Secret key negotiation method and device
A key negotiation and key technology, applied in the field of information security, can solve the problems of low security, complicated operation, and inability to authenticate terminal equipment, and achieve the effect of reducing costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
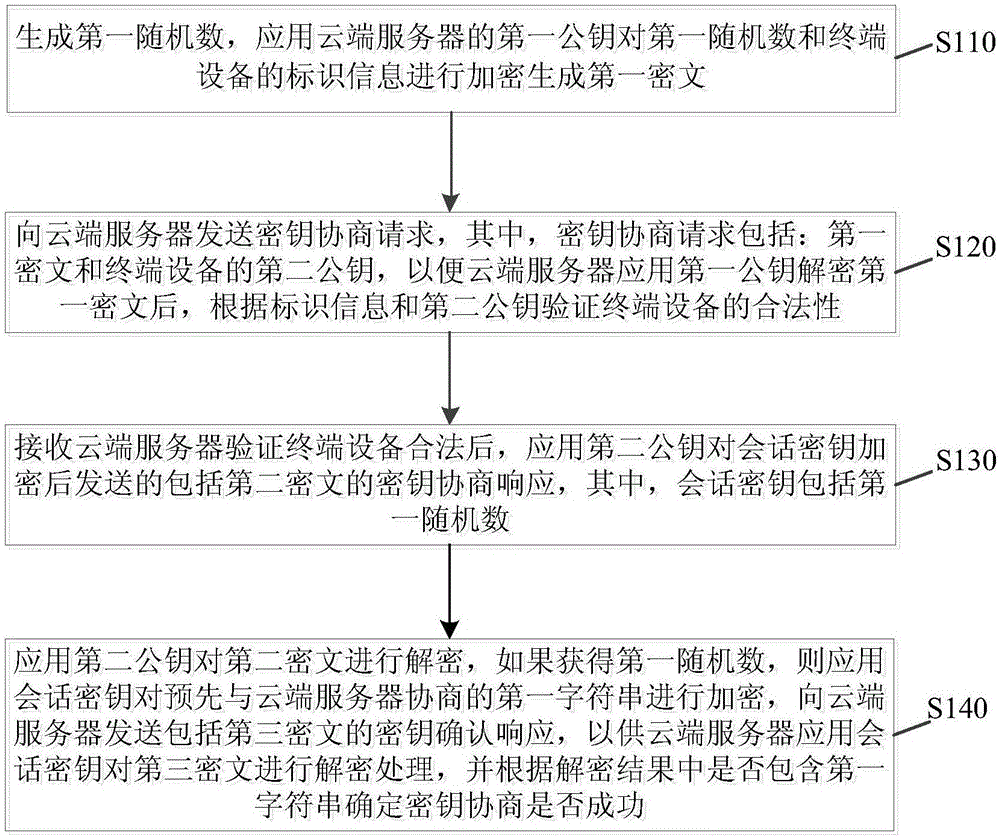
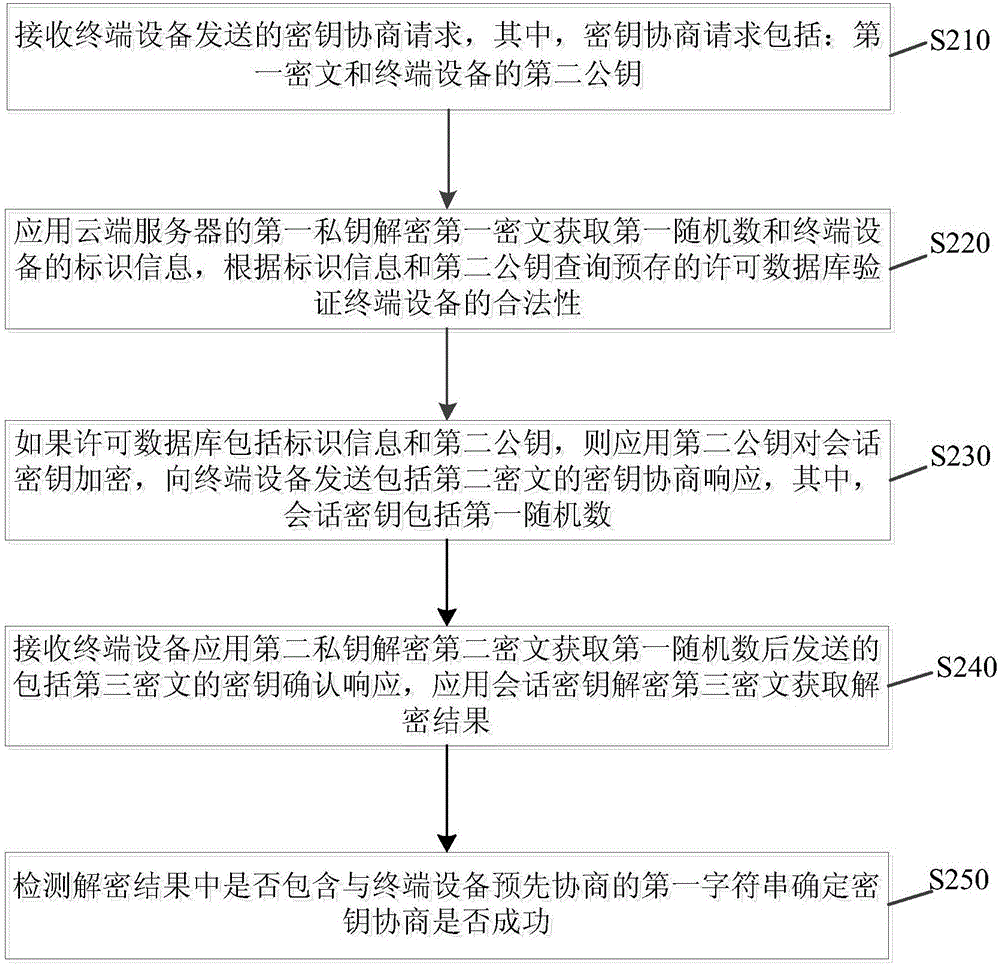
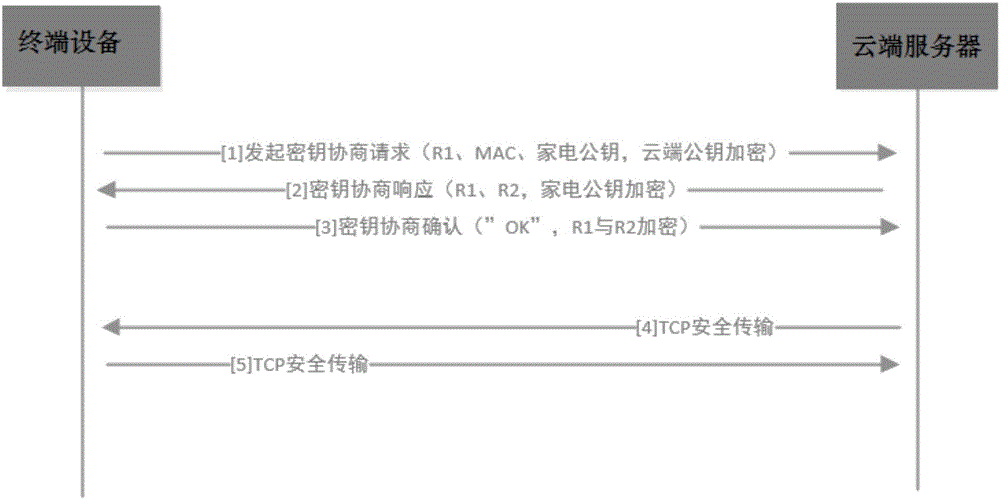
Method used
Image
Examples
Embodiment Construction
[0034] Embodiments of the present application are described in detail below, examples of which are shown in the drawings, wherein the same or similar reference numerals denote the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary, and are intended to explain the present application, and should not be construed as limiting the present application.
[0035] The method and device for key agreement in the embodiments of the present application are described below with reference to the accompanying drawings.
[0036] Usually, when SSL provides security services for network communication, it uses a CA certificate on the device side, encrypts and decrypts through the public-private key pairing of the device, and completes the authentication of the server.
[0037] For example, the terminal device sends a connection request to the server, and the server sends its own CA certif...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More