Method and system for managing terminal open platform power information
An open platform and terminal management technology, applied in the field of communication, can solve the problem of information configuration without application rights, and achieve the effect of ensuring security and overcoming insecurity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
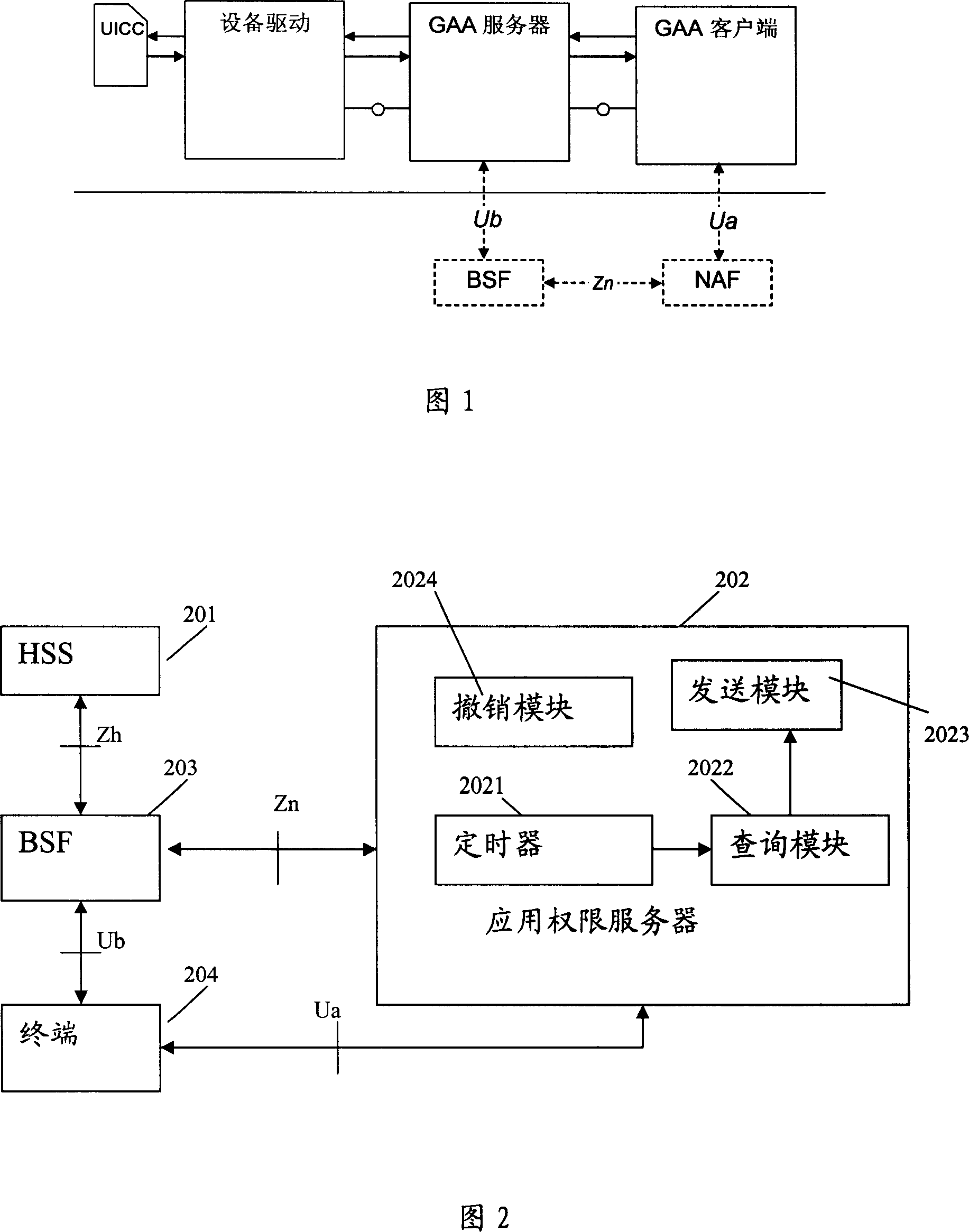
Method used
Image
Examples
Embodiment 1
[0039] In this embodiment, configuring and updating application permissions in the open platform can be realized through the terminal actively requesting relevant permission information, and the specific implementation method includes the following steps:
[0040] Step 401. An application on the open terminal platform requests access to certain confidential information during operation. (For example, a GAA application may want to access the UICC, and trigger the GBA function module of the terminal to execute the GBA process; or only require access to Ks; or only require access to the Ks derived key).
