Automatic penetration testing method based on AI
A penetration testing and automatic technology, applied in neural learning methods, biological neural network models, platform integrity maintenance, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
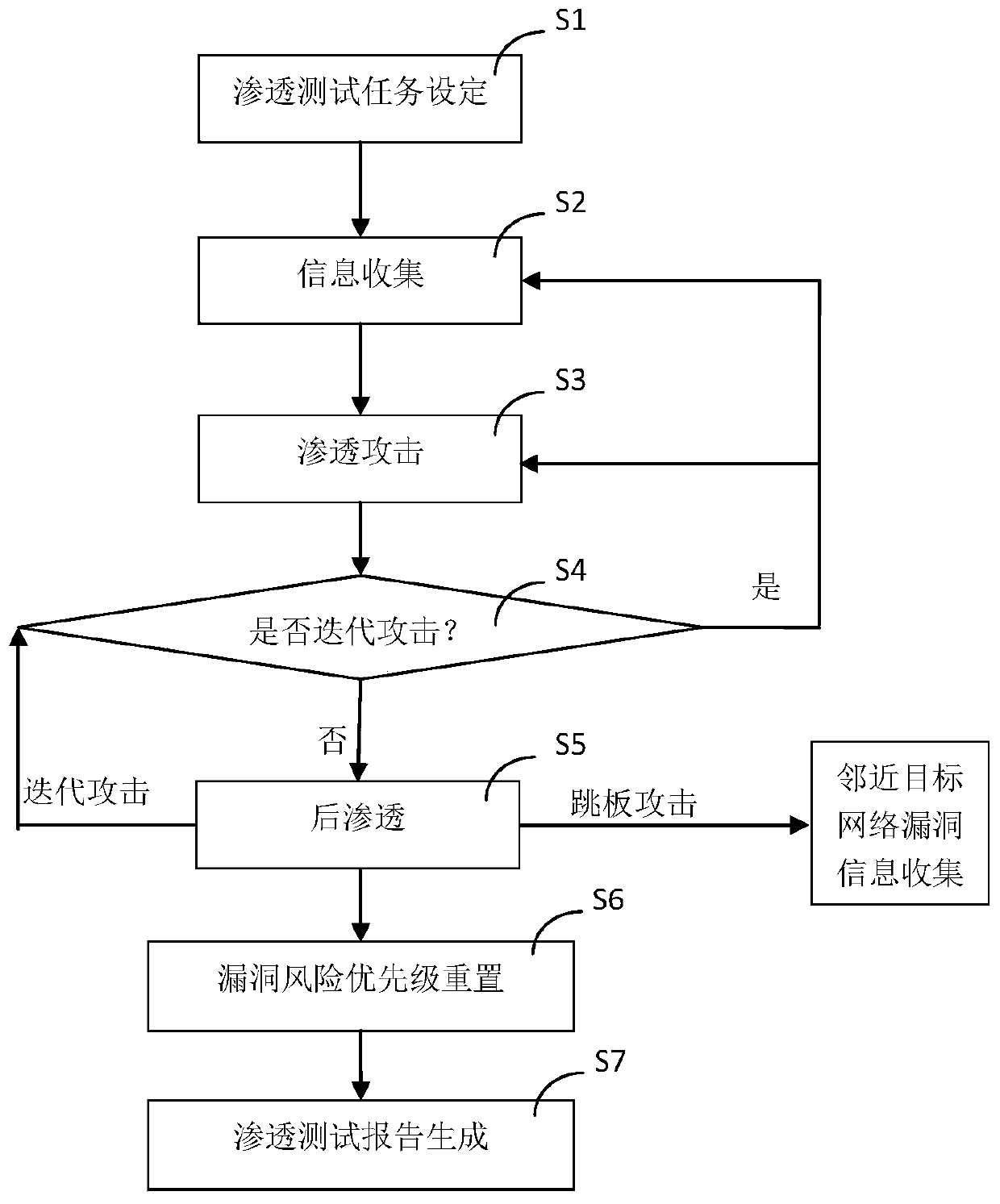
[0103] Such as figure 1 As shown, the present embodiment includes the following steps during use:
[0104] S1. Penetration test task setting: including setting the penetration