A Privacy Protection Method in Sensitive Data Publishing
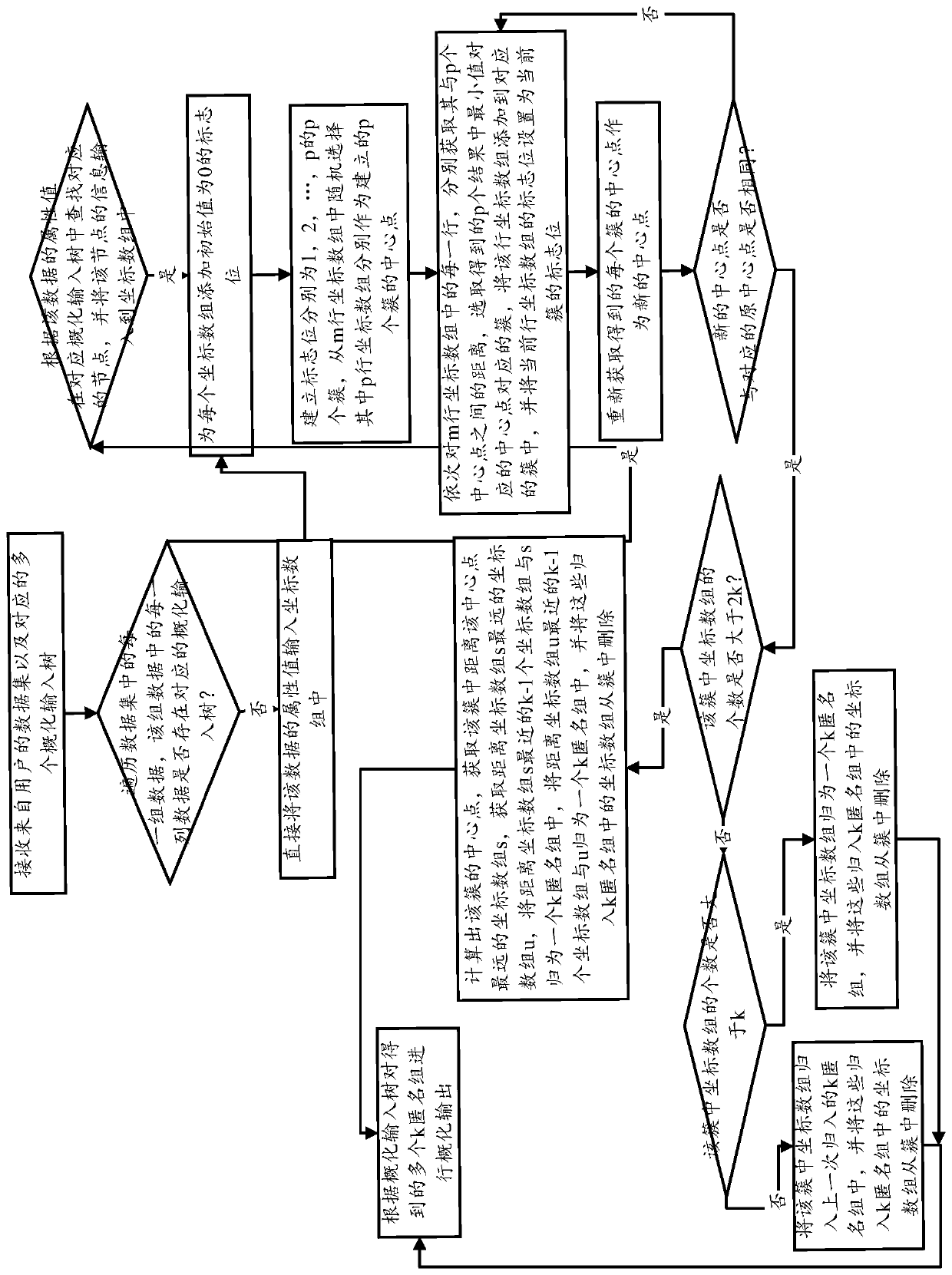
A privacy protection and sensitive data technology, applied in the field of privacy protection, can solve problems such as inaccurate similarity calculation and unreasonable allocation of k-anonymous groups, and achieve the effect of accurate similarity calculation, ensuring rational allocation, and reducing execution time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
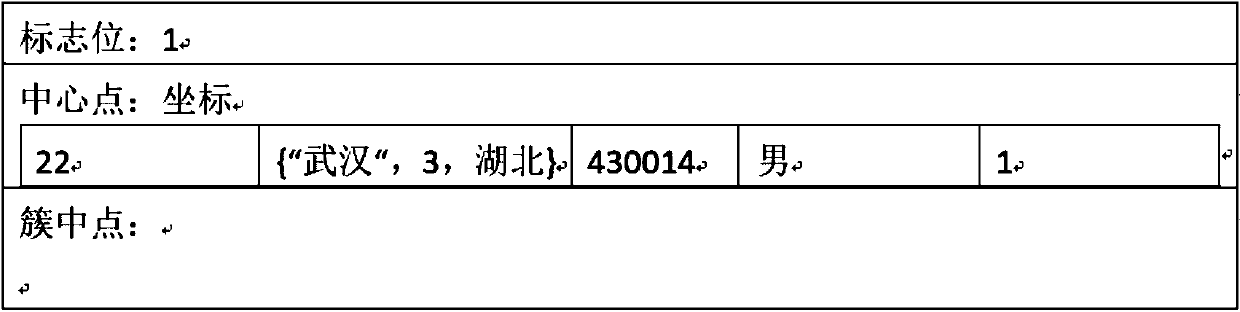
