A method, device and system for access control
An access control and equipment technology, applied in the field of information security, can solve the problems of breach of confidentiality and integrity, inability to guarantee confidentiality, and inability to combine confidentiality and integrity, so as to ensure confidentiality and integrity and ensure security. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
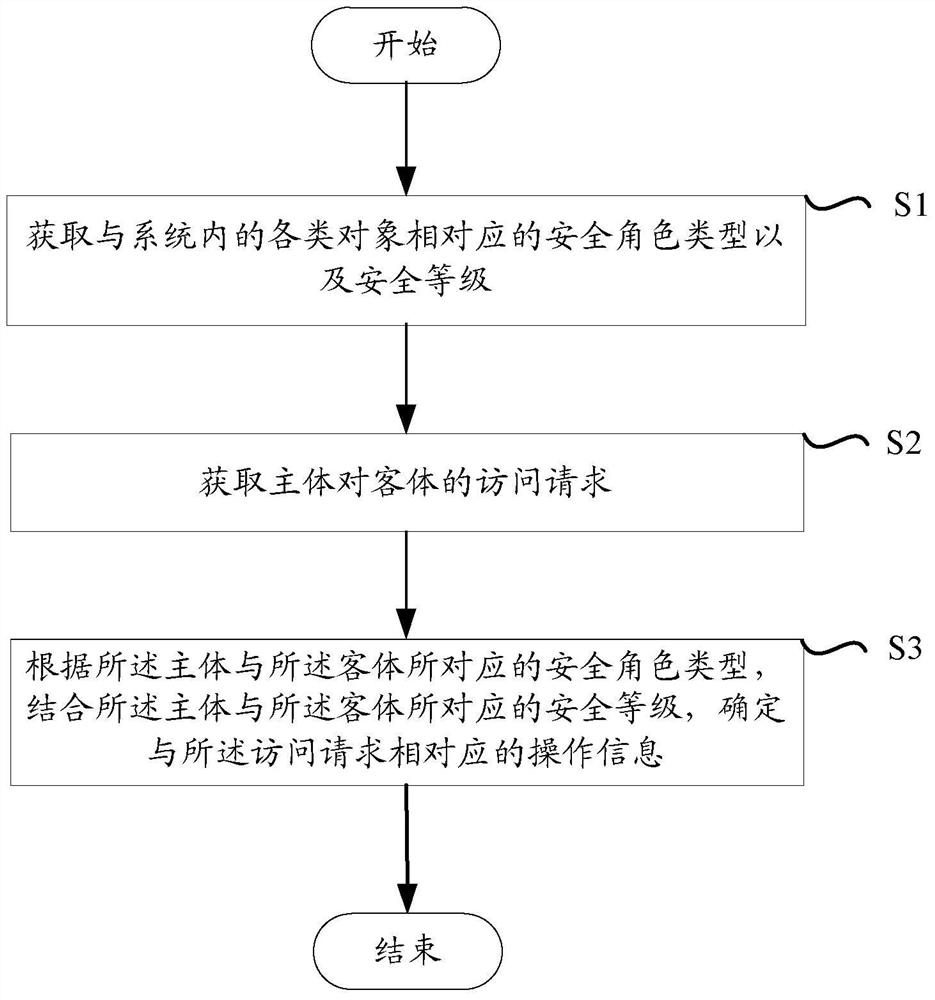
[0073] Before discussing the exemplary embodiments in more detail, it should be mentioned that some exemplary embodiments are described as processes or methods depicted as flowcharts. Although the flowcharts describe operations as sequential processing, many of the operations may be performed in parallel, concurrently, or simultaneously. In addition, the order of operations can be rearranged. The process may be terminated when its operations are complete, but may also have additional steps not included in the figure. The processing may correspond to a method, function, procedure, subroutine, subroutine, or the like.