target, parameters, whether to automatically springboard the attack, and start the task;
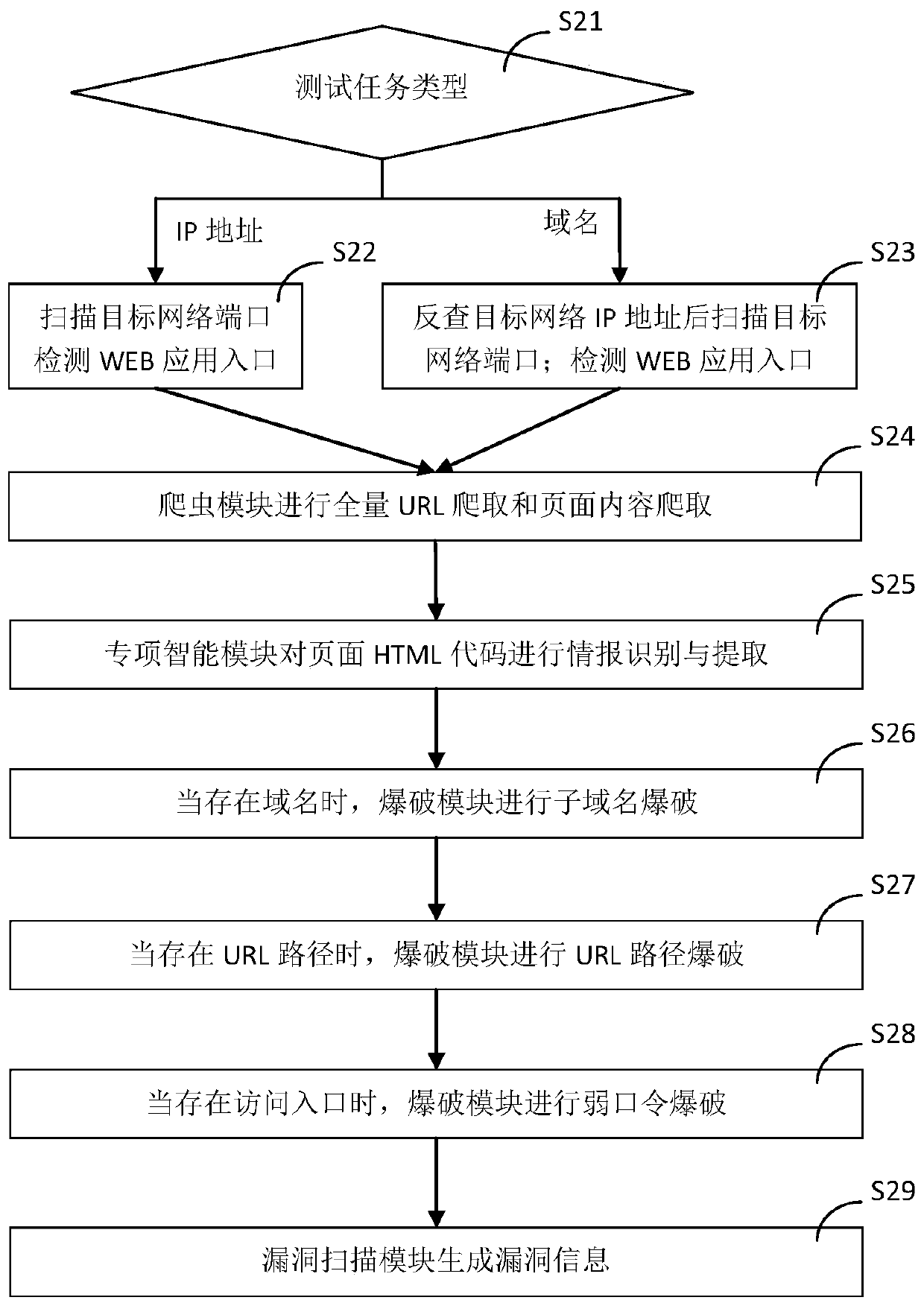
[0105] S2. Collection of attack surface, intelligence information, and vulnerability information: the decision-making brain module 420 generates a driving instruction according to the target IP or domain name set by the penetration testing task and sends it to the information collection module 100, and the information collection module 100 