Secure method of dual card combination
A safe and global technology, applied in the field of dual card systems, can solve the problems of inability to expose improper use of effective security systems, difficult to implement, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] Some implementations embodying the features and advantages of the present invention will be described in detail in the description in the following paragraphs. It should be understood that the present invention is capable of various changes in different forms without departing from the scope of the present invention, and that the description and drawings thereof are illustrative in nature and not limiting of the present invention.
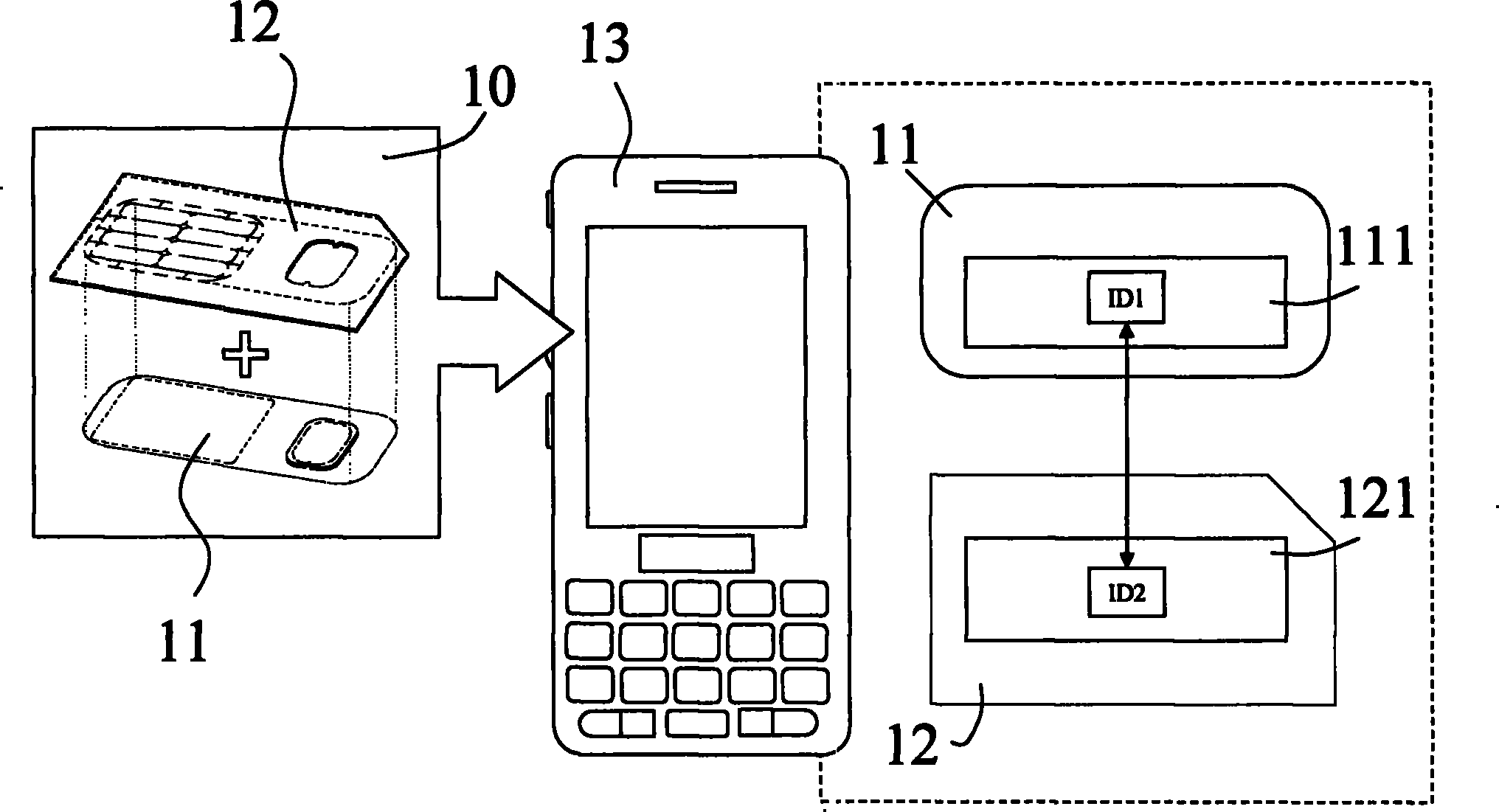
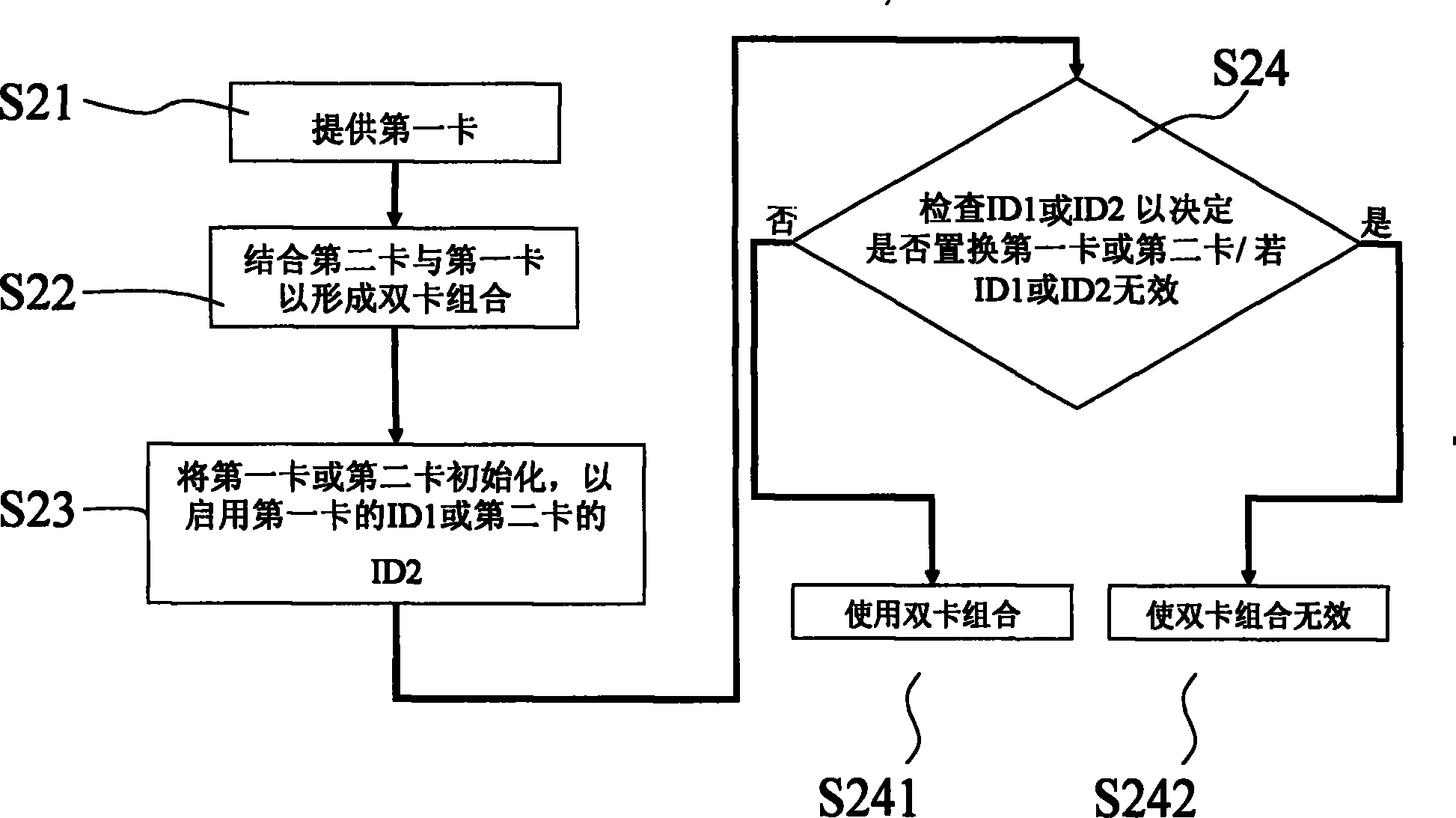
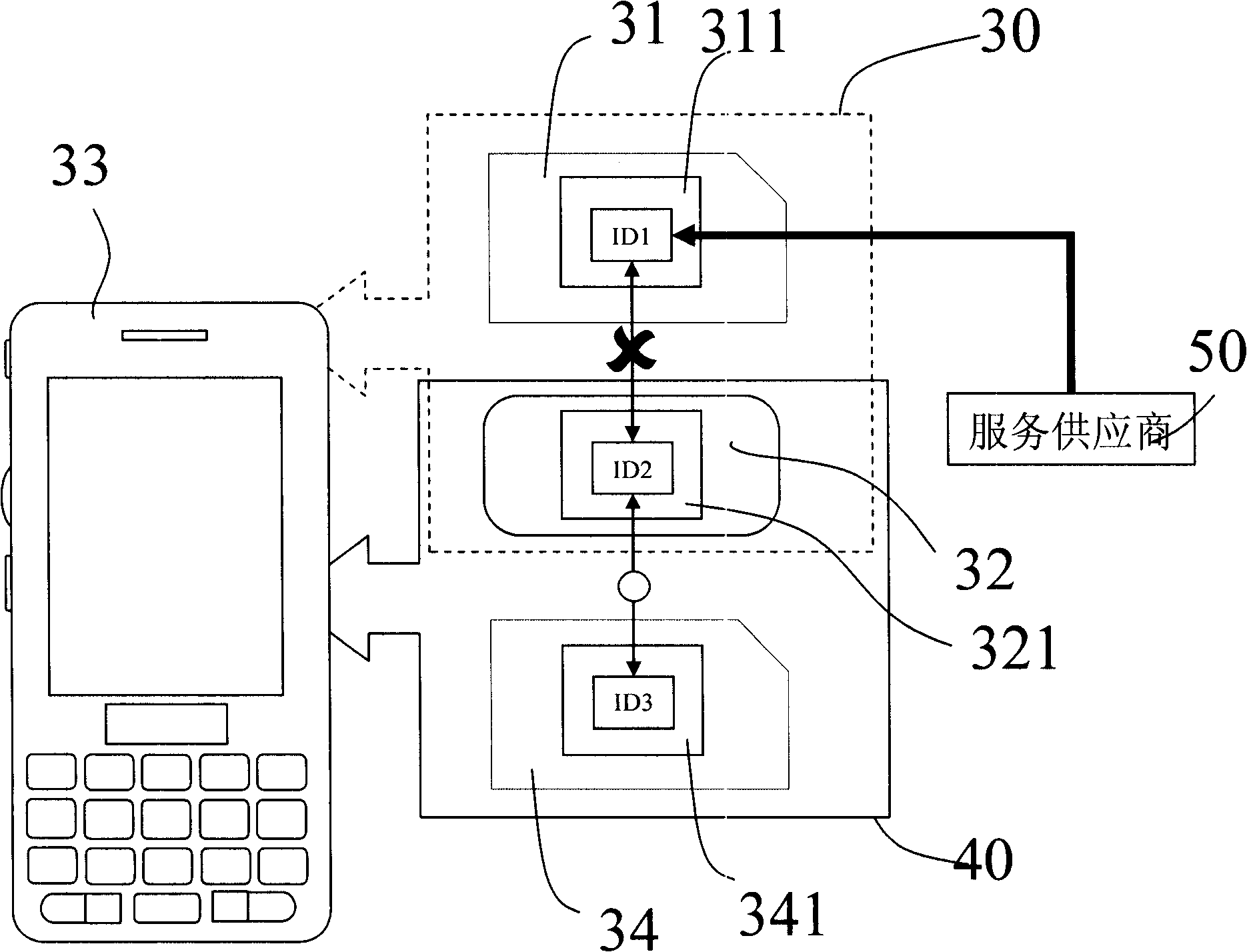
[0047] Please refer to figure 1 and figure 2 . The above-mentioned drawings are schematic diagrams of the security method for dual-card combination of a communication terminal according to the present invention. Such as figure 1 and figure 2 As shown, the security method of the present invention includes the following steps: a) providing the first card 11, as in step S21; b) combining the second card 12 and the first card 11 to form a dual card combination 10, as in step S22; The first card 11 or the second card 12 are initialized to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More