Merkle hash summation tree and verifiable database updating operation method using same
An operation method and database technology, applied in the field of verifiable databases, can solve the problem that the VDB scheme cannot support efficient all update operations and verification operations at the same time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0045] The application principle of the present invention will be described in detail below in conjunction with the accompanying drawings.
[0046] The Merkle hash summation tree provided by the embodiment of the present invention
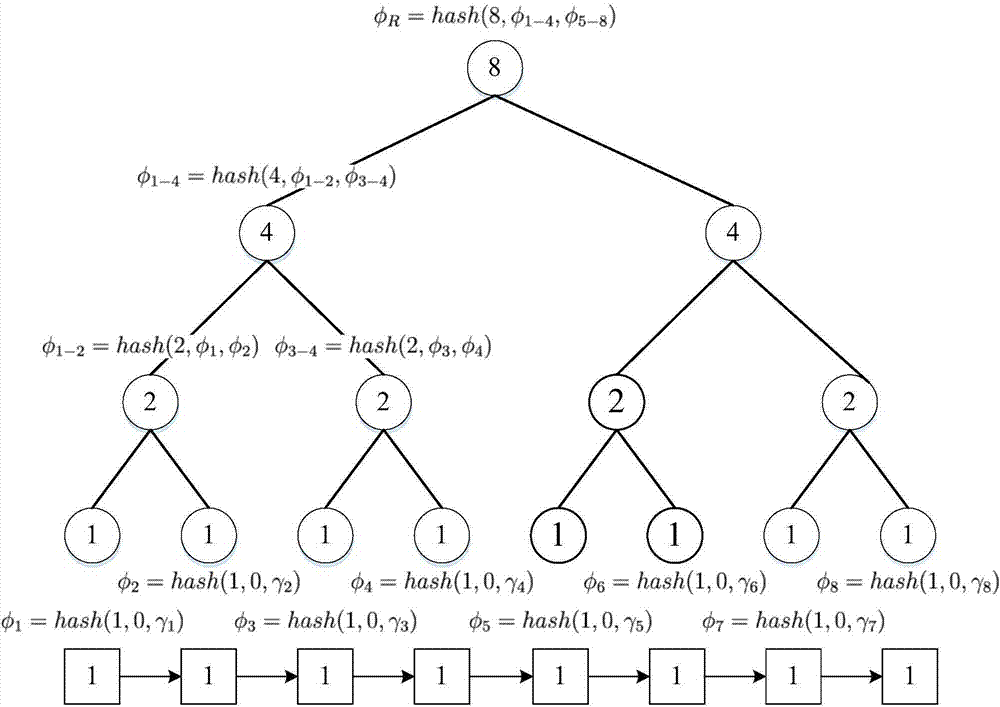
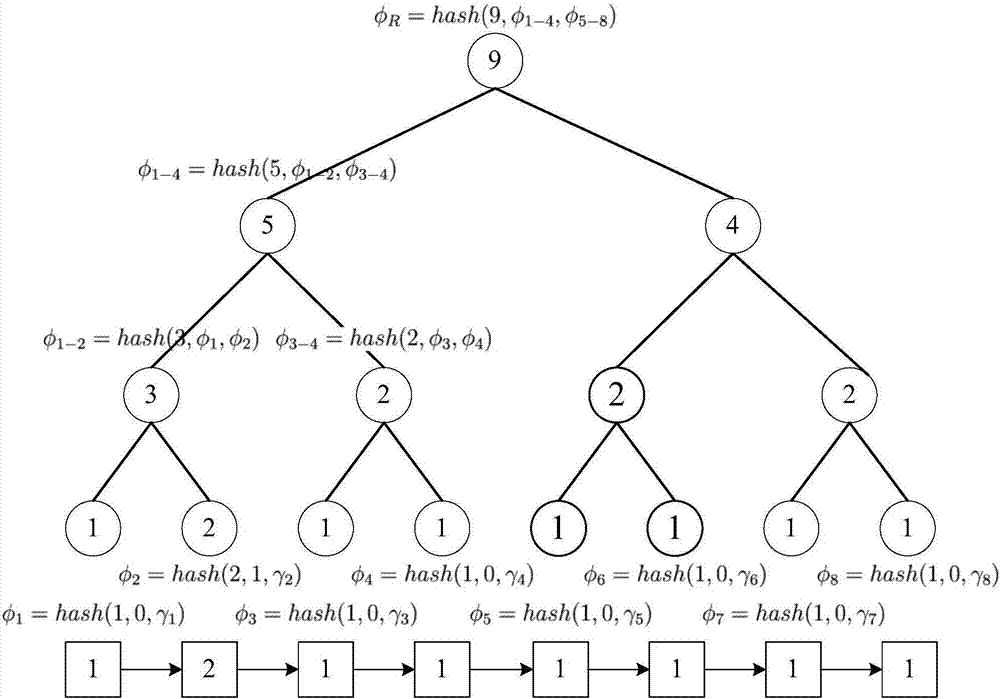
[0047] Such as figure 1 As shown, the construction method of the Merkle hash summation tree provided by the embodiment of the present invention includes the following steps:
[0048] (1) Select SHA-256 as a secure hash function (denoted as hash( )), given a database DB, there are eight records in total, respectively (x 1 ,v 1 ),(x 2 ,v 2 )...(x 8 ,v 8 );
[0049] (2) For each leaf node...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More