Network intrusion character configuration method and system
A network intrusion and configuration method technology, applied in the field of network security, can solve problems such as service termination, difficulty in obtaining upgrade packages, and difficulty in user acceptance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
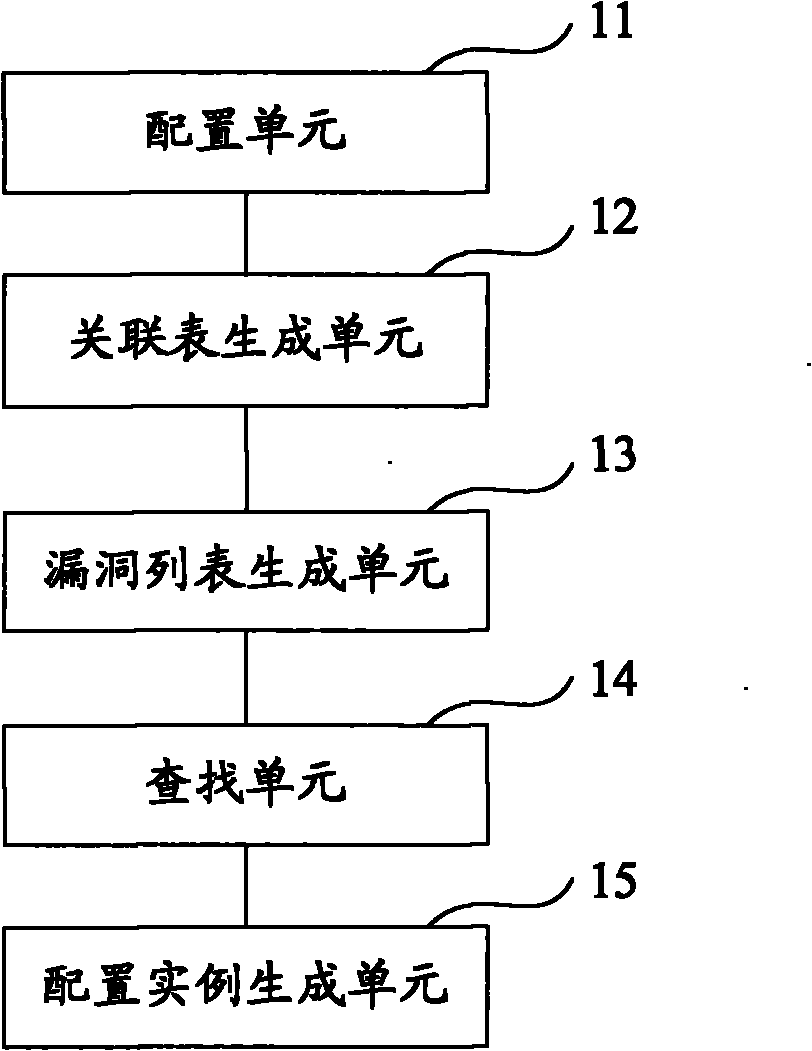
[0041] Embodiments of the present invention provide a network intrusion feature configuration method and system, which are used to provide IPS product users with a network intrusion feature configuration set that best matches the actual environment, so as to block illegal attacks on system loopholes in a targeted manner.
