Method for realizing network security and star network
A star-shaped network and network security technology, applied in the field of network communication, can solve the problems that the security of the star-shaped network needs to be improved, cannot be monitored in real time and block the leakage of internal confidential data, etc., and achieve the effect of improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
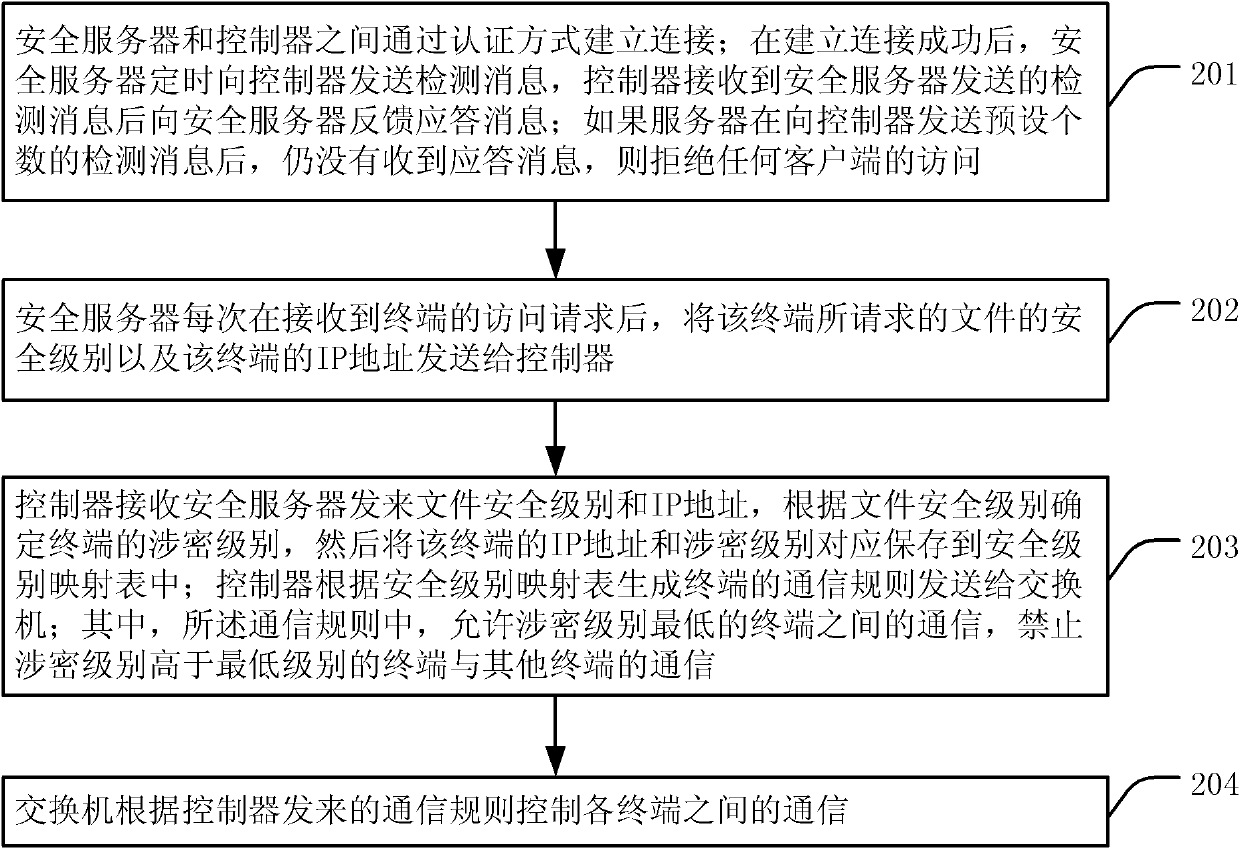
[0022] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
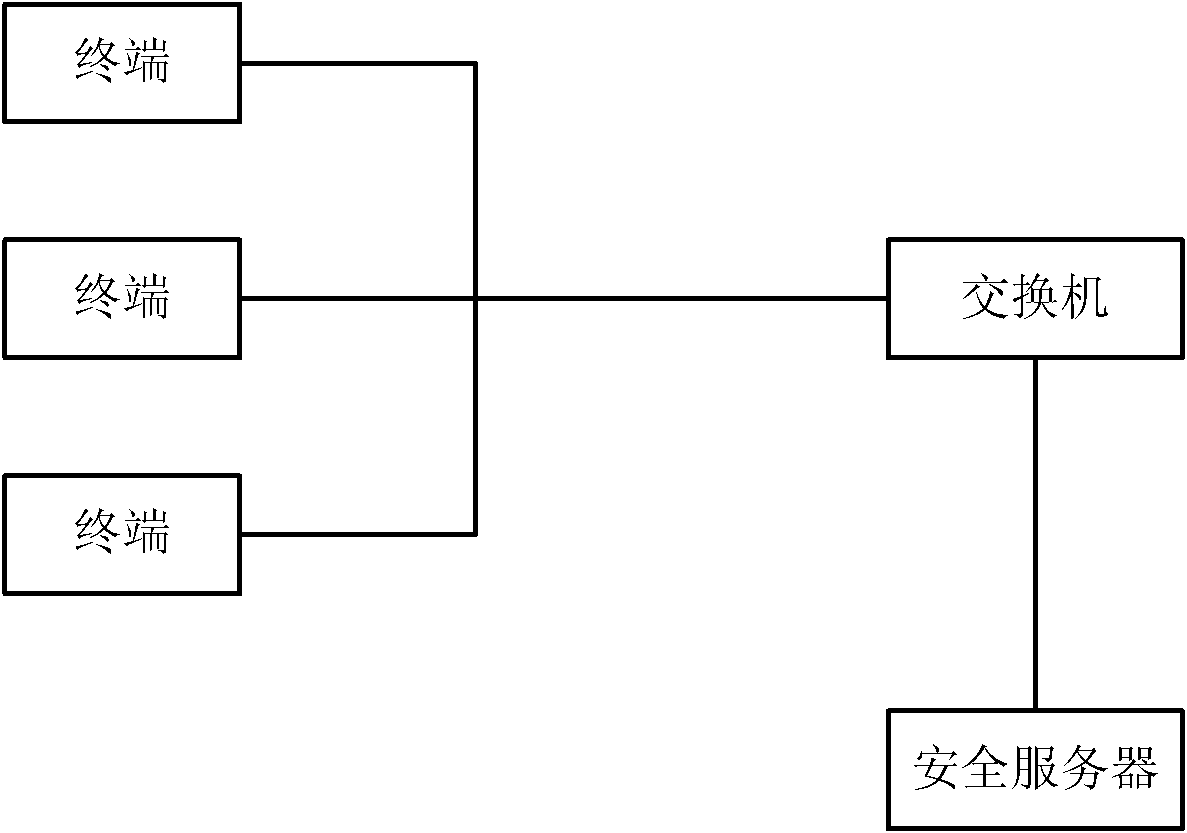
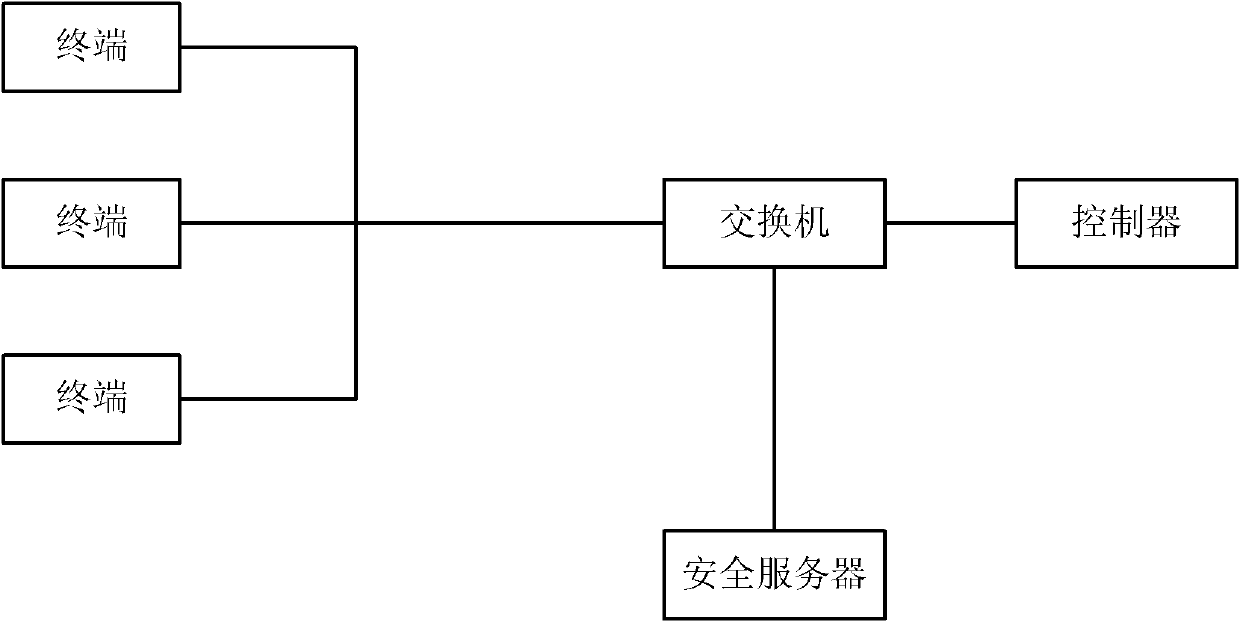
[0023] figure 2 It is a schematic diagram of a method for realizing network security in an embodiment of the present invention. This method is applicable to a star network in which a plurality of terminals communicate through a switch, and the multiple terminals access a security server through the switch, and a controller is also arranged in the star network, then as figure 2 As shown, the method includes:
[0024] 201. A connection is established between the security server and the controller through authentication; after the connection is successfully established, the security server regularly sends a detection message to the controller, and the controller feeds back a response message to the security server after receiving the detection mes...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More