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
[0038] Below at first explain and illustrate with regard to the technical terms of the present invention:
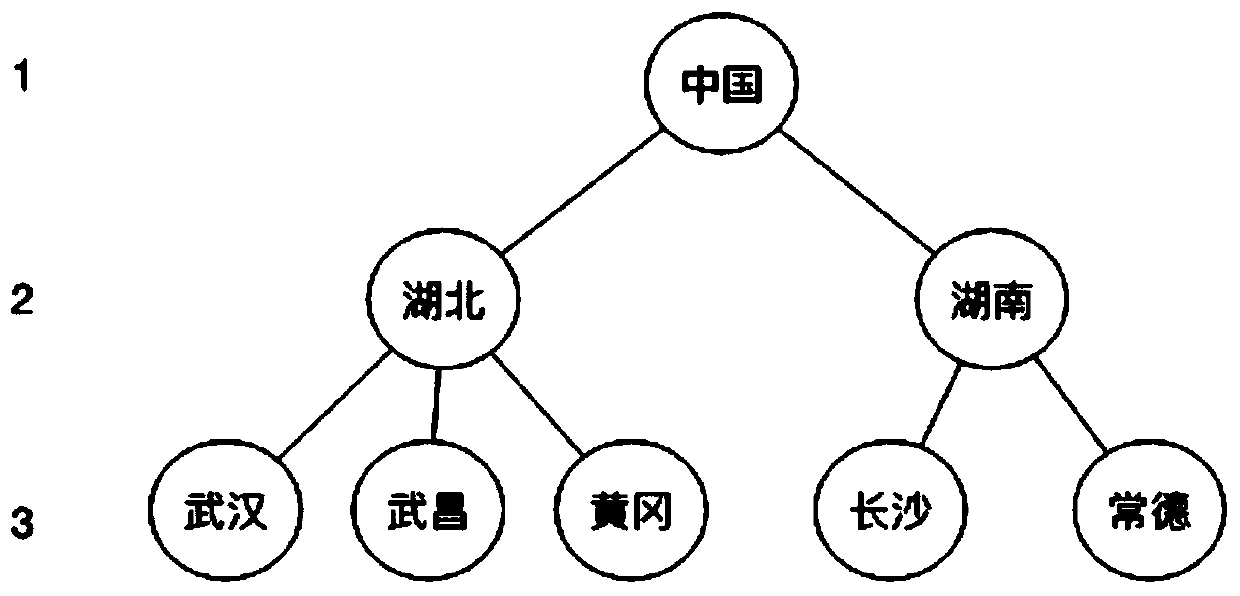
[0039] Identifiers and quasi-identifiers. For a set of data, what can uniquely identify the user becomes an identifier, such as name, ID number, etc. Quasi-Identifiers (QI) are those that cannot uniquely identify a user but have an attribute or a combination of attributes that belong to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More