Identity authentication method, apparatus and device
An identity verification method and identity verification technology, applied in the field of devices and equipment, and identity verification methods, can solve problems such as poor convenience and long user operation process, and achieve the effects of improving security, shortening operation process, and improving convenience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
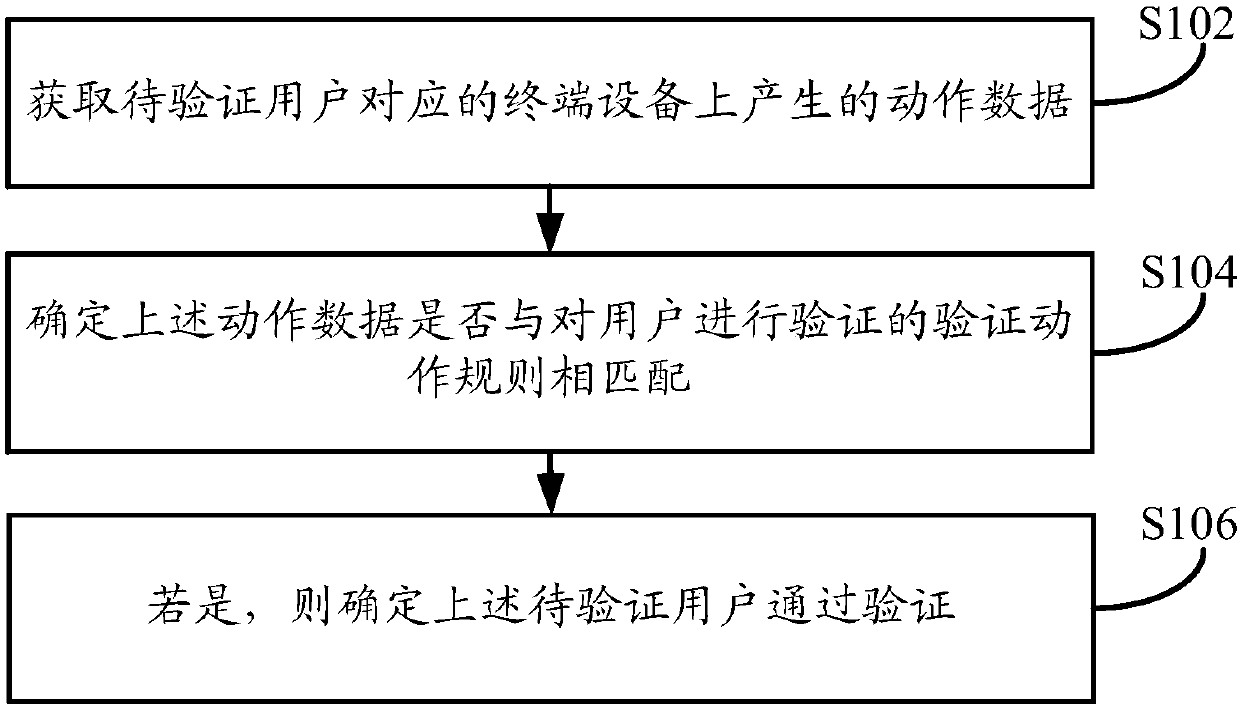
[0075] like figure 1 As shown, the embodiment of the present application provides an identity verification method. The execution body of the method can be a terminal device or a server, and the terminal device can be a mobile terminal device such as a mobile phone or a tablet computer, or a terminal device such as a personal computer. The device and the server can be an independent server, or a server cluster composed of multiple servers. In the embodiment of the present application, in order to improve the efficiency of identification, the execution subject of the method takes the server as an example to describe in detail. For the case of the terminal device, it can refer to the specific processing and execution of the server below, and details will not be repeated here. The method specifically may include the following steps:
[0076] In step S102, the action data generated on the terminal device corresponding to the user to be verified is acquired.
[0077] Wherein, the ...
Embodiment 2
[0090] like image 3 As shown, the embodiment of the present application provides an identity verification method. The execution body of the method can be a terminal device or a server, and the terminal device can be a mobile terminal device such as a mobile phone or a tablet computer, or a personal computer, etc. For the terminal device, the server can be an independent server, or a server cluster composed of multiple servers. In the embodiment of the present application, in order to improve the efficiency of identification, the execution subject of the method takes the server as an example to describe in detail. For the case of the terminal device, it can refer to the specific processing and execution of the server below, and details will not be repeated here. The method specifically may include the following steps:
[0091] In step S302, an identity verification request initiated by a user to be verified is received.
[0092] In implementation, personal information securi...
Embodiment 3
[0116] Combined with practical application scenarios, such as Figure 4 As shown, the embodiment of the present application also provides an identity verification method. The execution body of the method may be a terminal device or a server, and the terminal device may be a mobile terminal device such as a mobile phone or a tablet computer, or may be a personal computer, etc. For the terminal device, the server can be an independent server, or a server cluster composed of multiple servers. In the embodiment of the present application, in order to improve the efficiency of identification, the execution subject of the method takes the server as an example to describe in detail. For the case of the terminal device, it can refer to the specific processing and execution of the server below, and details will not be repeated here. The method specifically may include the following steps:
[0117] In step S402, according to the information of the user to be paid, a corresponding verif...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More