Method, device and equipment for detecting malicious click refreshing operation, and storage medium
A malicious, information-manipulating technology, applied in the Internet field, can solve the problem of not being able to detect the account as a robot, and achieve the effect of improving the recognition ability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
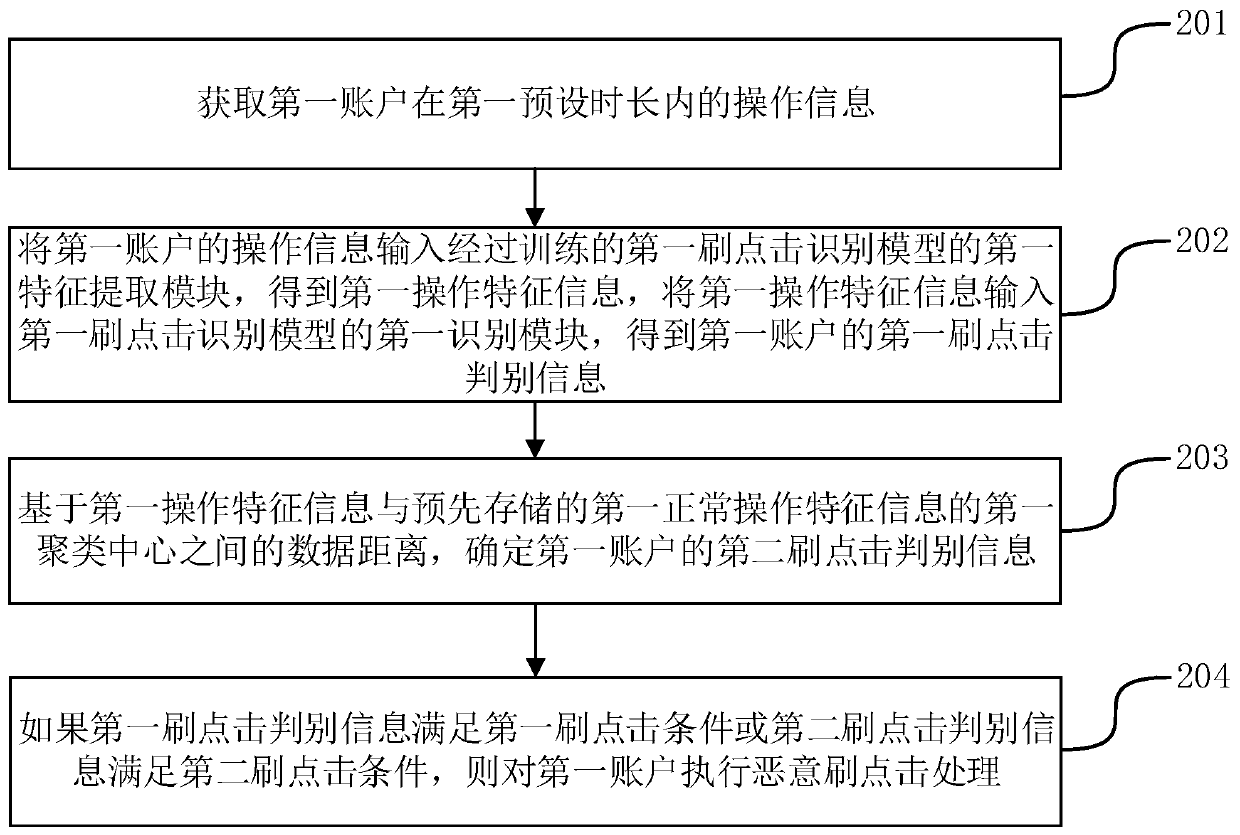
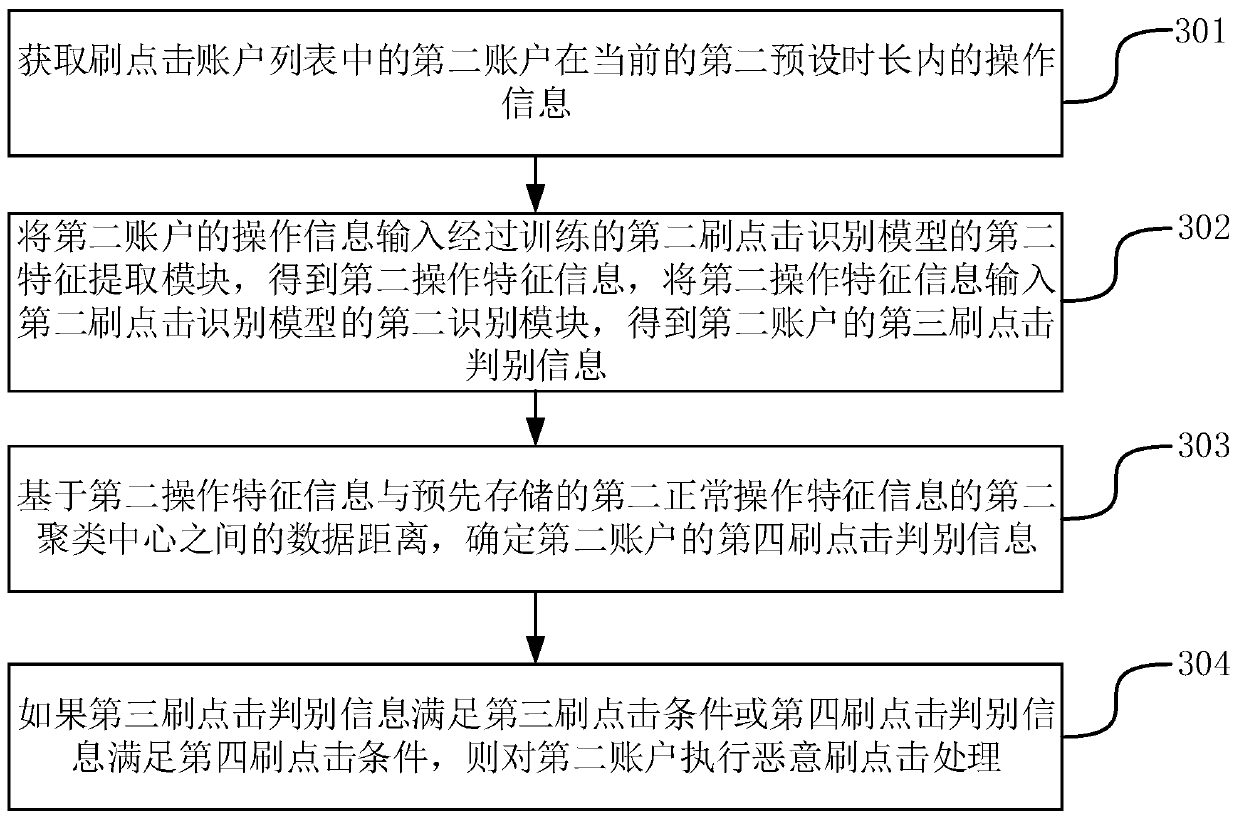
[0028] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
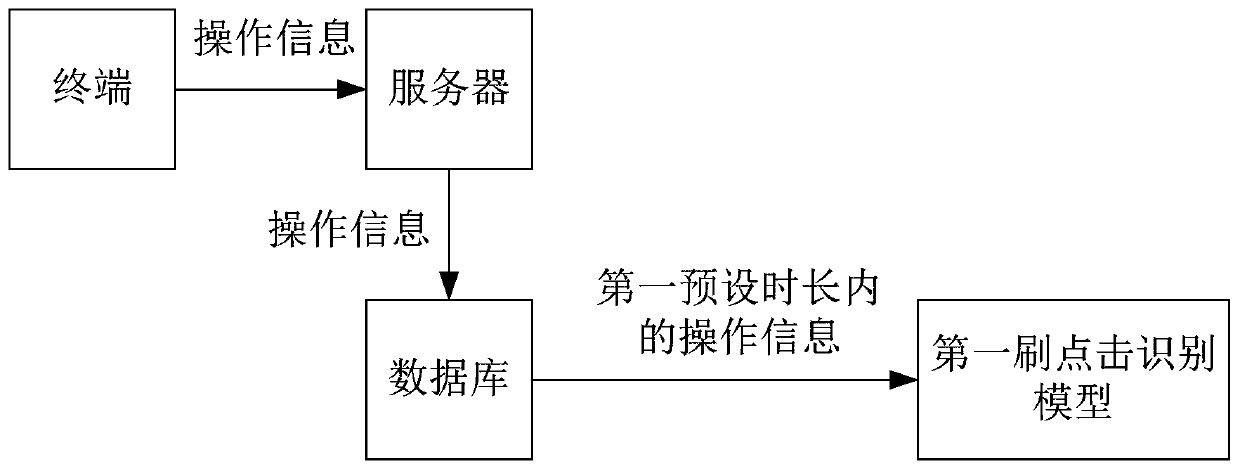
[0029] figure 1 It is a schematic diagram of an implementation environment provided by the embodiment of this application, see figure 1 . The method for detecting malicious swiping and clicking operations provided by the present application can be implemented by a terminal and a server, wherein the terminal runs a target application program and can access the Internet, and the server can establish communication with the terminal.
[0030] The target application program running in the terminal may be a live broadcast application program, a short video application program, a social application program, etc., which can enable users to interact and browse information through the Internet. Functions such as likes, comments, and down...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More