Privacy protection method, terminal and computer readable storage medium
A privacy protection and terminal technology, which is applied in computer security devices, internal/peripheral computer component protection, computing, etc., can solve the problems of not considering the impact of user privacy, adverse effects, and unfavorable user privacy, so as to improve the privacy protection function and The effect of user experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
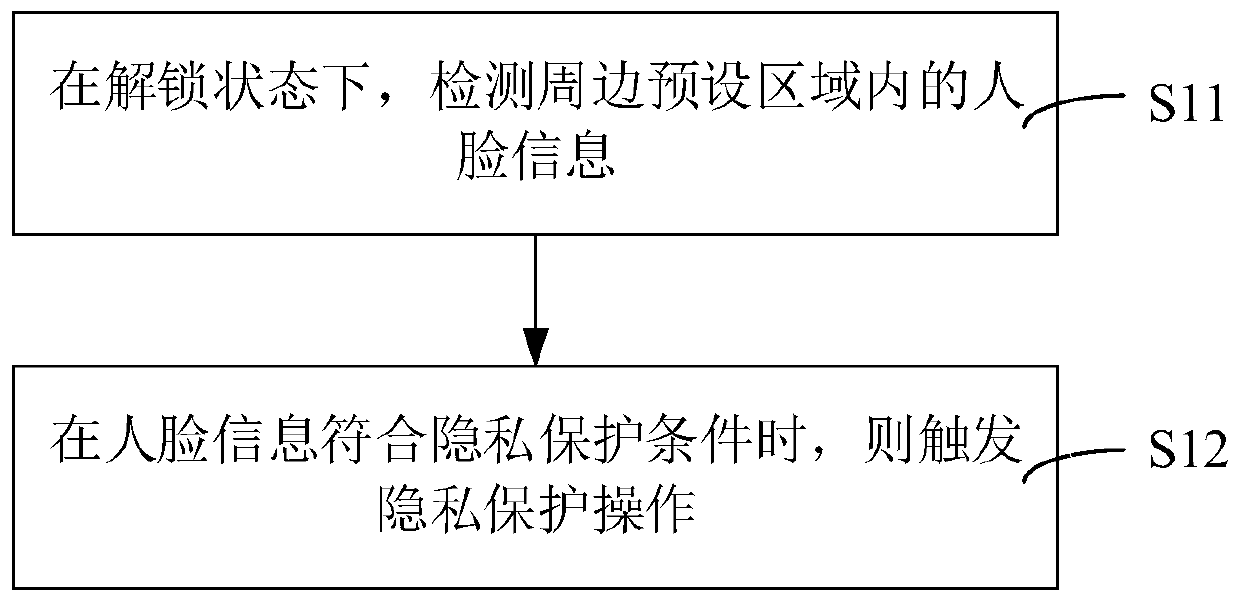
[0028] figure 1 is a schematic flowchart of the privacy protection method provided by the first embodiment of the present invention. In order to clearly describe the privacy protection method provided by the first embodiment of the present invention, please refer to figure 1 .
[0029] The privacy protection method provided by the first embodiment of the present invention is applied to a terminal, and the privacy protection method includes:
[0030] S11: In the unlocked state, detect the face information in the surrounding preset area.
[0031] In one embodiment, the step of detecting the face information in the surrounding preset area may, but is not limited to, include: detecting the face information in the surrounding preset area by biometric identification technology.
[0032] In one embodiment, the biometric identification technology may include, but is not limited to, at least one of face recognition technology (such as infrared face recognition technology) and iris r...
no. 2 example
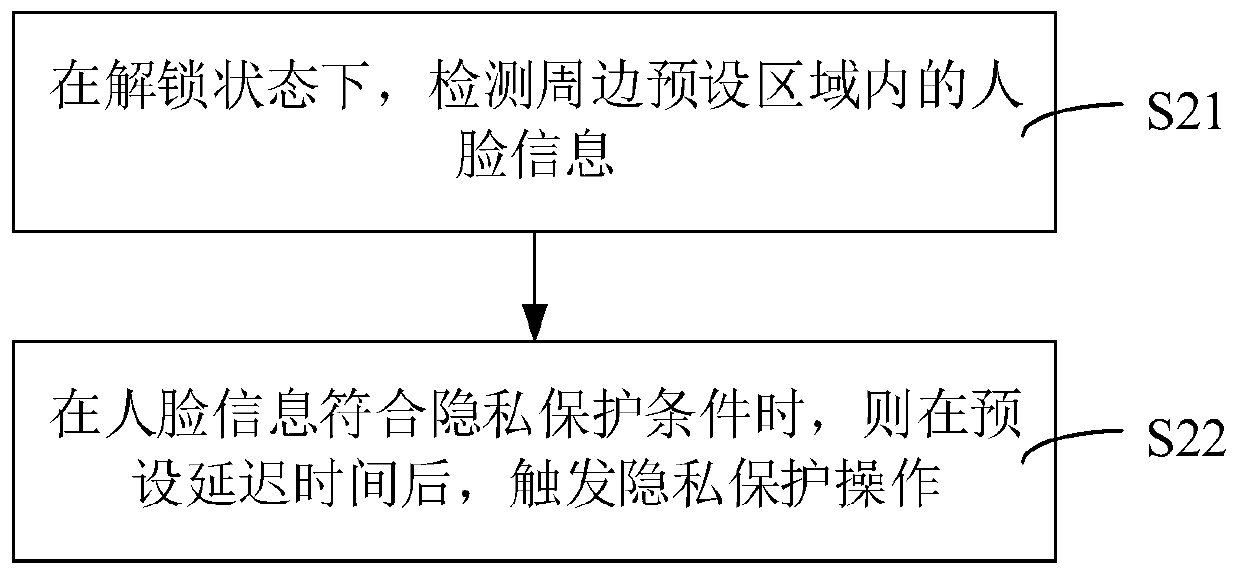
[0054] figure 2 is a schematic flowchart of the privacy protection method provided by the second embodiment of the present invention. In order to clearly describe the privacy protection method provided by the second embodiment of the present invention, please refer to figure 2 .
