A virtualized cloud cipher system based on cloud computing and its implementation method
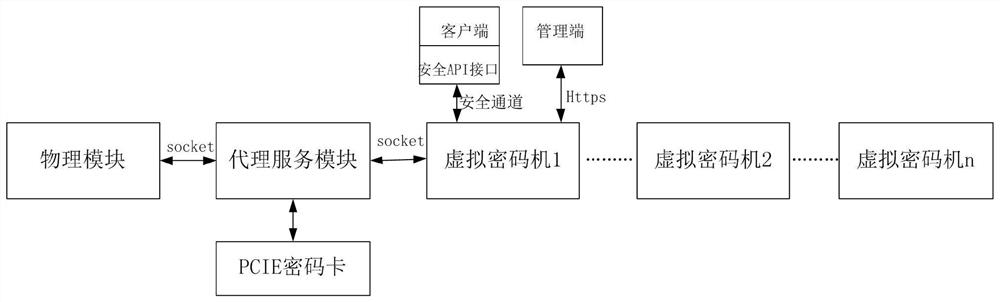
A virtual cryptographic machine and virtualized cloud technology, applied in the field of virtualized cloud cryptographic machine system, can solve the problems of low computing performance, cryptographic card does not support multi-thread encryption mode, low performance, etc., to ensure independence and save equipment resources The effect of investment and high availability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
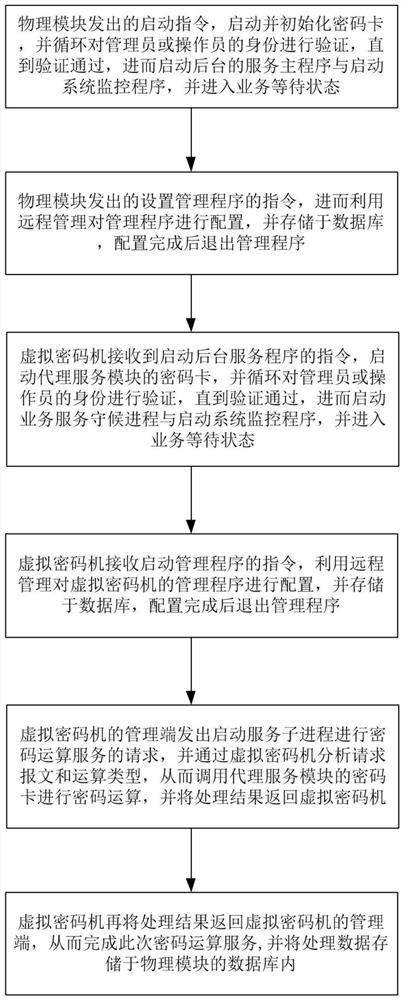
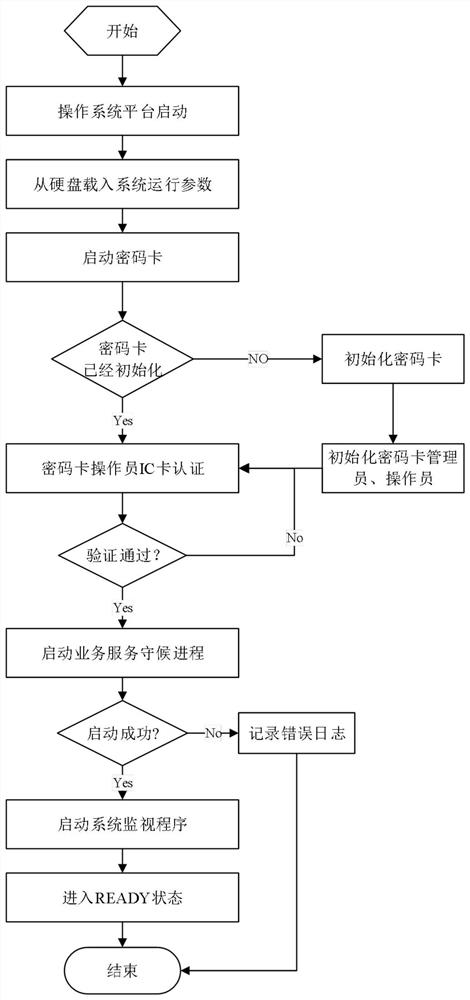
[0044] Such as figure 1 As shown, the implementation method of a virtualized cloud cipher machine system based on cloud computing disclosed by the present invention includes the following steps:
[0045] (1) Stored in the database, exit the management program after the configuration is completed;
[0046] (2) The virtual cipher machine receives the instruction to start the background service program, starts the cipher card of the agent service module, and cyclically verifies the identity of the administrator or operator until the verification is passed, and then starts the business service waiting process and starts the system monitoring program, and enter the business waiting state;
[0047] (3) The virtual cipher machine receives an instruction to start the management program, uses remote management to configure the management program of the virtual cipher machine, and stores it in the database, and exits the management program after the configuration is completed;
[0048...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More