Communicating with a machine to machine device
a technology of machine to machine device and communication channel, which is applied in the field of communication channel with machine to machine device, can solve the problems of increasing data overhead, generating additional data overhead, and many machine to machine devices, and achieves the effect of reducing the data overhead of the m2m device and/or a bootstrapping server, reducing or eliminating unnecessary data transfers
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
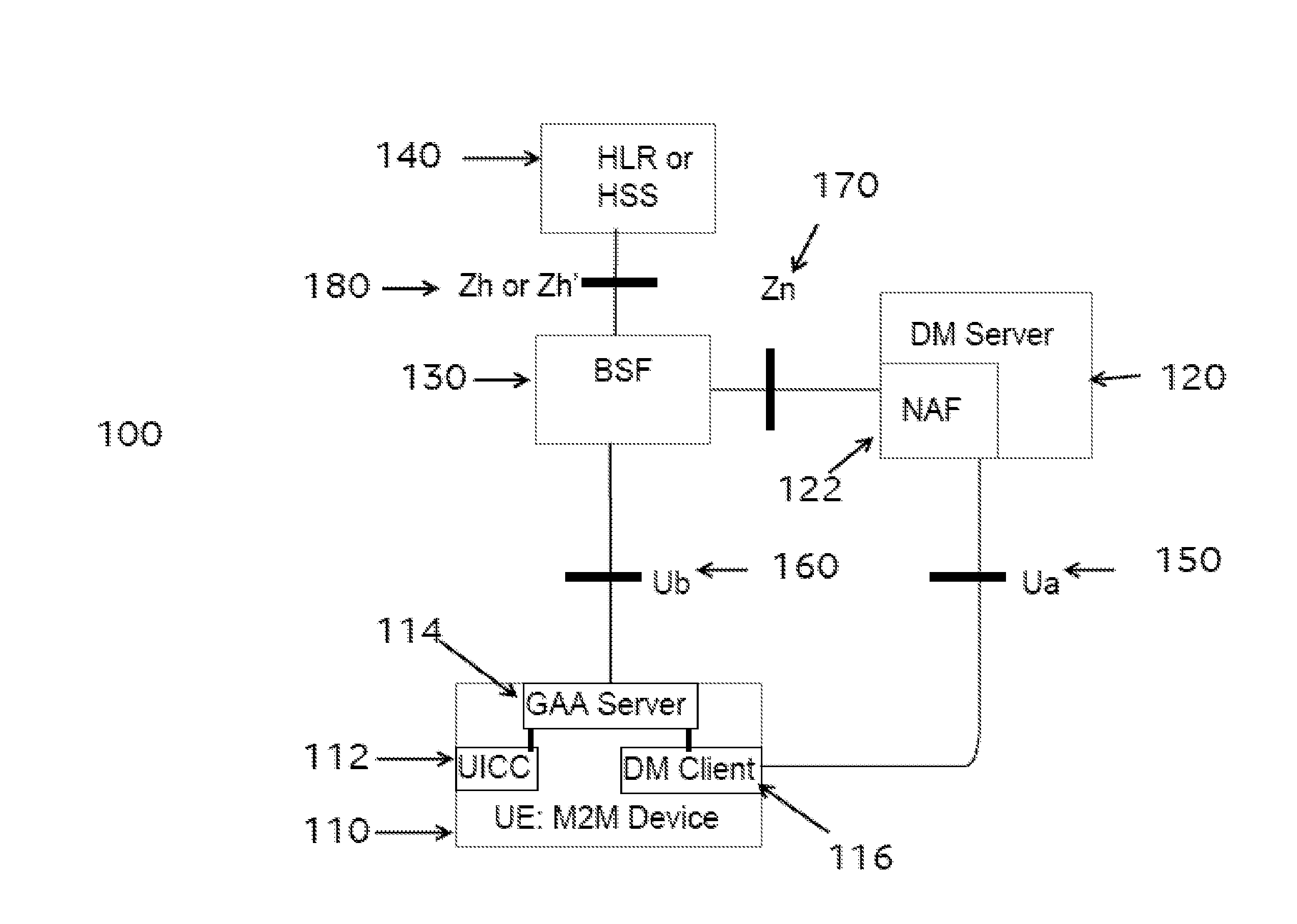
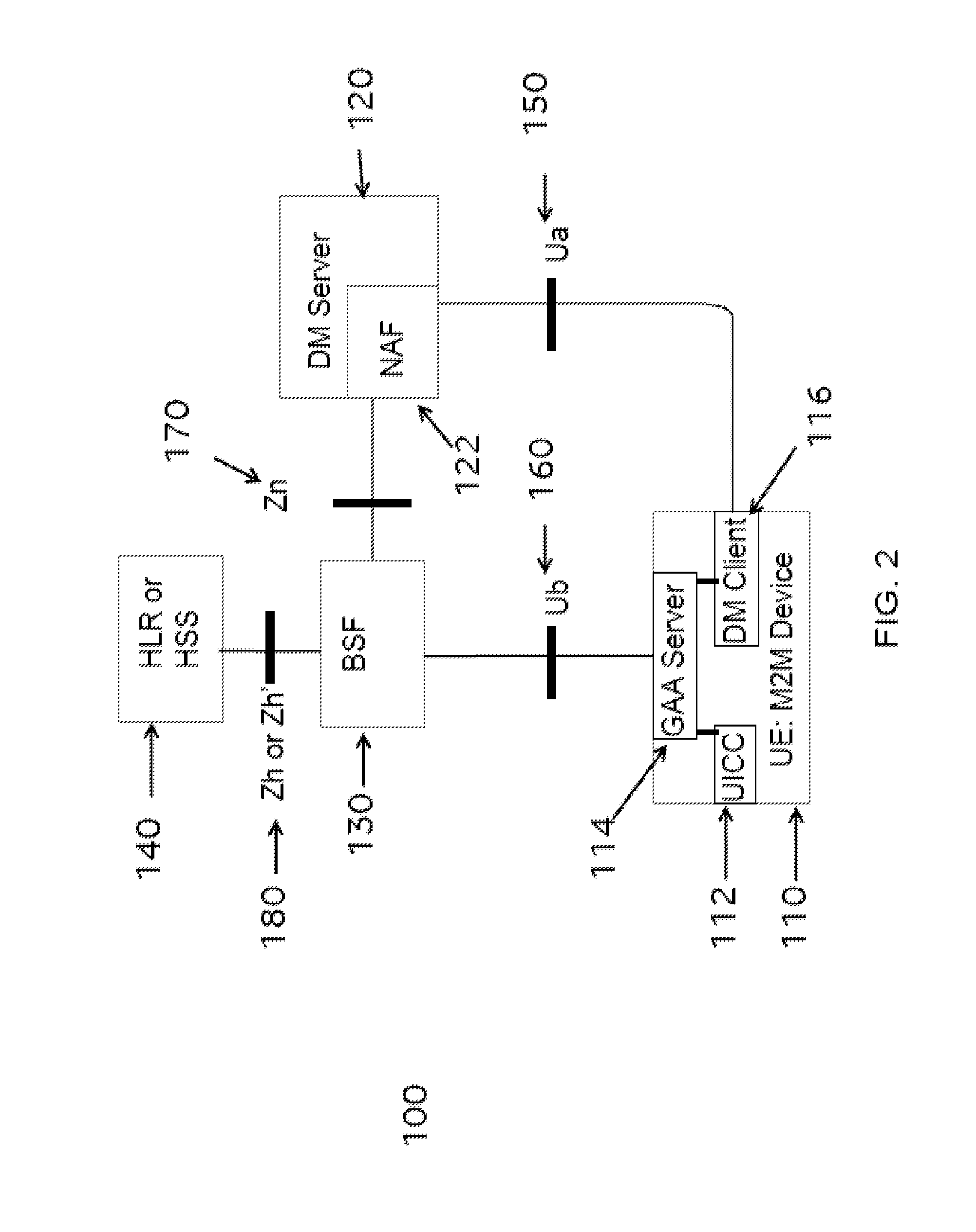
[0111]A device may communicate securely with a server. The device may be a Machine to Machine (M2M) device, or an equivalent device (e.g. a device, a generic or specific communication device, including one or more modules capable of providing M2M capabilities).
