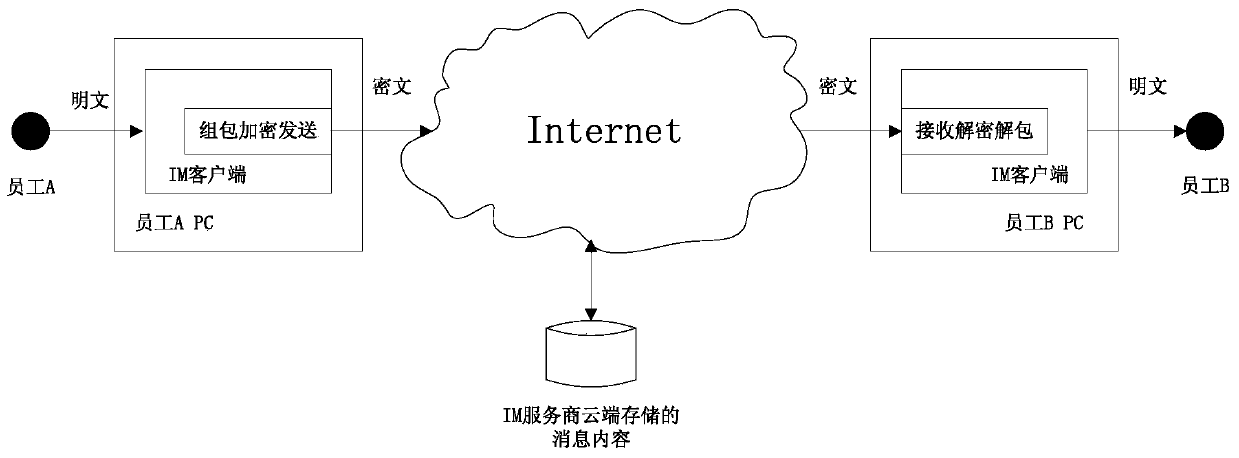
Method and device for message encryption and decryption
An encryption method and message technology, applied in the field of information security, can solve the problem of low security of IM messages and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
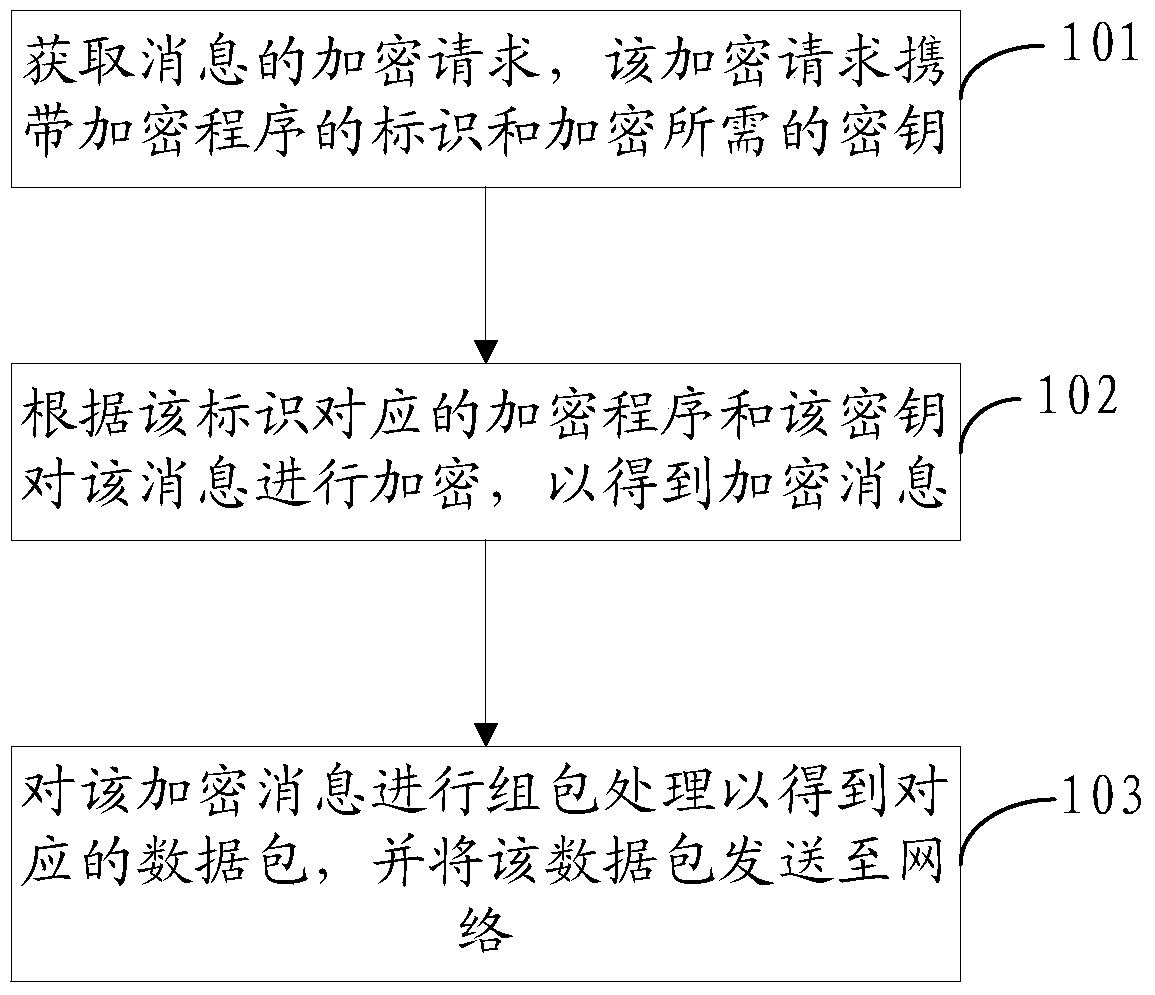
[0038] This embodiment will be described from the perspective of a message encryption device. Specifically, the message encryption device may be integrated in a terminal or other devices that need to perform message encryption.
[0039] A method for encrypting a message, comprising: obtaining an encryption request for a message, the encryption request carrying an identifier of an encryption program and a key required for encryption; encrypting the message according to the encryption program corresponding to the identifier and the key, to obtain encrypted message; performing packet processing on the encrypted message to obtain a corresponding data packet, and sending the data packet to the network.
[0040] Such as Figure 2a As shown, the specific flow of the message encryption method can be as follows:
