Dumb terminal security detection method and device, equipment and readable storage medium
A security detection, dumb terminal technology, applied in the computer field, can solve the problem that the access behavior is easy to be ignored and so on
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] Next, the technical scheme in the present application embodiment will be described in the present application embodiment, and it is understood that the described embodiments are merely the embodiments of the present application, not all of the embodiments. Based on the embodiments in the present application, one of ordinary skill in the art is in the scope of the present application without making creative labor premistence.
[0044] At present, the dumb end is the end device in the network, and its access behavior is easily ignored. To this end, the present application provides a dumb-end safety testing scheme that can be safely detected for the accessed behavior for the dumb terminal.
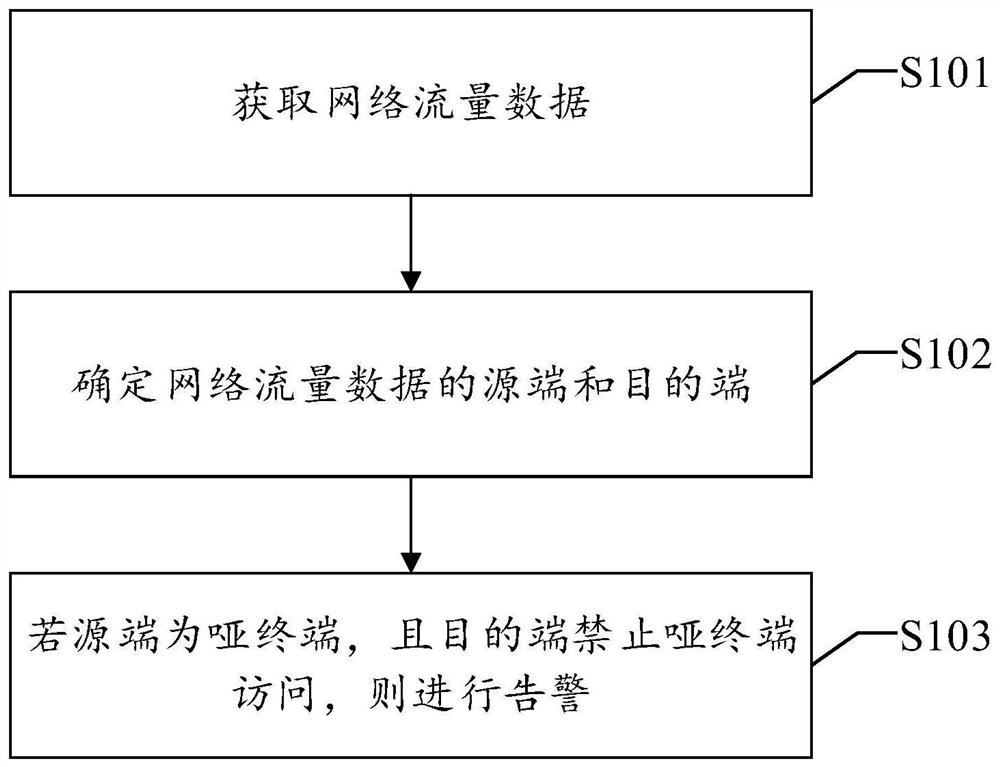
[0045] See figure 1 As shown, the present application discloses a dumb-end safety detection method, including:
[0046] S101, get network traffic data.
[0047] In an embodiment, the network traffic data is the traffic data flowing through the dumb terminal in the network, and the specific...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More