Authentication method and device
An authentication and triggering technology, applied in the field of communication, can solve problems such as low security, and achieve the effect of improving security, increasing privacy and fun.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
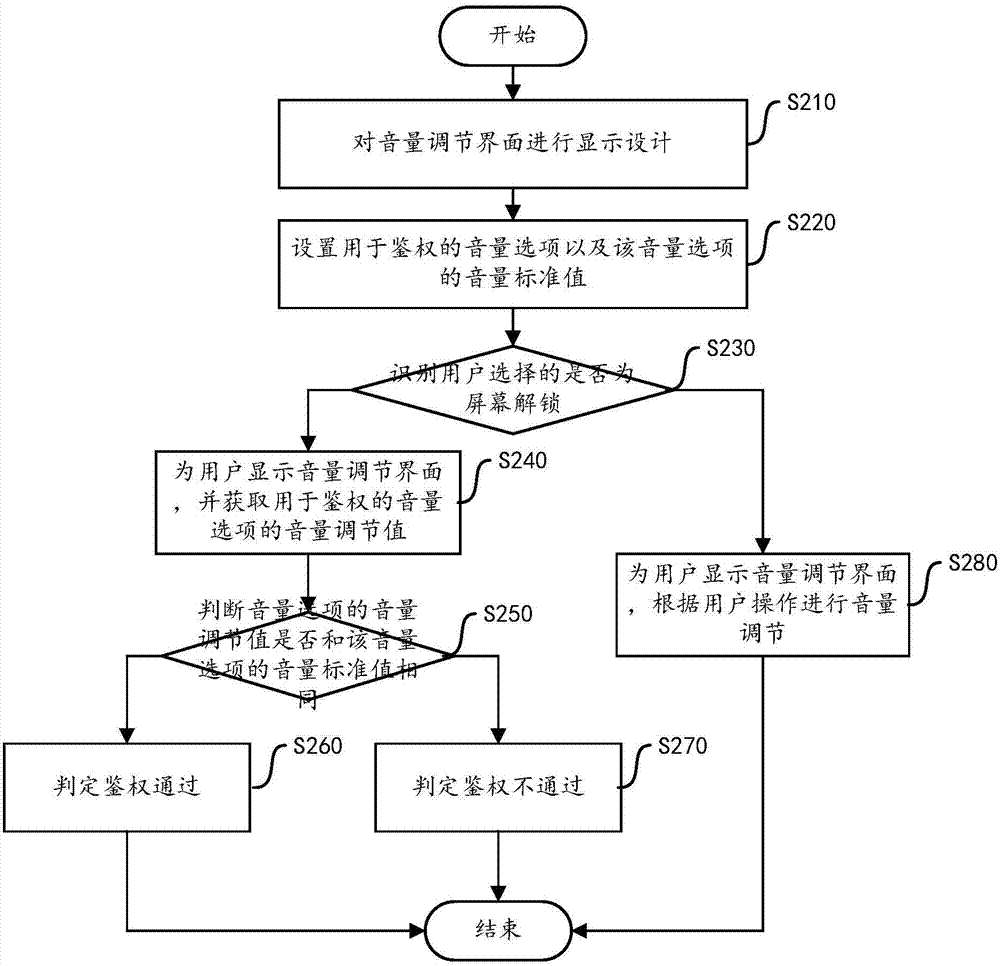
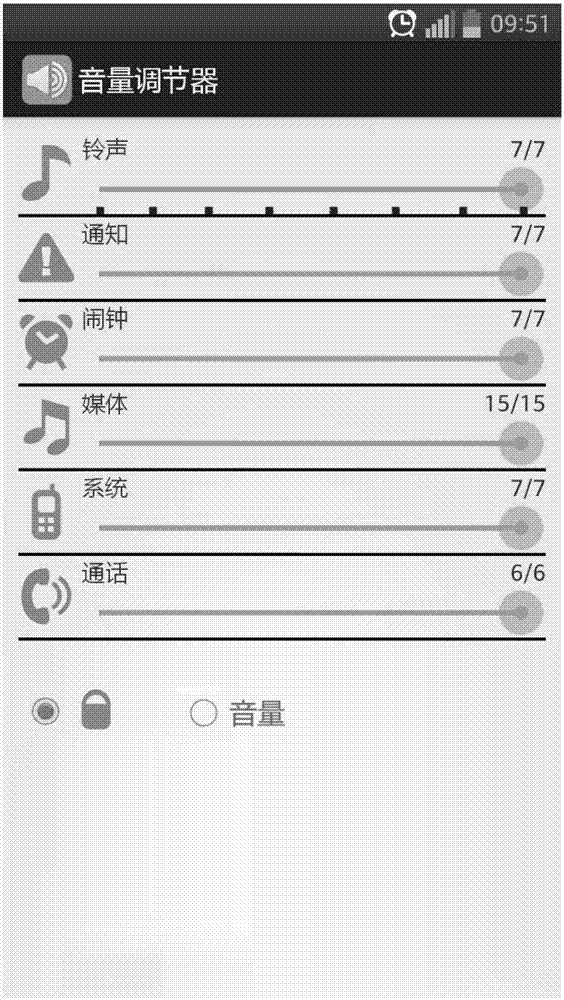
[0022] The authentication method of the present invention uses the volume value of the volume option as the authentication password (volume standard value), and adjusts the volume value of the volume option according to the preset volume standard value during authentication, so as to achieve the purpose of fast decryption. The invention makes it impossible for others to accurately record or crack passwords, improves the security of authentication, and increases the confidentiality and interest of authentication.
