Trusted network connecting method based on IPsec
A network connection and trusted technology, applied in the field of IPsec-based trusted network connection, can solve the problems of not considering how to protect terminal security, unable to guarantee service credibility, etc., to achieve the effect of ensuring dynamic credibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
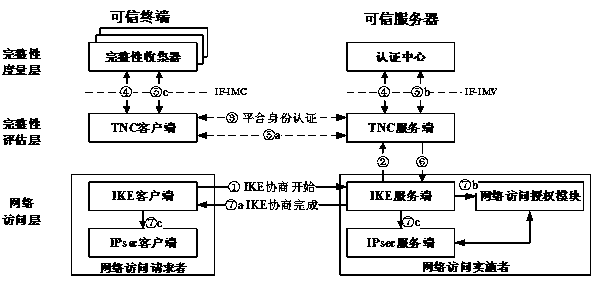
[0026] When the trusted terminal accesses the trusted server, the underlying communication channel uses the IPsec security channel. Before the life cycle of the security association (SA) used by the IPsec security channel ends, both parties need to conduct an IKE session to generate a new security association (SA).
[0027] This patent adds platform identity authentication and integrity verification to the process of IKE session connection establishment, so that when the security association (SA) is periodically updated through the IKE session between the terminal and the server, the platform identity authentication, integrity verification is also periodically performed. verify. Proceed as follows:
[0028] 1) The IKE client initiates a negotiation with the IKE server, and the first step is key negotiation.
[0029] 2) After the key negotiation between the IKE client and the IKE server is successful, the IKE server notifies the TNC server that an IKE negotiation request is c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More