Method and device for establishing session keys
A technology for establishing sessions and keys, which is applied in the field of network communication and can solve the problems of inability to meet security requirements and difficult to track attackers.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
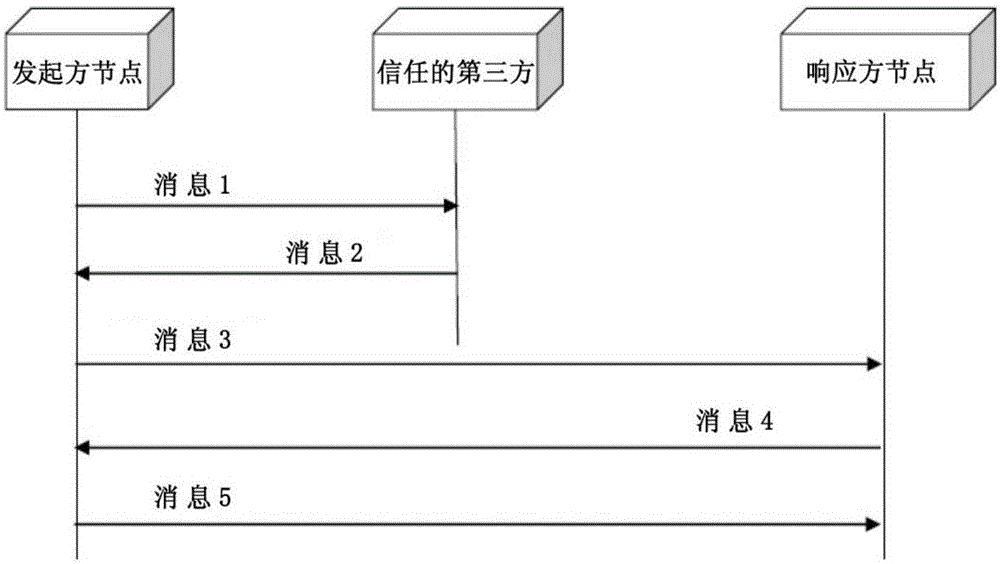
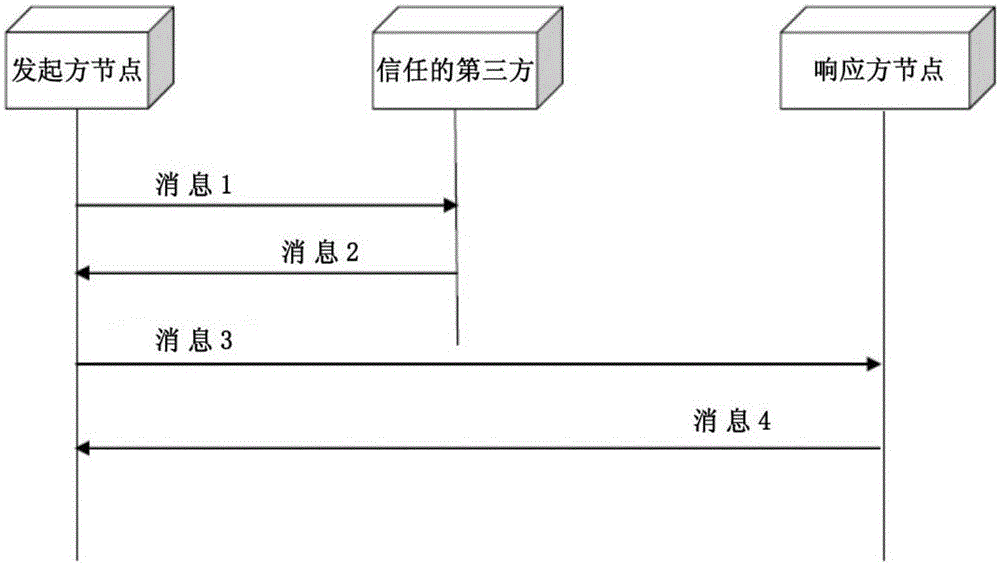
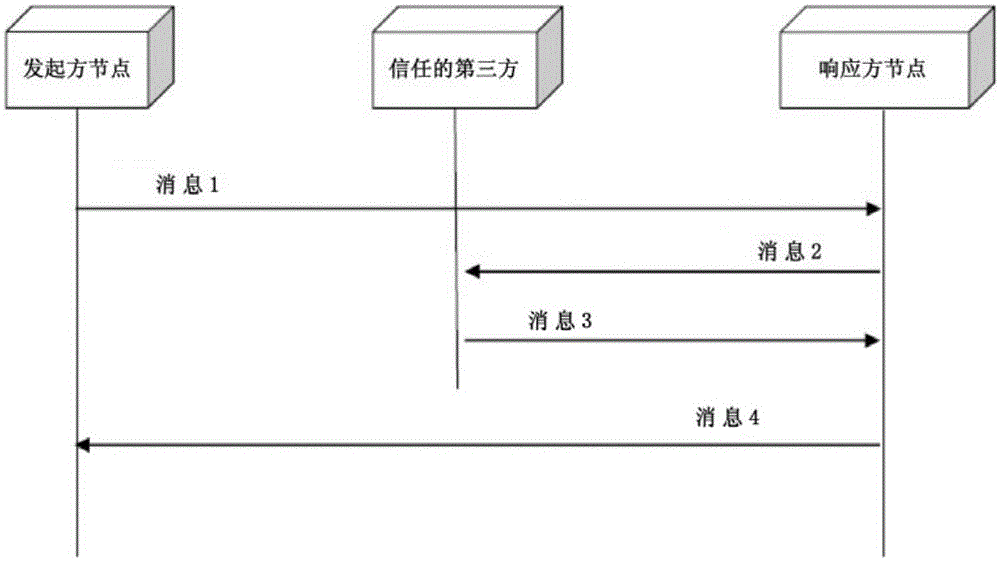
Method used
Image
Examples
Embodiment Construction
[0050] Figure 4 One example of a communication infrastructure 100 in which the present invention may be advantageously implemented is illustrated. For the sake of simplicity of description, rather than limitation of the present invention, Figure 4 The examples in . show only a limited number of entities (or nodes) and connections, but those skilled in the art will extend the described principles to multiple and various types of entities and connections (wireless, mobile, ultra-high speed).
[0051] A communication network (100) includes fixed or mobile entities capable of forming a network of objects (102). An entity may have a high resource limit (102-1, 102-n) or a low resource limit (112-1, 112-m).
[0052] Entities with high resource constraints may be wireless sensors or actuators, which have limited computational and / or memory capacity. They can also be active tabs. However, an entity that is not inherently constrained in terms of resources may only be temporarily ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More