Vulnerability mining method and device, and readable storage medium
A vulnerability mining and vulnerability technology, which is applied in the field of vulnerability mining methods, devices and readable storage media, can solve the problems of low application security and few security vulnerabilities, so as to improve security, reduce vulnerability detection, and improve vulnerability detection efficiency. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
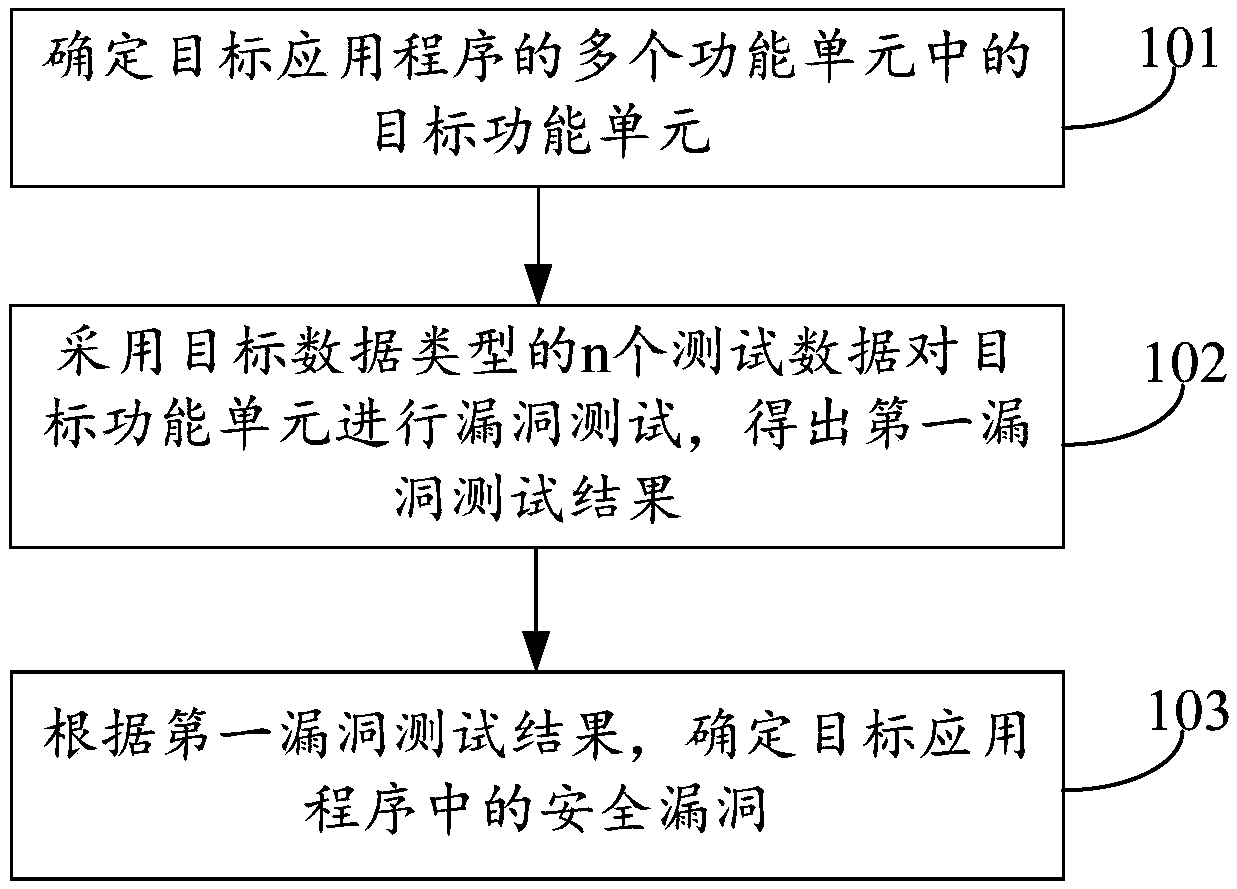
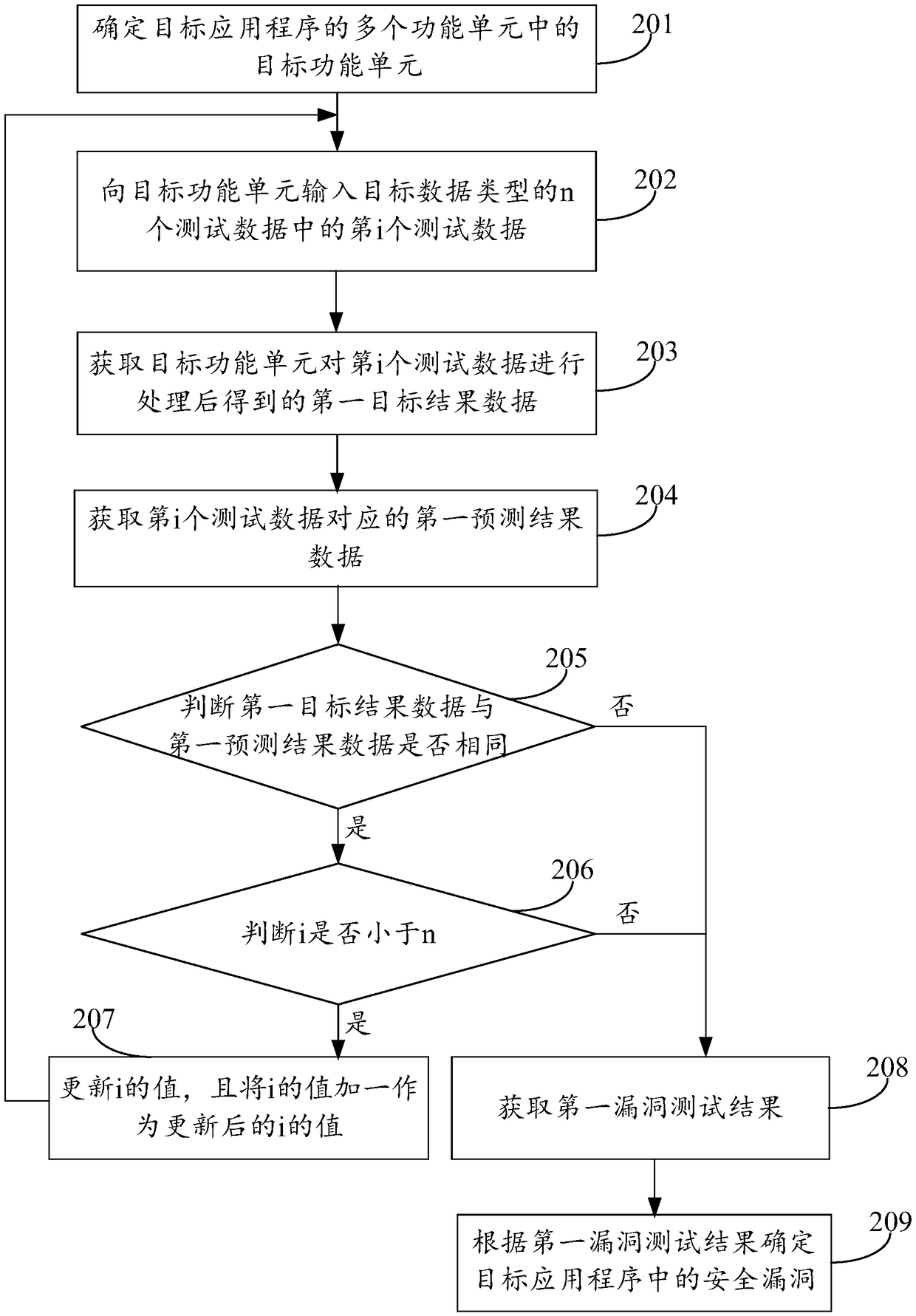
