Anomaly detection method and device based on host network behaviors
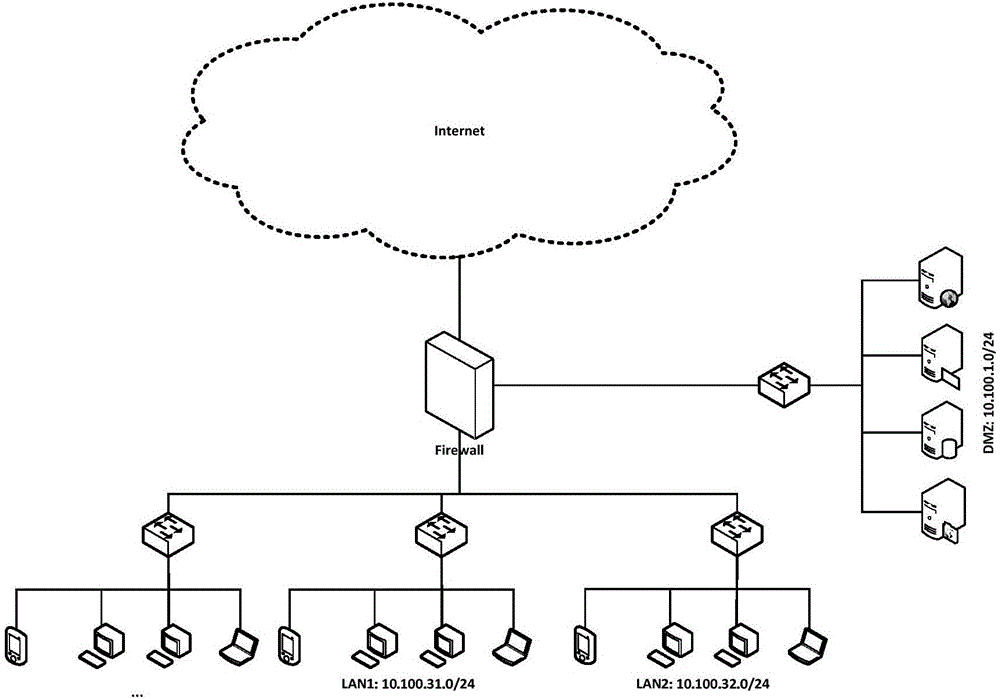
A host network, anomaly detection technology, applied in the Internet field, can solve problems such as detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
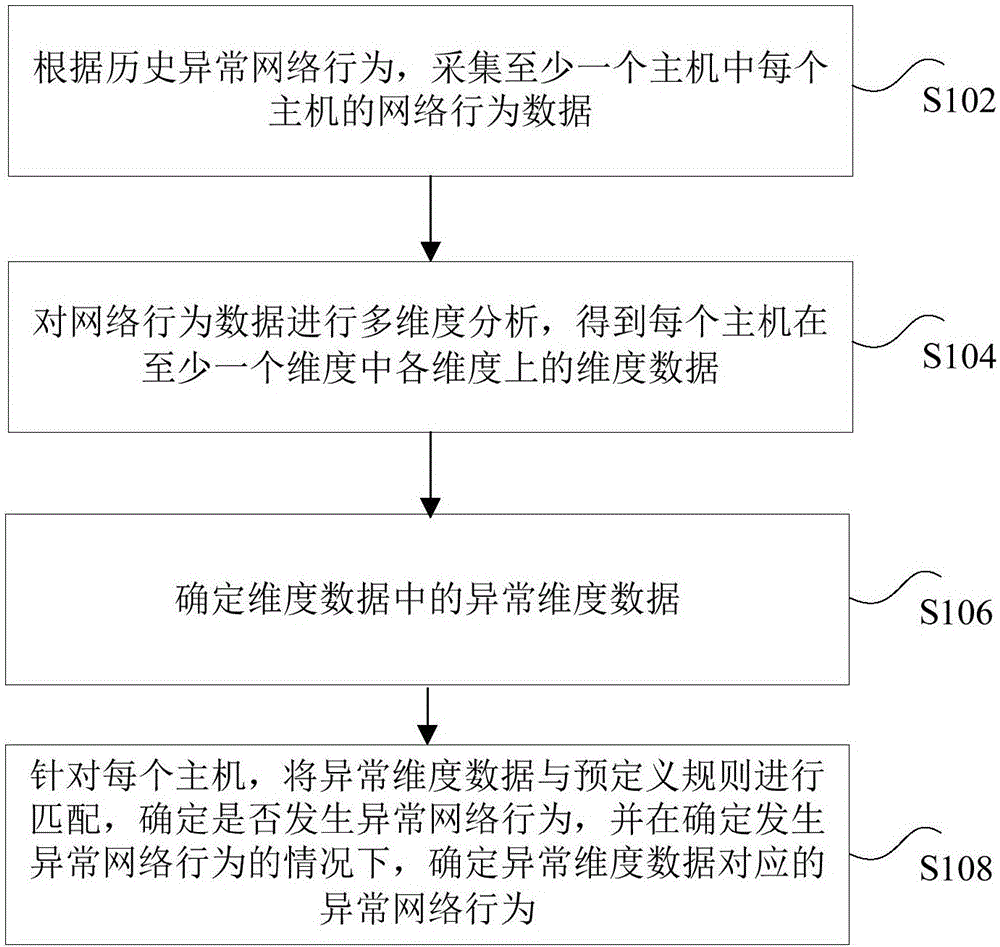
[0023] According to an embodiment of the present invention, a method embodiment of an anomaly detection method based on host network behavior is provided. It should be noted that the steps shown in the flowchart of the accompanying drawings can be implemented in a computer system such as a set of computer-executable instructions. and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that herein.
[0024] figure 2 is an anomaly detection method based on host network behavior according to an embodiment of the present invention, such as figure 2 As shown, the method includes the following steps:
[0025] Step S102: Collect network behavior data of each host in the at least one host according to the historical abnormal network behavior.
[0026] Specifically, the common network behaviors, that is, abnormal network behaviors, can be extracted according to the network behaviors of the existi...