[0041]Step 402, the terminal open platform verifies the identity of the application. Legally authorized applications need to sign an agreement with the operator or manufacturer in advance to obtain information that can prove the relevant identity. The open platform uses the relevant information at the time of signing for verification, and can use public key certificates to verif...
Embodiment 2
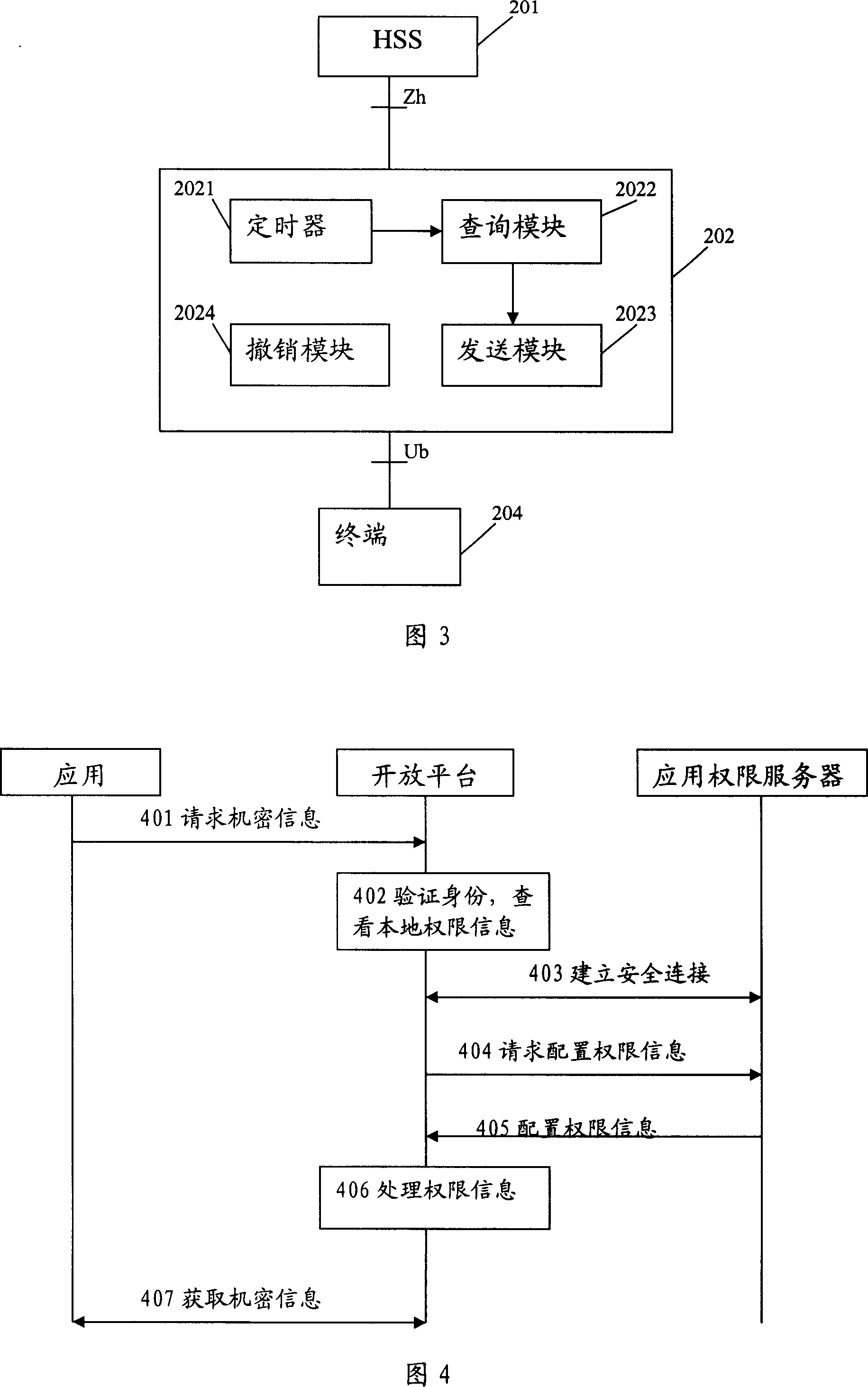
[0057] In addition to the implementation method in which the terminal actively requests relevant permission information, the network side may also use the PUSH technology to update or set the permission information in the terminal. The implementation is described in detail below based on the connection mode between the terminal and the application authority server in FIG. 2 :
[0058] Here, we choose the authority information server as the NAF to complete this embodiment, and in this embodiment, the secure connection initiated by the application authority information server is only an optional manner.
[0059] Step 501, the application authority server sends a message to the terminal, requesting the terminal to establish a secure connection with it. The application permission information server may send the message periodically or when the permission information of an application changes.
