Bayesian Game-Based Privacy Protection Method for Internet of Things Nodes under Fog Computing Architecture
A privacy protection and Internet of Things technology, which is applied in the field of privacy protection of Internet of Things nodes based on Bayesian game, can solve the problems of limited computing power of Internet of Things nodes, no consideration of malicious nodes and normal nodes of Internet of Things nodes, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
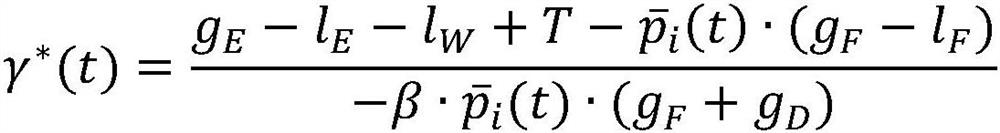
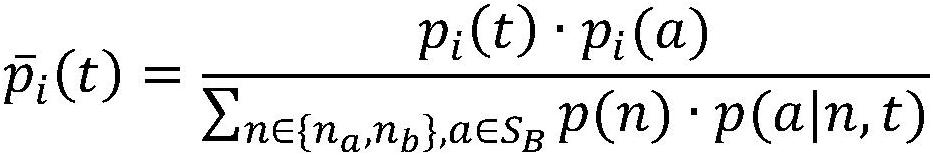
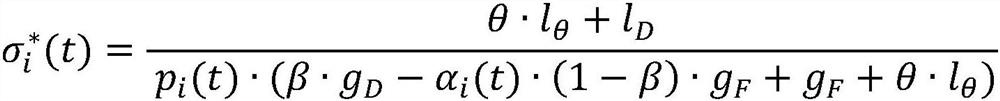
Method used
Image
Examples
Embodiment Construction
[0057] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
[0058] The Bayesian game-based privacy protection method for Internet of Things nodes under the fog computing architecture provided by the present invention is applied in an environment including Internet of Things nodes and fog computing nodes, wherein the Internet of Things nodes include a series of sensing nodes to achieve real-time online Monitoring, positioning traceability, remote control and other management or ap...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More