[0023] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
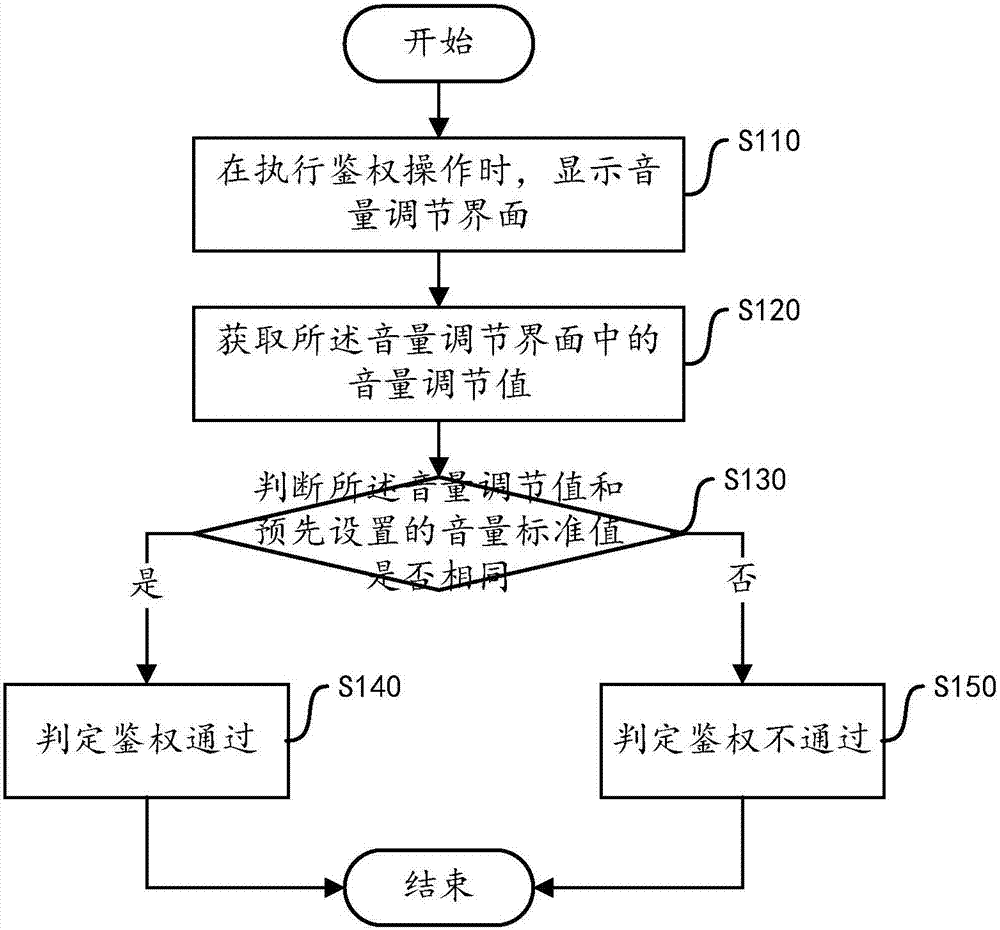
[0024] According to an embodiment of the present invention, an authentication method is provided, figure 1 is a flowchart of an authentication method according to an embodiment of the present invention. The execution subject of...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap