Data Security Communication Method
A communication method and data security technology, applied in the field of data communication, can solve the problems that the owner of the password cannot actively modify, the data is not completely consistent, and lack of initiative, etc., to shorten the establishment time, increase the speed of the handshake agreement, and reduce power consumption. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
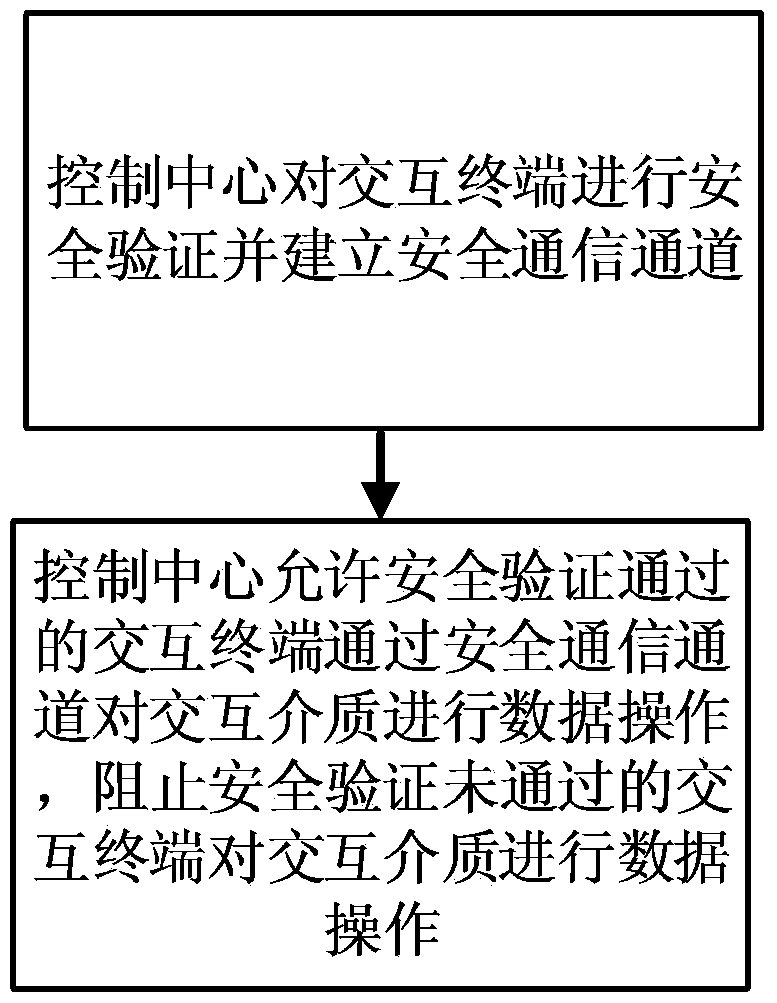
[0042] see figure 1 , the data security communication method of the present embodiment, comprises the following steps:
[0043] A data security communication method, comprising the steps of:
[0044] 1) The control center performs security verification on the interactive terminal and establishes a secure communication channel; specifically includes the following steps:
[0045]101) The interactive terminal queries the cached session connection information with the control center, uses the digest algorithm cached in the session connection information to perform digest calculation on the session key, and writes the session number and the digest calculation result into the connection application packet;
[0046] 102) The interactive terminal queries the cached control center certificate, and writes the serial number of the control center certificate and the serial number of the interactive terminal certificate into the connection application packet;
[0047] 103) The interactiv...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More