[0041] 101. Acquire an encryption request of a message, where the encryption request carries an encryption program identifier and a key required for encryption.
[0042] Fo...
Embodiment 2
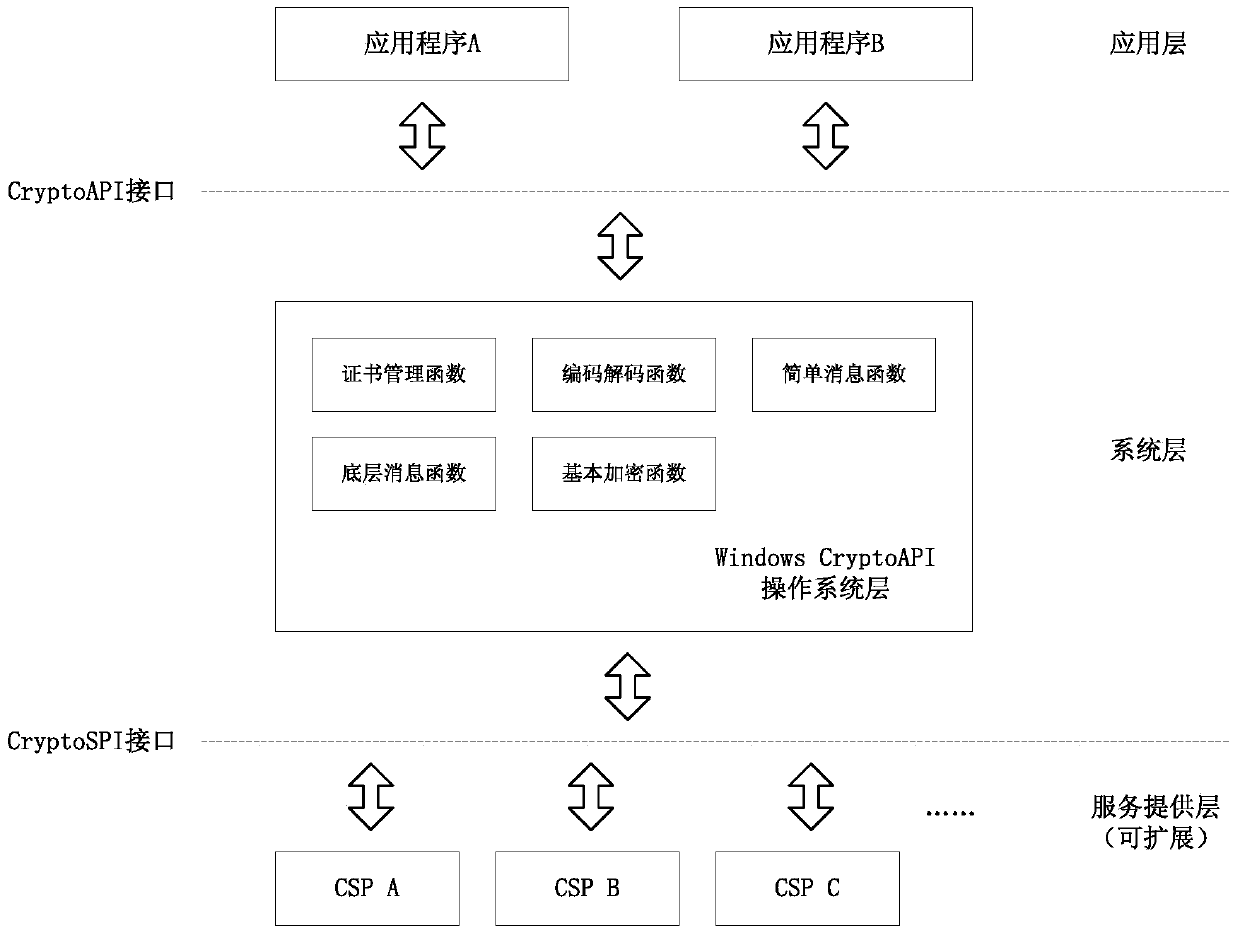
[0066] According to the method described in Embodiment 1, an example will be given below for further detailed description.
[0067] In this embodiment, description will be made by taking the message encryption device integrated in the terminal and the encryption program as CSP as an example.
[0068] Wherein, the message encryption device may be installed in the terminal in the form of a client or other software, for example, it may be installed in an IM client of the terminal.
[0069] Such as image 3 As shown, the specific flow of the message encryption method can be as follows:
[0070] 201. The terminal sends a configuration information acquisition request to a server, where the configuration information acquisition request carries a login account of the IM client.
[0071] For example, after the IM client on the terminal logs in, a configuration information acquisition request is sent to the cloud server on the IM service, and the request carries the login account of t...
Embodiment 3
[0095] This embodiment will be described from the perspective of a message decryption device, and the message decryption device may be integrated in a terminal or other devices that need to perform message decryption.
[0096] A method for decrypting a message, comprising: obtaining a data packet through a network, and performing unpacking processing on the data to obtain an encrypted message; obtaining a decryption request for the encrypted message, the decryption request carrying the identifier of the decryption program and the encryption required for decryption key; decrypt the encrypted message according to the decryption program corresponding to the identifier and the key to obtain the decrypted message.
[0097] Such as Figure 4 As shown, the specific flow of the message decryption method can be as follows:
[0098] 301. Obtain a data packet through the network, and perform unpacking processing on the data packet, so as to obtain an encrypted message.
[0099] For exa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More