Looped network and its protecting method
A technology for ring network and ring network failure, applied in the field of network communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 4
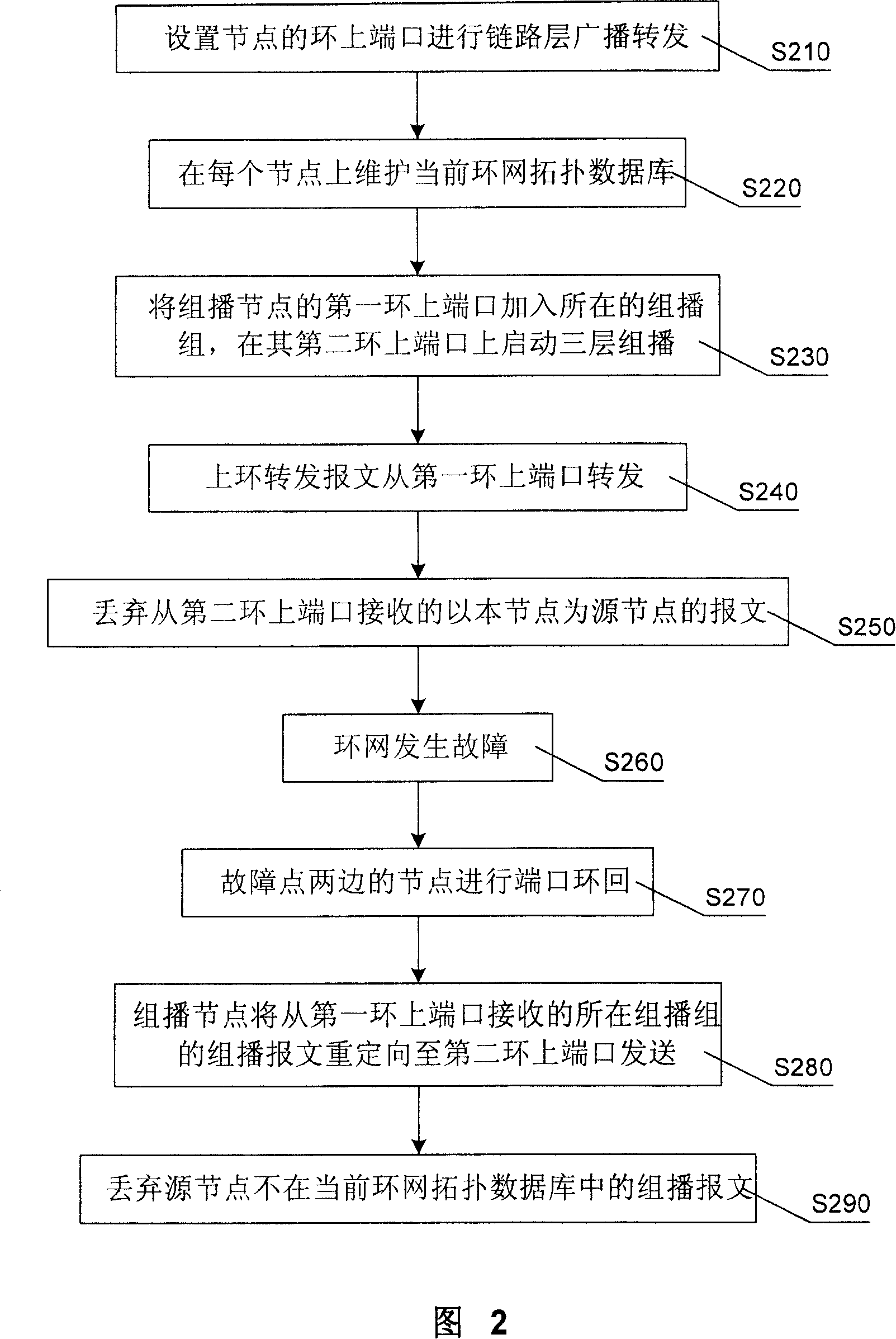
[0134] The ring network in Embodiment 4 is used to forward multicast packets, and the flow of the protection method is shown in FIG. 2 . In step S210, the link layer forwarding of the port on the ring is set on each node in a broadcast manner.
[0135] In step S220, each node on the ring network establishes and maintains a current topology database of the ring network, and retains the information of each connectable node on the current ring network and the adjacent relationship with each other.
[0136] In step S230, the node that needs to carry out three-layer forwarding of the multicast data message of a certain multicast group on the ring network and performs protocol processing on its multicast protocol message is the multicast node of the multicast group, and the multicast The port on the first ring of the node joins the multicast group, and the port on the second ring of the multicast node starts network layer multicast.
[0137] In step S240, the node forwards the mess...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com