Software authentication method based on softdog
An authentication method and dongle technology, applied in the direction of instrument, program/content distribution protection, electronic digital data processing, etc., can solve the problem of harming the interests of software publishers and software developers, low security, and insufficient protection of software authentication, etc. question
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
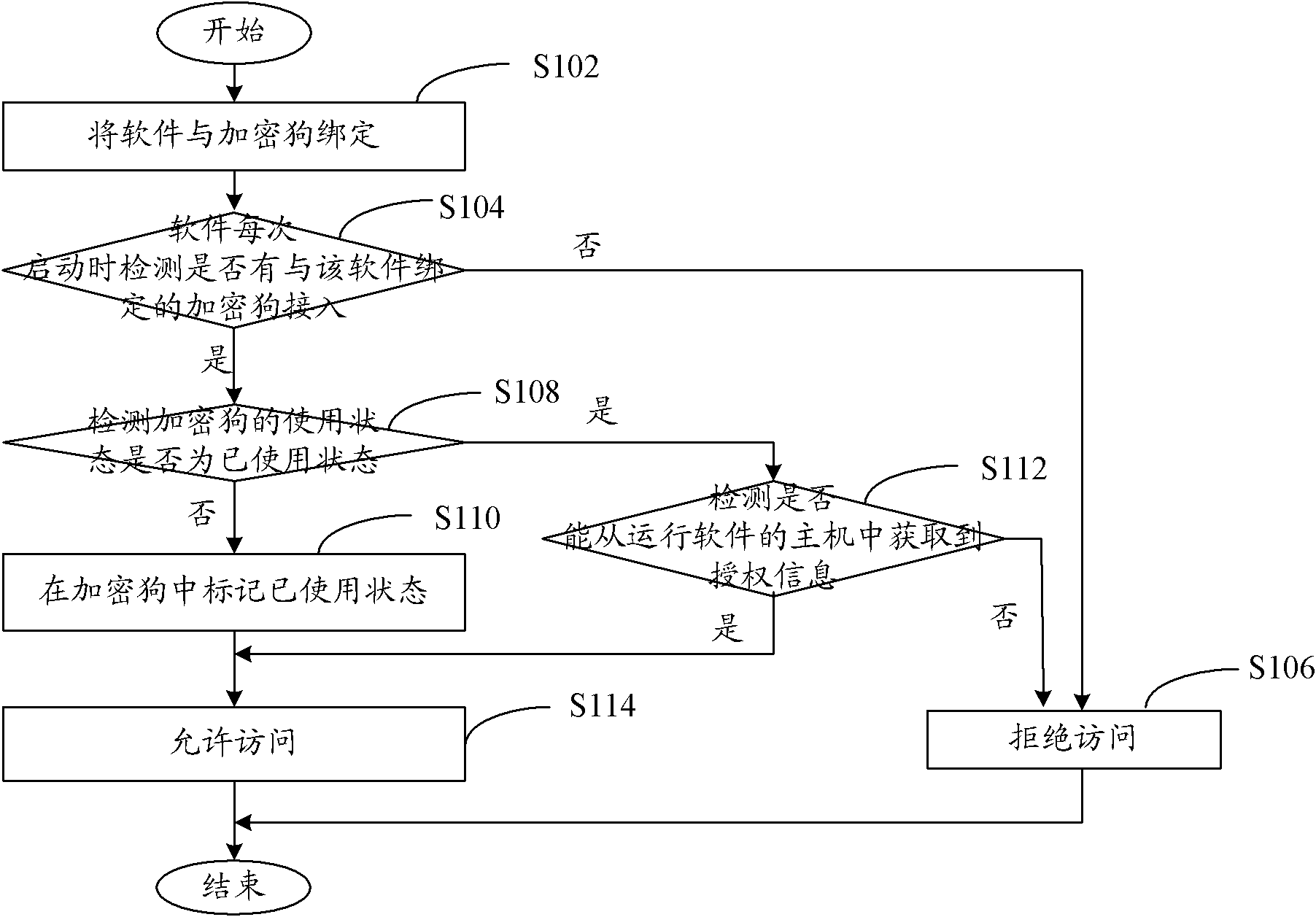
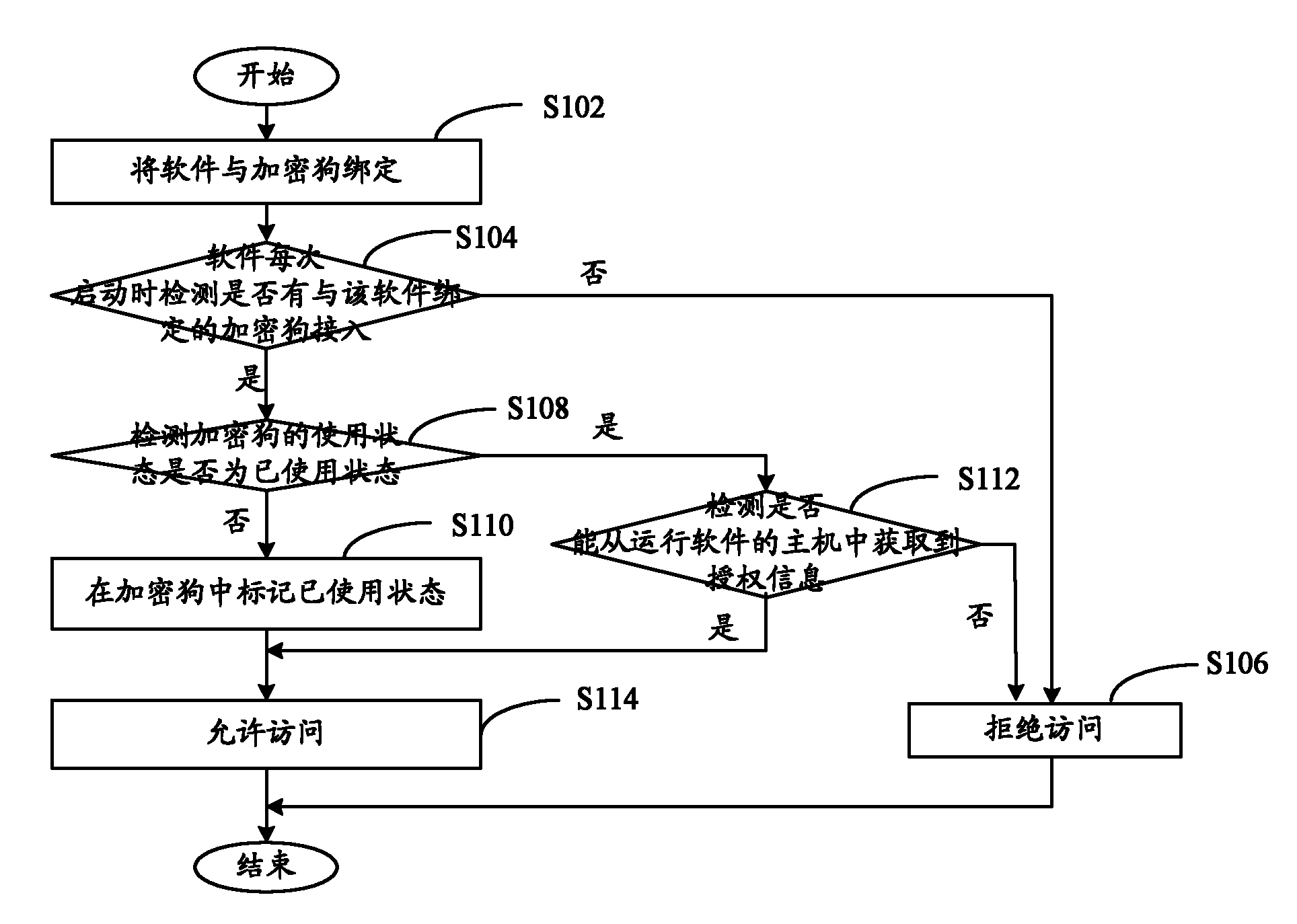
[0031] Such as figure 1 As shown, in Embodiment 1, the software authentication method based on dongle includes the following steps:
[0032] Step S102, binding the software with the dongle. Bind the protected files in the software with the dongle. When the user runs the software, the dongle needs to be inserted into the host where the software runs, otherwise the software cannot run.
[0033] Step S104, check whether there is a dongle bound with the software every time the software is started, if yes, go to step S108, otherwise go to step S106.
[0034] Step S106, access is denied. When the connected dongle is not a dongle bound with the software, the access is directly denied.
[0035] Step S108, detecting whether the use state of the dongle is in use, if yes, proceed to step S112, otherwise proceed to step S110.
[0036] Step S110, mark the used state in the dongle. If the usage state of the connected dongle is not in use, it indicates that the connected dongle has not ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More