Embedded security chip and Montgomery modular multiplication operational method thereof
An operation method and security chip technology, which is applied in the field of asymmetric key algorithm in cryptography, can solve problems such as multi-running time and resources, cost of embedded security chips, etc., and achieve the effect of saving storage space
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the technical problems, technical solutions and beneficial effects solved by the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
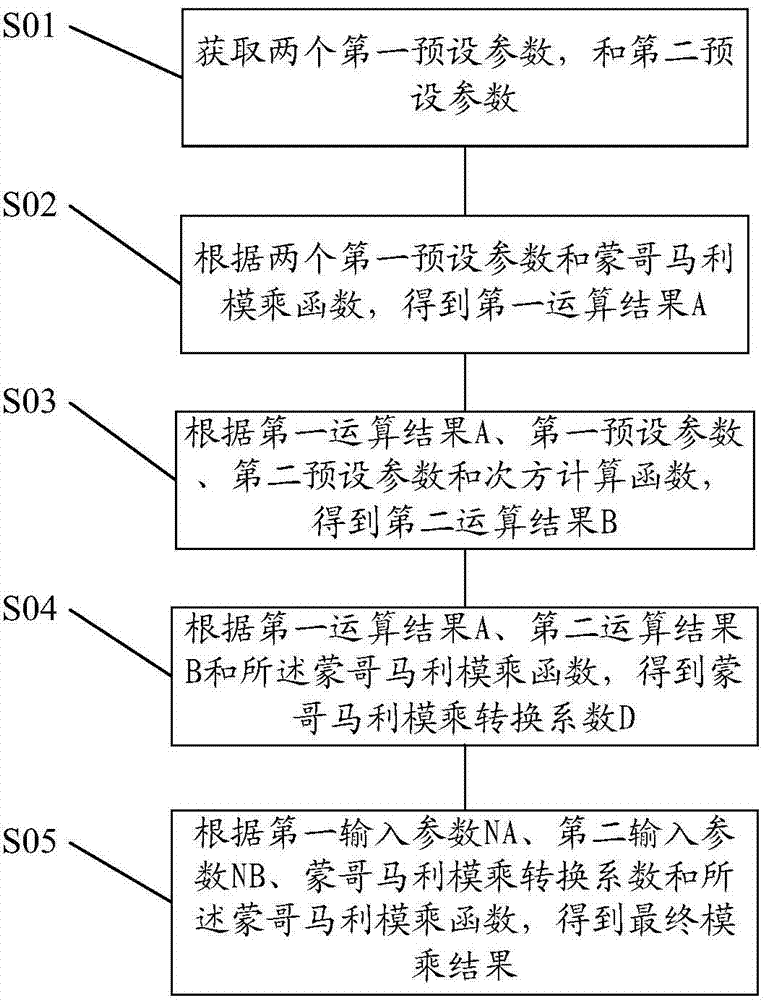
