Security protection methods, mobile terminal and memory medium
A mobile terminal, security protection technology, applied in the field of communication, can solve the problems of inability to call for help from emergency contacts, emergency contacts for help, etc., to achieve the effect of precious rescue time and avoid failure to call for help
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] The present invention will be further described below with reference to the accompanying drawings and specific embodiments. It should be noted that, on the premise of no conflict, the embodiments or technical features described below can be combined arbitrarily to form new embodiments. .
[0040] Embodiments of the present invention provide a security protection method, and a mobile terminal and storage medium using the method, which can send an alarm message to an emergency contact when a user does not operate for a long time, so as to timely discover that an accident occurs to the user.
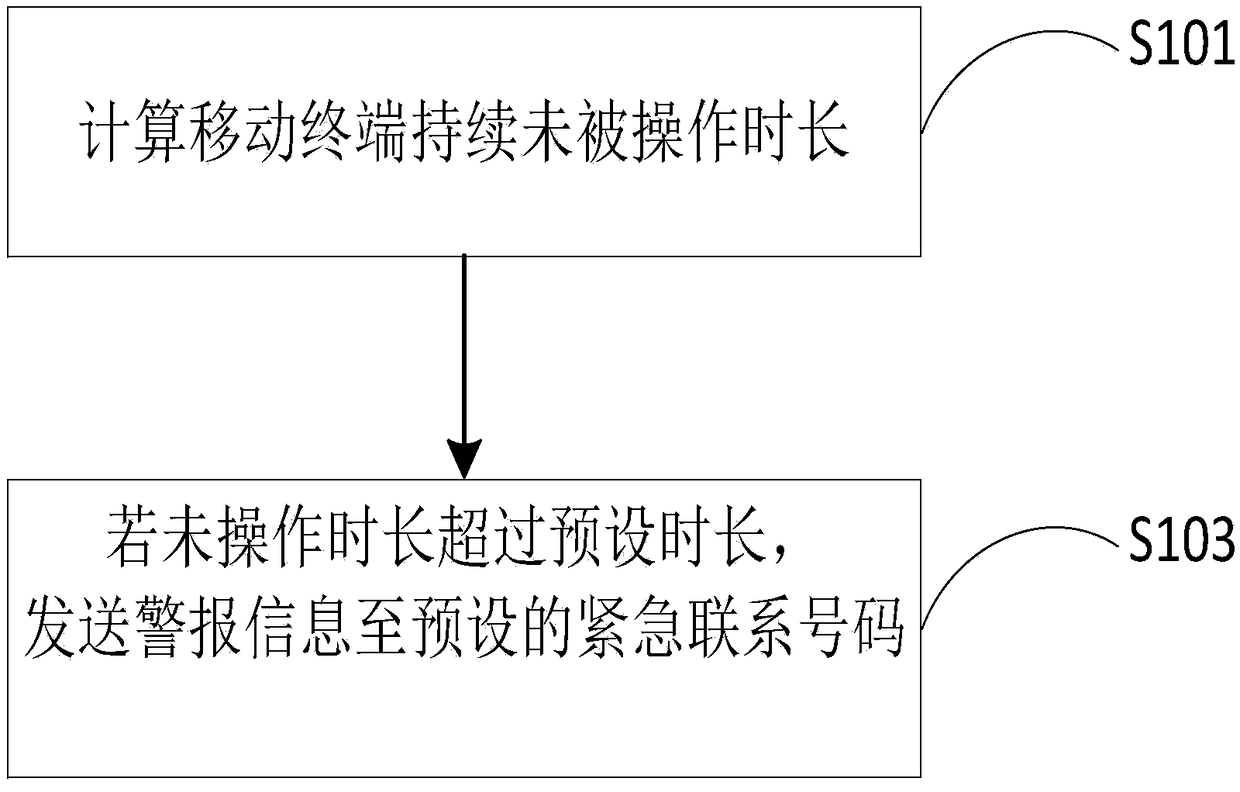
