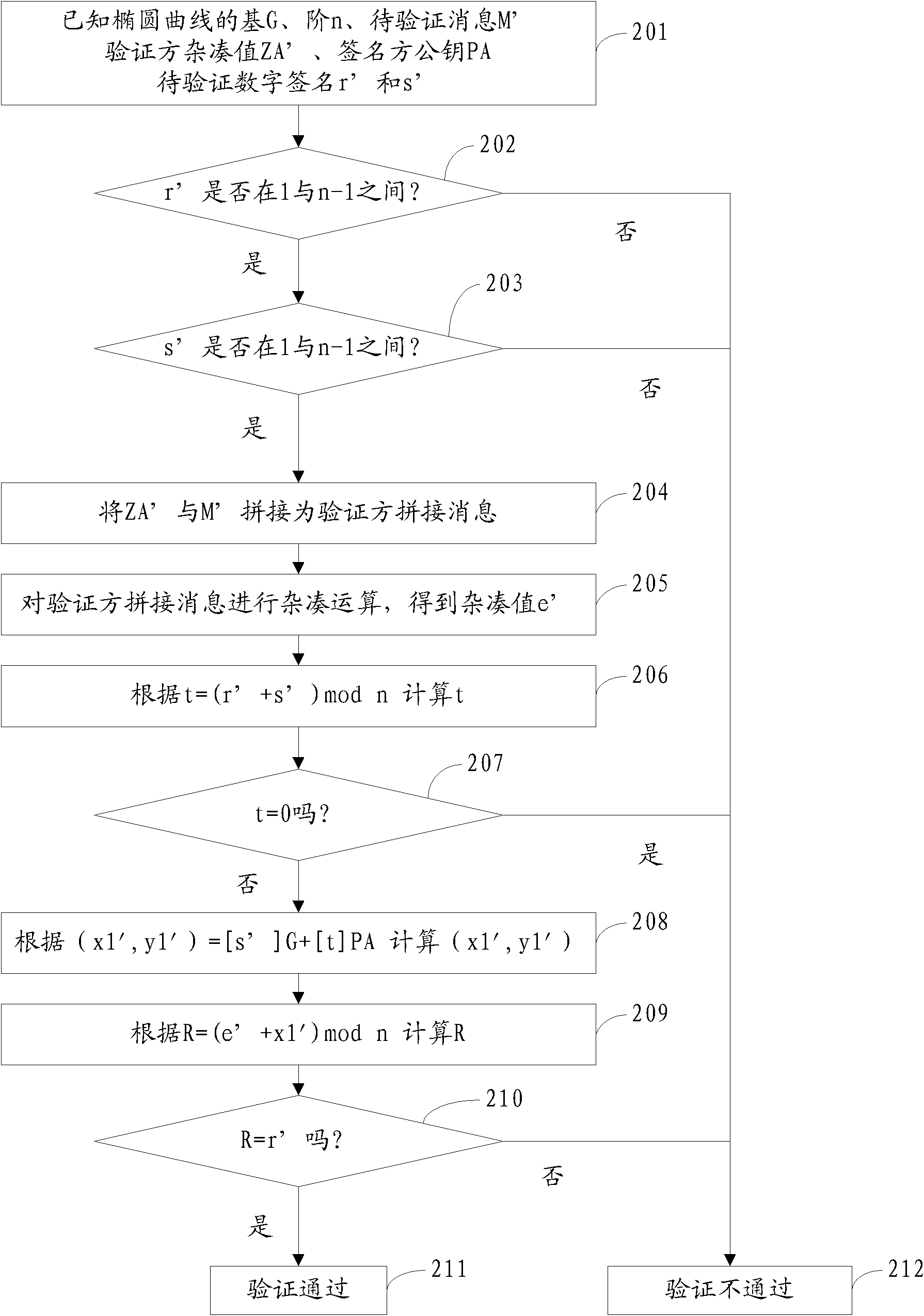
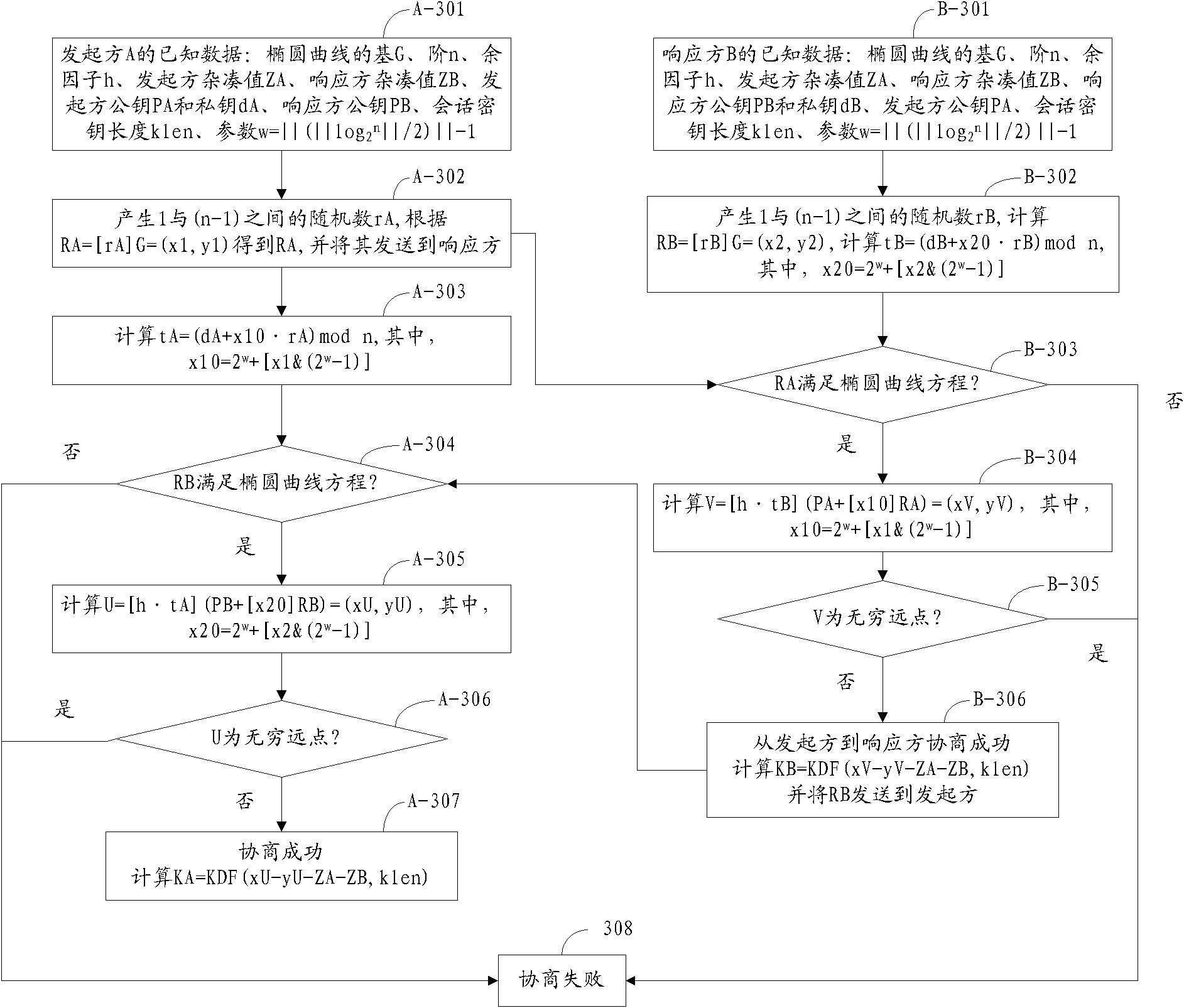
[0056] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
[0057] The p-element field SM2 elliptic curve public key encryption algorithm involved in the present invention is based on the elliptic curve in the p-element field (also known as p-element finite field, namely the finite field involved in the present invention). In the p-element domain, the equation of the elliptic curve is y 2 =x 3 +ax+b, where p is a prime number greater than 3, a and b are called the parameters of the elliptic curve, both of which are values in the field of the p element, and satisfy (4a 3 +27b 2 ) mod p is not 0, where mod is the modulo operator.
[0058] In addition, the elliptic curve in the p-element field has several characteristic quantities of basis, order and cofactor. The present...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More