Cyber threat intelligence generation method and system
A network and intelligence technology, applied in the field of information processing, can solve problems such as complex types, large amounts of data, and unidentified
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] Below in conjunction with accompanying drawing and embodiment, the specific embodiment of the present invention is described in further detail. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
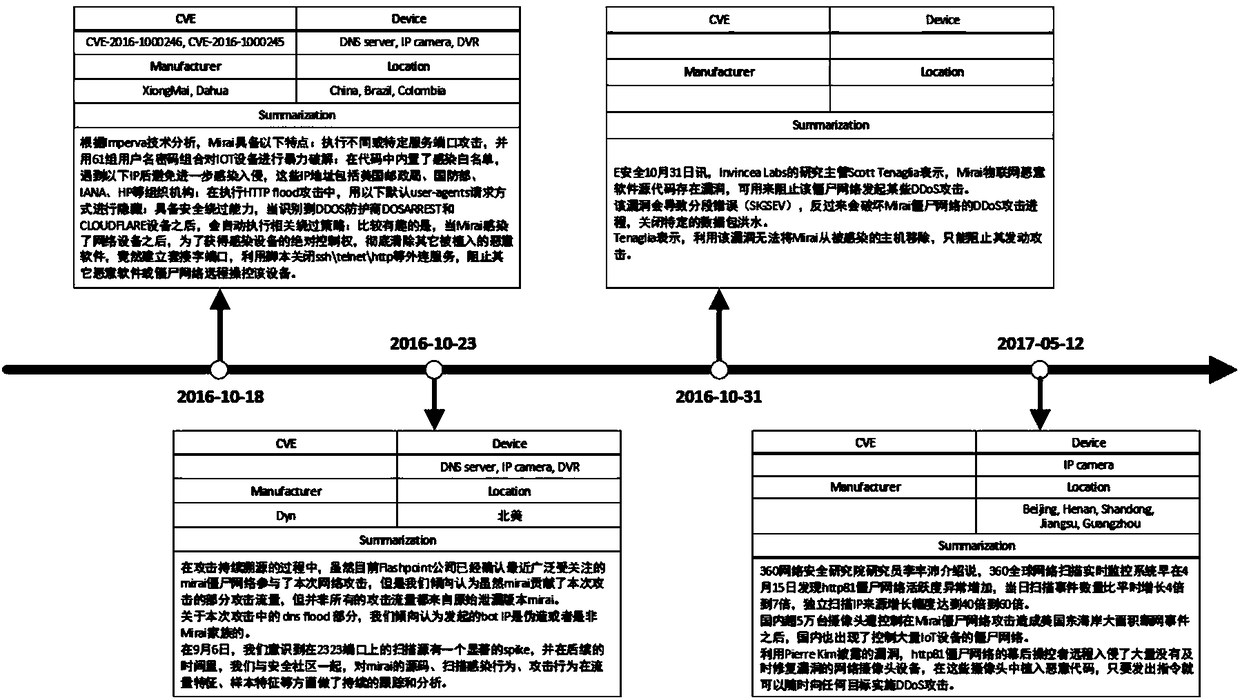
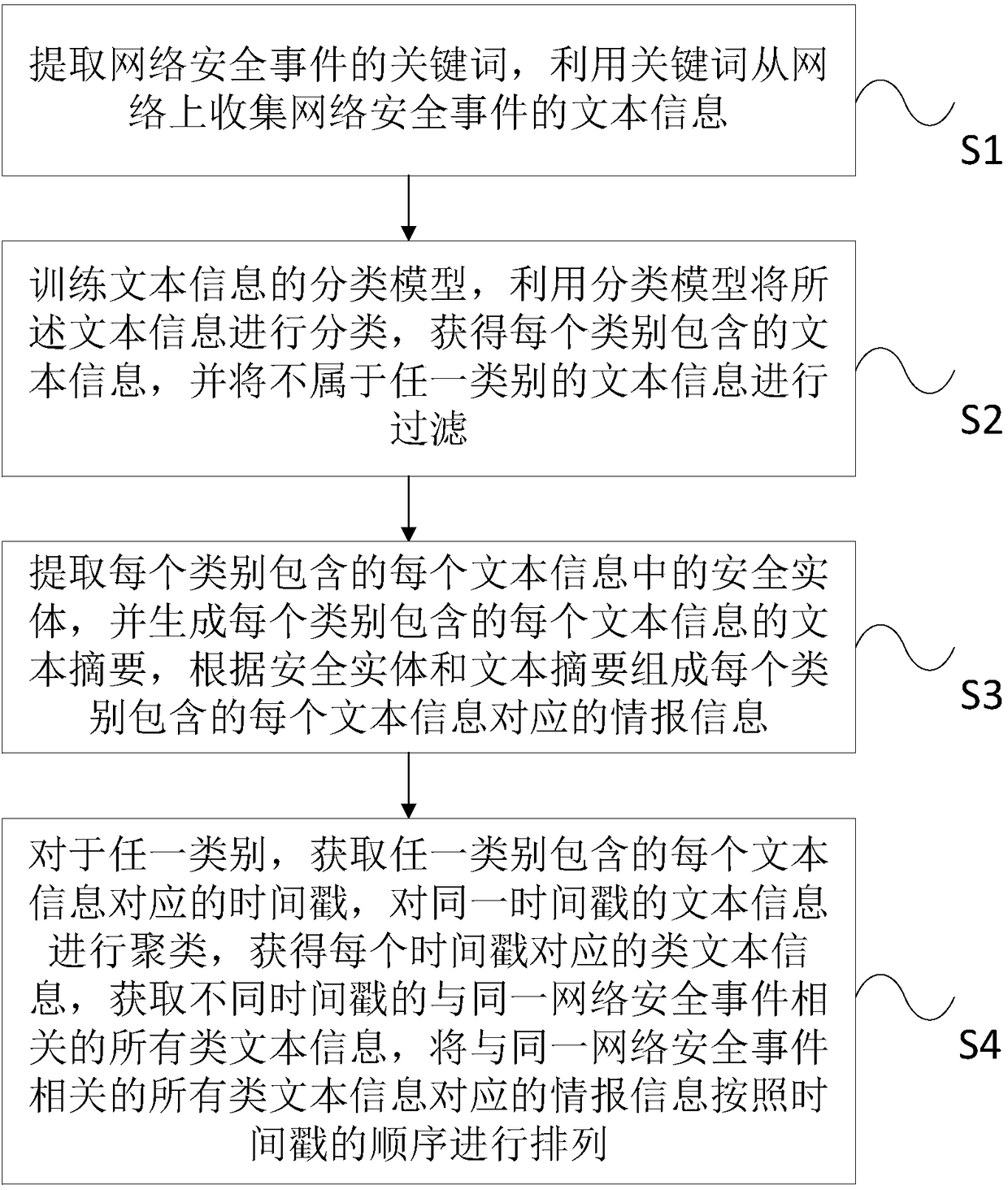
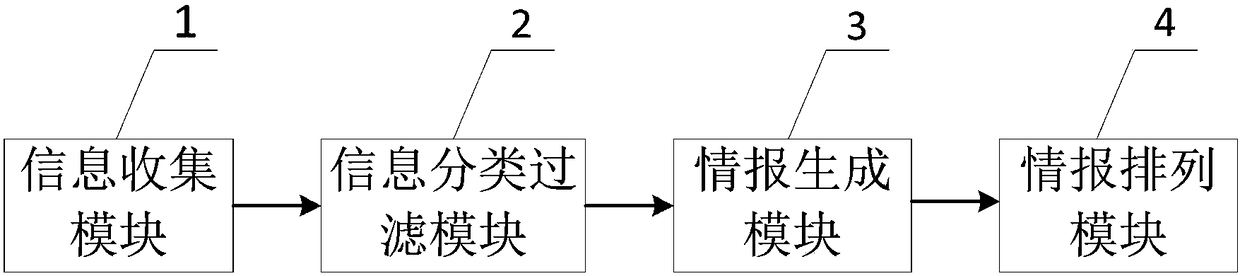
[0036] figure 1 It is a schematic diagram of the overall flow of a method for generating network threat intelligence according to an embodiment of the present invention, such as figure 1 As shown, the present invention provides a method for generating network threat intelligence, including:
[0037] S1, extracting keywords of network security incidents, using the keywords to collect text information of the network security incidents from the network;
[0038] S2, training the classification model of the text information, using the classification model to classify the text information, obtaining the text information contained in each category, and filtering the text information that does not b...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More