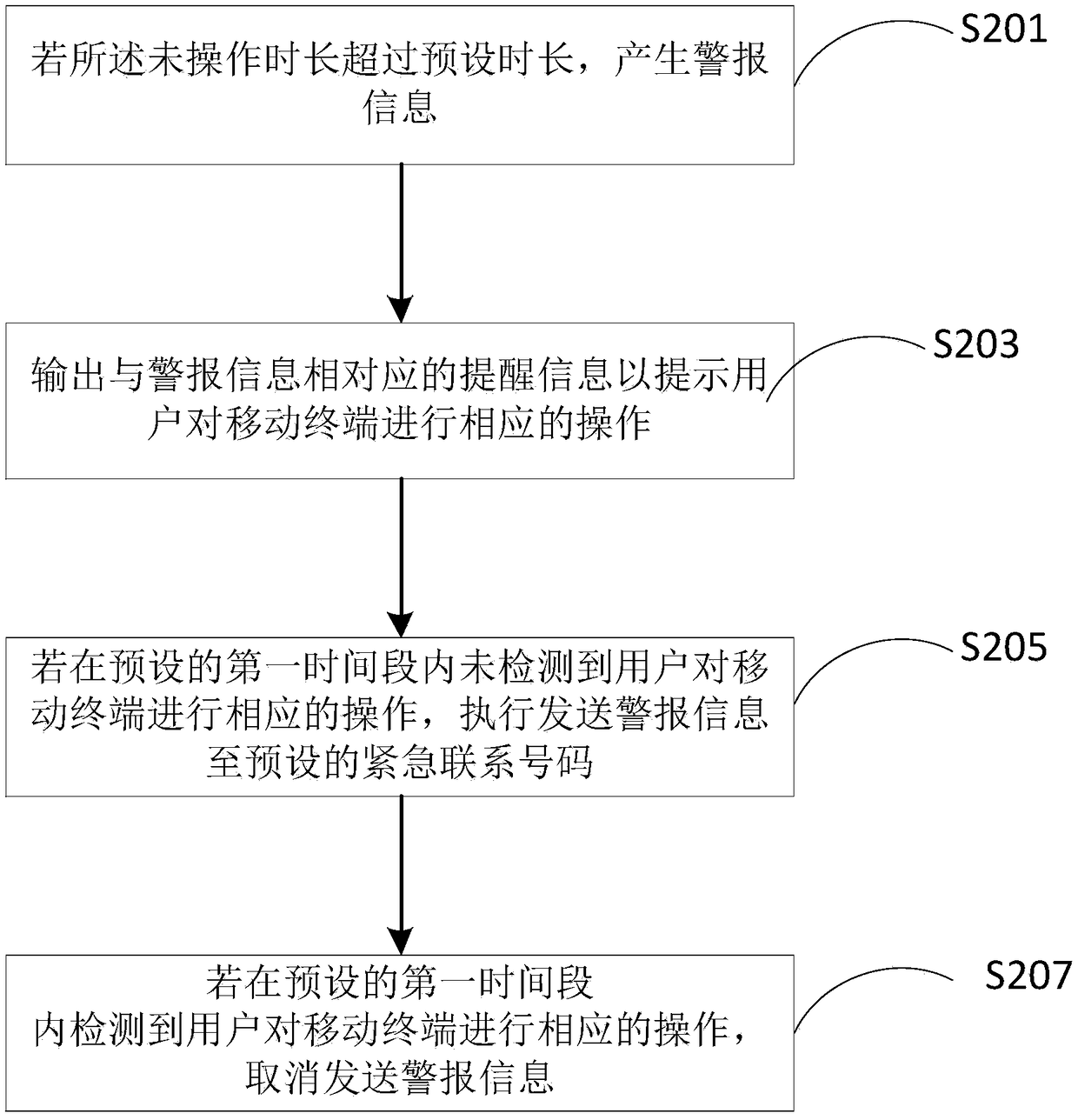
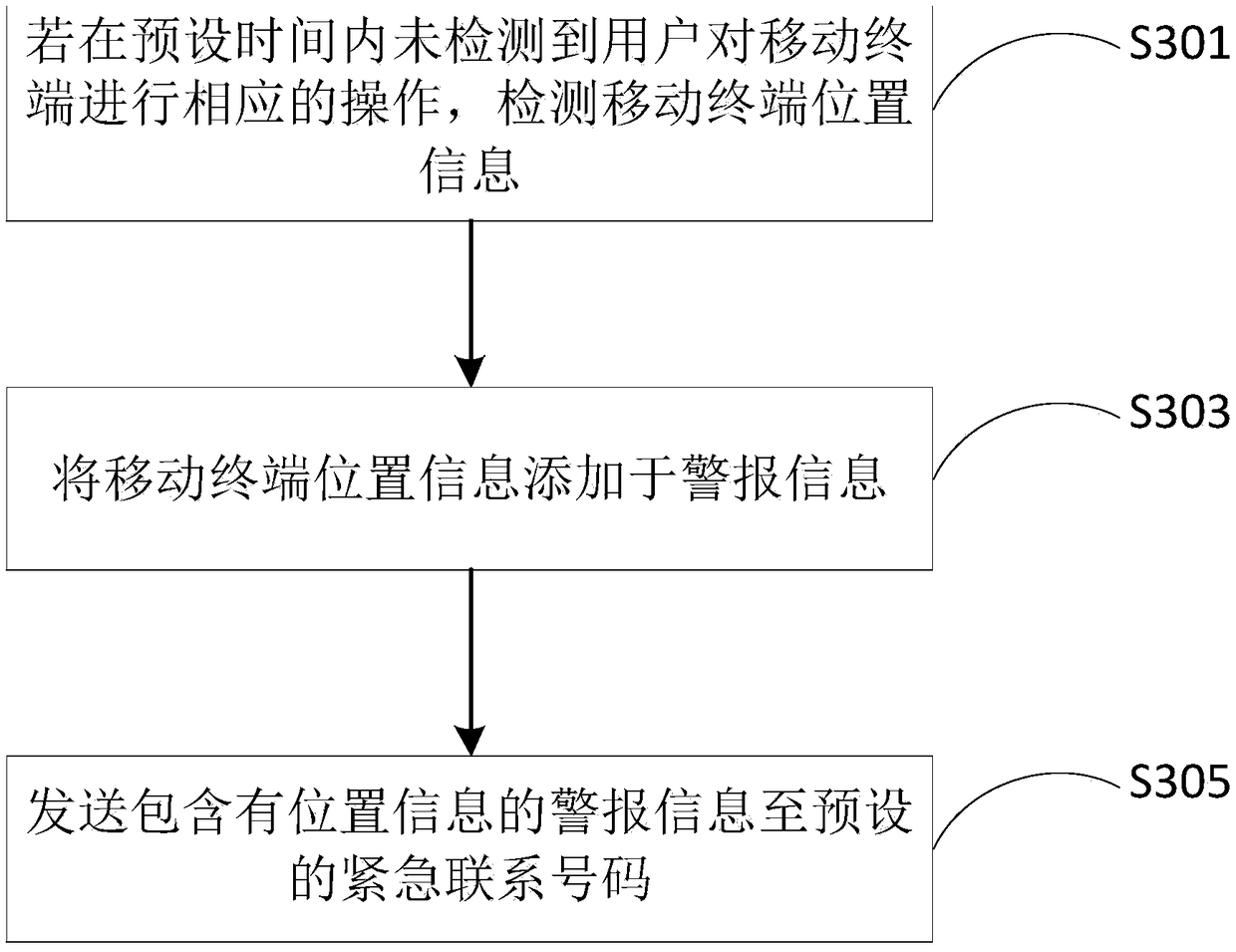
[0041] see figure 1 , a schematic flowchart of a security protection method provided by an embodiment of the present invention, the method includes the following steps.
[0042] Step S101, calculating the duration that the mobile terminal has not been operated; in this embodiment, the mobile terminal may be a smart phone, a smart bracelet, or a watch that can talk. Specifically, th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More