[0060] The first method: regular update; the application authority server records whic...
Embodiment 3
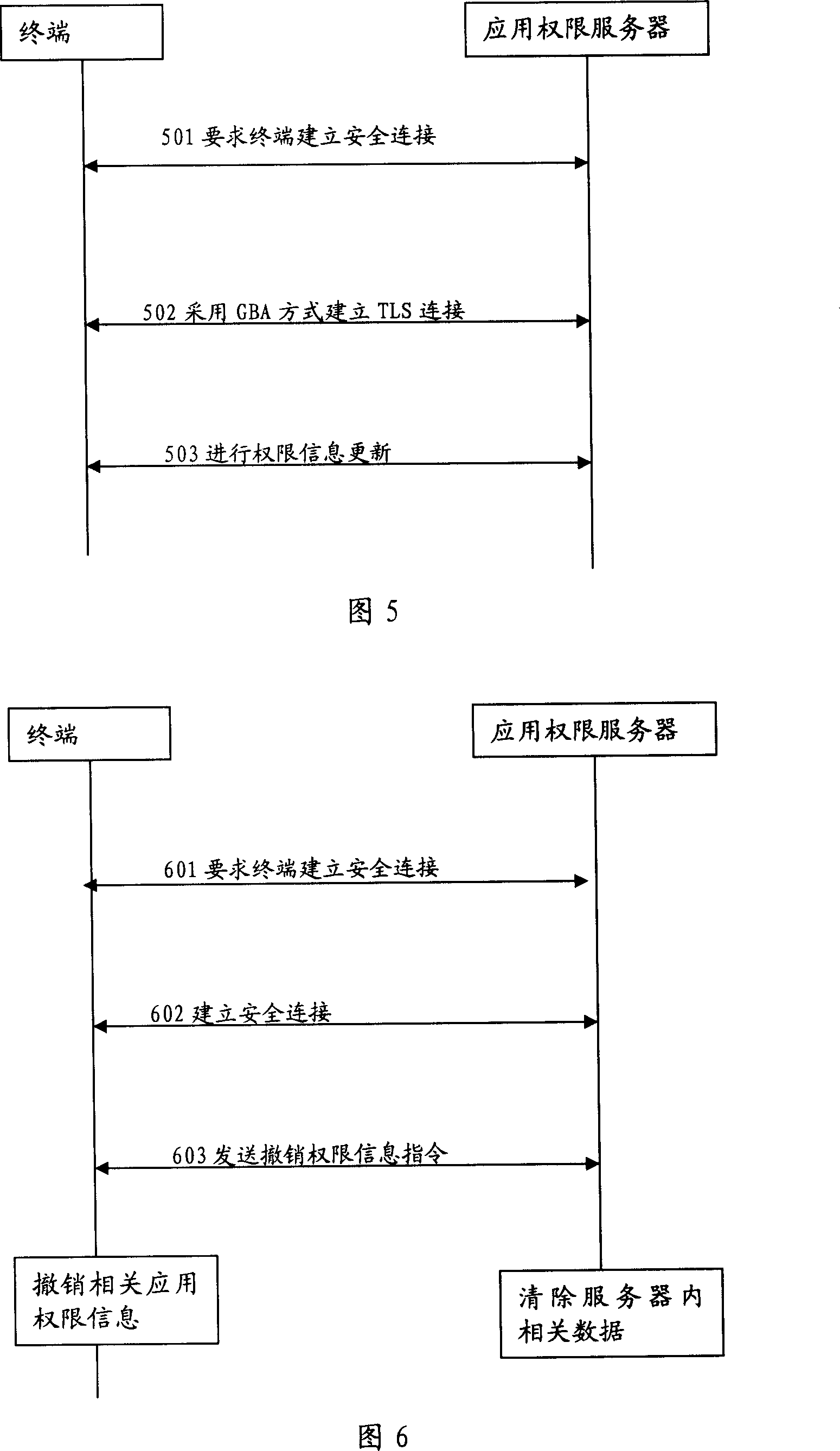
[0067] The open platform can also revoke the permission information of an application according to the command sent by the network application permission server. As shown in Figure 6, the process of revoking permission information includes the following steps:
[0068] Step 601, the application authority server sends a message to the terminal, requesting the terminal to establish a secure connection with it.
[0069] Step 602: After the terminal receives the message, it needs to actively send a request to establish a secure connection to the application authority information server. At this time, the application authority server establishes a secure connection with the terminal. The specific method of establishing a secure connection is the same as that in Embodiment 1. Let me repeat.
[0070] Step 603, after the secure connection is established, the application authority server will send an instruction to revoke the application authority information to the terminal, and the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More