[0042] In order to facilitate the understanding of those skilled in the art, the best implementation of the present invention will be described in detail below in conjunction with the accompanying drawings.
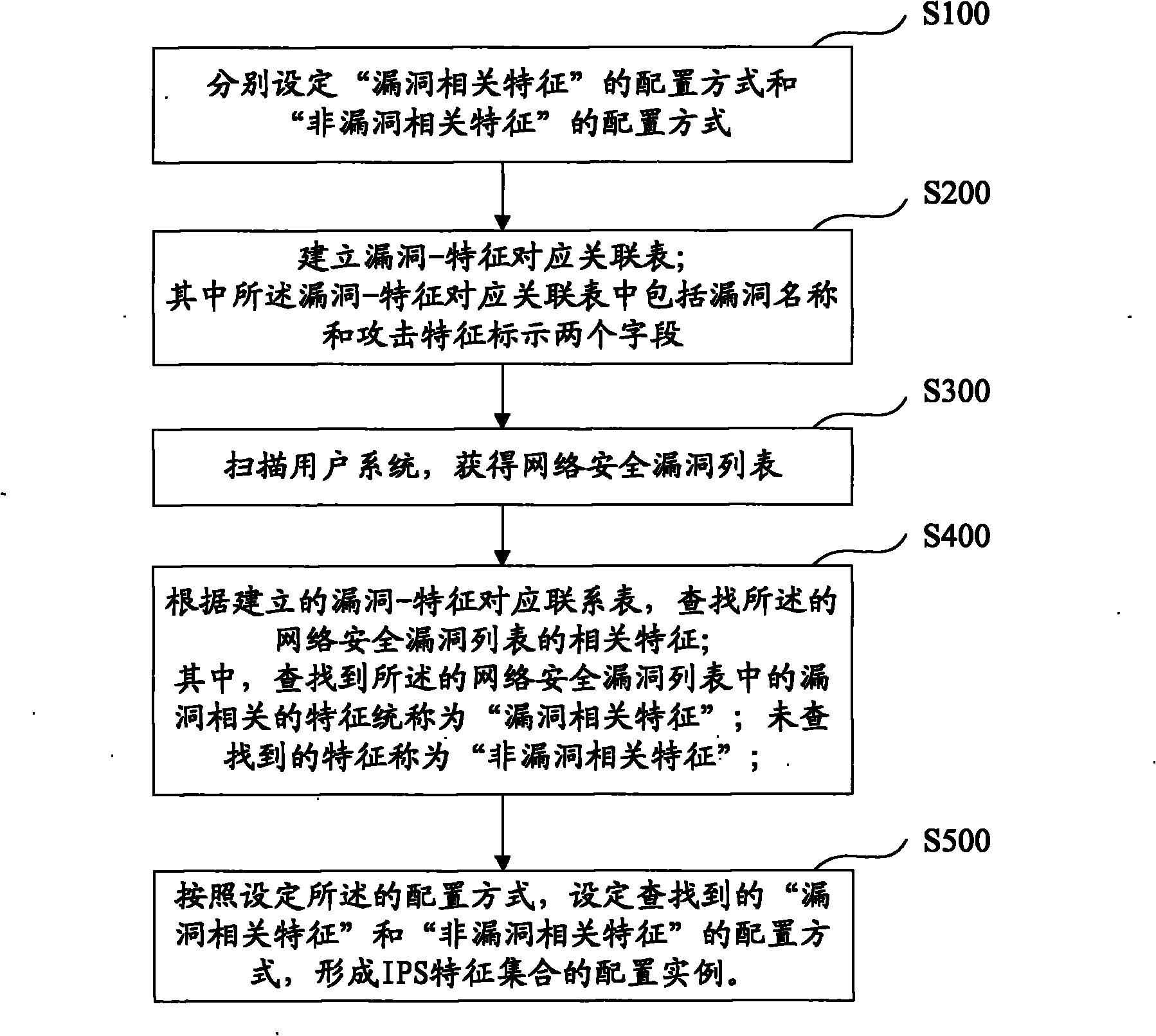
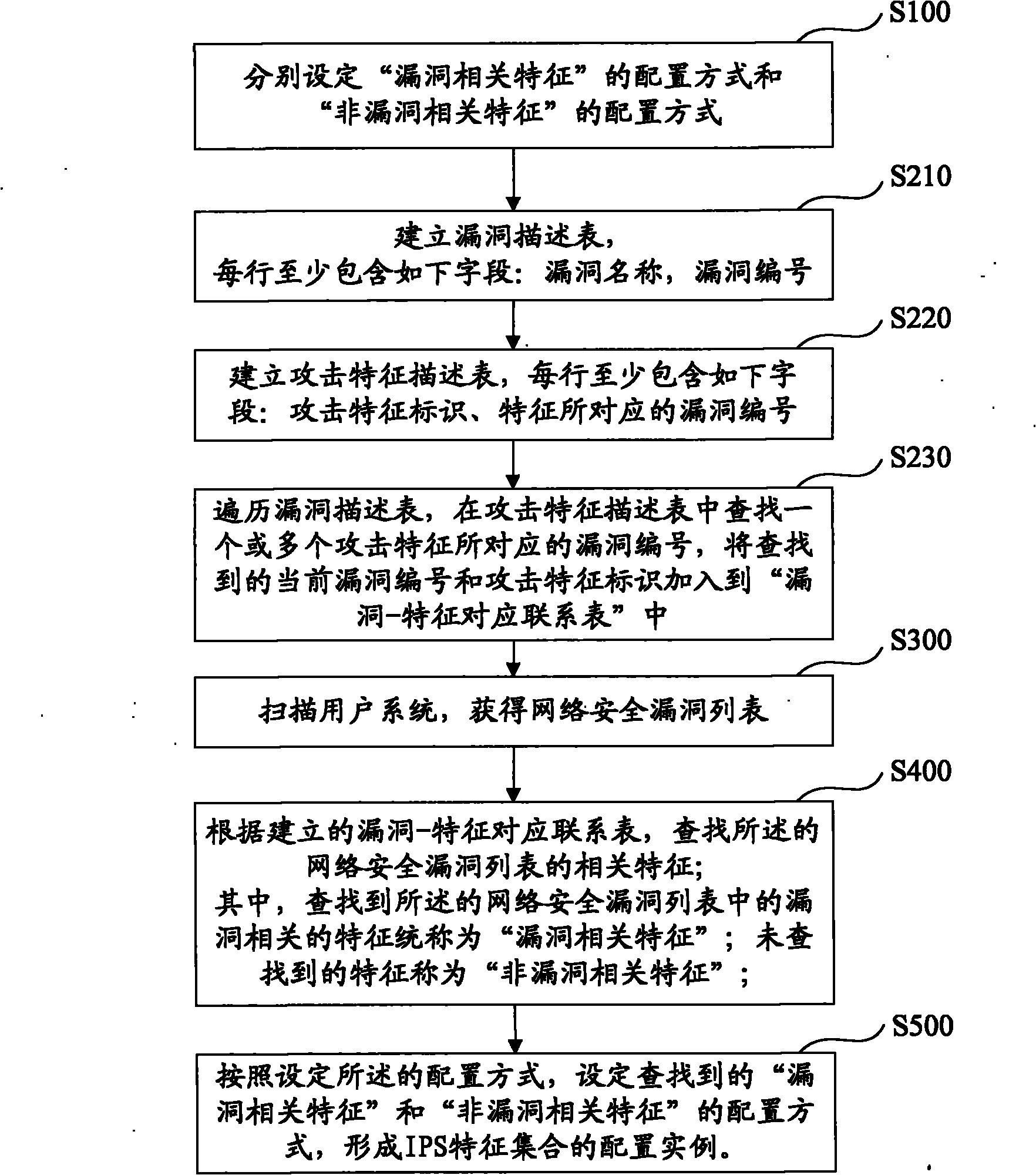
[0043] see figure 1 , which is a flow chart of the first embodiment of the network intrusion feature configuration method according to the present invention.
[0044] The network intrusion feature configuration method described in the first embodiment of the present invention includes the following steps:
[0045] S100, respectively setting a configuration mode of "vulnerability-related features" and a configuration mode of "non-vulnerability-related f...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More