Sensitive data analysis method, device, equipment and storage medium
A sensitive data and analysis method technology, applied in the Internet field, can solve problems such as simple and impractical sensitive data analysis methods, prone to abnormalities, and unable to meet users' sensitive data analysis needs, and achieve the effect of improving analysis and query performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application.
[0027] It should be understood that some embodiments described here are only used to explain the technical solutions of the present application, and are not intended to limit the technical scope of the present application.
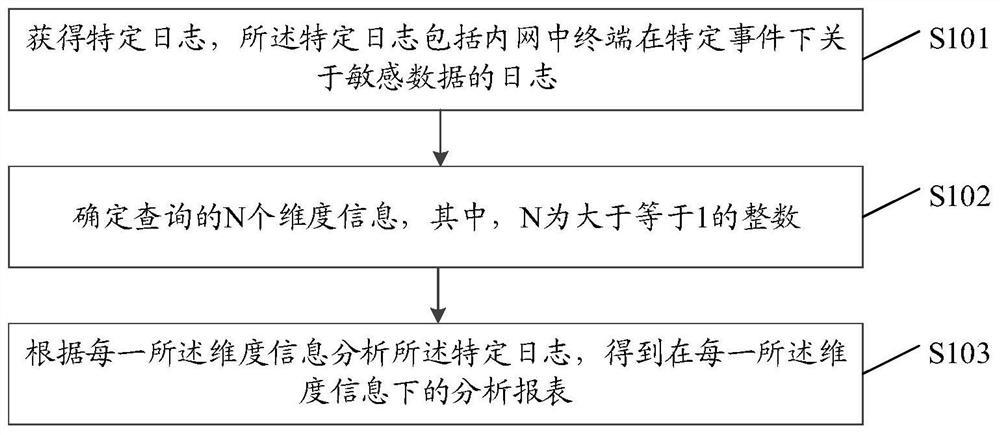
[0028] A schematic diagram of the implementation flow of a sensitive data analysis method provided in the embodiment of this application, which is applied to the analysis end, such as Figure 1A As shown, the method includes:
[0029] Step S101, obtain a specific log, the specific log includes the log of the sensitive data of the terminal in the intranet under a specific event;
[0030] Network devices, systems and service programs, etc., will generate an event record called a log (log) during operation; each line of log records the description of relate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More