Method and equipment for establishing safe data tunnel
A technology of data tunnel and secure data, applied in the field of mobile communication, can solve the problems of complex process, unsafe data tunnel, low efficiency, etc., and achieve the effect of a simple way
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
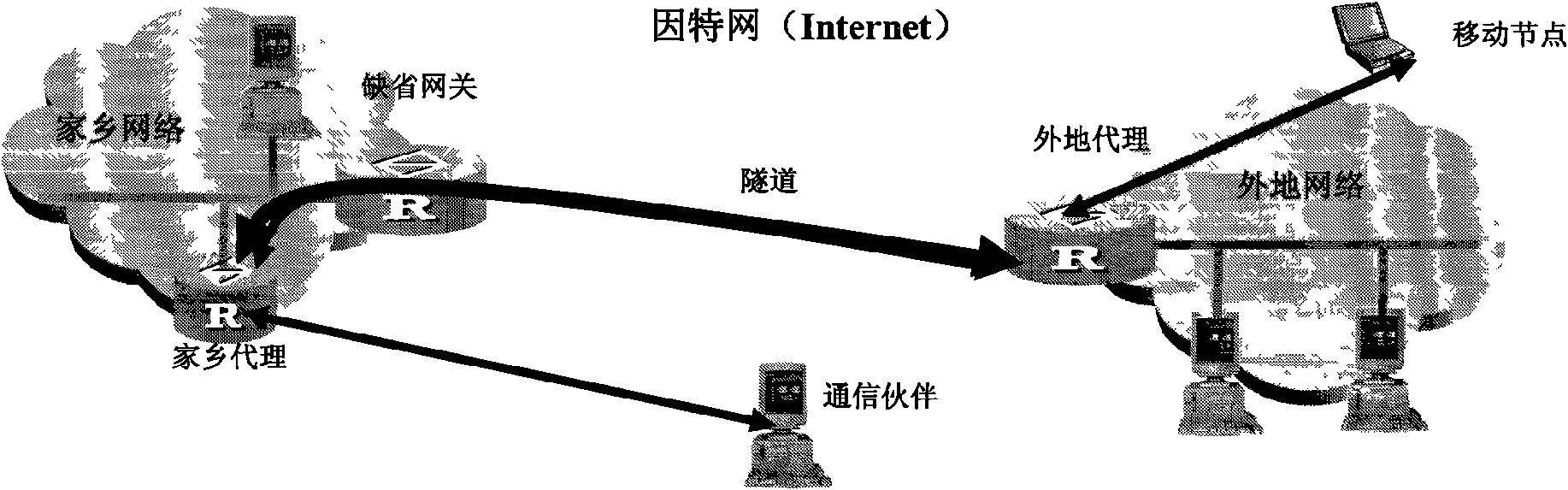
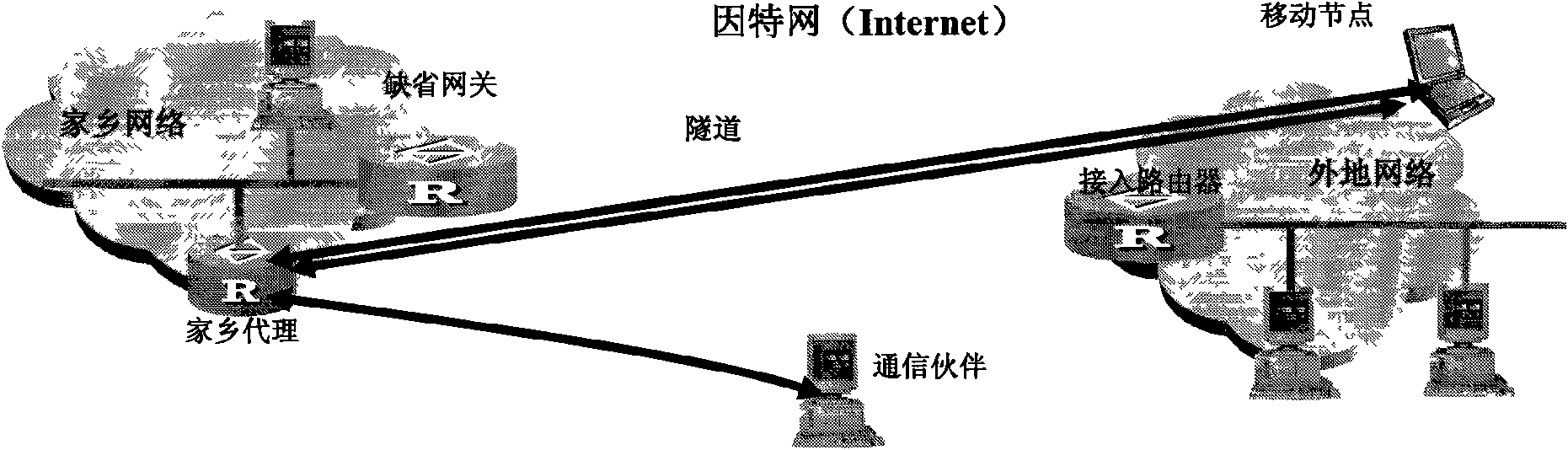
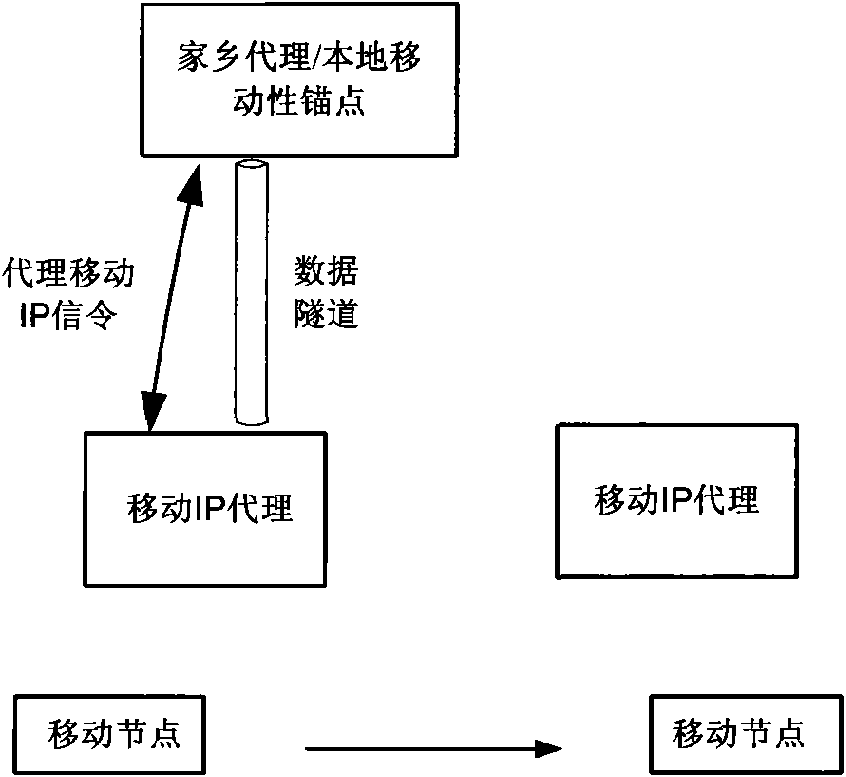
[0035] Embodiments of the present invention will be described below with reference to the accompanying drawings. see Figure 4 , is a schematic flowchart of an embodiment of a method for establishing a secure data tunnel in the present invention, wherein the IP network is a mobile IP network or a proxy mobile IP network, and the method includes:
[0036] 401. The first device sends a security parameter to the second device through a Mobile IP signaling request message, where the security parameter includes at least one of a security algorithm, a security mechanism, and a parameter for calculating a key.
[0037] Specifically, the security algorithm may be an integrity algorithm and an encryption algorithm, and the security algorithm may only include the integrity algorithm, or only the encryption algorithm, or include the two algorithms. If the first device and the second device have agreed on the security algorithm to be used in advance, the security algorithm may not be inc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More