HTTPS protocol analysis method, and system implementing method
A protocol analysis and separation technology, applied in transmission systems, digital transmission systems, other database retrieval, etc., can solve problems such as unsatisfactory traffic identification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
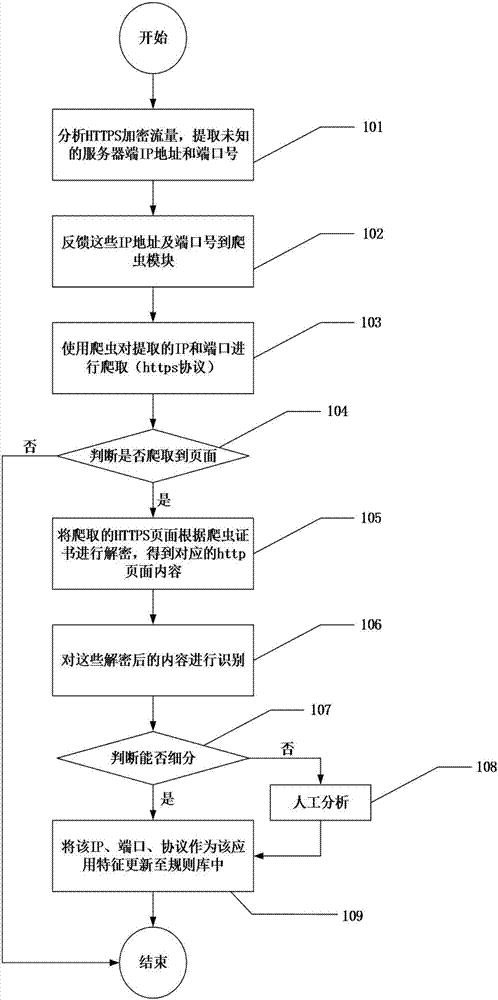
[0030] Refer to the attached figure 1 The present invention will be described in detail below.
[0031] HTTPS protocol analysis method of the present invention is realized in the following manner, comprises the following steps:
[0032] Step 101, separating the HTTPS encrypted traffic from the data packet, and extracting the unknown server-side IP address and corresponding port number from the HTTPS encrypted traffic;
[0033] Step 102, feeding back the IP address and the corresponding port number to the crawler module;
[0034] Step 103, using a crawler to crawl the IP address and the corresponding port number;
[0035] Step 104, decrypting the crawled HTTPS page according to the crawler certificate to obtain the corresponding http page content;
[0036] Step 105, identifying the http page;
[0037] Step 106, determine the application to which the http page belongs;
[0038] Step 107, after determining the application to which the http page belongs, updating the IP addre...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com