Enciphering and deciphering method for invoking data in software
A technology of encryption and decryption, encryption algorithm, applied in the field of information security, can solve the problem of neglecting data protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
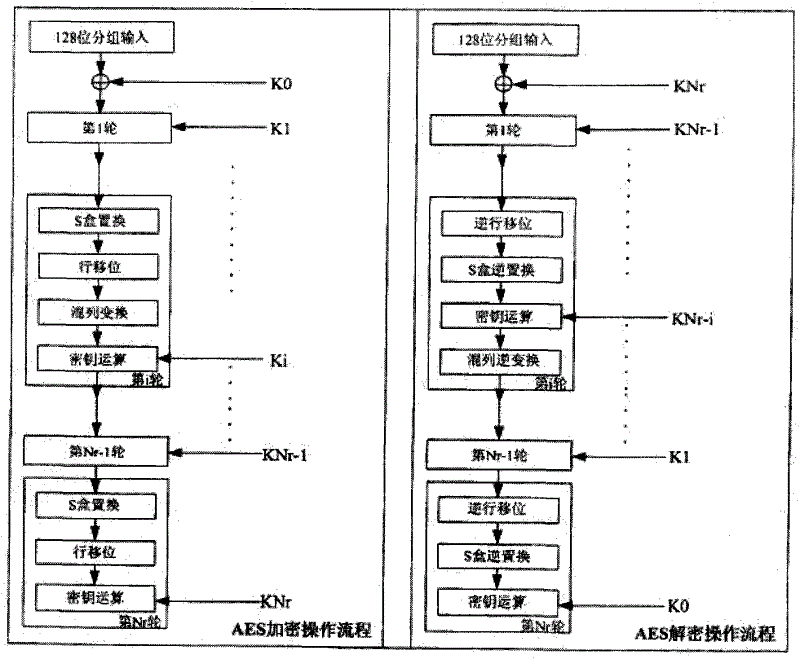
Method used
Image
Examples
Embodiment Construction
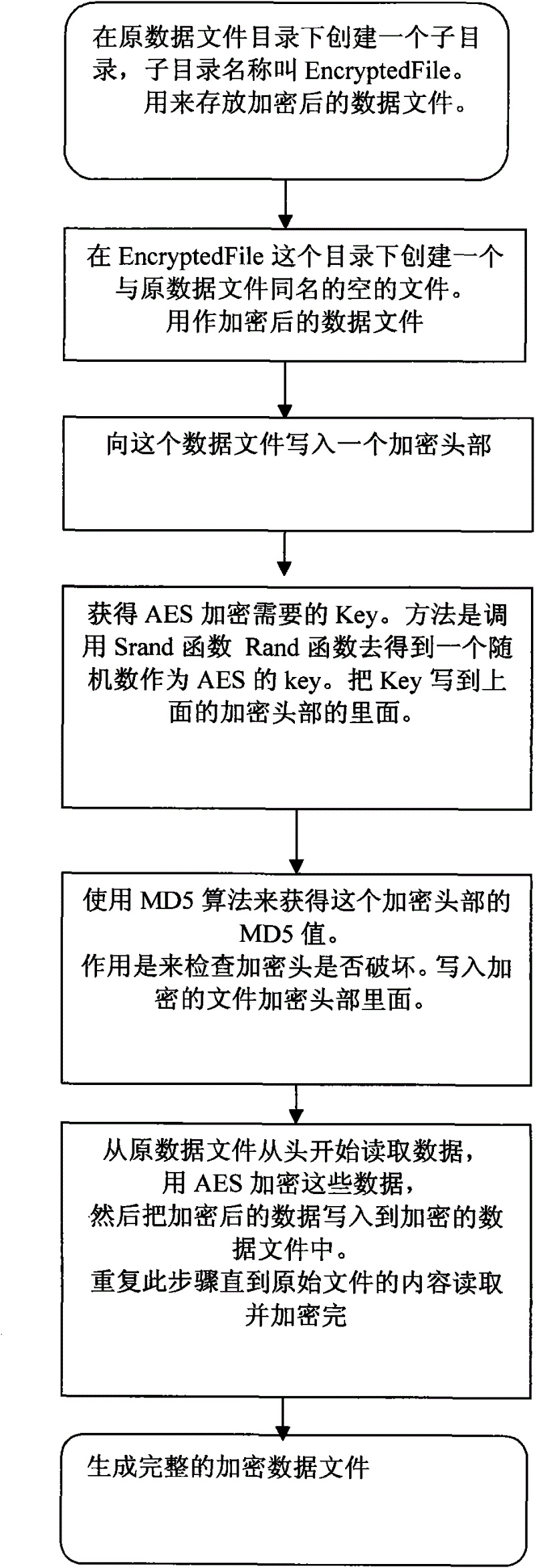
[0017] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described below in conjunction with the accompanying drawings and specific embodiments. Assume that the source data file is stored in the C drive, and the data file name is A, such as figure 2 Its workflow is shown as follows:
[0018] Create an empty data file in the same directory, named A1, which is used to store the encrypted data file; read the data file from the source file A, use the AES encryption algorithm to encrypt the data in A, and write Into A1, before writing to A1, it is necessary to make two judgments on the encrypted file header: the encrypted file header is a part of file A1: (start to perform the judgment operation) when the encrypted file header of A1 is empty, write to it Enter the encrypted file header; when the encrypted file header of A1 is not empty, use the MD5() algorithm to make a second logical judgment on...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com