Ciphertext Policy Attribute-Based Encryption with Efficient Attribute Revocation
A technology of attribute-based encryption and ciphertext strategy, applied in the field of information security, can solve the problems of not meeting actual needs, tediousness, low revocation efficiency, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
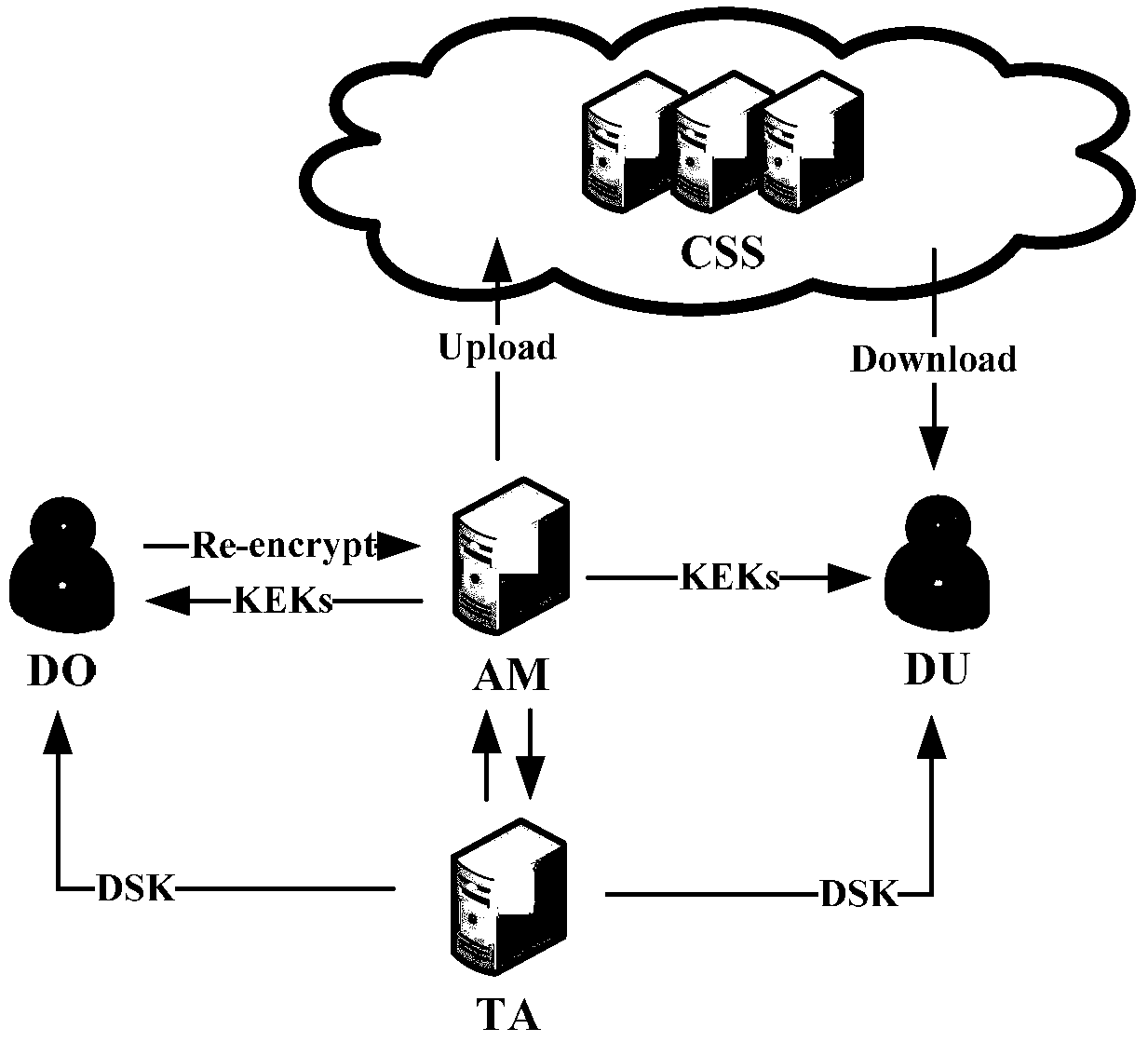
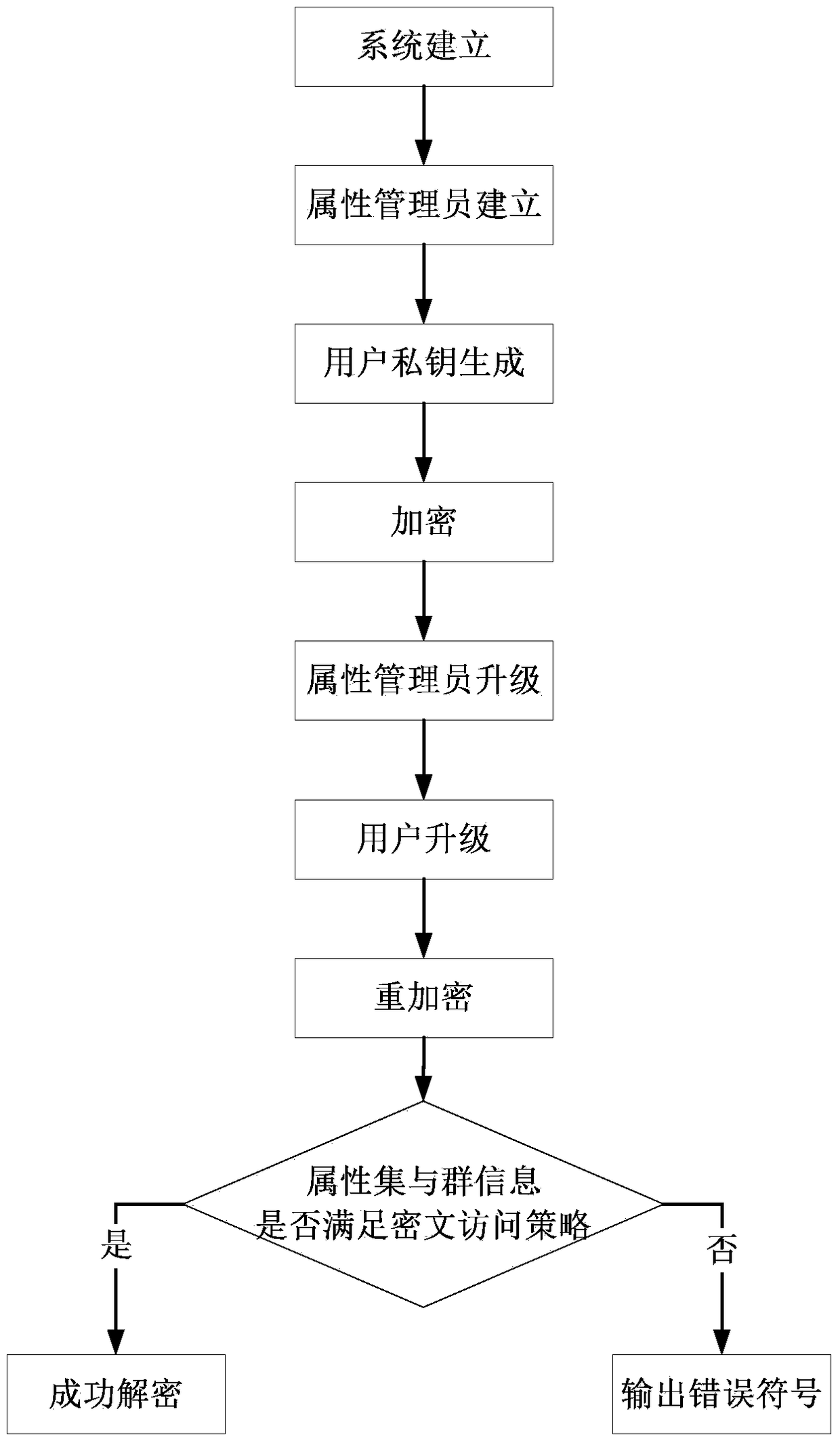
[0073] Such as figure 1 and figure 2 As shown, the specific process of this embodiment is as follows:
[0074] Step 1. System establishment
[0075] The attribute authority AA randomly selects a set of parameters α and β from the public key function database, including two multiplicative cyclic groups G and G whose order is a prime number p T , the generator g of the group G and the bilinear pairing map e: G×G→G T . Among them, the generator g is:
[0076] g=4825753236114302700181009551893401628723199415732972015970622054593498921292879986485027569312907193857799469116963683969768920235934912260481192099662160,4048850100117591308690978073403290894218008271572038432682891321098549039994467134474260108405016782650931484816763740889273827461896634534759269691983847,0
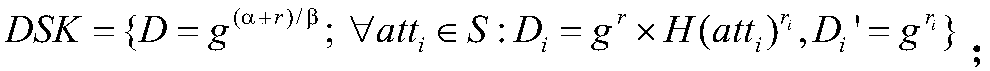
[0077] According to the selected parameters α and β, AA generates the system public parameters PK and the master private key MK, and makes the system public parameters PK public and keeps the master private k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More