Mutual authentication method between terminal and server
A two-way authentication, server technology, applied in user identity/authority verification, key distribution, can solve the problem of low communication security, and achieve the effect of ensuring security and privacy, simple two-way authentication method, and realizing protection.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0007] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
[0008] The two-way authentication method between the terminal and the server of the present invention is applicable to a general terminal (client)-server communication architecture, and the terminal can be a PC (Personal Computer), a mobile phone, a PDA (Personal Digital Assistant), a PMP (Personal Media Player) ) and other communication terminals.
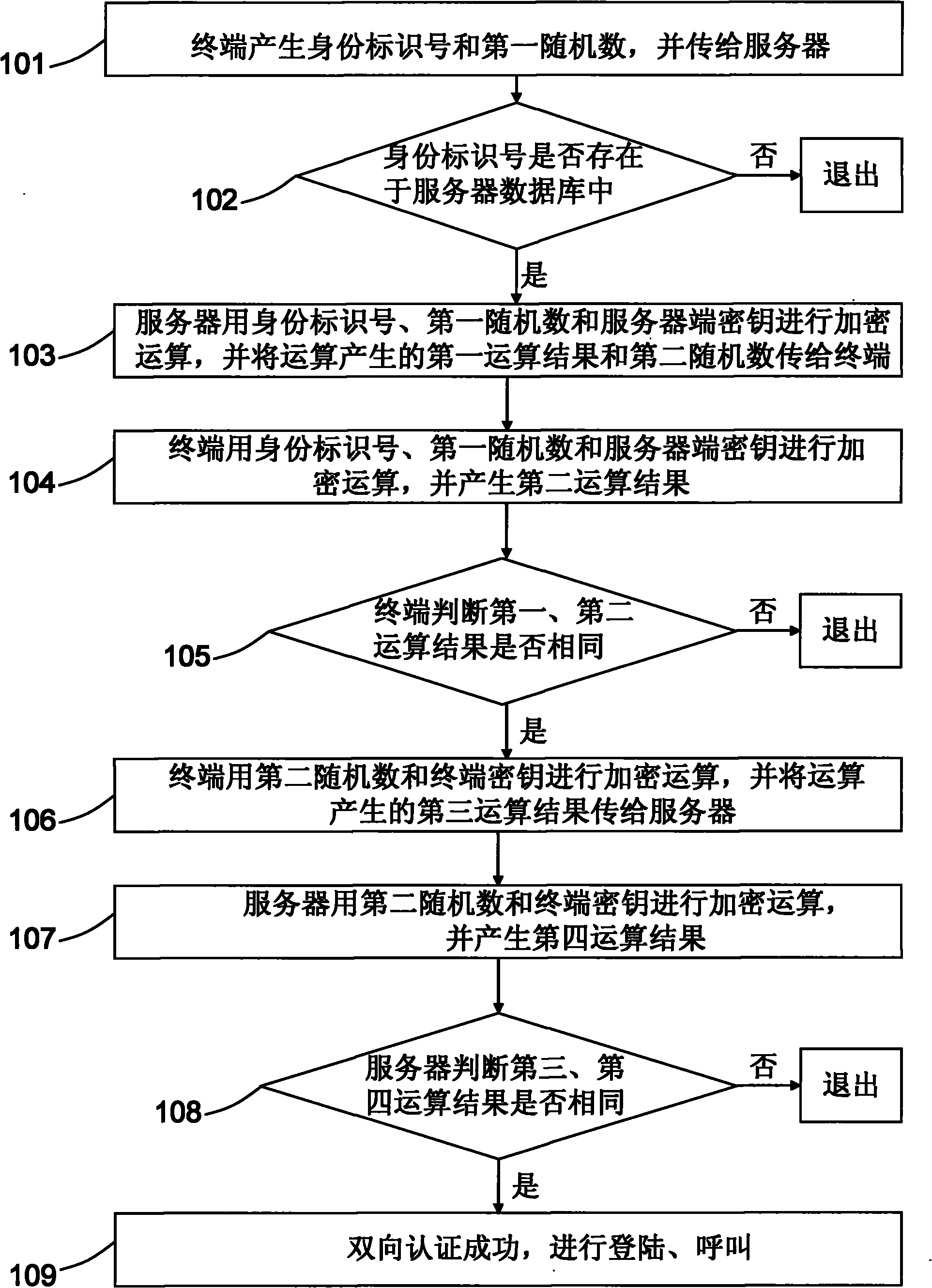
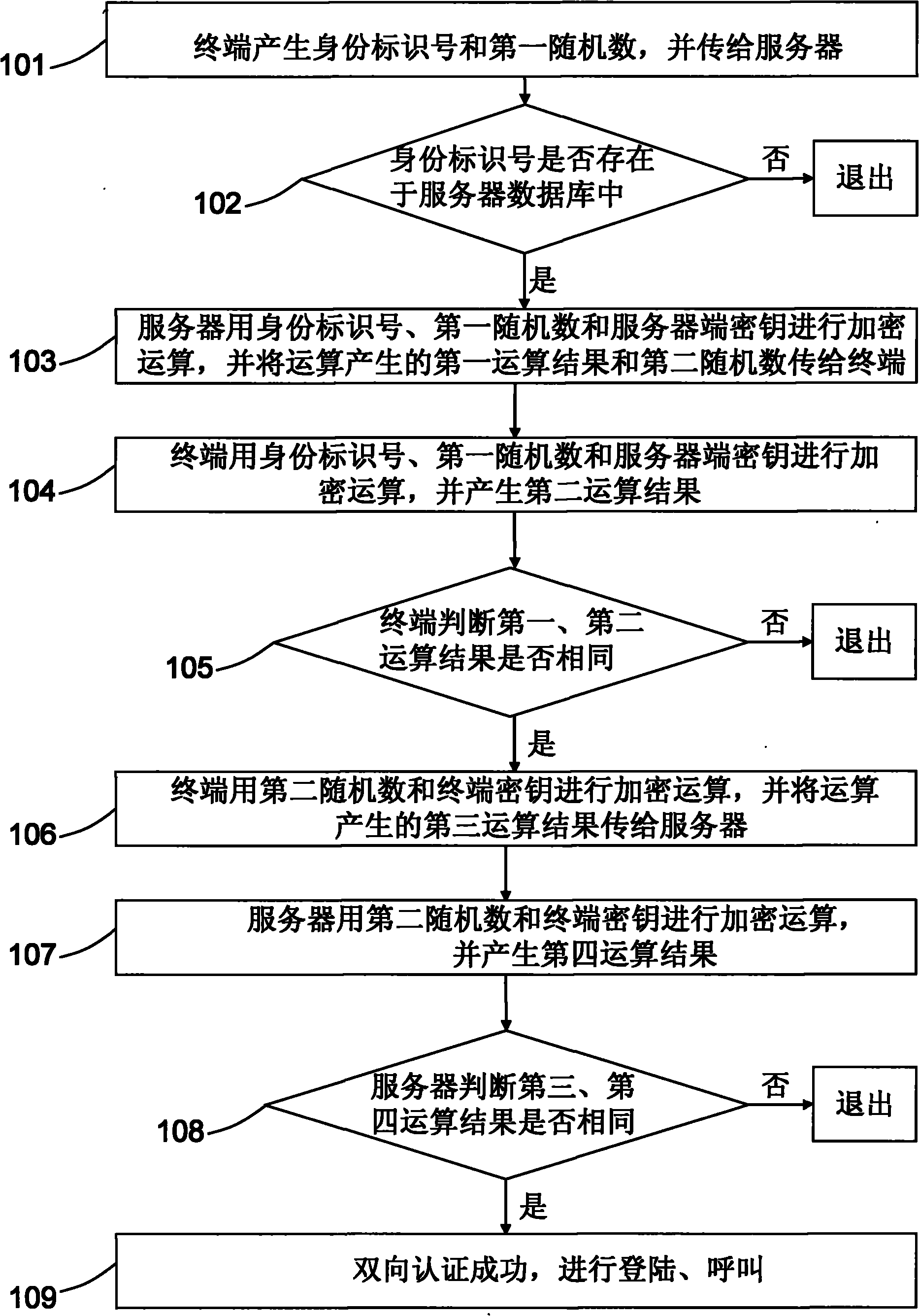
[0009] see figure 1 , is a flow chart of the two-way authentication method between the terminal and the server of the present invention. The two-way authentication method between the terminal and the server includes a process for the terminal to verify whether the server is legal and a process for the server to verify whether the terminal is legal, wherein the process for the terminal to verify whether the server is ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More