Method and system for trusted verification of object memory in access control
An access control and verification method technology, applied in the field of information security, can solve the problems of insufficient security protection capability, cumbersome verification system, and inability to ensure the trusted operation of upper-layer applications, and achieve the effect of ensuring dynamic trustworthiness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
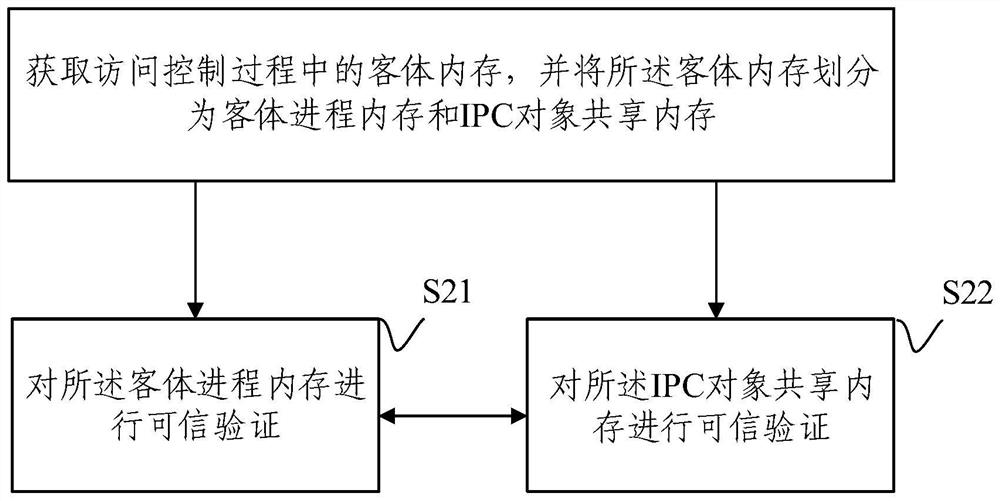
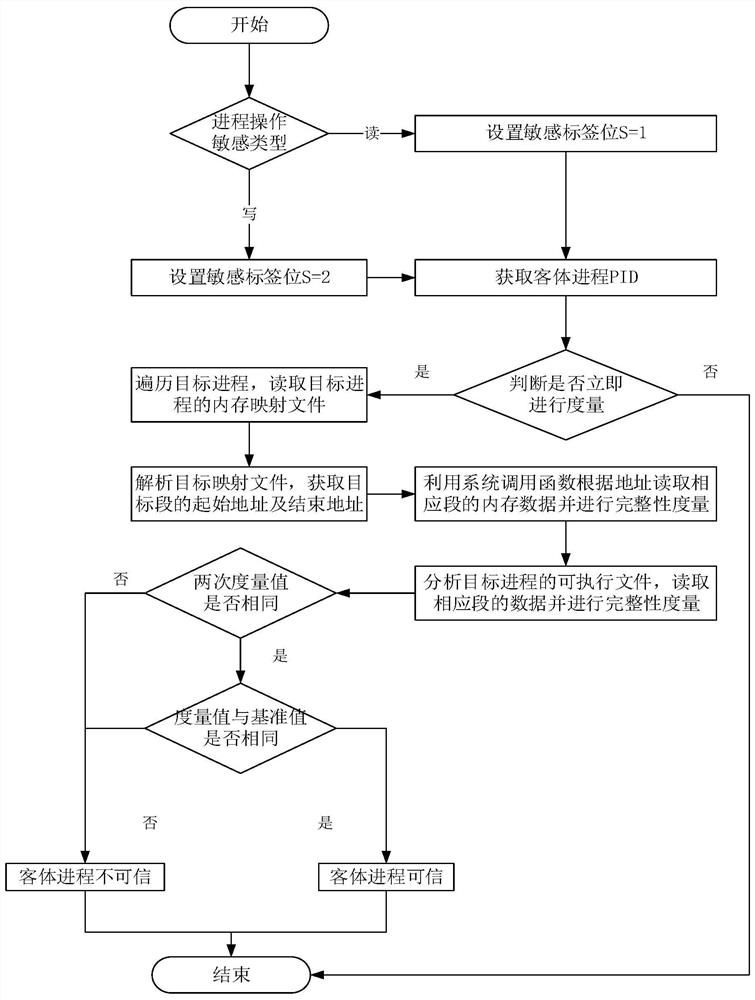
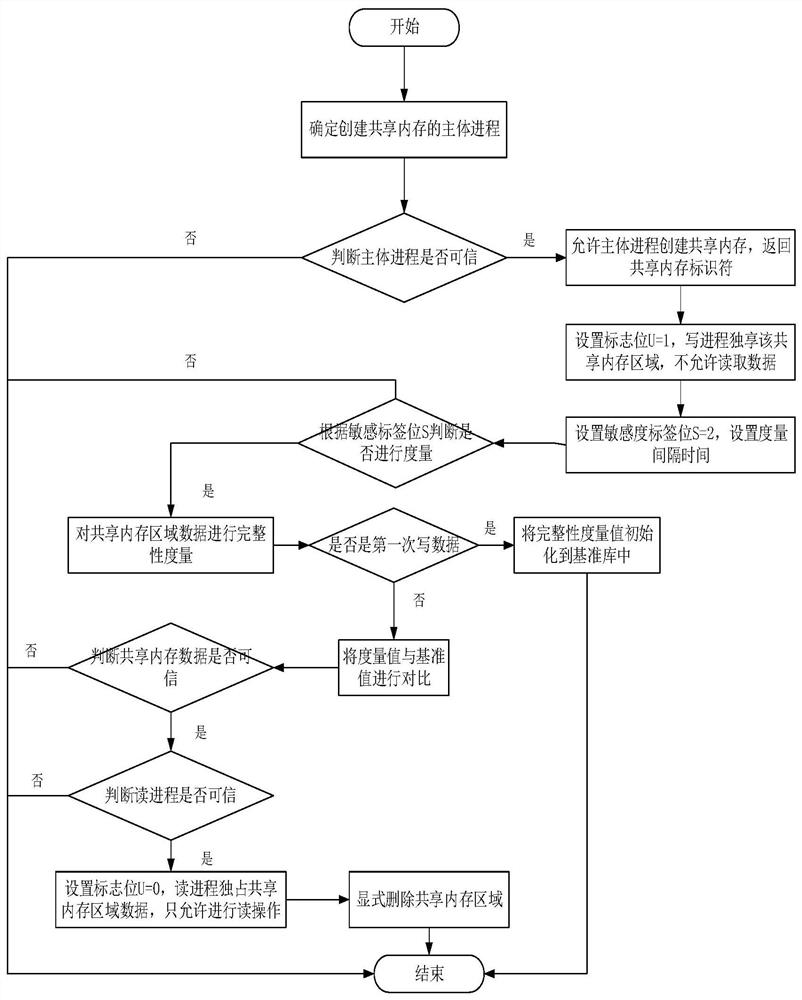
Method used
Image
Examples
Embodiment Construction
[0033] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Obviously, the described embodiments It is a part of embodiments of the present invention, but not all embodiments. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0034] Trusted computing technology can improve network security as follows:
[0035] 1. Operating system security upgrades, such as preventing rootkit insertion in UEFI, preventing rootkit insertion in OS, and preventing virus and attack driver injection, etc.
[0036] 2. Application integrity protection, such as preventing Trojan horses from be...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More