Safe multi-party calculation control method for realizing approximate maximum value calculation based on computer software and corresponding system
A technology for secure multi-party computing and software implementation, which is applied in the field of secure multi-party computing control methods and corresponding systems, and can solve problems such as protocols without polynomial communication complexity.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] In order to describe the technical content of the present invention more clearly, further description will be given below in conjunction with specific embodiments.
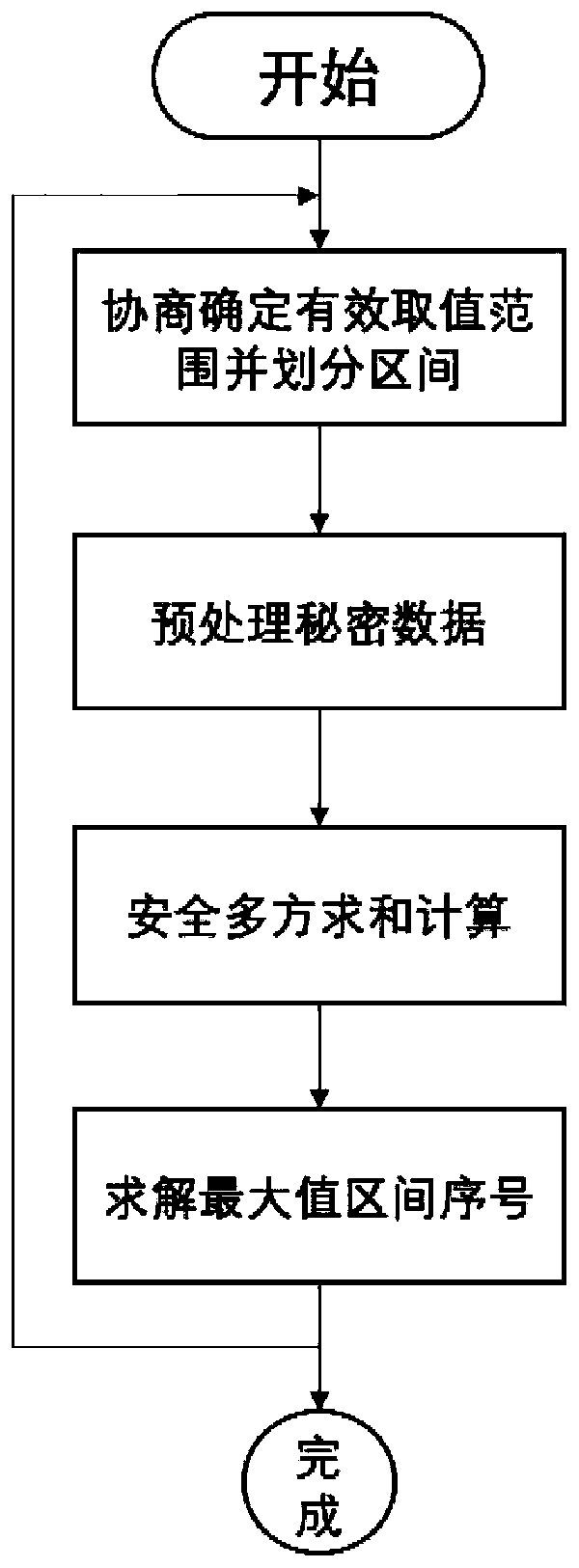
[0043] The secure multi-party computing control method based on computer software of the present invention to realize approximate maximum calculation includes the following steps:
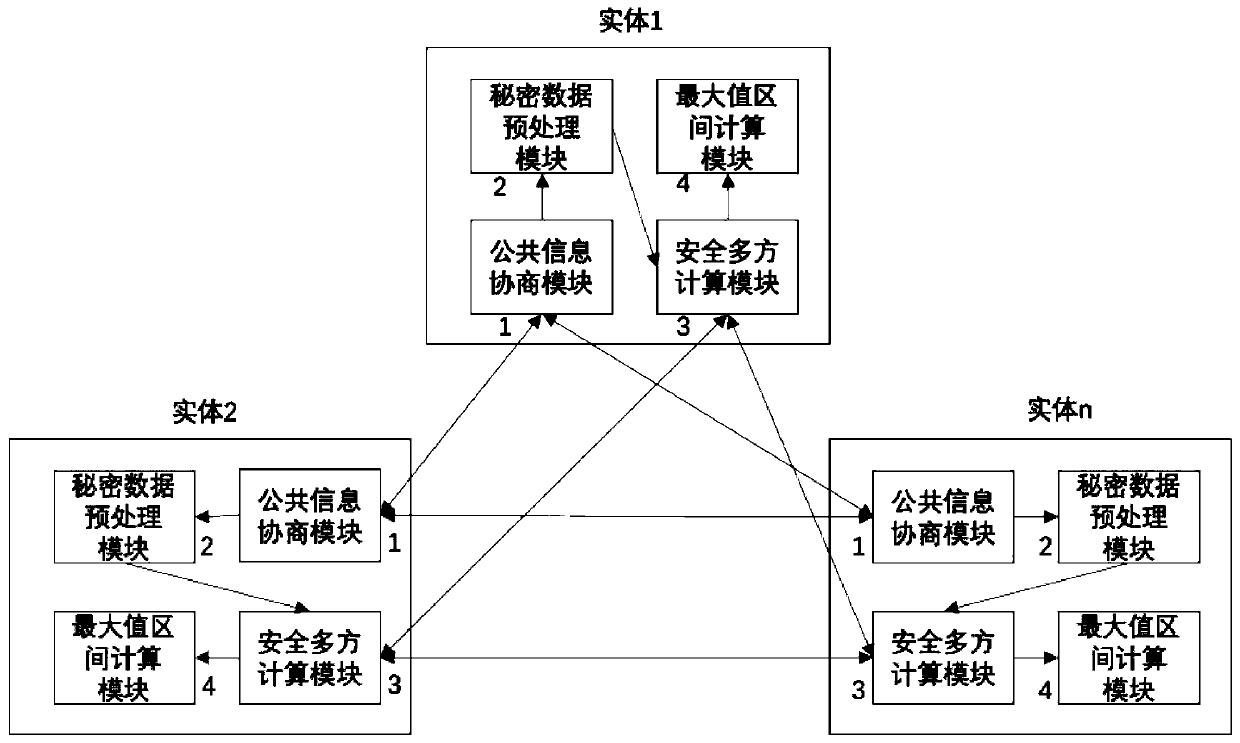
[0044] (1) The public information negotiation module negotiates to determine the effective value range and divides the interval;
[0045] (1.1) The public information negotiation module negotiates to determine the effective value range;
[0046] (1.2) The public information negotiation module takes different integers, and divides the effective value range into value intervals;
[0047] (2) The secret data preprocessing module determines the serial number of the value interval where the secret information is located, and calculates it;
[0048] (2.1) The secret data preprocessing module determines the serial number of the value...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More