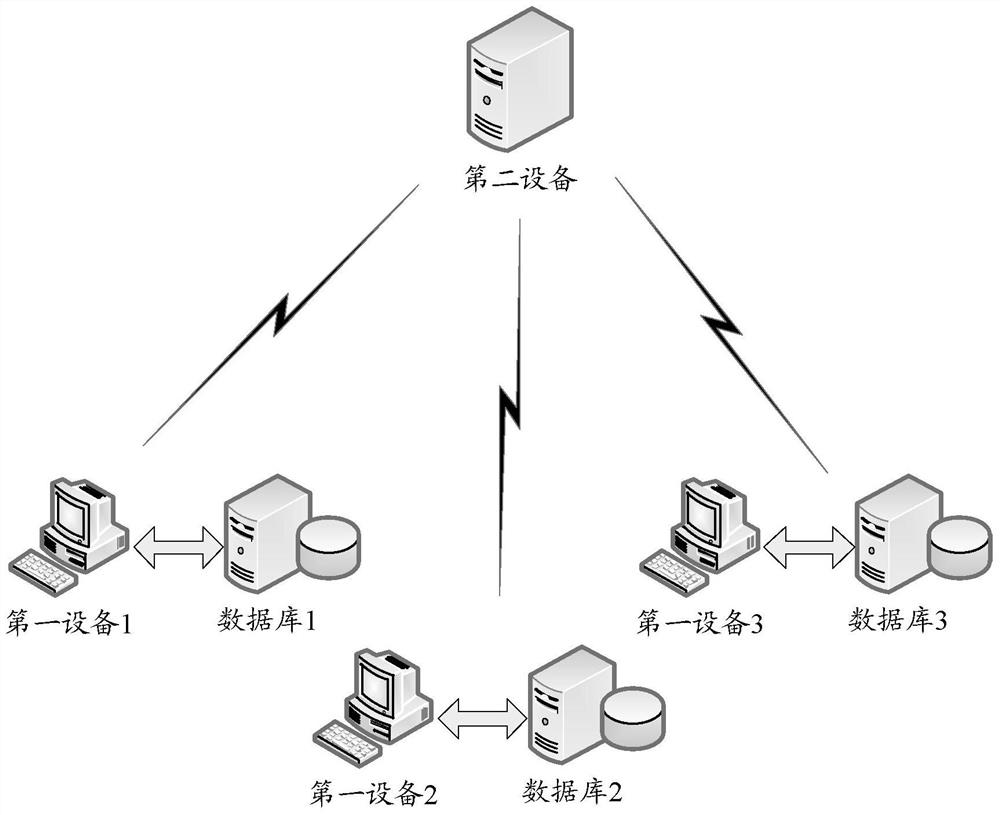
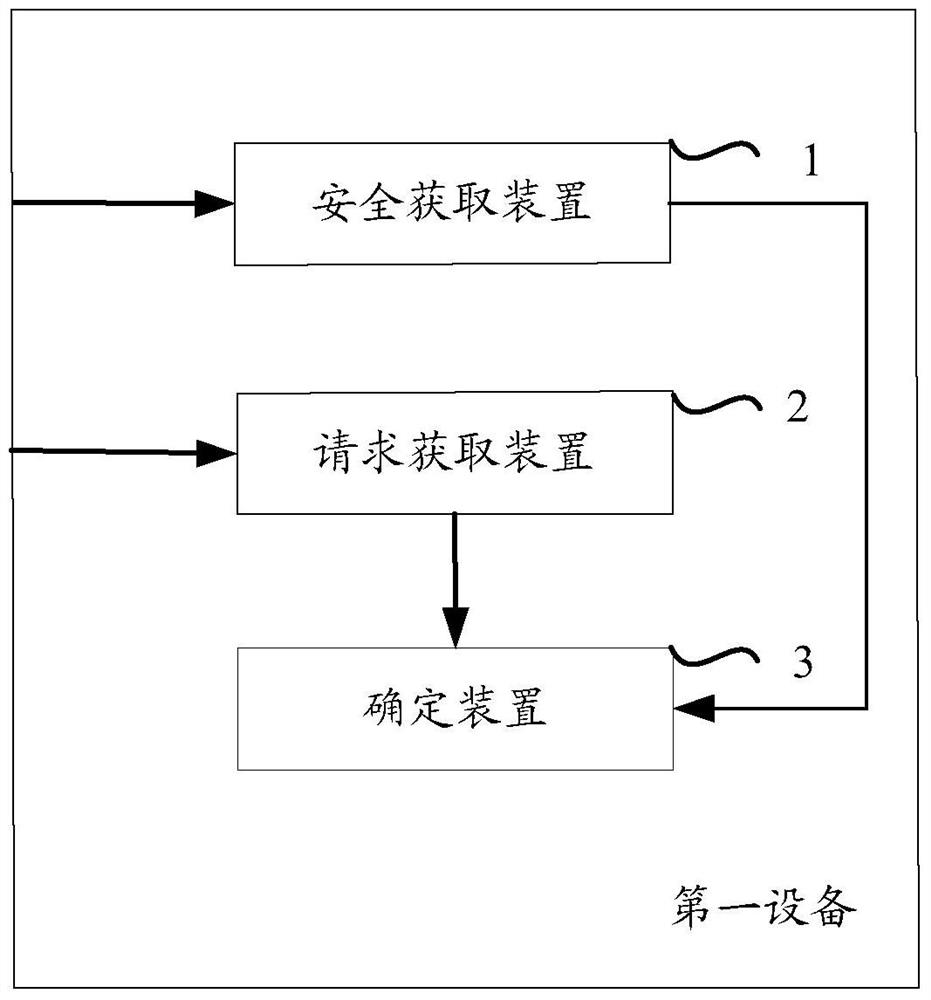
[0074] The "first device" and / or "second device" referred to in the context may include the "computer device" described below. The computer device, also referred to as "computer", refers to an intelligent electronic device that can perform predetermined processing procedures such as numerical calculations and / or logical calculations by running predetermined pro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More