Threat intelligence classification and evolution relationship analysis method
A technology of relational analysis and evolutionary relational diagram, applied in semantic analysis, text database clustering/classification, unstructured text data retrieval, etc., can solve problems such as low information quality, short shelf life, lack of in-depth analysis, etc., to achieve Solve the effects of low quality, information overload, and rich information
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0084] The following is a preferred embodiment of the present invention and the technical solutions of the present invention are further described in conjunction with the accompanying drawings, but the present invention is not limited to this embodiment.
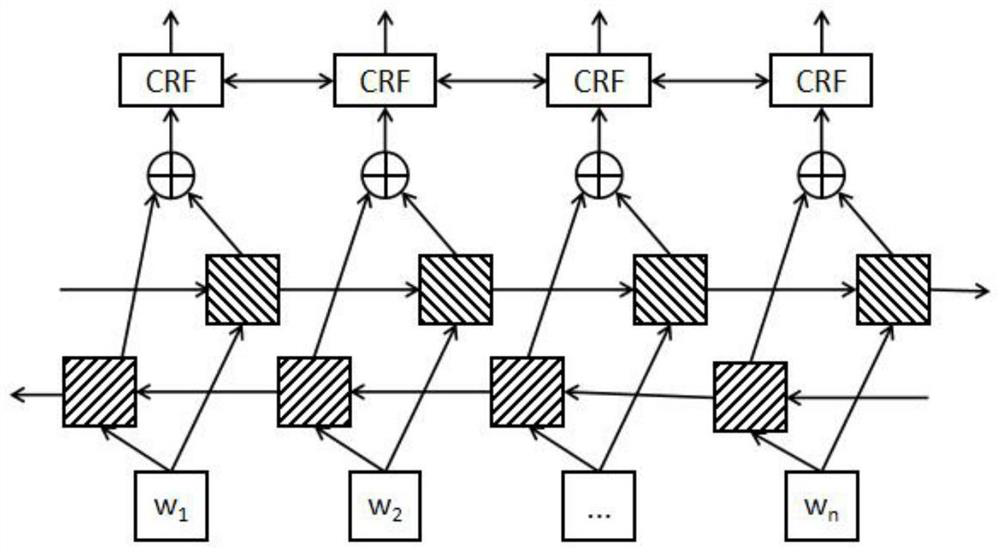
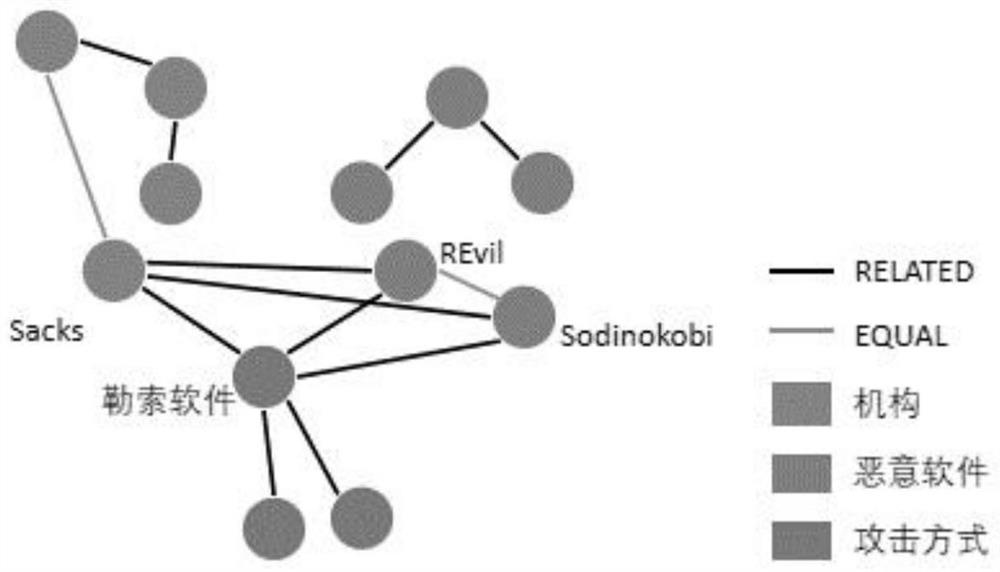
[0085] The invention proposes a method for categorizing threat intelligence and analyzing evolutionary relationships. This technology mainly includes two aspects, the first aspect is the classification technology of threat intelligence, and the second aspect is the evolution analysis method of threat intelligence. The classification method of threat intelligence mainly classifies the threat types of threat intelligence, and the evolution analysis of threat intelligence mainly analyzes the time series evolution relationship between threat intelligence.
[0086] Threat Intelligence Classification Techniques:
[0087] Compared with general corpus information, there are many information security elements in threat intelligence, s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More