collects the attack surface and intelligence according to the driving instruction information, vulnerability information and transmit the attack surface, intelligence information, and vulnerability information to the decision-making brain module 420; figure 2 As shown, step S2 further includes the following steps:
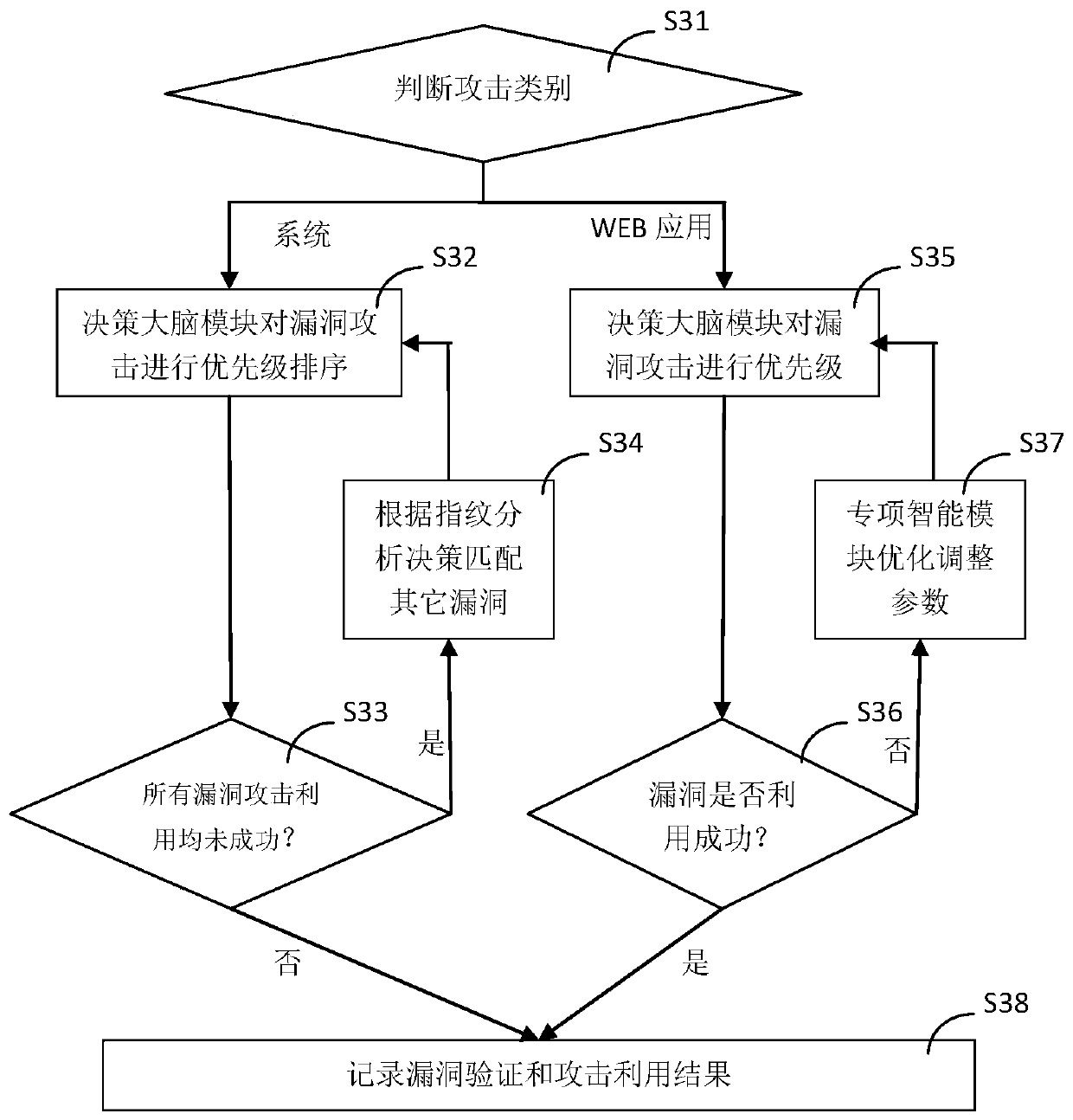
[0106] S21. The decision-making brain module 420 judges the t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More