Penetration attack method of AI-based automatic penetration test system
A penetration testing and vulnerability technology, applied in the field of network data security, to achieve the effect of stable service level, reduced risk exposure window, and fewer blind spots of knowledge
Active Publication Date: 2020-07-31
北京墨云科技有限公司
View PDF3 Cites 4 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
[0006] The present invention aims to solve the above-mentioned technical problems existing in penetration testing in the prior art when manual services and automated tools are used, and provides an automated penetration testing system based on AI, which can effectively improve the stability and efficiency of penetration testing
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
Embodiment 1
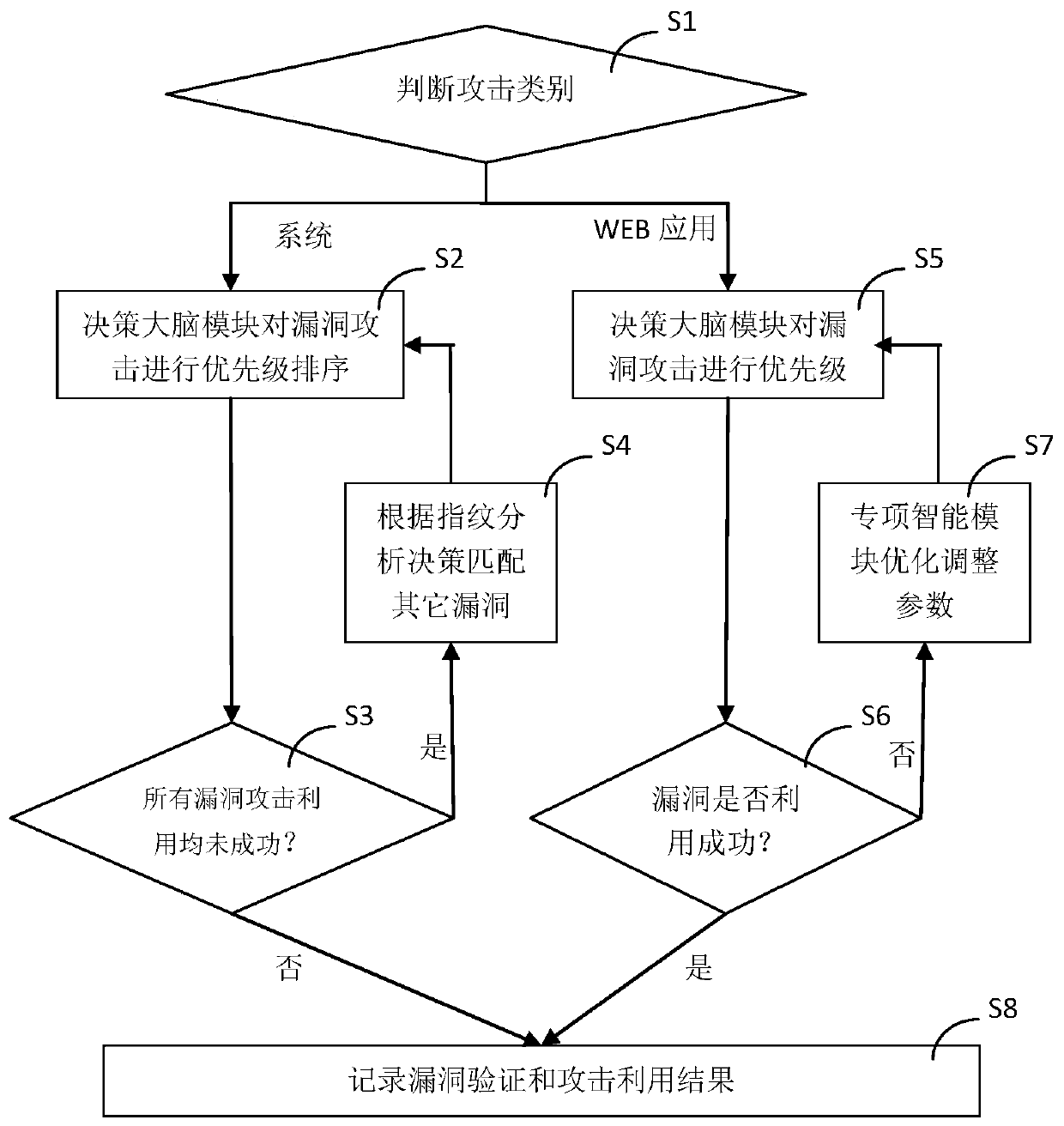
[0071] Such as figure 1 As shown, the present embodiment includes the following steps during use:
[0072] S1, determine the type of attack, enter step S2 when performing a penetration attack on the system, and enter step S5 when performing a penetration attack on a WEB application;