Embodiment 2
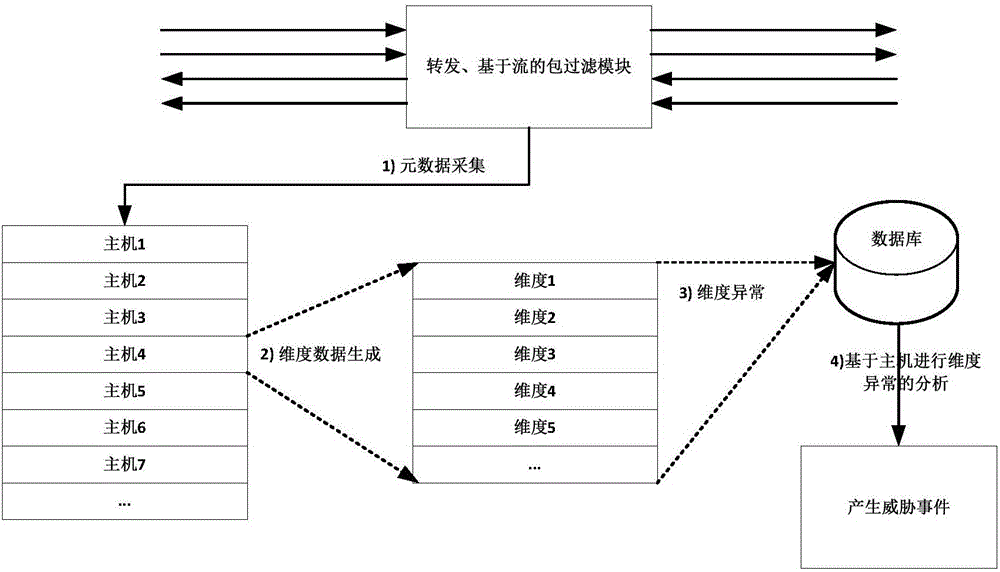
[0053] According to an embodiment of the present invention, a product embodiment of an abnormality detection device based on host network behavior is provided, Figure 4 is an anomaly detection device based on host network behavior according to an embodiment of the present invention, such as Figure 4 As shown, the device includes an acquisition module 101 , an analysis module 103 , a determination module 105 and a matching module 107 .
[0054] Among them, the collection module 101 is used to collect the network behavior data of each host in the at least one host according to the abnormal historical network behavior; the analysis module 103 is used to perform multi-dimensional analysis on the network behavior data, and obtain at least one dimension of each host. The dimensional data on each dimension in the dimensional data; the determination module 105 is used to determine the abnormal dimension data in the dimensional data; the matching module 107 is used to match the abnor...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More