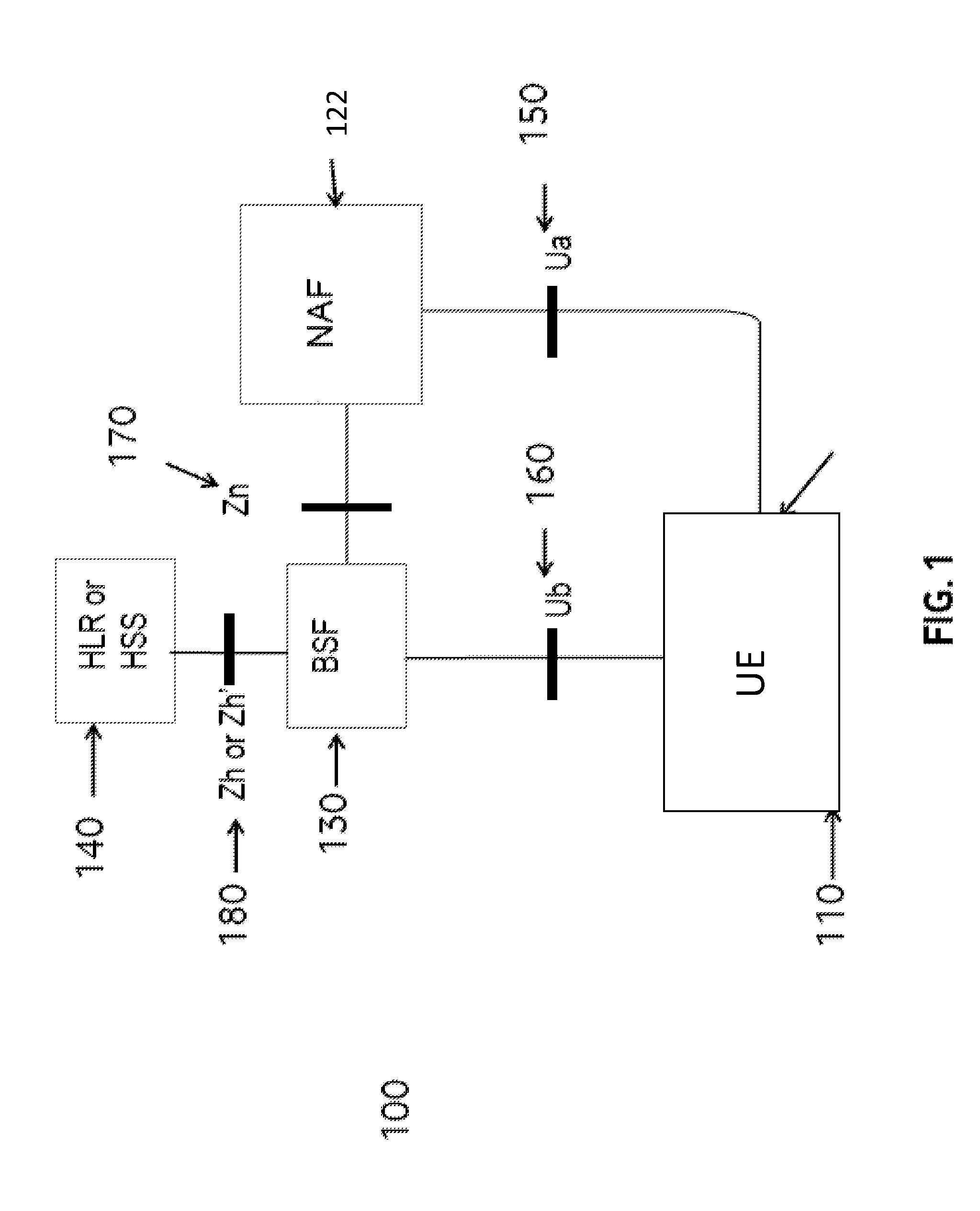
[0112]Aspects of the Generic Authentication Architecture (GAA) and Generic Bootstrapping Architecture (GBA) are identified in “Details of 3GPP standards and technologies used to implement aspects of the method and system” above. In particular, the specific architecture on which the method and system may be based is GBA.
[0113]Generic Bootstrapping Architecture (GBA) uses existing security associations between a network (e.g. a mobile network) and a card (e.g. a SIM card or UICC) to derive a key that can be used for the secure communication between the client and the server. Accordingly, if the device is associated with such a card, as well as with the client, the method can advantageously use the GBA to derive the security elem...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More