[0073] S2. The decision-making brain module 420 establishes attack branch nodes according to the attack surface, intelligence data, and vulnerability information, and prioritizes them according to the success rate of exploiting the vulnerabilities;
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
The invention discloses a penetration attack method of an AI-based automatic penetration system. The penetration attack method comprises the following steps of: S1, judging an attack category; S2, performing priority ranking by using vulnerability utilization success rates; S3, detecting vulnerabilities one by one; S4, matching other vulnerabilities by a special intelligent module; S5, performingpriority ranking by using vulnerability utilization success rates; S6, detecting the vulnerabilities one by one; S7, optimizing and adjusting parameters by the special intelligent module; and S8, generating a vulnerability verification result and a vulnerability utilization result by a penetration attack module. The penetration attack method of the AI-based automatic penetration test system provided by the invention can effectively improve the stability and efficiency of the penetration test.
Description
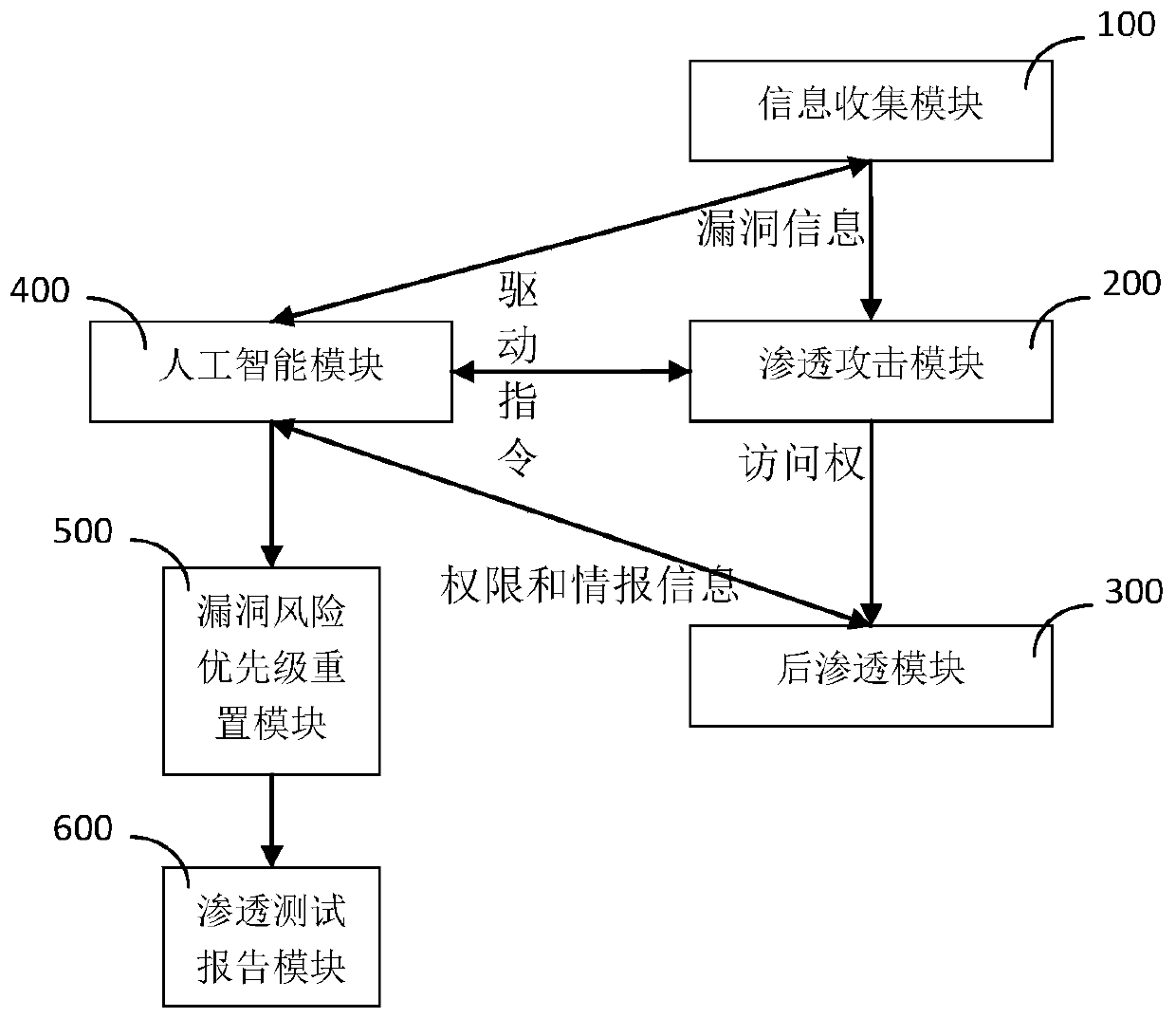
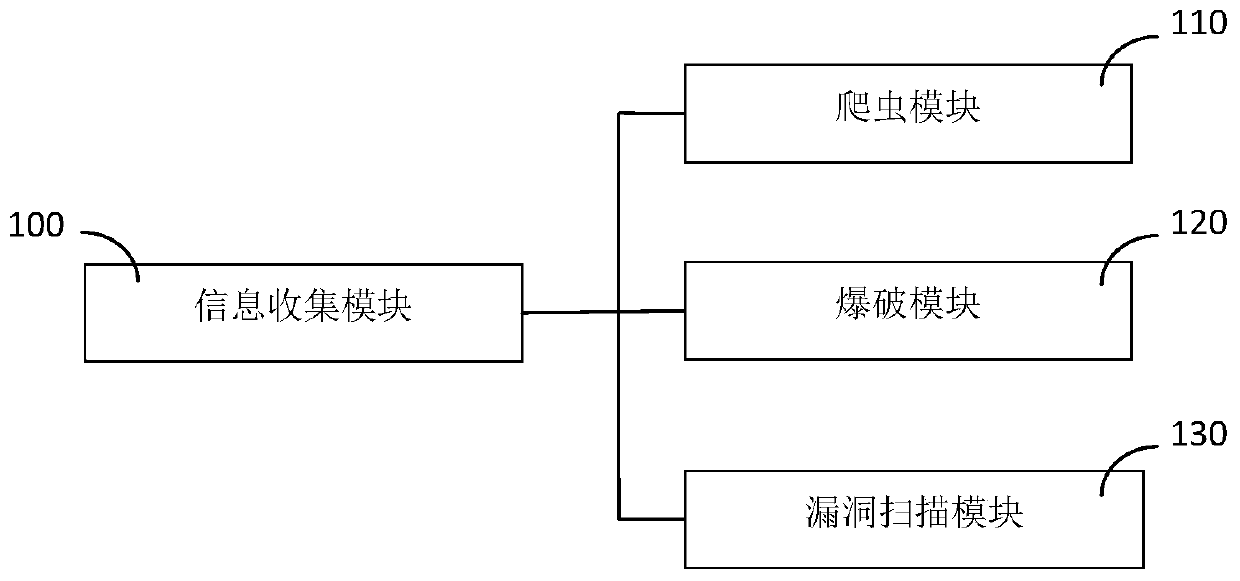
technical field [0001] The invention relates to the technical field of network data security, in particular to a penetration attack method of an AI-based automated penetration testing system. Background technique [0002] Penetration test is to completely simulate the attack technology and vulnerability discovery technology that hackers may use, conduct in-depth detection of the security of the target system, discover the most vulnerable link of the system, discover complex, interrelated security problems, and deeper weaknesses , and report the intrusion process and details to the user. The penetration testing workflow is mainly divided into three stages: pre-attack stage, attack stage, and post-attack stage. Pre-attack stage: The purpose is to collect information. Generally, information is obtained by detecting and analyzing targets through tools such as basic network information acquisition and regular vulnerability scanning. Attack phase: The purpose is to attack the t...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More Patent Type & Authority Applications(China)
IPC IPC(8): G06F21/57G06N7/02
CPCG06F21/577G06N7/02
Inventor 刘兵何召阳方仁贵何晓刚郗朝旭朱伟光
Owner 北京墨云科技有限公司