[0026] The present invention provides a Montgomery modular multiplication operation method of an embodiment embedded security chip, such as figure 1 As shown, the operation method includes the following steps:
[0027] Step S01, obtaining two first preset parameters and a second preset parameter, wherein the first preset parameter is a constant 1;
[0028] Step S02, according to the two first preset parameters and the Montgomery modular multiplication function, the first operation result A is obtained, and the first operation result A=MontF(1,1);
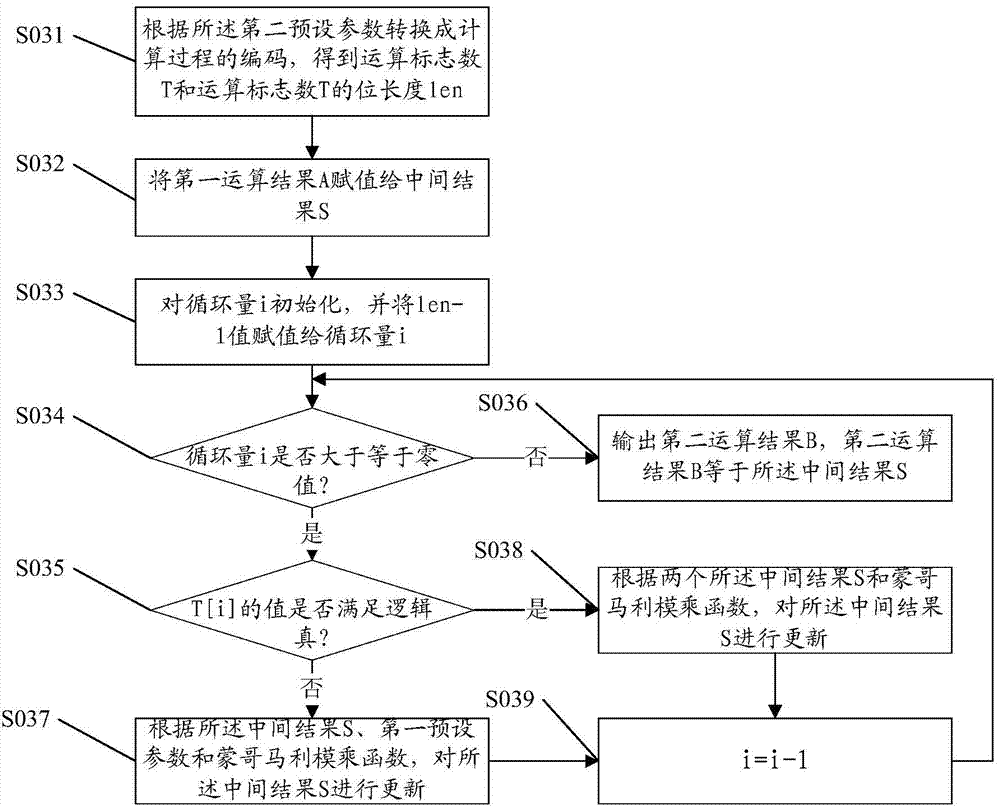
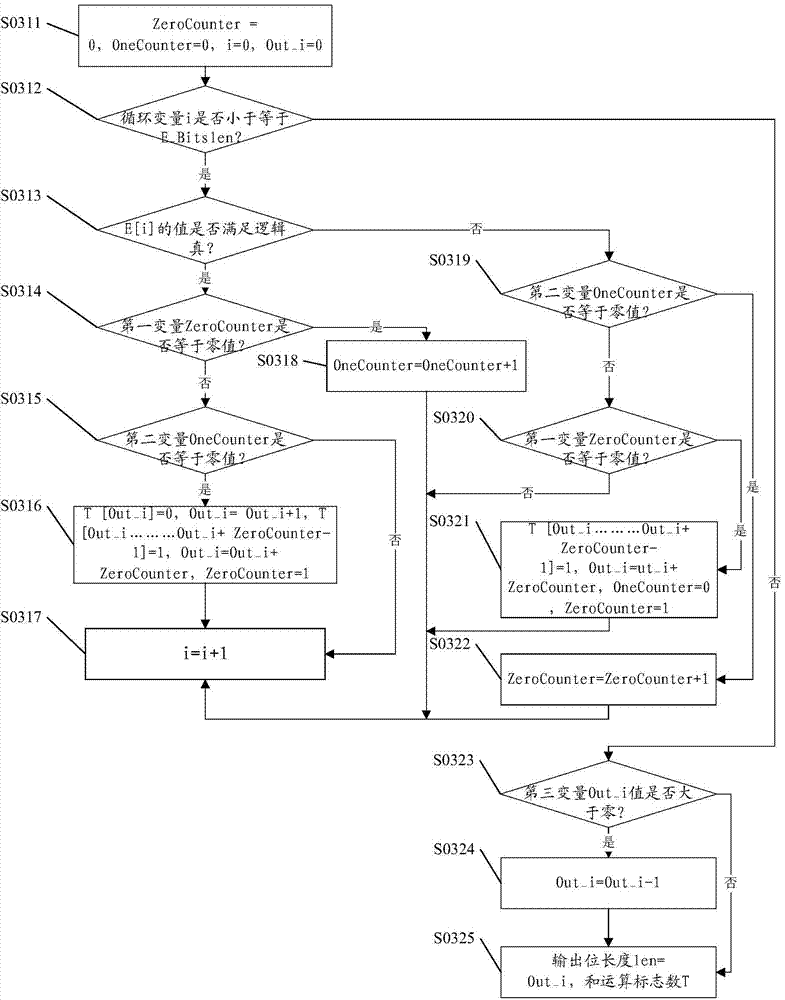
[0029] Step S03, acc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More