[0055] The privacy protection method provided by the second embodiment of the present invention is applied to a terminal, and the privacy protection method includes:
[0056] S21: In the unlocked state, detect the face information in the surrounding preset area.
[0057] In one embodiment, in step S21: in the unlocked state, before detecting the face information in the surrounding preset area, it may include but not limited to: receiving a delay setting instruction to obtain a preset delay time according to the delay setting instruction . For example, according to the operation information of the user on the delay setting interface or the delay setting control, the delay setting instruction is ...
no. 3 example
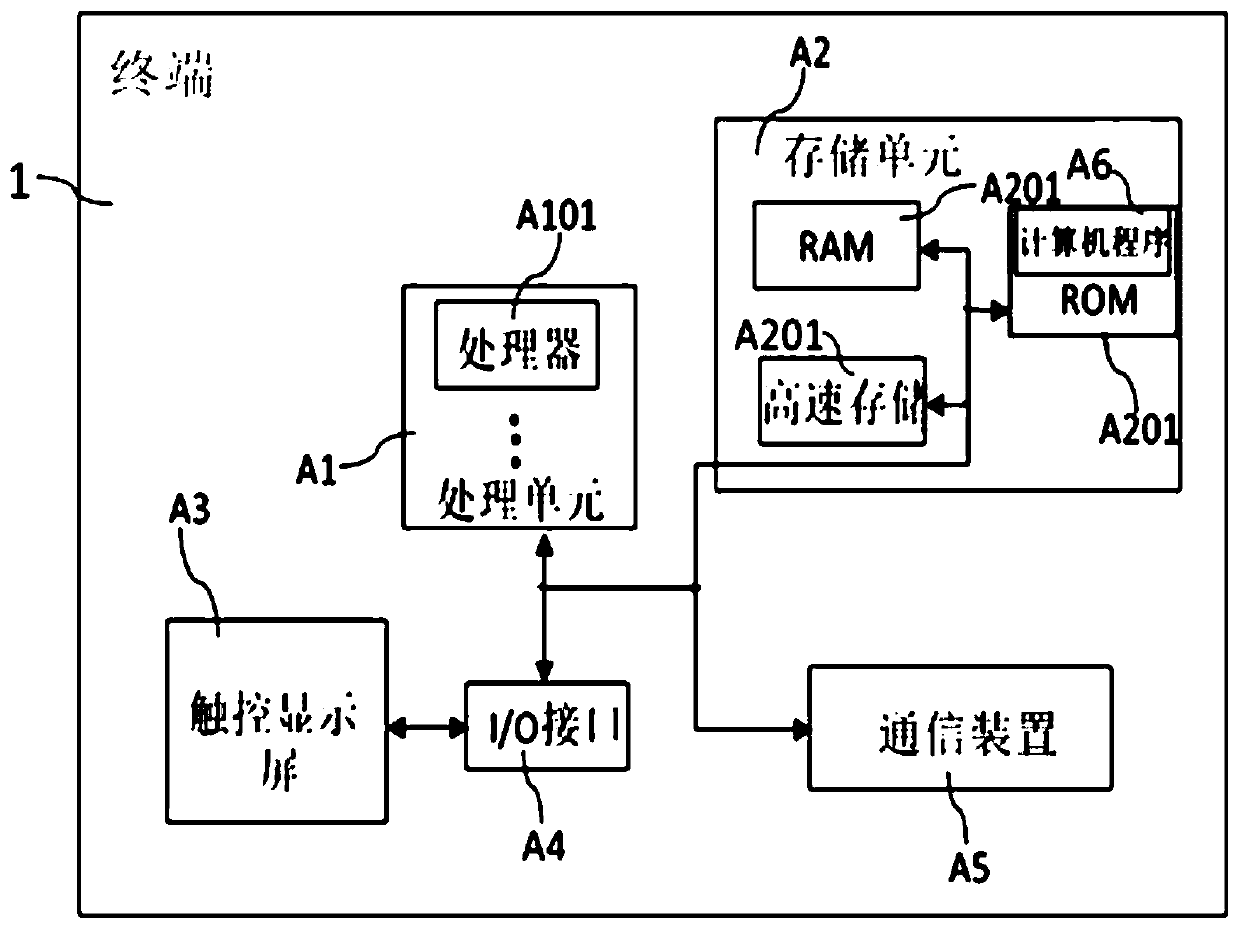
[0066] image 3 is a schematic structural diagram of a terminal provided by the third embodiment of the present invention. In order to clearly describe the terminal 1 provided by the third embodiment of the present invention, please refer to image 3 .
[0067] The terminal 1 provided by the third embodiment of the present invention includes: a processor A101 and a memory A201, wherein the processor A101 is used to execute the computer program A6 stored in the memory A201 to realize the The steps of the privacy protection method.
[0068] In an implementation manner, the terminal 1 provided in this embodiment may include at least one processor A101 and at least one memory A201. Wherein, at least one processor A101 may be called a processing unit A1, and at least one memory A201 may be called a storage unit A2. Specifically, the storage unit A2 stores a computer program A6, and when the computer program A6 is executed by the processing unit A1, the terminal 1 provided in th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More