Permission control method and device, storage medium and electronic equipment
A technology of permission control and permission configuration, applied in the computer field, which can solve the problems of low storage and usage efficiency, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
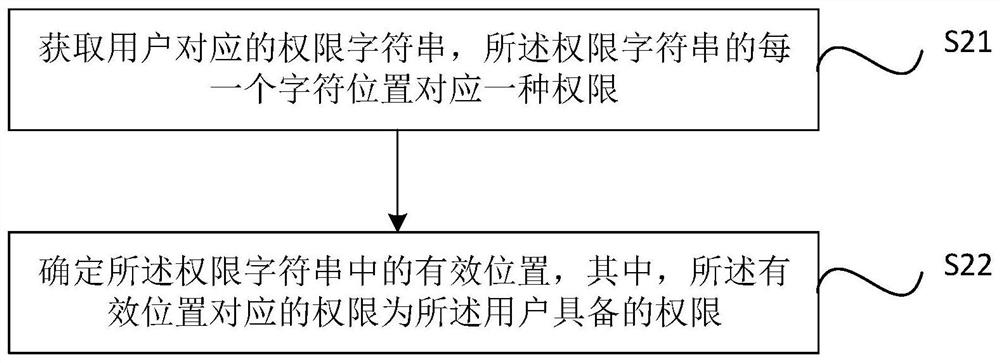
[0032] Specific embodiments of the present disclosure will be described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to illustrate and explain the present disclosure, and are not intended to limit the present disclosure.
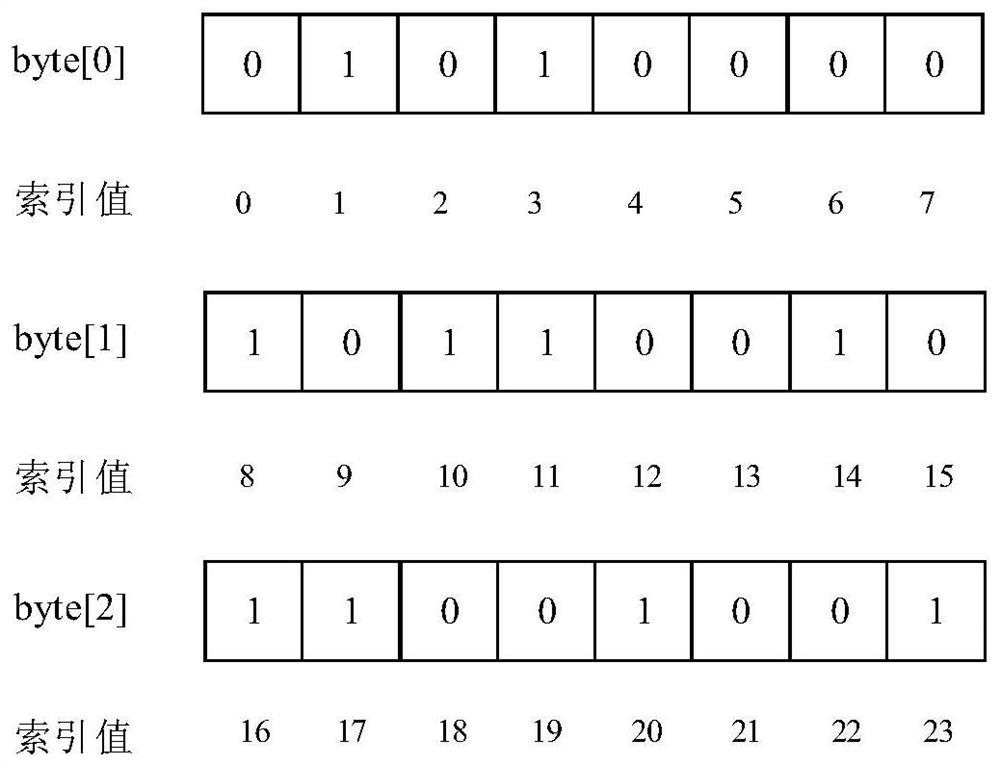
[0033] This disclosure relates to binary digital algorithms. According to the commonly used data representation mode in the computer field, in this disclosure, if there is no special explanation, "valid character" can be understood as the character "1", and "invalid character" can be understood as the character "0". However, this way of understanding should not limit the present disclosure. Those skilled in the art should know that when implementing the solution of the present disclosure, the "valid character" can also be "0", and correspondingly, the "invalid character" can also be "1".
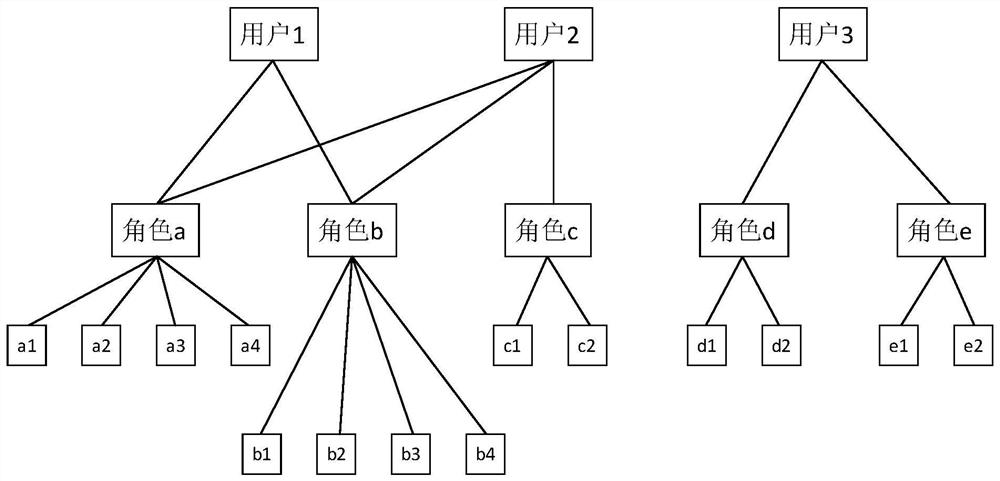
[0034] The permission control method adopted by the traditional Saas ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More