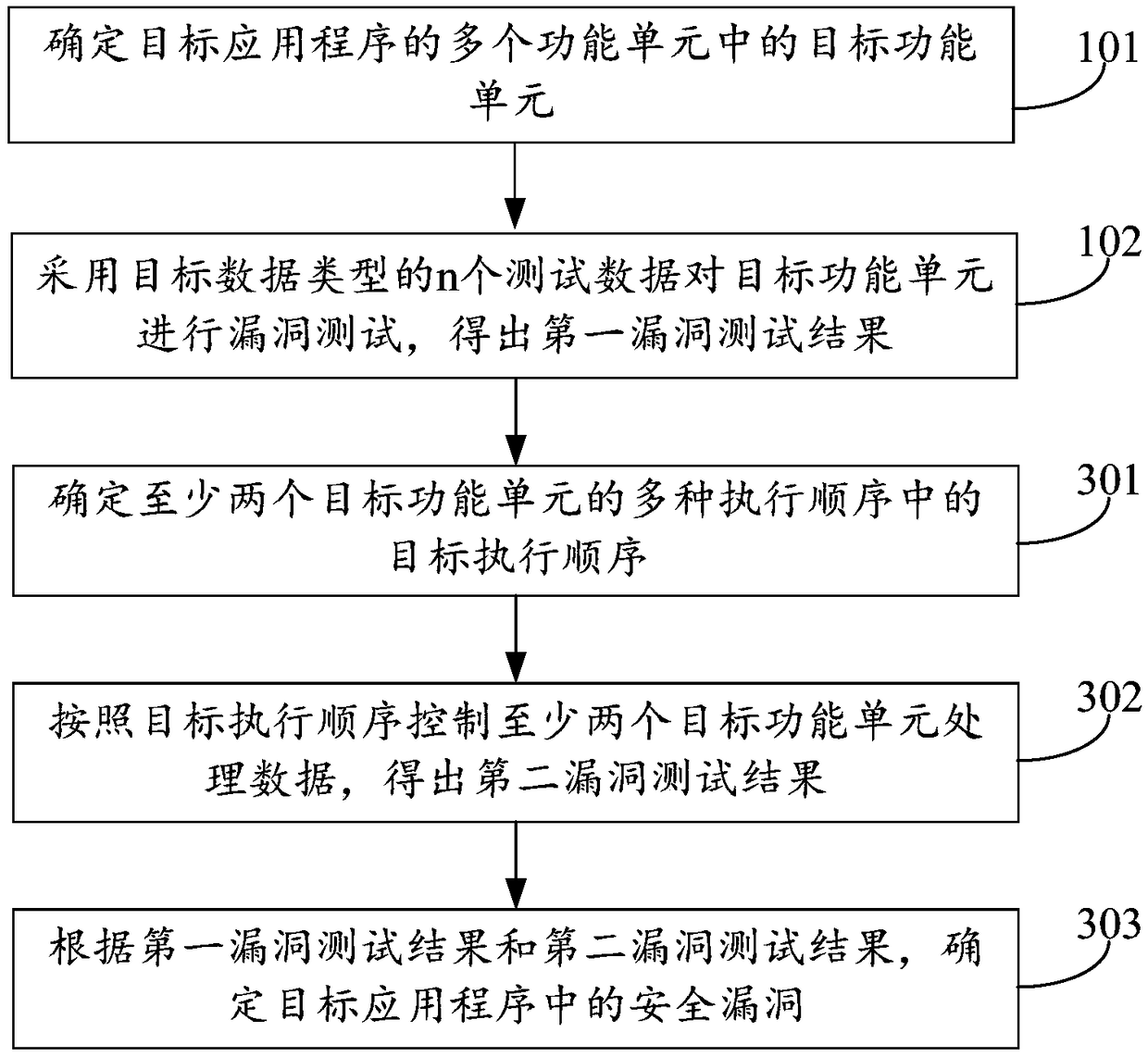
Image
Examples
Embodiment Construction
[0081] In order to make the purpose, technical solutions and advantages of the present disclosure clearer, the present disclosure will be further described in detail below in conjunction with the accompanying drawings. Apparently, the described embodiments are only some of the embodiments of the present disclosure, not all of them. Based on the embodiments in the present disclosure, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present disclosure.
[0082] With the rapid development of network communication technology, the security of application programs has attracted much attention. Usually, before the application is put into use, the fuzzing method is used to mine the application for vulnerabilities, so as to find as many security vulnerabilities as possible in the application, and then the discovered security vulnerabilities can be repaired to reduce the risk of the application before ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More